[Taciuc Marius] and his colleague noticed that days with low atmospheric pressure plus caffeine in their system meant a spike in blood pressure. Considering how this might impact his cardiovascular health, he decided to make a relative pressure barometer out of a jar to help him decide whether he should really have another cup of coffee.
Aside from a 3D printer, you’ll need to assemble a small jar with a lid, some 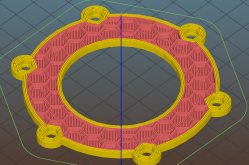 screws, lock washers, nuts, and a flexible membrane — a piece of a rubber glove or balloon will do nicely. [Marius] details the build process on his project page, advising others to print the parts at 0.2 resolution — potentially even upping the extrusion multiplier to 1.1 — to prevent gaps in the print that would compromise the airtight seal needed for the barometer to work properly.
screws, lock washers, nuts, and a flexible membrane — a piece of a rubber glove or balloon will do nicely. [Marius] details the build process on his project page, advising others to print the parts at 0.2 resolution — potentially even upping the extrusion multiplier to 1.1 — to prevent gaps in the print that would compromise the airtight seal needed for the barometer to work properly.
Additionally, thick glue or epoxy is recommended for the rest of the assembly process — it doesn’t have to be pretty, but it does need to be sealed! The final product can be easily tested by simply holding the jar.
While this barometer helps one make healthy choices, not all are created equal. This one tells you flat out how you should consider getting to work, while others have been tricked into behaving like touch sensors.















