[Oleg Kutkov] decided to build a wideband SDR – for satellite communication research and monitoring, you know, the usual. He decided on a battery of HackRF boards – entire eight of them, in fact. Two 1×4 and one 1×2 RF splitters and an LNA on their combined RF input made for a good start to the project, and from there, it only got more complex.
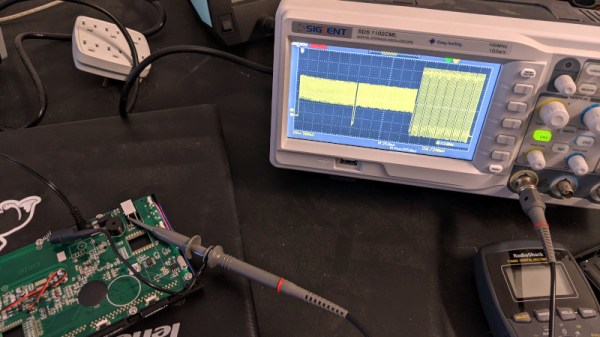
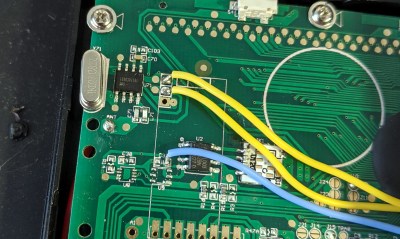
HackRF boards can be synchronized with a separate clock source, but you can’t just pull a single clock line to all of them in a star configuration. Thus, he’s built a clock distribution and amplifier board, with 4 ns propagation delay at 1 PPS, and only 10 ns delay at 10 MHz. Then, he integrated that board with the HackRF setup, adding a case, wiring up a purpose-built cable and dealing with the reflections that occurred.
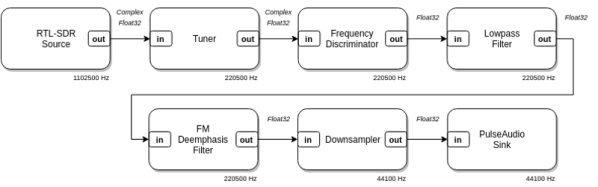
HackRF boards are USB 2.0 and able to generate a stream of data up to 320 MB/s, and there’d be no viable way to aggregate eight 2.0 links into one. To solve that, he’s used eight separate PCI-E to USB 3.0 cards, each of them with one HackRF plugged in, all connected to an AMD Ryzen 9-powered PC through PCI-E risers we typically see used for mining purposes. To tie it all together, he created a gnuradio flowgraph and patched the osmocom source block to enable the external clock synchronization mechanisms he decided to use.

In the end, [Oleg] shows us some promising results – two DVB-S transceivers visible on the waterfall display of the spectrum capture. The work is not over here, to be clear – he’s ran into a few roadblocks. The gnuradio flowgraph doesn’t lend itself well to multi-threading, even on a Ryzen 9 machine, and [Oleg] pledged to rewrite the capture mechanisms in C++ which can be nicely allocated to separate physical CPU cores, something gnuradio is apparently not quite good at.
More importantly, the spectrum captured is not continuous, and [Oleg] questions whether it can be demodulated properly. He had to resort to frequency overlaps due to upsampling, and he’s not quite sure how to compensate for that. Overall frequency stability is also in question. However, from here, seems like most of the work towards building a wideband receiver is done!
[Oleg] is typically seen on Twitter, lately doing some heavy tinkering with Starlink – as Kyiv, the city he’s currently in, is under bombardment of Russian Armed Forces. We can only respect and appreciate the dedication. In January, we’ve covered his work on an USA-imported Tesla LTE modem replacement to fix LTE band incompatibilities in Ukraine, and his blog is a treasure trove of experiments that we are yet to properly comb through, from astrophysics and satellite work to RS485 networks and Linux driver writing.





 But to do any of this, you need a receiver, and that starts with a horn antenna to collect the weak signal. In collaboration with a former student, high school teacher [ArtichokeHeartAttack] built a pyramidal horn antenna of insulation board and foil tape. This collects RF signals and directs them to the waveguide, built from a rectangular paint thinner can with a quarter-wavelength stub antenna protruding into it. The signal from the antenna is then piped into an inexpensive
But to do any of this, you need a receiver, and that starts with a horn antenna to collect the weak signal. In collaboration with a former student, high school teacher [ArtichokeHeartAttack] built a pyramidal horn antenna of insulation board and foil tape. This collects RF signals and directs them to the waveguide, built from a rectangular paint thinner can with a quarter-wavelength stub antenna protruding into it. The signal from the antenna is then piped into an inexpensive 








