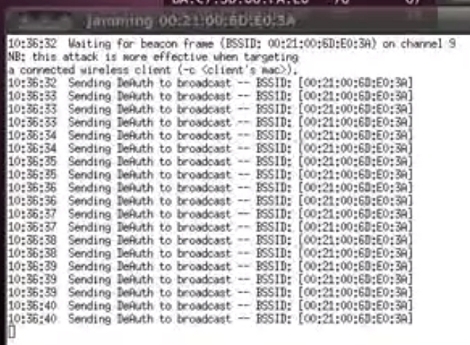
[Elliot] put together an intriguing proof-of-concept script that uses repeated deauthentication packet bursts to jam WiFi access points. From what we can tell it’s a new way to use an old tool. Aircrack-ng is a package often seen in WiFi hacking. It includes a deauthentication command which causes WiFi clients to stop using an access point and attempt to reauthenticate themselves. [Elliot’s] attack involves sending repeated deauthenitcation packets which in essence never allows a client to pass any data because they will always be tied up with authentication.
After the break you can see a video demonstration of how this works. The script detects access points in the area. The attacker selects which ones to jam and the script then calls the Aircrack-ng command. If you’ve got an idea on how to protect against this type of thing, we’d love to hear about. Leave your thoughts in the comments.
[youtube=http://www.youtube.com/watch?v=RmabhHiQ4yY&w=470]















SIR!
I am going to help you.
Please unplug your router form the wall.
Now plug your router back in.
Did that fix the problem sir?
Outsourced tech support at its finest.
hahahahaha!!!!!!
SUPERVISOR IS GENIUS!
S: Thank you to calling getnear tech support.
U: There’s a burning smell coming from my router.
S: Do you see a blinking light on your router?
U: There is smoke coming out of the router!
S: Ok, do you see a blinking light on the router?
U: Fire! It has burst into flames!
S: I cannot proceed with tech support unless you tell me if you see a blinking light.
U: AARG! Now the curtains are on fire!
S: I cannot help you with your curtains, sir.
You will need to call tech support of the people who sold you your curtains….
Tech Support at its best, who am I to complain ?
The aireplay command requires a parameter for how many deauths to send. I figure most people who have messed with aircrack at one time or another have put a really big number in there and realized it’s like a DoS attack.
As far as protecting yourself, I read some radios just ignore the deauth packets. If yours doesn’t, my guess is the deauths are handled in firmware/hardware so it might require some hacking. I don’t think WEP/WPA encryption protects from this attack, as I thought you could deauth a WPA client to capture the handshake.
aireplay-ng doesn’t require specifying a limited number of deauths. Using the number 0 is unlimited. I’m really shocked to see this script included on had since all it does is save you a few seconds typing airodump and aireplay commands, and includes nothing unique.
Nope. This is a 802.11 issue. But the attacker is injecting packages (radio transmission), so it could be detected and located. Then the baseball bat works well.
Shotgun diplomacy, hehe.
I think encryption does protect, because if you’re not authorized to issue commands to the router, you can knock but you can’t come in. That’s why PASSWORDS do exist. I also noticed he selected a channel showing “Open” that is unsecured. By which commands are authorized.
The commands aren’t to the router, its to the clients. It’s sending de-auth as a spoof of the AP’s MAC address. Also, if you look again the connection he is interfering with is WPA encrypted, the SSID is “openn” which doesn’t make it unencrypted just by giving it that name..
yep… this seems to be a very effective method of stopping all wireless communication. I dont see a way around this after thinking about it for a few minutes… even if the router were programmed to stop responding, it could still be a battle of SNR.
if(deauth_req_count > 2 && last_time_deauth < (10 * SECONDS)) ignore_deauth_req(10 * MINUTES);
Very basic stuff you’d think any coder would put in any code be it (driver-)software or firmware released since 25 years ago.
Thanks! we’ll patch immediately!
Hmm.. Mikrotik can encrypt the management part of the 802.11 protocol but only for mikrotik clients (It essentially breaks the protocol). I believe the Xirrus APs have such a feature built in to block rogue APs. They only way I can see to secure against this would be to encrypt the association packets to prevent spoofing of the disassoc packets.
wont this just irritate people at the airport :D
This could be the answer to aeronautical WiFi – especially where people are making VoIP calls!
Oh, you should see the controversy over Hotels wanting to jam routers. Sour grapes theory says that if you break everyone’s toys, they break yours.
I remember seeing someone who made a script that would scan and deauthenticate devices with Apple MAC addresses.
Woah, that sounds like an neat application. But how can you tell the vendor of the device based on a MAC address?
The first 3 bytes are dedicated to an organization, known as the OUI. You can look up who developed a device here:
http://standards.ieee.org/develop/regauth/oui/public.html
And if you really want to, you can download the database (updated daily) here: http://standards.ieee.org/develop/regauth/oui/oui.txt
MAC addresses are assigned in blocks to manufacturers. The first couple of bytes can be used to determine the manufacturer.
seems they have a bunch of them registered:
http://standards.ieee.org/cgi-bin/ouisearch
That’s not completely effective, as many Macs will have MAC addresses assigned to Intel.
Also, the world is full of duplicate and mismatched MAC addresses. They’re not really unique.
Not completely effective but great fun in the Apple sore, anyway.
It’s called Airdrop-ng.
This has been a fairly long-standing denial of service attack – Kismet has had it in the IDS for quite some time (on the order of 5 years or so), and the commercial WIDS systems have as well.
There’s no good defense under the current standards because management frames are unprotected.
You could modify your driver to be non-standards-compliant and ignore deauth/disassoc frames. You could be marginally more standards compliant and accept directed frames and ignore broadcasts.
There’s some standards being added to try to protect management frames (dot11w) but at best they’ll require a full overhaul of all the APs and clients to enforce them.
You could also go the proprietary route, with something like Cisco CCX which can help prevent it.
Or you get your handy crowbar, find the jerk knocking your network apart, and hit them with it.
NatureTM: No, wpa will not protect against it, because it’s management not data layer and as you say, there’s no protection there.
Adam: You’re smacking the clients, not the router, so every client driver would have to be modified with some sort of mitigation. There wouldn’t be a battle of SNR, so long as the client sees your packet, it will drop off the network.
Mark G: Airdrop, probably.
In general you won’t find unmodified drivers ignoring deauth or disassociate packets (and both can be used on broadcast to boot everyone), because they’ve got plenty of legitimate uses; Off the top of my head, AP congestion mitigation, true invalid authentication, and AP frequency balancing (send clients a reject/deauth on the first attempt to connect on 2.4ghz, in the hope they’ll shift up to 5ghz and try to use that instead)
You do realize that this attack is literally over 10 years old right? With published proof of concept and everything. Not that its bad to reinvent the wheel every now and then, but if you didn’t know this already then you should try google the next time you have a huge breakthrough.
I seriously cant believe that this news to anyone…
cool, but this has been a common hack since BackTrack2
Nothing new her, most routers can disable handling of deauth packets solving the problem once and for all. Alternatively triangulate the bastard doing this and file charges. In USA this is a felony. :)
@Dmitry Grinberg
That is completely false, even if you would tell a router to never send out deauthentication packets nearly all clients still respond to them, If you generate a false packet for deauthentication that appears to come from the router the client will still drop its connection.
As far as triangulation you’d need 3 points to do that, now you could track down someone doing this but the attacker would have to broadcast long enough for anyone to find him… It is a felony yes but is the average attacker going to get caught doing it? No probably not…
Sources: I’m an Offensive Security Wireless Professional
Triangulation needs 3 points, but 1 is the attacker. So 2 reasonable readings is enough.
Further it is easy enough with a set of antenna set at half wavelength apart to get direction to the attacker. The antenna would cancel each other out when aligned with attacker to give near zero signal strength. Walk a little bit across the signal line, and you would get a second directional reading that only intersects in 1 location within reasonable distances.
As far as legality, I think you hit a grey area. It isn’t really jamming the radio. You still can use the frequencies. The attack makes the use of the frequencies for WiFi pretty hard.
Now if only we had a way of making our own firmware for these radios such that we could turn the deauth command into something useful.
Not true.
You can detect deauth packets fairly easily, and there are tools out there that will let you see where it’s coming from (BSSID (AKA: MAC Address) of AP and the client). After that, it’s simply a matter of blocking all traffic to/from the BSSID who is sending these packets…
And while on most consumer grade routers, you cannot simply disable deauth packet handling, on custom built routers using PFSense, Vyatta, IPCop, Untangle etc, you can…
if a particular client is sending the deauthentication packets just to increase his download speed and if I am the one among the clients being deauthenticated. How can my device running kali linux reject the deauth. packets so that my device do not disconnect from the wifi. Is there any command to do that?
Triangulate obviously need 3 hence the tri, but a directional antenna can be used to find a transmitter, and has been for a long long time, they used it heavily in WW2 for instance.
oh and if you move a receiver around you can get several points and do the math obviously
If you’re really fancy you could spin a receiver in a circle and watch the doppler shift.
m1ndtr1p:
Sure you can detect deauth packets but you can’t prevent a client from accepting them as valid. You also can’t say “deny deauth packets from X bssid/mac” simply due to the fact that aireplay sends a deauth packet with info from the AP itself to the client. Mind you the AP doesn’t know/care about deauth packets in an attack situation. The main idea for a deauth is to make a client think the router is kicking it, and then it reconnects, usually to obtain a handshake.
Also mind you that BSSID (a Mac address….) can be easily spoofed. When doing offensive penetration testing, i roll out the 00:00:00:00:00:00 to start with (mainly to see if a target network/client has any sort of mac filtering to begin with).
Simple fact of the matter is: defense of this sort of attack is limited. You can’t “code” a driver for a wireless client to dismiss any deauth packets, If a router sends it, the client needs to respond to it, otherwise it’ll still think its connected when its not. And again, this attack doesn’t even involve the AP/router other than the fact that the client which is being attacked is connected to it.
You don’t need 3 points for simple direction finding. The Fluke network analyzer I use at work does it with only itself. Makes it very easy to track down the client sending these packets. I’ve never had deauths, but I’ve had other interfering devices I had to track down.
@m1ndtr1p: Corrosion is completely right, writing that it’s not the APs being the problem but the clients.
As for the triangulation: It’s only effective if the attacker does not move… If he does before you find him, then it’s useless. You can only determine where the attacker was when he sent the package, not where he is at the time you are searching for him. Of course, this means that using triangulation you could, in most cases, make sure that the attacker is unable to do this over a longer period of time.
Btw: the best way around this is still wired ethernet ;)
How is it a felony? You’re not receiving any data you’re not supposed to, and you’re sending transmissions that are well under power and fully within the ISM band.
@SA
You are purposely interfering with wireless communication which is a federal FCC violation.
This really never should have been posted here, a dos via deauth attacks have been happening forever and writing a bash script so you don’t have to do the work yourself is not new, nor is it a hack.
I’ve written a similar script over a year ago, its not here because i didn’t submit it because i knew it shouldn’t be here..
I’m not trying to play down somones work, you needed a solution and you created it, but it shouldn’t be on hackaday.
deauth isn’t a felony worldwide. as 2.4GHz is in the ISM band, in which you are free to do whatever you want, including denial of service as long as the transmit power complies with regulations.
its called hackaday man and this in my opinion is a hack? u mad bro?
Seriously, if you don’t know the proper meaning of “hack”, don’t use the word. “Hacking” means utilizing features of something to do a unexpected and unintended thing. “Cracking” is the act of illegally breaking into computer systems. Technically this is 100% legal, even if it might put you on a government watch list. Thats not to say that you should do it, but don’t attribute “hack” with illegal things.
Denial of service isn’t cracking.
FCC to Fine MC Dean $718K for Wi-Fi Blocking at Baltimore Conventions
how would you triangulate ? this is happening to me
Many different ways.
1) Low cost way – You just walk around measuring their signal strength until you ‘home in’ on them. This would be within the range of even just a person with an Android phone. A tool that could give you more than just binary “too far/close enough to receive” info (say, signal strength meter) or ‘cantenna’ (see Wikipedia) that at least lets you focus on a line. Just move around until you find the location with the highest signal strength. In Windows, ‘Network Stumbler’ AKA ‘Netstumbler’ is a good start if you’re wanting to try this with a laptop. I’m not familiar with using cell phones but it should be similar. In Linux, you’d use something like BackTrack 3 or newer which is a free boot CD that works even on non-Linux PC’s.
2) There are purpose-made microwave radios that have the ability to detect a specific device’s profile and are used by people along the lines of campus security or brown sleeves to find unauthorized WIFI routers. These are expensive (thousands of dollars) but work for ANY microwave source and have other related uses besides.
3) Some routers have firmware that will tell you automatically where a signal is coming from by comparing signal strength with other routers on the LAN. This approach is unfeasible if you have to ask how. It relies on mapping out the walls and entering GPS coordinates and… It essentially is overkill unless you have to do it every day. This is practical for business offices or schools or anywhere else with complex WIFI infrastructure and a security mindset, of course.
Oops, meant ‘A tool that can give more info would make this easier.’
Also, why do you think it’s on purpose? Do you actually pick up deauth packets in a tool like Wireshark/Ethereal? Could it possibly be just a microwave source? Wireless-N routers sometimes cause a lot of interference for example.
Even if the device is unattended, you can wait/use video to find out who’s doing it and tell them to cut it out, regardless of if it’s a felony. At the very least, they’re operating a jamming device and trespassing (in both the physical and biblical senses, heh).
Hi. I am completely lost when it comes to this sort of thing and was wondering if you would be interested in speaking with me outside of these website comments to help me with a similiar problem Ive had for a little over a year or more. (Wifi and NIC hack)… :(
@mark g
Your thinking of Airdrop-ng :)
In my experience, deauths sent to broadcast address are rarely effective.
Cisco wIPS has countermeasures for this. How long have WLAN Jack, Void11 been out? This is old news.
Huh?!?!? I’ve been doing this for years. How is this just now making it’s way up here?
The folks at remote exploit would really be discouraged that ‘hack’ is in the name of this site.
I’ve done something similar but there really is no need to do this, MDK3 Does it best
“If you’ve got an idea on how to protect against this type of thing, we’d love to hear about.” Sure, there’s something called “cables” and it works very well.
LMWHFGDAO!!!! Nothing can be more correct than Olivier’s response.
This isn’t so much a hack as using functionality that is a part of aircrack, and being a card carrying douchebag. Seriously, what’s the point?
Glad someone asked, but I fear the answer is simply assholes will be assholes, makes them feel ‘powerful’ and ‘real hackers’ I guess?
This “hack” is older than the internet.
In fact, this is more like a script kiddie who just found out how deauthentication works.
Oh and btw, mdk3 has much niftier DoS capabilities:
a – Authentication DoS mode
Sends authentication frames to all APs found in range.
d – Deauthentication / Disassociation Amok Mode
Kicks everybody found from AP
m – Michael shutdown exploitation (TKIP)
Cancels all traffic continuously
The simple answer on how to protect yourself from this:
the 802.11w standard.
Encrypted management frames == no spoofing and no disrupting without knowing the key.
See:
http://en.wikipedia.org/wiki/IEEE_802.11w-2009
Support for this is in the ath9k wireless module, so OpenWRT fans with an Atheros chip driven router, activate it… But be prepared that on client side, you need 802.11w support too, so better have a compatible chipset on that side too!
easy way around that is to change the software to stay authenticated and never expire the authentication.
also there would be a better way to jam it is to build a radio transmitter to sweep the 1 to 5 ghz range basically jamming cell phones and everything and maybe even crashing unshielded computers by interfering with logic clock signal to the cpu
I’m assuming you have limited idea how RF works. Firstly, a “jammer” is essentially a high powered rf noise amplifier. to effectively jam signals of anything in 1-5ghz range within a half mile you’d need to be broadcasting at minimum 15watts. Secondly, if you just wanted to jam wifi, just do it in 2.4 and 5.8ghz range, no need to add extra frequencies. 3rd. even TRY to start up something that powerful in the US or any civilized country and you will have the FCC up your ass and in cuffs with fines your children won’t be able to pay for. 4th, um, you’re not going to interfere with computer logic gates with a 1-5ghz noise amplifier….
5th. Go get a 1000watt 2.45ghz and stand right next to it, have fun :)
I Stand next to my microwave often. No trouble so far. But yep, it MIGHT just be the shielding…
“you’re not going to interfere with computer logic gates with a 1-5ghz noise amplifier….”
I can confirm that a UHF transmitter of 25 watts with the antenna within about 50′ can cause some computers to screw up (constantly reboot at the BIOS POST)
The closer to the computer’s clock frequency the transmitter is, the more easily it will do this (I saw this effect for a 470 Mhz xmtr on a 500 Mhz computer, had less effect when I lowered the xmtr frequency to ~ 430.Mhz) The RF seems to get in to the motherboard via cables acting as antennas (mouse, keyboard mostly it seems)
Made a wired ethernet router go crazy as I recall too..
“From what we can tell it’s a new way to use an old tool.”
What?? I’ve been doing this since the early existence of aircrack. For those folks saying this doesn’t work, bad news – it does. And windows is pretty slow figuring out it was disconnected and then reconnecting again, those only need to be flooded a couple of times each 10 seconds.
GPS + wifi = longitude and latitude of DOS machine
Then a sledge hammer work quite well as a solution.
Would be awesome if it was that easy.
Cameras combined with an array of routers with the right firmware and a common hardwire backbone makes it very easy to detect who did it and have a little office/classroom visit. Still, it’s hard to find them if it’s intermittent. Nothing stops this kind of foolery like embarrassment. If that doesn’t work, there’s always the more physical methods like kicking them out. ;)
Agreed, that ‘GPS+wifi’ is a misuse of terms. It’s not like you don’t already know where your own router/s is/are and the jammer sure isn’t going to give you their GPS coordinates!
Actually, using a Yagi antenna and aircrack-ng, you can easily pinpoint the direction a wifi signal is coming from. Do this from a couple of different positions (aka triangulation), and you’ll get a pretty good idea of the location.
this and a wifi pineapple could be interesting
jasager on the hak forums, http://forums.hak5.org/index.php?showforum=49
deauth detection, http://hak5.org/episodes/episode-706
dont broadcast the ap name
no name no target
Wrong! When you associate a AP with a cloacked ESSID, your client has to send the ESSID. That means you will uncloak the ESSID.
Geezz, where did all of these wifi “experts” came from?
You probably think that MAC filtering works, as well… :/
@wethecom these tools work using the BSSID not SSID name, so not broadcasting does nothing. Linux tools like Kismet see hidden AP names by gathering the name from packets. I have been preaching for years that businesses stop using WIFI all together for this and many reasons. I even ran a demo for one business that had printers shared to the world. But as long as people remain ignorant and un-educated this type of script kiddie attacking will continue.
thanks-derp
1. Deauth flooding works, it was demonstrated at BH2001.
2. It spoofs the AP’s mac address, can’t track it by mac.
3. It doesn’t need to over power the AP’s radio signal.
4. A deauth is a management FRAME NOT a PACKET!
5. There is a way to identify spoofed frames but not block them.
6 Triangulation of low power spread spectrum isn’t easy.
#6 is the killer… If someone only jams for a short while/from multiple locations, it’s VERY hard to narrow the suspect down. Of course, like in my previous comment, if someone is stupid enough to do it near cameras and you have multiple routers, then it makes it a lot easier.
Strange, I tried something similar on my router. I found if i didn’t specify the clients mac, the the deauth wouldn’t work. If I did specify the -c command (i think that was it) then it would deauth. So all i did was set my router to only except a wirelesses connection form a certain mac and poof couldn’t death. But its super easy to use the macchanger tool in BackTrack so its useless exept for super script kiddies lol.
this is actually baked into cisco wireless controllers…you can send the deauth packet to either a client or an ap by designating it as a rogue. I assume the same with other brands
Mikrotik (Wireless Manufacturer used by many Wireless ISP’s) deals with this by using a PSK to encrypt and validate management frames. It’s a proprietary feature, which is the big disappointment, but it works awesome on point-to-point and point-to-multipoint links.
I haven’t had a chance to look yet, but I would interested to see how “secure” their management encryption actually is. For all I know a couple XOR’s later and they could still be vulnerable. Either way, it’s a neat idea.
Run cable like I have. That way you have no WiFi to attack.
Look into IEEE 802.11w. This is a standard for management frame protection, the deauth frames (and others) are then also signed. Often used on not so critical control networks but where some jamming resistance is wanted (you can always just jam the rf signal, but most scriptkiddies can’t).
You could mod the linux mac80211 to ignore deauth and disassoc, but then normal coordinated handovers in large wlan instalations would also stop working.
Another way to jam wifi is spamming RTS frames telling every node to be silent for some time, if you can hack the cards firmware you can specify 0xFFFF as duration, which is somewhere around 32s if I remember correctly. This cannot be patched in software and requires hacking the card, but so does running the attack (one could send RTS frames using the cards short calculated duration, and it works if you do it fast enough, but then you don’t have the magic ‘one packet’ Dos.). This jams the entire channel btw, the RTS packets have no source.
You could also, on WPA networks, inject fake EAPOL frames causing the authentication to fail every time. You can try disconnection already authenticated cllients by sending an EAPOL logoff frame, but most clients and soms AP’s ignore them, so you might start with deauth and then fake eapol. The fancy thing about this is that you can make the authentication look succesful to the client and ap, they just calculated another key so communication will not work, but it takes most clients 20 seconds trying dhcp to figure that out.
Wifi Jamming via a DOS attack… not new.
Why did you guys write this? This has been part of aircrack tools for few years!
Use directional antennas at client side.
Triangulate the jammer and surround him with low power narrow band jammers. Choke him in noise so that he can’t verify the results easily. Consider upgrading to hardware with encrypted packets.
I did this as a joke to annoy my flatmate 10 years ago!
How about with this new moderation system we can block the troll articles as well as the troll comments?
… or a scoring system for the articles. like/dislike or something.
Don’t yell at me if I’m wrong, but couldn’t you just send the same deauthenticate packets/frame whatever back to the original person sending them and disable them the same way?
@jesse
No, unfortunately because the attacker is not associated with any access point when performing an attack, so you cant kick him off a network if hes not connected to one.
Sadly there is no way to block such an attack yet, in fact the IEEE when they created the 802.11N Standards they decided that a deauthentication attack wasn’t a big enough security issue to patch.
-Corrosion:Offensive Security Wireless Professional
Okay, now to port it to Android…
bananas
woah, people still use Azureus/Vuze?
An update on this topic. The WFA (Wi-Fi Alliance) is progressing on a new spec called PMF (Protected Management Frames). The certification program began Jan 26, 2012 and will become mandatory for WAP2 (EAP/PSK) after 18 months. The scope of the PFM certification is to increase the security by providing data confidentiality of management frames, mechanisms that enable data integrity, data origin authenticity, and replay protection.
Yup
http://www.cisco.com/en/US/tech/tk722/tk809/technologies_configuration_example09186a008080dc8c.shtml
Any ideas why the client is receiving tha packets but the AP doesnt? My output looks like “……[53] 0 ACKs”, http://www.aircrack-ng.org/doku.php?id=deauthentication says the second number is the number of packets the AP receives, but mine is always 0. Any way to solve or it will still jam the connection even if it shows 0?
40% of comments are like “I already knew it [time] ago” and “I can do it but you are a script kiddie for not having noticed this before” etc…nothing is going to happen other than your ego getting bigger and annoying people with such useless comments. This had to be said.
mirror auth packet
deauth == NOP::{duration}FFFFD000
bulshit syntax but im sure someone can do it better
to easy right?
DE:AD:BE:EF
Can anyone direct me at somewhere I can find an example of a deauth frame? or the exact process to capture one on WireShark. I have been using WS with the wlan.fc.type_subtype==12 filter and have not captured any even though the capture is on promiscuous mode, I can see other wireless traffic and I am using aircrack in my tablet ( wireshark is running in my laptop), still, no love. I need to see the exact composition of a deauth frame.
how exactly does a deauth packet look like? because i want to write my own deauth attacking program in c?
This is a very good reason why you should restart your networking hardware when your WiFi drops out. To put it simply, this kind of attack should time out while the AP restarts, unless some other customized options were used in the attack. Some idiots will deauth all day just to anoy someone.