The best thing about buying your own home is that you can hang things on the walls. It’s a human right all too often denied to renters the world over. Regardless, five years later, when you’re doing the mandatory minimalist remodel, you’ll be ruing the day you put in all those wall anchors. At that point, consider removing them with this nifty tool from [XDIY with Itzik].
The design aims to remove wall anchors as cleanly as possible. It’s easiest to watch the video to get the idea of how it works.
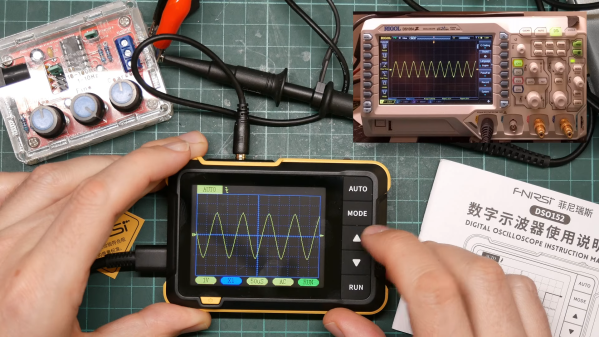
The tool features a block which holds a bearing. That bearing acts as a rotating stop for a wood screw. The idea is that you place the block against the wall, and use a power drill to drive a wood screw into the anchor at high speed. The screw can’t move forward, so the threads basically yank the plug out of the wall, and relatively neatly at that. Once removed, there’s a little push stopper you can use to hold the old plug in place as you remove the wood screw from the device, ready to go again.
[Itzik] demonstrates the device by removing ten wall plugs in just 40 seconds. If you’ve got a lot to do, or it’s a job you do regularly, you might like to have this tool in your kit.
Oftentimes, having the right tool can make a job ten times faster, and this seems like one of those cases. Video after the break.
Continue reading “Remove Wall Plugs Fast With A Custom Tool”