Here’s a common story when it comes to password retrieval: guy sets up a PC, and being very security-conscious, puts a password on his Seagate hard drive. Fast forward a few months, and the password is, of course, forgotten. Hard drive gets shuffled around between a few ‘computer experts’ in an attempt to solve the problem, and eventually winds up on [blacklotus89]’s workbench. Here’s how he solved this problem.
What followed is a walk down Hackaday posts from years ago. [blacklotus] originally found one of our posts regarding the ATA password lock on a hard drive. After downloading the required tool, he found it only worked on WD hard drives, and not the Seagate sitting lifeless on his desk. Another Hackaday post proved to be more promising. By accessing the hard drive controller’s serial port, [blacklotus] was able to see the first few lines of the memory and the buffer.
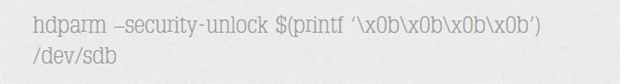
Two hours and two Python scripts later, [blacklotus] was able to dump the contents of his drive. He then took another Seagate drive, locked it, dumped it, and analyzed the data coming from this new locked drive. He found his old password and used the same method to look for the password on the old, previously impenetrable drive. It turns out the password for the old drive was set to ‘0000’, an apparently highly secure password.
In going through a few forums, [blacklotus] found a lot of people asking for help with the same problem, and a lot of replies saying. ‘we don’t know if this hard drive is yours so we can’t help you.’ It appears those code junkies didn’t know how to unlock a hard drive ether, so [blacklotus] put all his tools up on GitHub. Great work, and something that didn’t end up as a Hackaday Fail of the Week as [blacklotus] originally expected.















0000? That’s the combination on my luggage!
And our cold war era nuclear launch codes. I wish I was kidding.
No, no… that was 00000000. Twice as long, twice a secure.
All My passwords are 000000000! Gen-us!
Not one of those launch code hacking, rogue AIs in the movies ever tried 00000000.
Hey why are you guys raging on “0000” it’s the only password you can say when you forget it, you forget your password and say “OOOO S**T!”. It’s the perfect password!
Who-we-who-we-whooo! (IntenseYawning)
Don’t worry I got the Spaceballs reference.
I see you bought the expensive stuff, mine only has three zeros :¬(
Better write it down before you forget
ether – class of organic compounds used in 1800’s medicine as an anesthetic, alkyl or aryl groups joined by an oxygen molecule.
either – one of two possible choices
Don’t worry, I got the Third Reich reference.
Ahh but this is ” hard drive ether”, the substance used to knock out your data when the drive fails…
It’s funny, they used to postulate there was this ‘aether’ filling space to transfer stuff. Then later we all laughed at the concept. Now we again came with the same theory, just not using the term aether.
Sometimes it does no look like science is moving forwards anymore.
do you mean the higgs field?
Weird how hard they found it to crack that password… Just saying…
I’m part of a research lab that does alot of data recovery work, the problem with the 0000 for password is a common issue, some hard drives have this terrible habbit when they fail to revert back to default passwords, or when they are flash/updated.
0000
00000000
0000000000000000
are three moment common passwords, passwords can be found in the firmware/roms which its possible to dump via the serial connections.
Funny bit is that the ‘firmware’ is mostly stored on platters. Makes it a royal PITA in some ways when trying to recover a bad board, but great in other ways…
is there any way of contacting BlackLotus regarding the python he wrote?