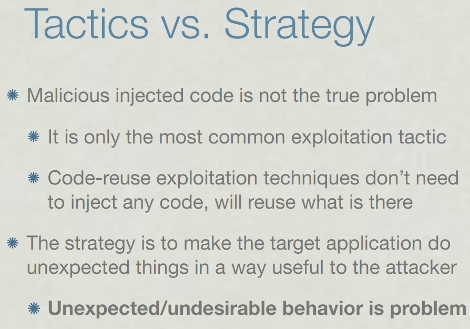
[Dino A. Dai Zovi] gave a talk in the earlier part of 2010 where he shares his thoughts on the future of malicious exploits. You can watch it on Ustream and he’s also posted a set of slides (PDF) that goes along with it. We find the 48 minute video to be quite interested. Instead of going into mundane detail, he covers the broader picture; what has been done in the past, what will happen in the future, and how are we currently ill-equipped to respond to future threats? That last question is covered throughout the video, but seems to come back to the concept that we are stuck in a rut of terminology and past practice that is impeding our ability to innovate security strategies at the same rate that the bad guys are coming up with the next nasty thing to come down the pipeline.















Curious how you find a video to be interested… what is it interested in?
/grammarnazi
Thanks for posting this, sounds quite interesting.
I hoped the future of cyberattacks was in exploiting C compiler bugs, however I found this article yesterday
http://arstechnica.com/open-source/news/2010/12/fbi-accused-of-planting-backdoor-in-openbsd-ipsec-stack.ars
Probably doesn’t help that all NX bit implementations are broken, and nobody uses the ACLs that have been in NT since forever..
The baddest rootkit currently writes an encrypted FS and patches SSDT on NT..Almost decade old methods, just like spreading through heap and stack overflows..