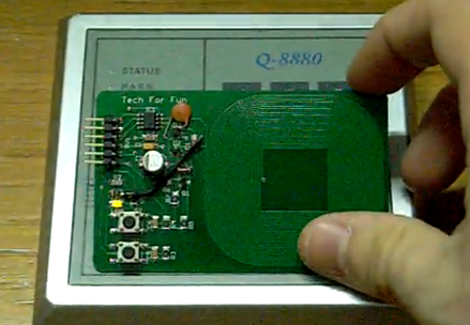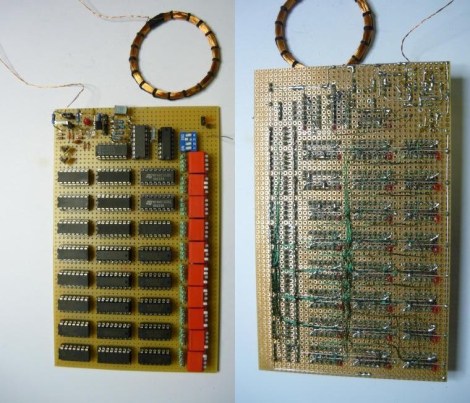
This soldering nightmare is a configurable RFID tag which has been built from 7400-series logic chips. The beast of a project results in an iPhone-sized module which can be used as your new access card for security systems that uses the 125 kHz tags. The best part is that a series of switches makes the tag hand programmable, albeit in binary.
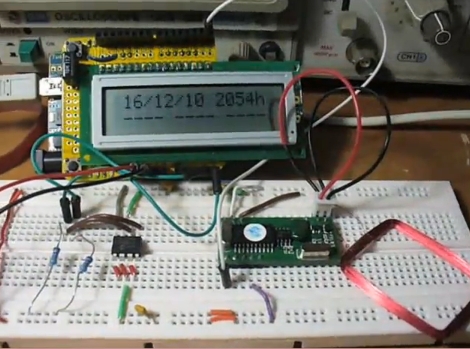
Of course this is an entry in this year’s 7400 Logic Competition. It’s from last year’s winner, and he’s spent a lot of time documenting the project; which we love. We were surprised that this many chips can be powered simply by what is induced in the coil from the reader. This is just one of the reasons the 7400-series have been so popular over the years. After working out the numbers, a 64-bit shift register was built to feed the tag ID to the encoding portion of the design. There were many kinks to work out along the way, but once it was functional a surface-mount design was put together resulting in the final product shown off in the video after the break.
Continue reading “Configurable RFID Tag From 7400 Logic Chips”