We had a wild time at DEF CON last week. Here’s a look back on everything that happened.
 For us, the festivities closed out with a Hackaday Breakfast Meetup on Sunday morning. Usually we’d find a bar and have people congregate in the evening but there are so many parties at this conference (official and unofficial) that we didn’t want people to have to choose between them. Instead, we made people shake off the hangover and get out of bed in time for the 10:30am event.
For us, the festivities closed out with a Hackaday Breakfast Meetup on Sunday morning. Usually we’d find a bar and have people congregate in the evening but there are so many parties at this conference (official and unofficial) that we didn’t want people to have to choose between them. Instead, we made people shake off the hangover and get out of bed in time for the 10:30am event.
We had a great group show up and many of them brought hardware with them. [TrueControl] spilled all the beans about the hardware and software design of this year’s Whiskey Pirate badge. This was by far my favorite unofficial badge of the conference… I made a post covering all the badges I could find over the weekend.
We had about thirty people roll through and many of them stayed for two hours. A big thanks to Supplyframe, Hackaday’s parent company, for picking up the breakfast check and for making trips like this possible for the Hackaday crew.
Hat Hacking
For DEF CON 22 I built a hat that scrolls messages and also serves as a simple WiFi-based crypto game. Log onto the access point and try to load any webpage and you’ll be greeted with the scoreboard shown above. Crack any of the hashes and you can log into the hat, put your name on the scoreboard, and make the hat say anything you want.
Last year only one person hacked the hat, this year there were 7 names on the scoreboard for a total of 22 cracked hashes. Nice work!
- erich_jjyaco_cpp 16 Accounts
- UniversityOfAriz 1 Account
- @badgerops 1 Account
- conorpp_VT 1 Account
- C0D3X Pwnd you 1 Account
- D0ubleN 1 Account
- erichahn525_VTe 1 Account
Three of these hackers talked to me, the other four were covert about their hat hacking. The top scorer used a shell script to automate logging-in with the cracked passwords and putting his name on the scoreboard.
I’d really like to change it up next year. Perhaps three hats worn by three people who involves some type of 3-part key to add different challenges to this. If you have any ideas I’d love to hear them below, or as comments on the project page.
[Eric Evenchick] on socketCAN
 One of the “village” talks that I really enjoyed was from [Eric Evenchick]. He’s been a writer here for a few years, but his serious engineering life is gobbling up more and more of his time — good for him!
One of the “village” talks that I really enjoyed was from [Eric Evenchick]. He’s been a writer here for a few years, but his serious engineering life is gobbling up more and more of his time — good for him!
You probably remember the CANtact tool he built to bring car hacking into Open Source. Since then he’s been all over the place giving talks about it. This includes Blackhat Asia earlier in the year (here are the slides), and a talk at BlackHat a few days before DEF CON.
This village talk wasn’t the same as those, instead he focused on showing what socketCAN is capable of and how you might use it in your own hacking. This is an open source software suite that is in the Linux repos. It provides a range of tools that let you listen in on CAN packets, record them, and send them out to your own car. It was great to hear [Eric] rattle off examples of when each would be useful.
Our Posts from DEF CON 23
If you missed any of them, here’s our coverage from the conference. We had a blast and are looking forward to seeing everyone there next year!
- Help Decipher the DEF CON Badge
- DEF CON Uber Badge so Hot It’s Radioactive
- DEF CON: The Proxy for ProxyHam
- Cory Doctorow Rails Against the Effect of DRM and the DMCA
- DEF CON: Abusing Scripts in Multiplayer Games
- Hacking a KVM: Teach a Keyboard Switch to Spy
- DEF CON: HDMI CEC Fuzzing
- All the Unofficial Electronic Badges of DEF CON







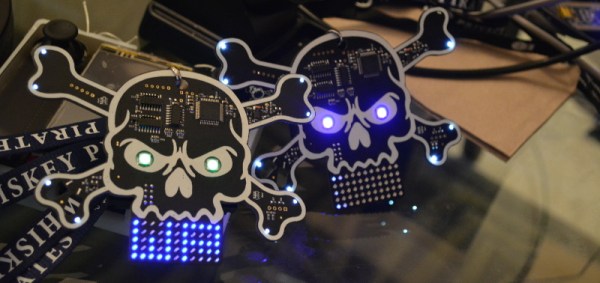


![DSC_0528 Gorgeous text treatment on back of this badge is indicative of [True's] mastery](https://i0.wp.com/hackaday.com/wp-content/uploads/2015/08/dsc_0528.jpg?w=262&h=174&ssl=1)