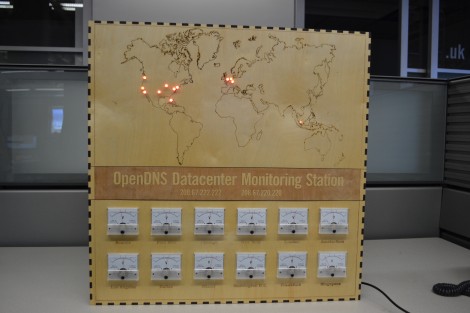
Nothing says Cold War like a map of the work with LEDs embedded in it. Throw in some analog dials for good measure and you’ve got a piece that would be comfortable mounted next the WOPR in everyone’s favorite ’80s-computers-run-amok movie. We think [Dima] really hit the mark when building this status panel for OpenDNS datacenter monitoring.
[Dima] works for OpenDNS and wanted to make something special for its upcoming 5 year anniversary. He’d already been toying with making boxes from laser-cut wooden pieces. This was just a matter of choosing a size that would fit the dials and leave a suitable area for a laser-etched map. Each of the twelve panel meters gets a PWM signal from the Arduino Mega that he used to bring the device to life. It shows a comparative server load for each data center based on the previous day’s numbers. There is an LED in the map for each of these centers. Right now they’re all red, but he used RGB LEDs and plans to upgrade the capability soon. He should have no problem doing this as he sourced some TLC5940 drivers to extend his I/O capabilities.
Don’t forget the check out the clip embedded after the break. Continue reading “Monitoring The World’s DNS Status Using A Display Straight Out Of WarGames”











