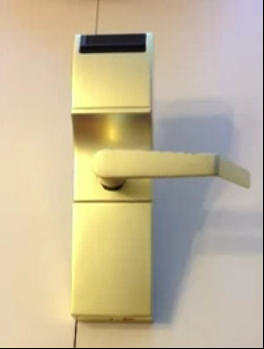
Can anyone argue against this being the least-secure hotel room lock on the market? Regular readers will recognize it as an Onity key card lock. A few months back a glaring flaw in the security was exposed that allows these locks to be opened electronically in less than a second. So we are not surprised to hear that a series of hotel room robberies in Houston are suspected to have been performed using this technique.
The image above is from a demonstration video we saw back in October. That hack used an Arduino-compatible chip inside of a dry erase marker as an end-run around the lock’s electronics. It reinforced the warning sound by [Cody Brocious] when he presented the exploit at this year’s Blackhat conference. The barrel jack on the outside of the door lock doubles as a 1-wire communications port and that is how an attacker can gain access. Investigators can find no other means of entry for these thefts.
We applaud one of the victims in this story. At the end of the article she is asked if the information about the Onity flaw should have been kept secret. She said that if there’s a vulnerability that’s not being fixed people have a right to know about it. Bravo [Janet Wolf]!
[Thanks Andrew]















Like the traffic light story, this just reinforces my belief that HaD needs to be more careful about the information they disseminate. Obviously, like Janet said, it’s important for the exploit to be known to the general public so they can protect themselves. But you guys took it a step further and linked to an article that not only explained exactly how the exploit worked, but also how to disguise a device to take advantage of it!
I disagree with your statement completely this was disclosed at blackhat a public security conference. As well as the presenter provided a full white paper online . HaD has provided no information beyond what is already out there. This was brought to public attention two months before HaD posted an article about it.
It is the company’s fault because it didn’t make a recall of hardware for amendment. Mind you that the company here sells security devices! A security breach in such devices is not a simple minor fault, it rather makes the entire hardware useless!
Furthermore if you read more about the story, you will know that the company even tried to charge their CUSTOMERS for amendments in the hardware.
Companies like this one should not be protected.. They deserve to suffer the consequences and let more competent companies take their cake.
EDIT: The company Onity did not charge their costumer (hotel) for the update charges, they wanted the HOTEL CUSTOMERS to pay!!! This is absurd at best.
It doesn’t matter whether the company deserved it or not. This exploit doesn’t harm the company, it harms the people who had their belongings stolen. It’s not their fault that the manufacturer won’t replace the locks.
Even when it was disclosed the company did nothing. Like the security researcher said it was so simple it has probably been used for years. If it was kept in the dark it is guaranteed that that the company and hotels would turn a blind eye to it.
Read my other post below. I’m not saying the exploit shouldn’t have been released. I’m saying that HaD shouldn’t have linked to an article that demonstrated how to effectively conceal a device to take advantage of it.
Would it have been okay for HaD to link to an article that shows how to conceal an Arduino or any AVR or PIC in a dry erase marker to, for example, make a smart whiteboard? Because the hack would have been morally equivalent — how to put a chip and supporting infrastructure into a marker.
Is it morally wrong to point out that a glass beer or soda bottle oil lantern isn’t significantly different from a molotov cocktail?
David your still wrong.
“not talking about it” does not make anything anymore secure
all the information was available to the criminals already.
HAD just helped making everybody else aware of it too
@lamer: Read my other posts and stop twisting my words. I said that it’s perfectly OK to talk about the exploit. It’s not OK to demonstrate how to conceal a functional device in a way that isn’t useful for anything but malicious purposes.
I think that without knowing the existence of the exploit and the easy of it it would be hard to convince the general public that this was the case here (and I mind you – it perhaps is not true even now!).
If the exploit is so easy as it is claimed then these locks should be replaced imidiatelly.
The assumption to being made here seems pretty pesimistic. The asumption that HAD posting a link some how directly influenced these crimes. I am not condoning nor objecting to the practice of posting “how to” security breaches. But the argument seems to be about are they morally responcible. It is possible that the person commiting these crimes has never heard of HAD but simpliy frequents Black-Hat write-ups. It is also possible that they used a completely different method of disguising the one-wire device.
If the criminal is caught, and he states “i got the idea from HAD” i would be willing to entertain this sort of discussion. If the discussion is with regard to black-hat, i agree to some degree they may be to blame. But I believe that this should be in the news, and disclamers made to some extent by the hotel staff. I realize that this is a huge design flaw, and one that i feel the hotels are the victim, but it is really the duty of sites like this to report how easy and how discrete a breakin could be. Now you are aware, ASSUME YOUR HOTEL ROOM IS INSECURE, take the necessary steps to protect yourself.
I could not agree more!
Stuff like this should be disclosed or it won’t be fixed ever. So do-it-yourself-instructions seem like a good idea to me to increase pressure. :-)
Like I said, talking about the exploit is fine. Even a schematic would have been OK. But demonstrating how to conceal the device itself is crossing a line. It’s equivalent to providing sample code for a software exploit, but also explaining how to inject it into a process and execute it under an AV application’s nose. The first part is instructive. The second part is malicious.
Ah… I see your point now.
But do you really think that the last video was the deciding factor for the thieves? Do you really think that just because there is no sourcecode samples for a hack, that it then wont be exploited?
I’m not that naive. I just think that by posting the link, Hack a Day made it easier for someone with malicious intent to find the information. Posting source code for a hack is fine. The part I have a problem with is coupling that information with methods for concealing and carrying out the hack.
What’s the point of posting source-code if you don’t explain how it’s used? In order for the code to be a story it needs context. The original author had contacted the manufacturer and publicized the security flaw. The company/hotels had a chance to fix it and didn’t. I could understand your position if the HaD article were the first notification anyone had of it but this exploit was far from a 0-day.
If the reader is savvy enough to program an mcu is it really that outlandish to think that they wouldn’t think to house it in a marker? There’s really no need to ‘hide’ it in a marker body anyways. The assembly isn’t that big to begin with and it doesn’t take that long to implement so the only time it’s actually hidden is when you aren’t using it. when was the last time you saw someone sticking a marker in a lock and thought: “oh, that looks normal”.
Yeah, I’m pretty sure the hard part for the people commited to build the device is to think of a way to disguise a small chip and few bit of wiring…
Let think…
aircraft carrier: no need seawater
battleship: see aircraft carrier
fridge: not enough wheels to move easily
18 wheeler: need special driving license + cost of fuel too high
dry erase marker: YES THANK YOU HAD NOBODY WOULD HAVE THOUGHT ABOOT THIS. Only guns gets masqueraded as pens usually. THANK YOU AGAIN.
You are a Don Quichotte, fighting a useless battle against made up enemy. aka empty outrage.
And is there any proof that they did use a pen at all? the Arduino could easily be hidden in your pocket and you’ll just use a long cord. I don’t really see any reason to disguise it at all, if there’s no guests or staff in the hallway then you could even use a laptop, it’s not like the Arduino is the only way to hack the locks.
I can’t fault them for it. It A. demonstrated for the layperson that this was NOT something that would be easily noticed because the thief was carrying a an armful of wires, and B. was a fairly obvious step for anyone wanting to use this for malicious purposes.
Personally, I’d’ve put the brains on an armband and run the wires down a jacket sleeve. Tape the barrrel connector to my finger, or mount it in the tip of a glove finger. From the outside, it looks like I’m carrying NOTHING AT ALL. Anyone that needed illustrated instructions on how to put it in a dry-erase marker was NOT pushed over the edge to crime by Hackaday.
No, HaD handled exactly the way they should have. Who is to say that knowing such information would prompt another hacker to create a cheap and viable fix?
If you want to hack and you want the knowledge, you need to take the bad with the good. That’s not just in hacking but in everything. We’re slowly screwing ourselves because we expend so much effort with filtering the bad that the good becomes impractical.
I saw this story repeated on several news networks already. If the original hack was kept a secret and this dweeb never burglarized the rooms would Onity be getting any negative attention now?
Even if HaD didn’t link to the exploit it wouldn’t mean the exploit wasn’t out there and could still be found through other websites.
Your stance is absurdly puritanical and misinformed. By disseminating this information HaD was making a rare display of good journalism. There are numerous examples of other researchers is a range of fields publishing research that illuminates a vulnerability of a system which puts people or property at risk. In most of those cases the research was reported on by real news outlets who presumably felt they had an obligation as journalists to report on the story.
Security through obscurity is not security at all.
David. It’s perfectly right and proper that all the ways that a vulnerability may be exploited should be known as widely as possible. In this case, the information that would allow someone to rob the hotel rooms in as sophisticated and stealthy way is exactly the information which should be known by as many people as possible. Security will always involve an arms-race and the advantage is always with those having with the better information.
s/as sophisticated/a sophisticated/
s/having with the better information/having the better information/
wtf is wrong with me?
HaD posting it or not would have had exactly NO effect.
Do you not think that at least ONE criminal who can understand the gist of this hack, is capable of using Google?
If HaD did not link to the article as you suggest, instead of two clicks, it would have instead been a select-text, right-click, click, click.
Implying that is better security for the hotel guests is simply fooling yourself at best, and stupidity at worst.
What was the traffic light story?
The company put their bets on security by obscurity and lost.
Yet Onity still won’t pay for fixes or replacements for their faulty hardware.
Anyone else smell a lawsuit?
What faulty hardware? There is always a better and more secure way to do things… There locks do exactly as they are intended to to. Back when the model was designed the public usage and knowledge of mcu’s was likely not a fraction of what it is now, and this being done probably wasn’t even a thought… For how long many of those locks have been around, the internet might not have even been around to widespread the info, even if someone figured it out, let alone easy to learn and program mcu’s that the common thief would be able to do it with. If you have the time, you can reverse engineer and crack most anything electronic, look at blue-ray encryption. There was no small complication there, should there be a lawsuit over that being crackable? You can always build a better / more complicated / more expensive mousetrap, and these locks are what they are. I don’t fault the lock mfg in the least, there design wasn’t out of the question for when/what they were designed for.
All they need some BIG NAME hotel chain to step up to the lawsuit homeplate and start the game. Onity will be fixing/changing their easy to bypass locks or be leaving town.
So I find it amusing that there was an ad at the top for a site that sells locks, including locks from Onity.
Locks only keep honest people honest. The same kind of information on how to pick a padlock or any of the common house locks is also all over the web. More info is better, it lest smart people asses the situation and make there own risk assesment.
I thought the fix was just to put some glue in the barrel jack? Couldnt be easier?
That barrel jack is there for a reason.
I suppose that anyone staying in a room could choose to vandalize the jack, if that was what they want to do. Their decision.
I don’t feel it is up to HaD to try to police the hacking information already released publicly.
It was my understanding that the “fix” was a little metal shim they could install that would essentially cover the hole. I didn’t read whether or not it was supposed to be glued into place or screwed.
That is their free fix. It uses torx screws.
Honestly this hack is one of the most convoluted ways to get into a hotel room with Onity locks. I know of two other, faster nondestructive ways to open a door like this. There is three more that I am aware of in theory. The obvious way, a clever way with a bit of wire, another one with a smaller bit of wire, one that requires math but no electronics, and the last is just some wetware business.
What is a Dell employee doing with a Toshiba laptop, one wonders to onesself.
Thumbs.
cheap and viable fix.
fill barrel jack with 5 min epoxy putty when checking in
haha
Thanks HaD for the original exploit post, and this showing of it being abused.
If this exploit wasn’t known very well, how could the cops even suspect this method?
Ergo, information is not the problem. Onity should be sued.
In terms of the victimized hotel customers, this isn’t Onity’s problem. Hotels need to step up and shell out the money for new locks to replace the old ones. These locks do the job they’re intended to do, but there will always be exploits, regardless of the technology. If these locks are found to be outdated and exploitable, it’s the hotels job to protect their customer’s security. They are the ones who chose and purchased the locks, and the locks apparently passed the hotel’s quality control standard. Now, the hotels might have some beef with Onity. I could see hotel customer’s suing the hotel, and the hotel’s *maybe* suing Onity.
This was never a flaw. It was a feature that was designed in from the beginning. Why else have a communications channel that is outside the housing… anyone authorized to work on the lock would be able to open the lock and get at anything inside already.
Hotel room lock? They use these for machine shop and housing access at my University o.0
I’ve notified some hotels about this security flaw in their locks. The managers had no knowledge of the problem. Onity is not informing their customers (the hotels) about this problem.
In august, I went to a hotel in Nampa, ID that still uses KEYS. Yup, ye olde hunks of metal. It’s not some fleabag hotel either, it’s a large one in one of the major national hotel chains. It’s so far behind the times the in room TVs are still 19″ CRT models.
I was once locked out of a room with a similar lock. The hotel maintenance guy got me in with a simple gadget made from a coathanger and a piece of twine. The hangar was slipped under the door. It was bent to loop over the the handle on the inside. The twine was tied to the loop. He slid it under the door, rotated it up to engage the handle, then pulled on the twine to turn it. Took about ten seconds and I was in.
No electronics or technical knowledge required, just a chunk of wire bent in three places and a piece of heavy string.
The construction of the lock isn’t that odd, the odd part is why the locks weren’t given individual passwords for each site (hotel) so that one had to send a 10 digit number (changeable through the same tool) to access the lock.
This is a fix that should still be possible to apply too, you need to reprogram the locks mcu unless it’s a cheap single programmable model.
blah blah blah
the only reason why you all say its bad to tell the world of it’s own flaws, is because you only contemplate the wrong thing to do, or even the right thing to do.
why not do the fun thing ???
open all the doors at 2am and NOT steal anything.
it’d be pretty hard to get caught, i mean there would be no stolen items on your person
do this to a new hotel every night till the hotels all get a M. F.ing refund for what they paid. because the update port is on the outside. afterall, if the manager wants to service the door he can do it from the inside using his master key, no?
this is akin to having a deadbolt installed backwards, key on inside but handle on outside.
this is the hotel’s fault. Firstly, their quality assurance should’ve prevented these locks from being purchased. They should also keep their ear to the ground to hear about news such as that revealed at the black hat conference. When they found out about this issue, they should’ve immediately replaced the locks and possibly sued Onity.
It’d be poetic justice if Onity execs have their hotel rooms burglarised due to this flaw.
It’s bad practice from Onity, but ultimately it’s the hotel’s fault. Firstly, their quality assurance should’ve prevented these locks from being purchased. They should also keep their ear to the ground to hear about news such as that revealed at the black hat conference. When they found out about this issue, they should’ve immediately replaced the locks and possibly sued Onity.
It’d be poetic justice if Onity execs have their hotel rooms burglarised due to this flaw.
I may have one of these, but only the card-reader side (they replaced the locks at the hotel I was staying at, and just threw the one from the outside door on the ground amongst the shrubbery, that wouldn’t be stealing if I were to pick it up, right?)
Anything fun I can do with it with just a Windows PC and basic electronics stuff? (Like, I can make a connector to attach to the pins inside it, if USB can talk to it, and I have a breadboard and resistors and caps, but no Arduino.) Also it’s powered by 4 AA alkaline batteries, and they are IN THERE, it’d be a chore to replace them, but I guess that’s when you just replace the entire thing with the modern RFID lock.