The last few weeks have been quite tense for the Mooltipass team as we were impatiently waiting for our smart cards, cases and front panels to come back from production. Today we received a package from China, so we knew it was the hour of truth. Follow us after the break if you have a good internet connection and want to see more pictures of the final product…
We never mentioned this on Hackaday before, but we actually produced two different versions of Olivier’s case: a slim one and a thick one. The slim one isn’t Arduino compatible and is only intended for our dear contributors as it is made of aluminium and therefore very costly :
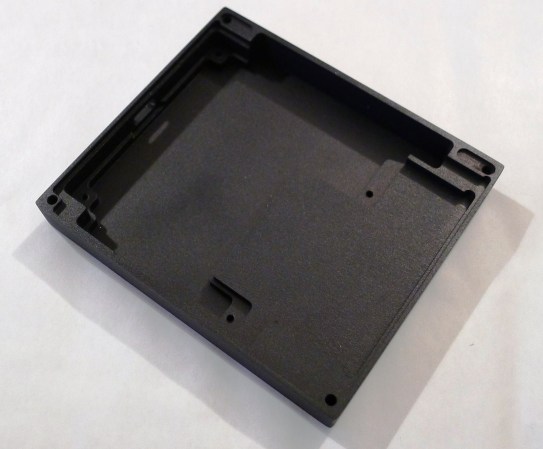
The thick Arduino-compatible case is only 1.9mm thicker (13.9mm instead of 12mm) and is made of black ABS. You can notice the connector grooves :
As you may have guessed all the prototypes were CNC machined and then anodized or painted. We’ll obviously go for injection molded cases for bigger quantities, which will be one of our main challenges in the coming months…
It was quite a relief when we saw that our PCBs could tightly fit inside the cases, especially given that several of them were produced and shipped to our contributors around the world :
In our last developed on Hackaday series article we stated that we had decided to switch our transparent front panel for a tinted one. The new one we just received perfectly fits on top of our assembled prototype and give it a clean professional look when the screen is off :
Rest assured that our capacitive touch interface performs remarkably well even with this 1mm thick acrylic panel on top of it. We’re using a 0.11mm thick double-sided tape between our top PCB and our panel to maintain good contact.
Finally, we also received the smart cards that our dear Hackaday reader selected. Unfortunately they were printed in the wrong direction, leaving the wrong part sticking out of the Mooltipass.
So what’s next for the Mooltipass project?
Now that we know that our hardware is final we are going to select beta testers and have a small Mooltipass production run shipped to them. In the meantime our contributors will be hard at work and hopefully in a few months we may start our crowdfunding campaign!
Want to stay informed? You can join the official Mooltipass Google Group or follow us on Hackaday Projects.





















How can I become a beta tester?
the call for beta tester is over… but we might do a second one. Stay tuned ;)
Is it possible to pay and get mooltipas prototype whitout becoming a beta tester?
of course!
It will be a bit expensive though, as we’ll make a small batch.
You may contact me at mathieu (at) hackaday…
Please make a large batch so everyone can enjoy one at a reasonable cost :)
this is why we may launch a crowdfunding campaign ;)
Strange that after all this now, Digg is promoting http://gizmodo.com/the-fifth-element-is-starting-to-come-true-1586278002
What the heck is up with 5th Element lately?
ahaha :D
Nice!
How do I know if I was selected as a beta tester. I filled in the form and joined the Google group…
Either way good to see solid progress.
we’ll notify the selected persons in less than 1 (2?) weeks :)
Am I the only one who doesn’t understand what the heck this thing does, lol?
It sits on your desk and invites people to come over and ask “what does that do” like all good new tech.
Phew.. glad I wasn’t the only one and that you asked first :). I can’t figure out what problem it actually solves either, even after reading the very terse blurb on the site and looking through it for a FAQ. As far as I can figure it, isn’t this thing just doing in hardware what the Firefox ‘Remember Password’ function does?
I’m left wondering how are the enthusiasts / originators of this project going to convince me I need one (hey! maybe I do, I don’t know!) and why I should then throw some money at them? Whatever it is, it shur looks purty, I’ll give it that.
Perhaps you should give the first developed on hackaday series post a read then :)
http://hackaday.com/2013/12/06/developed-on-hackaday-lets-build-some-hardware/
Thanks Mathhieu but I still don’t get it, Do I plug my USB keyboard into it and then into the computer, and it sends keystrokes? Do I just plug it in and install a custom USB driver? Is it a standalone device like those RSA keyfobs? Does it supplant a repository like KeePass? Does it generate random passwords on that screen or do I copy passwords to it? Frankly, NONE of these questions are answered by that link. I gleaned more about the project from the comments than the content. These are my simple questions – maybe dumb to you – but how about an FAQ for starters please.
Oh, and :)
The Mooltipass is a driverless-device that is detected as a keyboard.
It indeed stores all the password you may have, encrypted inside the device. It generates random passwords.
The FAQ is at github.com/limpkin/mooltipass , I’ll update it with your questions ;).
is the data encrypted before transmission over USB? seems that without this, sniffing any passkeys is ridiculously easy on the PC side.
Eh?
You mean like how the data coming from your keyboard is encrypted?
There are applications which allow for the encryption of keyboard data, and a keyboard’s primary use isn’t as a security device.
given this device exists ONLY as a security device, to story and input passwords, it seems that even the slightest consideration for this otherwise gaping security hole would be prudent.
Hey guys,
Encrypting the data would only make sense if it is encrypted between the mooltipass and the website, which would involve making partnerships directly with them (all of them…)
Therefore, the Mooltipass only reduces the number of attack vectors.
No. Your browser sends the passwords to the websites in encrypted form. You wouldn’t have to partner with websites, you’d just have to write browser plugins. But that’d take oh so precious development time away from designing graphics and LED accents. It isnt surprising to see that you considered appearance to be of greater importance than function.
this encryption is performed at the HTTPS level, and if anything recent news told us is that this is not as secure as it used to be…
And if you’re so concerned that we’re not spending enough time on the encryption side of things… why not contribute?
So the front of that is some kind of tinted glass, right? And you stenciled black on the back? What company did you find to do this?
I actually don’t know!
I contacted dozens of companies throughout the world and when I innocently asked my usual part sourcing chinese guy he informed me he knew some company that could do so.
I just had to give him the DXF files and let him negociate…
What license are you using for it? And movement on getting it onto GPL?
I admire your persistence :)
It’s still in the talks…
Cool
SEXY !!! Great work guys , really enjoying watching this one.
thanks!
for a security product this sure does have a look a look at me feel when the lights are on. Maybe be a little more discreet?
So,why would I want this over LastPass?
What does it do that makes it a better choice?
Lastpass is purely SW based… so hypothetically at a given moment there’s your main pass phrase in memory + your encrypted passwords. One attacker could then get all your passwords at once
Wow, just wow. So with this glorified HID device, all the passwords you store on it are going to be in memory too. And because it is a HID device, it makes it a fucking joke to capture them, compared to having figure out the offset that Lastpass uses to store a password. It is trivial to log HID devices, there are countless programs to do so. I know this for a fact since i’ve written userland and kernel based key stroke loggers on OS X and Windows.
So I guess you never use your keyboard to enter your passwords then :).
” figure out the offset that Lastpass uses to store a password.” >> this is actually fairly easy
Where this is an important milestone for those working on the project; congratulations. Because I can’t see this as something I’ll be able to use I hadn’t followed the project beyond reading the article proved here. Why? using the card would require public access or any other computers to have the reader. Here in Kansas public access computers are few and far in between. Our small library has four, there nearest others is 15 miles away. Perhaps if the wireless was eliminated, this could be shrunk key ring fob size USB pluggable PortableApps like device that could be used with any Windows compute. Windows because any public access computer is likely to be running Windows. The congradulations/ congratulation thing was tripping me up so I used Google
and seen this;
http://youtu.be/wDajqW561KM
Thanks!
In this case you’d have to carry your mooltipass around then ;).
Ever since you launched the project I’ve had the feeling of deja vu. Then I realized that you’re basically creating your own Common Access Card and everything fell into place.
Two questions:
1. Where are you getting your smart cards?
2. My Thinkpad has a smart card reader in it. Is there any way to use the reader software without the hardware reader?
1) from suppliers mainly located in China
2) It depends on your thinkpad model. However I’m not sure what’d be the advantage in doing so, as you skip the whole “keep everything off the computer” point.
2) Ah. I missed that. I thought you were writing the passwords to the card. If you were, then removing the card takes care of that concern. But you aren’t, so nevermind.
I wonder, can this only enter passwords on websites?
Or is it able to enter passwords inside a program/game too?
we’re aiming for both :)
excellent.
I’ll order one as soon as it’s finished.
thanks!
What about storing crypto keys vs passwords, will there be a limitation on password length or characters ?
nope! you can store all kind of data you want ;)
Congratulations!