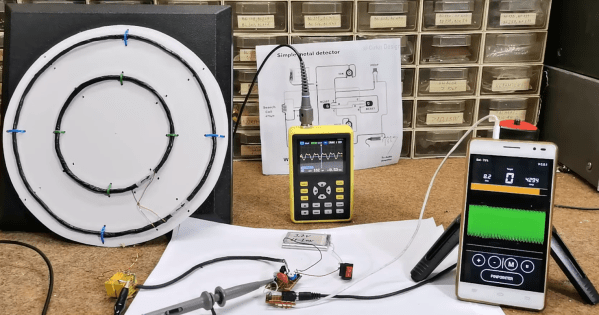
[mircemk] is quite a wizard when it comes to using coils of wires in projects, especially when their application is within easy-to-build metal detectors. There are all kinds of ways to send signals through coiled wire to detect metal objects in the ground, and today [mircemk] is demonstrating a new method he is experimenting with which uses a smartphone to detect the frequency changes generated by the metal detector.
Like other metal detectors, this one uses two coils of wire with an oscillator circuit and some transistors. The unique part of this build, though, is how the detector alerts the user to a piece of metal. Normally there would be an audible alert as the frequencies of the circuit change when in the presence of metal, but this one uses a smartphone to analyze the frequency information instead. The circuit is fed directly into the headphone jack on the smartphone and can be calibrated and used from within an Android app.
Not only can this build detect metal, but it can discriminate between different types of metal. [mircemk] notes that since this was just for experimentation, it needs to be calibrated often and isn’t as sensitive as others he’s built in the past. Of course this build also presumes that your phone still has a headphone jack, but we won’t dig up that can of worms for this feature. Instead, we’ll point out that [mircemk] has shown off other builds that don’t require any external hardware to uncover buried treasure.