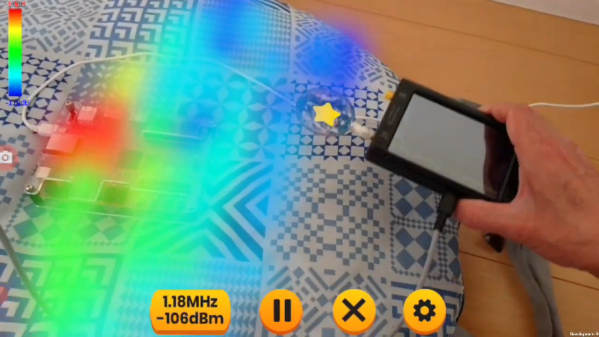
So you want to play some games from the early days of 32-bit iPhone OS that no longer run on recent OS versions? [Hikari-no-yume] wrote a sweet high-level emulator, touchHLE, to do so on modern iOS phones. But maybe you don’t have an iPhone? [Ciciplusplus] has your back. He ported the iPhone OS emulator, written in Rust, to Android, and then ported a version of DOOM that runs on iPhone OS to go with it.
[Ciciplusplus] also made a video (embedded below) where he documented the trials and tribulations of porting Rust code to the Android platform – an intensely Java environment. It doesn’t sound like it was at all trivial. Of course, this couldn’t have been accomplished without [Hikari-no-yume]’s original work on touchHLE, which was made essentially to fulfill [Hikari-no-yume]’s long-time obsession with the game Super Monkey Ball.
So for now, touchHLE can boast the ability to run a few old 32-bit games on Android and desktop operating systems. What other games from the first years of gaming on smart phones (and iPods) do you need to see ported? Get involved in the project if you’ve got an itch you need scratched.