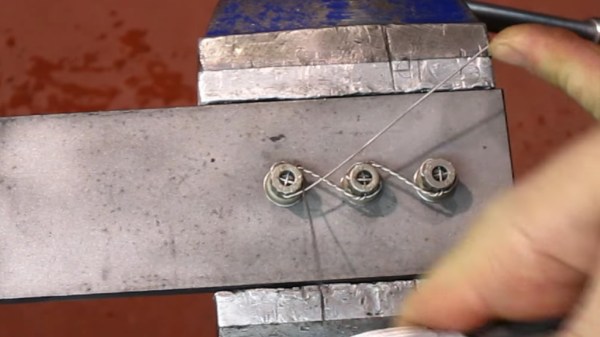
We were tipped off to an older video by [AgentJayZ] which demonstrates the proper use of lockwire also known as ‘safety wire.’ In high vibration operations like jet engines, street racers, machine guns, and that rickety old wheelchair you want to turn into a drift trike, a loose bolt can spell disaster. Nylon fails under heat and mechanical lock washers rely on friction which has its limits. Safety wire holds up under heat and resists loosening as long as the wire is intact.
Many of our readers will already be familiar with lockwire since it is hardly a cutting-edge technology — unless you are talking about the cut ends of lockwire which [AgentJayZ] warns will slice up your fingers if you aren’t mindful. Some of us Jacks-or-Jills-of-all-trades, with knowledge an inch deep and a mile wide, may not realize all there is to lockwire. In the first eight minutes, we’ll bet that you’ve gotten at least two inches deep into this subject.
[Editor’s Note: an inch is exactly 25.4 mm, if the previous metaphors get lost in translation. A mile is something like 2,933.333 Assyrian cubits. Way bigger than an inch, anyway.]
Now, those pesky loose bolts which cost us time and sighs have a clear solution. For the old-hands, you can brush up on lockwire by watching the rest of video after the break.
Thank you [Keith Olson] for the tip, and we’ll be keeping an eye on [AgentJayZ] who, to date, has published over 450 videos about jet engines.
If safety isn’t your highest priority, consider this jet engine on a bicycle or marvel at the intricacies of a printable jet engine.