In today’s digital era, we almost take for granted that all our information is saved and backed up, be it on our local drives or in the cloud — whether automatically, manually, or via some other service. For information from decades past, that isn’t always the case, and recovery can be a dicey process. Despite the tricky challenges, the team at [Museo dell’Informatica Funzionante] and [mera400.pl], as well as researchers and scientists from various museums, institutions, and more all came together in the attempt to recover the Polish CROOK operating system believed to be stored on five magnetic tapes.
Originally stored at the Warsaw Museum of Technology, the tapes were ideally preserved, but — despite some preliminary test prep — the museum’s tape reader kept hanging at the 800 BPI NRZI encoded header, even though the rest of the tape was 1600 BPI phase encoding. Some head scratching later, the team decided to crack open their Qualstar 1052 tape reader and attempt to read the data directly off the circuits themselves!!
 Using an Arduino Mega as a sampling device and the tape in test mode, the team were able to read the tapes, but the header remained inscrutable and accompanied by errors in the rest of the data. Promising nonetheless!
Using an Arduino Mega as a sampling device and the tape in test mode, the team were able to read the tapes, but the header remained inscrutable and accompanied by errors in the rest of the data. Promising nonetheless!
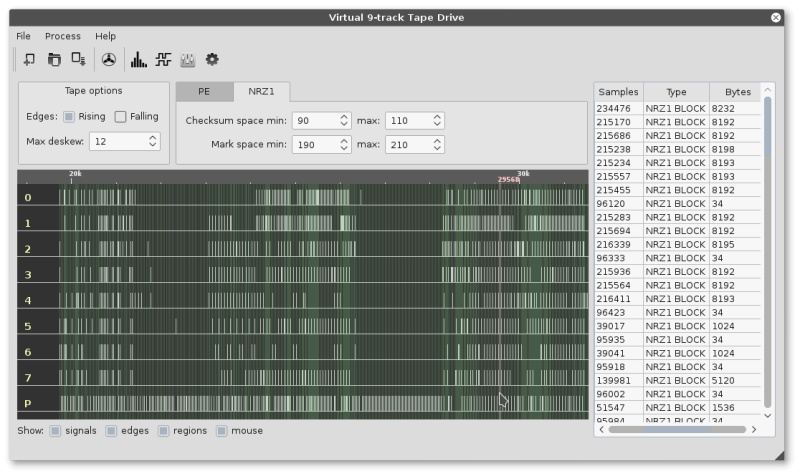
Switching gears, the decision was made to use a logic analyzer to read the tapes and use software to decode the data. While they waited for their new analyzer to ship, one of the team members, [Jacob Filipowicz] harnessed the power of Python to write a program called Nine Track Labs (pictured below) which would allow them to read any kind of magnetic tape, at any speed, BPI, and writing standard. Armed with the software and analyzer, the team was able to successfully recover the data from the tapes in its entirety without errors!
Among the data recovered, there were numerous versions of the CROOK operating system — allowing them to reproduce the OS’s development process, as well as hundreds of other files containing programs and tools hitherto believed to be lost. There was also a backup of a ‘live’ MERA-400 system with a binary CROOK-3 OS, ready to run in emulation. All things considered, the techno-archeological tour-de-force was a smashing success.
 If — in your more modern travels — you need to recover an audio recording gone awry, know that you can retrieve that data with a hex editor.
If — in your more modern travels — you need to recover an audio recording gone awry, know that you can retrieve that data with a hex editor.


















Techniques like this are going to become more important as we move on.
There is an irony that we are creating more data than in any time in history, but in a 100 years there may be less information about our century than we have now about our ancestors. We send emails instead of letters, photos never get printed and books move to e-books.
We may make back-ups, but unless those back-ups are continually renewed the likelihood will be that the next generation will have as much chance of accessing them as I have in reading Cretean Linear-B.
This is where the hacking community is so important by ensuring that legacy technology is retained
Otherwise we might find ourselves in this sort of situation https://en.wikipedia.org/wiki/Apollo_11_missing_tapes
Kudos to the team and hopefully they will share there code so others can follow.
You can find some sources here:
https://github.com/jakubfi?tab=repositories
Agreed, that combined with ever longer copyright protection and complex DRM systems as great deal of what has been produced over the past 30 years will be lost.
This is perhaps exactly what the companies want: buy my game now, or you may never experience it again!
Something someone wrote on a rock 30 centuries ago can be read by people today, an OS written 30 years ago takes a freaking super hacking team to tease out of the aether.
This disregards the millions of rocks and tablets that were lost to time.
or the Rosetta stone
maybe we should have a typewriter for making clay tablets for long term information retention
That is a truly brilliant idea for a hack !
Some kind of instant CNC engraving machine, with concrete paste for corrections!
CNC? Have You worked with clay? wet clay isn’t something youd like to mill. Typewriter is much better idea extrude clay into tablet form and have “typewriter” impress signs on it then to circular automatic kiln they use in mass producing pottery then to storage. It could be fully automatic process but needs to be packed into shock resistant crates else earhquake or transportation accident and it will crack.
Deciphering languages and symbols from ancient rock-based texts typically requires a hacking team of a different sort.
Can you imagine were all information is centralised then catastrophe strikes world wide city disasters, The learning that would be lost and the backwards people will go it will happen again.
A friend of mine reads linear-B. It’s apparently not that hard.
My Bad – I meant Linear-A. I tried linear-B put it was all Greek to me
Quote: “There is an irony that we are creating more data than in any time in history, but in a 100 years there may be less information about our century than we have now about our ancestors. We send emails instead of letters, photos never get printed and books move to e-books.”
We hit that problem before. A century and more ago, most people kept in touch with letters, even if they lived in the same city. Phones just weren’t that common. When daily conversations to those nearby shifted to phones, historians and biographers lost a critical source of information. Technically, emails return us to that earlier era, since they are fixed in form. But that depends on people saving them like they do letters, as well as the technology to read what they’re stored on.
You hit on the head! Good JOB!
Yep, for example, the wife of a French politicians is accused have been paid from public fund until 2013 for a work that she probably never did. When people find it’s strange that no emails exist about her work, the argument they used is that nobody keep their emails…
https://hackaday.io/project/10579-retro-futuristic-automobile-control-panel/log/49862-test-example-post-mainframes-behind-the-iron-curtain
Always love seeing your content Skaarj. Post more on YouTube!
>So we ordered a chinese “Saleae” 16 channels logic analyzer
hehe, why buy counterfeit chinese saleaeaaee clone when genuine SeeedStudio DSLogic offers better specs at same price?
There is something magical about tape storage. It always bothered me nobody tried to bring multi track compact cassette storage to home computers in the eighties, even just reusing stereo head would double capacity and speed.
9 track Digital Compact Cassette with pretty much same speed as the 1/2 inch from the article came to late in 1992.
Why did they not bring multitrack to homes? Well, money… In those days, multitracks were considered “professional” equipment and as such it was designed and made to a certain quality standard, making them rather expensive for the average Joe…
That being said, I don’t understand why nobody tried to utilise the power of an ordinary VCR for digital data storage… You get almost a megahertz of bandwidth (obviously not with LP though) for at least 45 minutes, that’s quite a bit of data to be stored…
One could either have a DSP box that would transform data into something resembling a TV signal (you need the sync pulses in order for the VCR to record anything meaningful) or just use the mechanics of an OEM and make a data-only VCR…
Yes, todays tape drive storage for computer use works exactly in the same manner (at least as far as the way data is written on the tape), but they are too expensive for the consumer market…
VCR data storage was a thing. See Video Backup System (VBS) for the Commodore Amiga, for example.
http://www.hugolyppens.com/VBS.html
And yet this died faster then Betamax…
Also, >400MB per 4hr tape is pretty…conservative…, the tape can definitely handle a lot more.
Error correction. If the tape gets eaten and you splice it back together you may still be able to recover all the data.
It was designed as a low cost backup solution (minimal extra hardware) , to be robust and compatible with all kinds of VCRs. Yes it is possible to store much more data but it is much harder and more expensive.
Examples of the above: this design used a monochrome signal making the color encoding and quirks of those a non-issue, it limits the data rate so that a 68020 14MHz processor could encode and decode a Reed-Solomon error correction code in software.
There have been other designs that could store more data but those were considerably more expensive than that solution.
Home users who used “standard” tape drives had no need for bigger or better storage. Hackers, power users and professionals either used disks or hard drives, and typically had more capable machines than classic 8-bit computers…
This was done for the Atari ST as well. Far better than cassette but a bit cumbersome and slow nonetheless. Cheaper SCSI/IDE/Floppy tape drives hitting the market like the QIC-80, etc kinda killed the need.
These did exist, ArVid was popular in Russia, used a standard VCR and an ISA card, sent data to the VCR over a composite video cable. There were other systems that used a SVHS cassette for storage, but the system itself was different than a standard VCR, aside from the transport mechanism and heads. (I.e., it didn’t use a video signal to encode the data). There was also D-VHS which existed for a few years in the late 90s-Early 2000s, I seem to remember DirecTV having a receiver with a D-VHS recorder built into it, for recording satellite programs. It was quickly supplanted by hard disk based DVRs and DVD recorders.
It’s exist. For example search for “PCM adaptors”, it’s was used to record digital audio on VCR. It was even the standard method before the DAT to use Sony U-matic video tape to transfer the digital master to the CD plants.
Yes. VCR solutions existed, but VCR was expensive in the 80s, even in the nineties it cost as much as 16bit computer.
Im really baffled why people didnt go for the cheap win and used stereo heads in 8bit computer tape storage devices (datasette etc). Well, Im not baffled by Commodore not doing that, they were dysfunctional and always delivered mediocrity while wasting time and money on stupid ideas (C65 anyone? C128, A600, CDTV lol), but there were multiple independent shops making hardware for 8bitters, yet not a single multi track cassette tape storage.
CROOK! What a name for an OS. Could it be trusted?
Developers of CROOK OS presented their design idea for it during seminar at Institute of Mathematical Machines. Everyone told them such design would never work. They already had working system at their laboratory, so clearly someone was cheating, hence the name…
The name alone would have made it great choice as a real article on April 1st.
I read a bit about it on the author’s page. Apparently the authors put the DRM mechanism into the OS that was corrupting program in memory if the program’s disk copy was pirated from another institute. I think it is amusing that it dates so far back.
It is also a partly a wordplay. CROOK spelled “K-R-U-K” means Raven in Polish.The previous version of CROOK was called SOWA – an Owl in Polish.
This sort of thing is what got me into Python. I had typed in printouts of a BBC micro game, and wanted to test it, but the emulator didn’t seem to have a way to pipe my text into it.
I found a Python program that I could hack to turn text into- virtual tapes for the emulator (Whatever they were called.) & was thus able to enjoy playing a game that hadn’t run anywhere in a decade or 2.
The original author of the game was grateful, and I’ve been a Python fan ever since. :)
I looked at the program. It is C++, not python. I’m not sure why the article says it is python.
https://github.com/jakubfi/ninetracklab
Quite right.
Maybe they were confused because the tools directory has some python 3 files. Looks like it maybe generates test data..
That was an interesting read. CROOK is absolutely new to me, as I suspect it may be to most. I have to ask, is “CROOK” an acronym for something? And what was its intent? Was it a general-user OS or was it dedicated to a particular task? Finally, which systems (as in make/model) ran CROOK?
Thanks,
Keith V.
There’s a wiki entry on mera400.pl about it. Unfortunately, it doesn’t mention the name’s origin. The first three versions were written for K-202 machine (https://en.wikipedia.org/wiki/K-202), The third one worked also on MERA-400, later versions worked only on MERA. The wiki says it became a “universal, multitasking and multiuser” OS.
I had no problem finding the origins of name on Mera-400 wiki, which I translated here: http://hackaday.com/2017/03/03/raiders-of-the-lost-os-reclaiming-a-piece-of-polish-it-history/#comment-3429031
You’re welcome…
Also CROOK was similar in it’s capabilities to UNIX, but was written in K-202 Assembly. Even later, Mera-400 only versions were written in that language, extended by few new ASM commands that were available on that CPU…
Am I really the only one that had real troubles reading Polish IT history in all caps?
You are definitely not the only one; I was confuzzled.
Love the story, because I just did some digital archeology of my own, though with 3.5″ floppy disks for pc and Amiga. Some tracks didn’t read well but there was no physical disk surface damage. I modified a drive to tap directly into the dtive head analogue signal, captured it on the rigol ds1054z scope, moved the waveform file via usb and processed it in software succesfully. I learned a lot from this.
That is good use of modern technology.
I remember having a floppy drive in my main computer up to early 2012, otherwise a quite up-to-date machine. To that day it was the easiest way to flash a video BIOS – i was a gamer and serious overclocker at that time, then came more important things like graduating and making a living. :) Oh and booting whatever from USB was made easy.
Coincidence or not, i work as a tech at a company that also does data recovery – but we sure don’t see any tape or floppies these days. Either way, kudos for the team that pulled this piece of computer history intact. Thinking out of the box = win.
there is a kryoflux controller that automates recovering bad floppies using same method http://www.kryoflux.com/
I ran a conversion program on about 200 mag tapes off a PDP-11 system many years ago. A stand alone tape drive connected to a windows PC. The tapes were about 5-15 years old at the time. The 3 worst tapes could not be read as they had gone sticky and would jam in the tape drive. After a weeks work I was able to ZIP up the restructured data and store it on one 640MB CD. Where is the CD’s now?