Sometimes, the answer to, “Why would you bother with a project like that?” is just as simple as, “Because it’s cool.” We suspect that was the motivation behind [Dirk-Jan]’s project to make portable versions of classic rotary telephones.
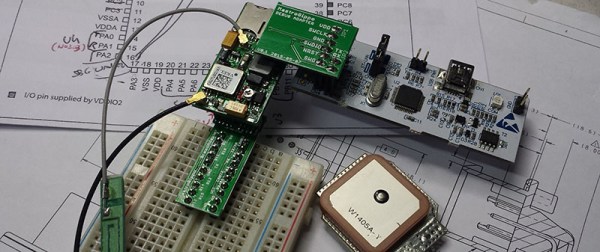
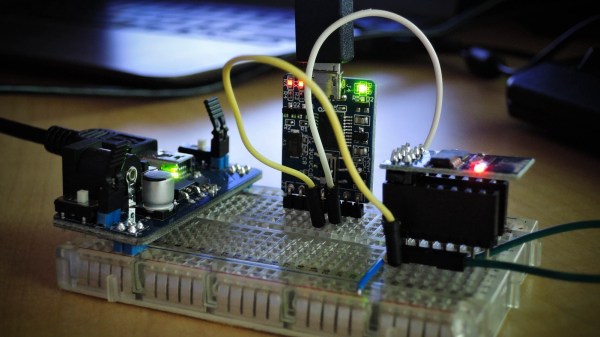
On style points alone, [Dirk-Jan] scores big. The mid-1950s vintage Belgian RTT model 56 phone has wonderful lines in its Bakelite case and handset and a really cool flip-up bail to carry it around, making it a great choice for a portable. The guts of the phone were replaced with a SIM900 GSM module coupled with a PIC microcontroller and an H-bridge to drive the ringer solenoids, along with a Li-ion battery and charger to keep it totally wireless – except for the original handset cord, of course. The video after the break show the phone in action both making and receiving calls; there’s something pleasing on a very basic level about the sound of a dial tone and the gentle ringing of the bell. And it may be slow, but a rotary dial has plenty of tactile appeal too.
Rotary-to-cell conversions are a popular “just because” project, like this conversion designed to allow an angry slam-down of the handset. The orange Siemens phone in that project is nice and all, but we really favor the ’50s look for a portable.