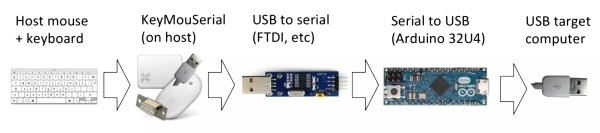
All laptops have a working keyboard and mouse built into them, the only problem is that you can’t use these tools on other computers that don’t have them. At least, until now. [Peter] has created the KeyMouSerial in order to use his laptop’s keyboard and mouse as physical devices on his Raspberry Pi, finally freeing the bonds holding our laptops’ human interface devices back.
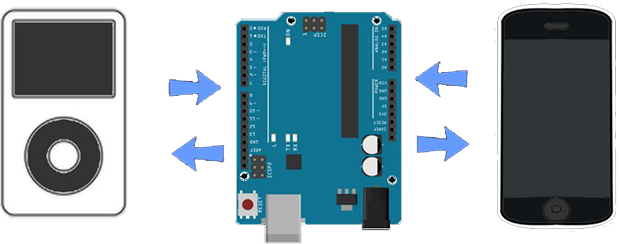
The software for KeyMouSerial copies keystroke and mouse information and sends this out via a serial port on his laptop (using a USB to serial adapter). From there the information is translated by an Arduino into HID commands which are sent via USB to the target computer, in this case a Raspberry Pi. It’s a pretty elegant solution to carrying a bulky keyboard and mouse along just for a Raspberry Pi, or for any computer that might not have access to a network and SSH.
[Peter] has also been working on using his iPod as a serial-to-USB converter, so if you’re a Rockbox developer and want to help out then drop him a line. All of the software is available (for Windows, Mac, or Linux) including the Arduino sketch if you want to try this software out for yourself. And, if you don’t want to turn a computer into a keyboard and want to go the other direction and turn a keyboard into a computer, that is also an option.

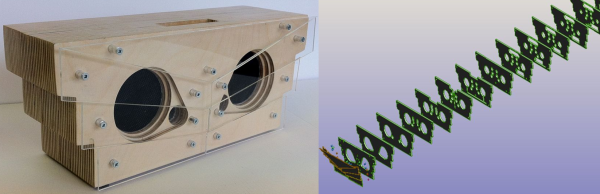
 The case is made out of plywood: many, many layers of plywood. Each layer of plywood was cut out using a laser cutter. Unlike most speaker cabinets that have a distinct boxy enclosure, this unit is mostly solid with cutouts in each layer only where voids were designed to be. [decpower] tried to replicate the Bose Wave Radio internal sound passages. Up top a dock slot complete with a 30-pin connector makes connecting an iPod super simple.
The case is made out of plywood: many, many layers of plywood. Each layer of plywood was cut out using a laser cutter. Unlike most speaker cabinets that have a distinct boxy enclosure, this unit is mostly solid with cutouts in each layer only where voids were designed to be. [decpower] tried to replicate the Bose Wave Radio internal sound passages. Up top a dock slot complete with a 30-pin connector makes connecting an iPod super simple.