Although smartwatches seem to be just a recent fad, people have been strapping wristwatches to their wrists with all kinds of functionality. Whether a miniscule calculator, a remote control, an organizer or as in the case of the Web-@nywhere Watch a web browser. In the last case only sort of, naturally, as it was released in 2001 and this little early 2000s marvel cost only $85 (or $150 in 2024 USD), so what could it really be capable of? This is the million dollar question that [Cameron Kaiser] sought to find out as he found a new-in-box unit for sale.

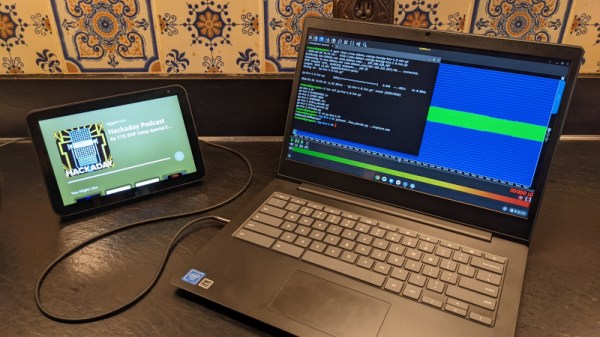
Beforehand he knew already that the unit required interaction with a PC-based application to sync the 93 kB of on-watch data, with the required software and remote servers now being very much outdated and/or gone. This required some reverse-engineering to once more bring this watch widget back to life. Along the way it became also quite clear that this watch was designed as a cheap rip-off of the much better 1998 Seiko Ruputer – which later got sold also as the onHand PC – using the same joystick-driven interface.
After some poking around with the Windows-based software that came with the watch [Cameron] quickly realized that while it could establish a serial link with the watch in its cradle, it fully relied on a now defunct FTP server formerly run by the manufacturer, Kinger, along with any games and content on it. Since FTP servers were never archived like HTTP sites, this content is likely gone forever.
Fortunately, the protocol between the PC and the watch is a standard serial link (with parity), so [Cameron] was able to sniff the serial traffic and figure out the protocol, the results of which he has made available on GitHub in the form of a Perl script for transforming text and a C-based application to do the uploading. Now once again Web-@nywhere users can proudly roam the streets with 2024-era website content on their wrists.