This weekend is ShmooCon, a hacker convention held in Washington DC. Brian Benchoff and I will be there, both of us for the first time. We’d love your input on what talks look the most interesting. Check out the schedule of speakers, then leave a comment below to let us know which talks you think we should cover.
It’s great hearing the big presentations, but I find a lot of times great hacks can be found in smaller venues, or just by walking around. Two examples from 2015 DEF CON: the best talk I sat in on had about 10 people spectating in the IoT village, and I had a great time trying to track down everyone who had an unofficial hardware badge. If you’re at ShmooCon and have something to show off, please find us (@szczys, @bbenchoff)!
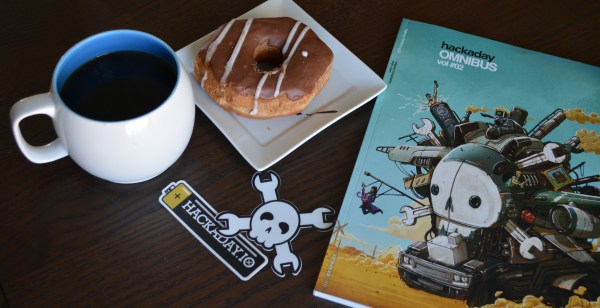
On Saturday join us for a Hackaday meetup in the lobby of the Washington Hilton. ShmooCon is well-regarded for the quality of its “lobby-con”, what better place to gather? Look for the Hackaday crowd starting Saturday 1/16 at 8:45am. We’ll bring the donuts, and some swag like Hackaday Omnibus Vol. 02 and of course, some Jolly Wrencher stickers.


 Both [Voja Antonic] and [Nava Whiteford] will be attending this year’s 32C3, which runs from Sunday the 27th through Wednesday the 30th.
Both [Voja Antonic] and [Nava Whiteford] will be attending this year’s 32C3, which runs from Sunday the 27th through Wednesday the 30th. Shmoocon
Shmoocon