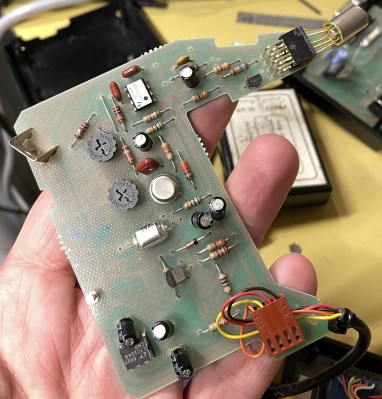
The Apple Touch Bar was an oddity on a fairly small number of Apple laptops which replaced the function key row with a touch display. Yet what is special about this display other than its odd form factor when you consider it as a generic touch display? As [Wenting Zhang] describes in a recent reverse-engineering video, this 2,170 x 60 pixel display is somewhat limited in that it doesn’t support the MIPI DSI video mode, only command mode, along with a special instruction (0x3C) for automatic address offsets. The results of this project can be found on the GitLab account.
In a way these limitations make sense when you consider Apple’s use case for these special MIPI-DSI displays. As a touch screen with dynamic controls being displayed on it, features such as video playback never were a goal, and thus Apple likely decided to save a few bucks, possibly also due to MIPI licensing costs. What this means is that if you had dreamed of snapping up an extremely long and narrow OLED display for a video project you’re in for somewhat of a bad time. Although animated content is possible – as [Wenting] demonstrates – this comes with all the limitations of command mode, meaning slower updates, higher power usage and a lot more overhead.
Continue reading “Reverse Engineering The Apple Touch Bar Screen”