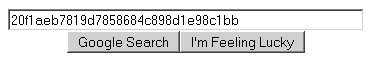
Usually we’re into hardware hacks, but once in a while I run across something that’s just too good. [Steven]’s blog was cracked a while back, and while he was doing forensics, he was trying to crack the md5 hashed password for the unauthorized account. Eventually he slapped the hash into Google, and guess that it was ‘Anthony’ based on the results that came up. Thanks to [gr] for pointing it out.
(Yes, I know it was on Slashdot a few days ago, but I don’t care.)
24 thoughts on “Google As A Password Cracker”
Leave a Reply
Please be kind and respectful to help make the comments section excellent. (Comment Policy)
















And this is why you should salt your hashes.
That is cool… and scary… simultaneously. I’ll have to try that next time I hack Microsoft. :-P
Not to mention ketchup and tabasco sauce.
This is only useful if Google has at one point indexed a hash and its decrypted counter-part (which is highly unlikely), and if you can actually get your hands on the hash in the first place! Your better off using a reverse MD5 database utility like this one: md5.benramsey.com
This is equivalent to saying, look my name is in google!
Nothing really special about it and there are much better tools for doing it.
Now if google included a reverse lookup for md5 that would be something to talk about.
Actually, this is more effective than you would think–it worked for me in a test situation 15 times out of 20.
thats pretty interesting, i was looking for a similar hash to decrypt, i’m not sure if it’s md5, but I wish i thought of it.
You know, google tracks every search.
so , it s nice what i m saying , i already test it, but it doesn’t work every time, if it’s stored in some pages we can say it but not every time
i think that i will speak about that in my blog if u wanna let a comment :
http://amedupirate.c.la
http://en.wikipedia.org/wiki/MD5#_note-5
http://www.lightbluetouchpaper.org/2007/11/16/google-as-a-password-cracker/
ya… This just goes to show that you should definetly salt your hashes, but some people are just too stupid / lazy to do so.
Even better. You can take a password, hash it, then search google for the hash to find out if other admins have used it as a password :D
If this works on production site or database then the people there must be morons.
It’s the equivalent of having your password guessed by a human..literally. Hash tables work on the same model. They don’t actually attack the algorithm just the lack of creativity by a user base.
That’s why you have to add some “custom” encryption and not rely on built in functions…
Simply reading/translating a sha1 or md5 takes 0.0002 seconds and about 5 lines of code…
So if I googlefight MD5 hashes, I could check which passwords are used more often? I understand it wouldn’t be very accurate because people salt their hashes and stuff, but with googlefight, how convenient is that!
I think this is something people tend to be interested in check out try a MD5 here
http://us.md5.crysm.net/
hi,I dont know much about hashes and i got a question: i got this hash “JR:1003:aad3b435b51404eeaad3b435b51404ee:37c088d8d1e18c245c25483c5fd5314d/empty/:
How can i know if is ntlm or md5? and if is ntlm there is a way to convert it in md5? thanks for the help
While using Google to crack MD5 passwords is interesting and useful, I don’t think it’s really worth posting about. I thought this use of Google was obvious; I’ve done it myself a few times.
hmm lets hash a password
http://www.zappersoftware.com/Help/md5.php
take hash pop it into Google and trys it….
op my password looks good, not in Google.
I would think this only works for a dictionary of common words. Trick is add #’s to your passwords people. Lets be smart.
I wrote this site http://www.md5crack.com to do this with relative ease. check it out
Uhmm.. what is an md5 hash?
Funny, when I $ `echo anthony | md5sum`, I get “e4ea5477492b160a8d7aeac1fb16d107 -“
Hello. I am woman. Could you help me, that I find out password of Admin of one forum? I am from Croatia and in one Forum, they behave very very unfair to me. So, now I want to log myself as Admin, and do one little funny revenge to them. Could you tell me what is the way for doing that? Thank you. Some Trojan program, or something similar?
Could you please move my surname? :)