In order to help his friend prepare for a talk at DEFCON this weekend, [Craig] built an IR photodiode amplifier circuit. The circuit extended the detection range of the hack from a few inches to a few feet. We’re suckers for some well-designed analog circuitry, and if you are too, be sure to check out the video embedded below.
The talk concerns fingerprinting cellphones by the IR emissions that their proximity sensors emit. These sensors are there to tell the phone whether the phone is being held up to your ear, for instance. Of course, if the IR emitter in the proximity sensor were running all the time, it would be a battery drain, so the manufacturers turn them on only intermittently. If different manufacturers use different patterns, you can fingerprint the phones — if you can detect the IR from a long enough distance to be useful.
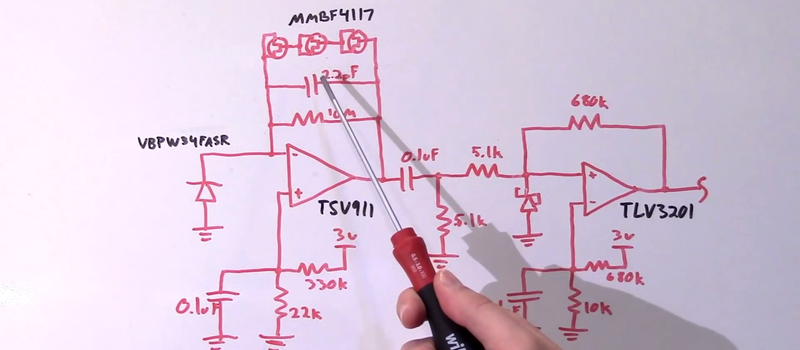
And that brings us to IR photodetector amplifiers. The circuit is “almost” a simple op-amp current-to-voltage (transimpedance) amplifier. But there are complications. To get very high gain, the circuit becomes prone to oscillating due to the inherent capacitance of the photodiode, so there’s a damping capacitor in the feedback loop. To avoid slamming rail to rail, [Craig] biases the positive input and adds some diodes in the feedback loop to reduce the output range. Since the output is going into a microcontroller, it’s run through a comparator to make it nice and digital. Finally, [Craig] used a nice big photodiode with good sensitivity.
We wonder why [Craig] spent so much effort keeping the first-stage op-amp out of saturation when he’s following it with a comparator anyway. Anyone?
Anyway, being able to detect IR pulses from far away is cool. And did you know that you can use photodiodes to detect (beta and gamma) radiation? The same caveats about oscillation and signal conditioning apply!















Why avoid saturation, even if a comparator follows? One word: speed. A saturated op amp will be slew rate limited for recovery.
+1
just for more information: http://www.analog.com/library/analogdialogue/archives/37-04/comparator.html
Why speed ? It’s 750Hz !
‘Speed’ refers to rise and fall times; not period.
With a cheap eBay fresnel lens, this could became a nice frontend for an anti-IR-speed-trap early warning system.
The problem with IR warning systems is that by the time you detect the light, they’ve gotten a read on your speed. They don’t spread as wide or range as far as the old radar systems, they usually aim a laser at your license plate and use the retroreflective plate bounce the light back at them. At least, that’s how they do it here, the technique is probably different for provinces/states that don’t require front plates.
@Jeff clan y ou provide a link to more thorough documentation/détails on this ?
I don’t think he can right now.
[Jeff] was pulled over for speeding and is currently explaining to the officer that his speedometer must be wrong.
If you don’t believe Wikipedia than take this link from a cop forum.
http://forums.officer.com/t102024/
Well, without reflective license plate, the device may be taking the peak speed of all reflections, its not entirely impossible that the next sizable fast reflection came from the top of the wheel cover (going about 180% of the car’s speed… that probability would be rather low IMHO, but theres always bayesian statistics, so those who know of themselves they were speeding simply don’t go to cop forums to find out about possible misreadings…
anyway, good luck trying to explain bayesian statistics to the police…
another possible reading could have been specular (mirror like) reflection from the targeted car, towards a retroreflective traffic sign on same side of the road, or retroreflective license plate of a car on opposite lane to give the reading of 2X target car speed in first case, or 2X target car speed + 1X car in opposite lane in second case…
I get it, but i don’t get it.
Does this do anything other than tell you what you could figure out from photos or walking past the target when they have their phone out?
Sure it’s useful to know what phone they’re using, but this method seems convoluted. I guess I’ll have to watch the talk when it’s released.
Leithoa – It’s like I said before, these HaD folks (I mean US too now :-) ) are like a citizen DARPA. Evidently this [Tim Quester] below stumbled on something amazing about our cellphones and tablets. The first half of the first paragraph of the abstract below would interest you as your posting would suggest.
Source: http://defcon-wireless-village.com/speakers.htm (from [Craig] above)
Sorry I dropped the L from .HTML – link was supposed o be http://defcon-wireless-village.com/speakers.html
Leithoa – This exploit can be compared with putting an IR beacon on the target’s car and tracking him with an IR camera (i.e. loose tail?). If you know the IR pattern other makes and models emit, you could compare it with other IR beacons in a hypothetical room and figure out where your target is among a crowd of other IR beacons. [Craig] is suggesting putting the detector on a sniper scope and pointing it around the room to track your target. To block the exploit simply turn the face of your phone around in the hip holster so that your camera is pointing outward. This way the IR array is emitting toward your hip rather than outward toward the room.
@tb69rr actually ran the project! I just helped with some of the firmware and presentation. Was a ton of fun to work with him! (And thanks for the article HaD!)
Like I said before, I get what it’s doing, I still don’t see how this is terribly useful.
This simple ‘tracking device’ can be foiled by putting your phone in your pocket instead of using a fanny pack of the 00’s.
Unless you’re using the proxy sensor to tx/rx data all you’ve done is narrow down what can plainly be seen by the people tasked with following the suspect. Even if you can tell that they’re using some 3rd party app to control the screen brightness, except for rare cases this doesn’t give you any actionable information.
Sure maybe if they’ve got trade/state secrets on the phone & you want to track a specific device or ID it in a pile of evidence, but every other case still requires a surveillance team to be within LOS of the person you’re following anyways.
I agree with you 100%. However, this idea is kinda’ cool as it means you don’t have to place any electronic asset equipment (i.e. a bug) on the target. You just need to know his IR profile. When you enter a large convention center during a loose tail, your little gadget can pick him out of the crowd. Your team approach might spook the suspect as they kinda’ stick out like sore thumbs at events like this (i.e. crew cuts, no visible ink, no piercings or no ear lobe enhancements, Motorola ear-pieces, Oakleys (indoors), etc.). And yes putting the phone in his pocket defeats it – if it is not facing outward as IR could penetrate thin clothing. But most people like hip-belt holsters (especially men). The device could detect IR reflections off of faces (when phone in use) and reflective clothing. The sniper scope kinda’ sticks out though.
I think with some work this idea could be very useful. It just needs some evolution a bit. I’m sure someone will figure out something and soon…
>But most people like hip-belt holsters (especially men).
They what now? I see maybe 0.5% of users with a hip holster. The other 99.5% of men use pockets, and women seem to be probably 60/40 pocket/purse. To say “most like holsters” is ridiculous.
Eric – OK let me re-word that: “…most of the men I see in my everyday pursuits (in Northeastern USA) seem to like the belt mounted hip holster as if it were a gun or something. Some of the YOUNGER women I see love to put the smartphone in their back pocket of their jeans with the top of the phone poking out.” So my experience is not absolute. I imagine there are exceptions to the rule. Belt mounts seem so utilitarian. You can grab it quickly when it rings. Fumbling for it in a pocket or purse sounds counter-intuitive to me. I keep getting calls from “pocket-dialers”. That is so annoying too! All you hear is the person walking and background noise. Saying HELLO! loudly doesn’t work either.
I’m thinking of inventing a long button-hole on the bottom left or right side of a t-shirt for men who like to wear sweat pants and un-tucked t-shirts (i.e ugly-American look?). The hemmed up hole would support your holster clip and wont weigh down your sweat pants that does not have a belt. Clipping it to your collar looks weird. Clipping it to your sweat pants makes your pants fall down if your draw sting is too loose. Carrying it is annoying. Upper arm jogging holsters are problematic too.
Trying to analyze any non-obvious analog design is tantamount to correctly analyzing the winning code of The International Obfuscated C Code Contest. The only way to justify educational(?) print space on such a design is with absolute detail–all details–provided by the designer.
See some of the late Bob Pease’s work for outstanding examples.