You know how the saying goes — they don’t make them like this anymore. It’s arguably true of pretty much any electronic device given the way technology changes over time, though whether or not it’s objectively a bad thing is going to vary from case to case.
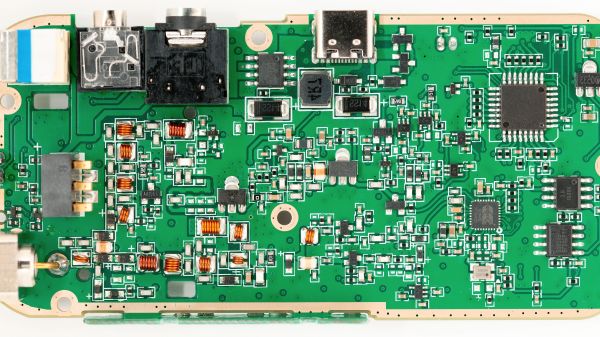
As a practical example, take a look at the insides of this 80’s vintage HP 3314A function generator shared on the EEV Blog Forum by [D Straney].

With multiple PCBs stacked on top of each other, it’s hard to imagine that more components could possibly be crammed into it. One board in particular appears to be an entire Motorola 6800 computer, something which today would likely be replaced with a single microcontroller.
Which is actually why [D Straney] shared this with us in the first place. After seeing our recent post about a modern waveform generator that’s basically an empty box thanks to its modern components, they thought this would be a nice example of the opposite extreme.
So, is it a good or a bad thing that test equipment isn’t made this way anymore? Well, it’s hard to argue with the improved capabilities, smaller footprint, and reduced cost of most modern gear. But damn is the inside of this HP 3314A gorgeous. As one of the commenters on the page put it, hardware from this era was really a work of art.