We all know that speakers are microphones and microphones are speakers, right? If not, take a moment to plug your headphones into a microphone jack and yell into them. It’s not exactly hi-fi, but it works.
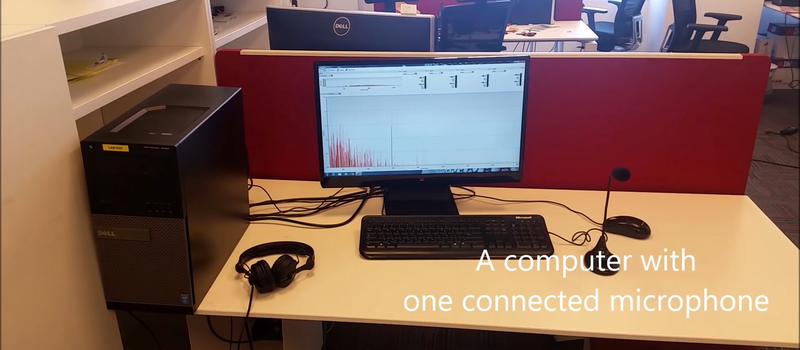
So it’s not a huge surprise that three security researchers in Israel have managed to turn the combination headphone and microphone input jacks that are present on most laptops into an eavesdropping device. (Paper here as PDF, with an obligatory demo video on YouTube, embedded below.) Speake(a)r is a neat proof-of-concept and a horrid pun.
There’s almost no exploit here; the just ask the codec chip to dump its output to an input channel, and listen in. The audio is weak, but they fully characterize what they can get out of it, and that includes voice or up to 1 Kbps of bandwidth. And the fact that this exfiltration capability is sitting around in almost every office environment just waiting to be (ab)used is reason for concern.
Of course, you could just unplug the earphones, and this makes us think about cell phones with their built-in hardware. The exploit assumes that the malware has access to your audio devices, so if you’ve got a microphone in your laptop, the game would be already over. Discuss this hack amongst yourselves in the comments.
via TechCrunch, and thanks for the tip from [bthy]!















speaker/headphones into mics sure but i don’t think you can turn a mic into a speaker….
Using a microphone as a speaker: https://www.youtube.com/watch?v=JbIiUYf7oYM
Dynamic ones can.
agreed but i would still argue that most cheap mic in use today are not actually dynamic microphones but some kind of condenser mic (or variation) that don’t actually work “in reverse”
A condenser/electret microphone can work in reverse. You are just driving the diaphragm with an electric field instead of a magnetic field. Most simple microphones have an integrated mosfet to amplify the signal. This is a one way system of course.
/*
Rant:
“just ask the codec chip to dump its output to an input channel”
I’ve been under the impression that what was known as stereo mix had finally been taken out of most modern codecs because the big A’s DMCA and other worldly equivalents. I know it started with Macroshaft and their Bimbos malware removing the option in their so called OS.
My Multimedia laptop has the functionality in the codec, but for some reason it doesn’t show up in alsamixer (even though it shows on an old distro).
Pulseaudio (falseaudio) has stupid latencies on it’s loopback plugin… Heaven forbid doing anything slightly CPU taxing oooooorrrrrrr tttthhhhhee llllatttttttteeeenccccyyyy iiiinnnndddduuuucccceeeedddd ttttiiiiimmmmeeeeeeesssssttrreeeettttccchhh iiiisssss wworrrrrssssseee tthhhhaaaaannnnnn tttthhhhhiiiissssss eeexxxaaaammmmppplllleeeeee.
Also on my system, that would mean having to re-install pulseaudio every time I need a loopback function in place of the better functioning one that is sitting dormant.
rant */
On topic:
To be fair, this is a clever technique. could be stopped by placing a unity gain buffer and a pre-amp for the output to isolate the EMF from the headphones (sound induced EMF for the pedantic).
But for use as random spying on unsuspected Joe public victims.. simplified
This has nothing to do with capturing the stereo mix. This is a feature of recent codecs to allow jacks to be used for whatever you plug into them. They just override the microphone/headphone auto detection.
Fair point….
However:
“could be stopped by placing a unity gain buffer and a pre-amp for the output to isolate the EMF from the headphones ”
still stands as a work around….
Can you turn a mic into a speaker?
Somewhat, yes….
“dynamic”:
Voice-coil at >600Ohm (usually, unless peasant grade market….)
Ceramic / Piezo – makes an OK tweeter (some are very good IMHO)
Electeret – remove fet and use high voltage might achieve >16Khz
The last one I’m not too sure about, But this is hack a day…. someone will…. eventually…. maybe… get it to work. Think static speakers.
An electret element can be a microphone or a speaker. More like a headphone, there are electret headphones. I’ve never seen them scaled up to speakers, though there are electrostatic speakers, which require a constant high voltage bias, while electrets have the charge built in.
But you’re right, the fet built into the electret microphone would limit the sound one could get out of it.
I would point out that electret microphone modules are cheap, and worth taking one apart. The time I did, the fet was in a tiny package, but still distinctive, I was expecting something more integrated. So one might be able to open one up, and get it back together after taking out the fet, for experimenting with electret “earbuds”.
Of course, while speakers and microphones can be used in reverse, something designed as a microphone does that job better than a speaker, and vice versa. But it’s optimization rather than the basic principal.
Michael
Man, I wanted to see them smack those headphones thus undeniably proving they’re the source.
Interesting from the High Security Installation standpoint but there’s so many lower hanging fruit available to exploit I wonder how serious a threat this is.
Many monitors already come with webcam/mic’s installed, laptops are hard to find without them, phone malware will undoubtedly have higher fidelity. Skype’s still closed source so I’m sure there’s exploits floating around the black market for it, not sure if G+ is much better. I presume the intelligence/diplomatic agencies use something a little more robust for video conference.
Unless you’ve got everything else locked down it’s like putting a vault door on your screened in patio.
On top of that you’ve still got to exfiltrate the audio. A constant 1kbps stream (or even bursts of recordings) shouldn’t be impossibly difficult detect on your network, IF you’re looking for them.
Low grade consumer laptops are hard to find without them. It’s trivial to buy a business class laptop without them. Dell and HP both sell all their business class laptops with the mic and camera delete.
Just use a hifi amp and speakers and kill a lot of birds (starlings) in one place.
This was old news, leaked years before Snowden when people already knew the government was spying on everyone and assumed it was common knowledge.
Good luck if you’re using a USB DAC the Amps don’t reverse well.
Wonder if that’d work with my 7.1 PC speakers… The speaker outputs on my motherboard can all be turned into individual line-ins in software… I guess the question is, what happens at the powered amp/subwoofer between the PC and speakers…
I works only if there is no amp between speaker and input. Any amp makes it one way.
At this point in life, I just assume all electronic devices with audio input or video input are capable of being tapped by whoever has the time and energy to exploit them. I put tape over my webcam and employ the recommended security measures but other than that what can a guy do? Probably just use electronics less and live life outside!
You are trying to convert speaker into microphone, i think that doesn’t work well actually. Why don’t you instead try out some good quality headphone. I personally using Sony headphones with mic https://www.vplak.com/sony-mdr-xb450ap-extra-bass-headphones-with-mic-p244 ,its working very well as having great bass volume as well as good features like ibuilt microphone etc.
You’re attempting to turn the speaker into a microphone, which in my opinion doesn’t really work. Instead, why not test out some high-quality headphones. I personally use Bower & Wilkins earbuds ( https://www.avfive.com/products/bowers-wilkins-pi5-wireless-supreme-earbuds? ) which work really well and have amazing features like an in-built in addition to having a strong bass volume.