Numbers stations are shortwave stations that broadcast cryptic messages that are widely assumed to be used for communications between nation states and spies. But who’s to say it’s up to the government to have all the fun? If you’ve always dreamed of running your own spy ring, you’ll need a way to talk to them too. Start with this guide on how to run your own numbers station.
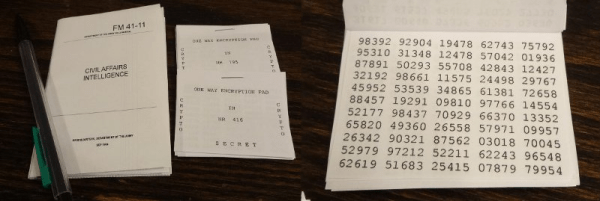
The requirements are simple – you just need random numbers, one time pads for each recipient (available from our store!) and a way to send the audio – ideally a powerful shortwave transmitter, but for an intelligence agency on a budget, online streaming will work. Then you’re ready to send your message. [Jake Zielke] shares techniques on how to easily encode a message into numbers for transmission, and how to encrypt them with one time pad techniques. Done properly, this is an unbreakable form of encryption. [Jake] then rounds out the guide with tips on how to format your station’s transmissions to address multiple secret agents effectively.
It’s a great way to get started in the world of spooky secret radio communications. All the tools needed to get started are available on the page, so you’ll be up and running in no time. Meanwhile, why not do a little more research on the history of numbers stations?