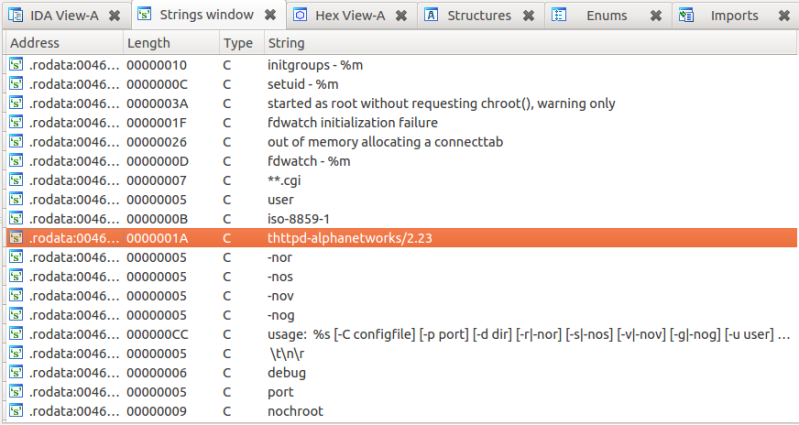
Here’s one true hack (Google cache link) for our dear Hackaday readers. On a Saturday night, as [Craig] didn’t have anything else to do, he decided to download the firmware of an old D-Link DIR-100 router (because who wouldn’t?). His goal was to see what interesting things he could find in it. He fired up binwalk to extract the SquashFS file system, then opened the router webserver on the multi-processor disassembler/debugger IDA. [Craig] discovered that the webserver is actually a modified version of thttpd, providing the administrative interface for the router. As you can see in the picture above, it seems Alphanetworks (a spin-off of D-Link) performed the modifications.
Luckily for [Craig], the guys at Alphanetworks were kind enough to prepend many of their custom function names with the string “alpha”. Looking at the disassembly of the http identification functions revealed that a backdoor is implemented on the firmware. If one malicious user has the string “xmlset_roodkcableoj28840ybtide” as his browser user agent, no authentication is required to gain access to the router. One of the comments on the reddit thread points out that reading that string backwords results in: “edit by (04882) joel backdoor”.
















Very interesting, surprised such a backdoor was added to it.
Interesting. I wonder why such a backdoor was added, and also, why anyone would put their name into it?
I read someone’s assumption that it’s for automated patching, and since users can change the login name and password on the box, that would make maintenance more difficult.. this way they can just make a windows .exe that does it all for you.
Maybe “Joel” works for the NSA?
NSAKEY was too obvious
You assume that Joel is really his name.
His name is Joel Backdoor, obviously.
Oops, accidentally clicked “report” instead of “reply”. Nothing to report here, will now press the nurse button.
Let those not using OpenWRT suffer!
What is OpenWRT? The article is about a D-link Router, did you even read it?
http://wiki.openwrt.org/toh/start#d-link
Note how the router isn’t on that list?
Note that it doesn’t excuse you from suffering.
Therefore he shouldn’t have bought it. Lack of OpenWRT compatibility is a dealbreaker
@Krzysztof Września
Eh, I’m more a Tomato guy.
So, what? Do it like true hardcore men do: Buy the router, port OpenWRT, submit patches… PROFIT!
@Andrew.
Nah, real men use 2900 series routers snagged from the local university’s surplus store.
No one is going to notice that, or notice that most of the routers involved in this problem are 11g or even pre-G devices. OpenWRT has so much bloat that it wouldn’t even fit in the 1 to 2 megs of firmware space that these older devices used. Instead, someone will insist that ‘real hackers would port it’ (oh, someone did that already) instead of porting it themselves because they know the words but don’t understand the device that the article is talking about.
OpenWRT is a community-based custom router firmware used on consumer devices made by D-Link, Netgear, Linksys and several others. I use tomato, personally.
Let me rephrase Andrew’s comment:
Let those not using a superior option suffer!
Since you are not aware of this option for many consumer routers, maybe you should look into it rather than flying off the handle at the mention of something you are not aware of. A 10 second Google search could have helped you a bit.
Exactly. PFsense or other REAL firewall, none of this low end consumer grade junk in my home.
Watchguard Firebox 700 running pfsense for real protection. anything else is just kiddie stuff.
So what is your upgrade path if you ever get fiber or some other service greater than 100Mbps? Serious question, not trolling; while I’m not expecting fiber in my area any time soon, I have a gigabit network within the house and if Comcast makes good on their promise of 100Mb+ speeds here next year, I’ll be in the market for a GigE firewall.
Please provide more intel on your home security setup as well as your external IP address. =P
@kaidenshi
Gigabit capable security appliances are still incredibly expensive. Even fancy enterprise level networks do not generally have any proper firewalls on Gb core networks. The traffic is often filtered in distribution or access, which just doesn’t need that kind of speed.
The only reasonable option for an individual that needs a firewall that can handle that sort of speed is to roll their own out of an old system. Even then, unless the machine is powerful and dedicated, there will be significant latency.
Another thing to consider is practical threats. If everything is configured well including your infrastructure, a firewall isn’t going to do much. It is like having a bulletproof front door and installing a picket fence.
@kaidenshi
pfSense runs on regular x86 hardware too so you can get a small form factor system w/ gigabit ethernet support built in or as PCIe cards.
There is the $99 Ubiquiti EdgeRouter Lite that can route a full 1Gbps
traffic. Smallnetbuilder has a review of it. It is low power and silent
alternative to a PC based solution. It is running a fork of Vyatta 6.3.
What I’m wondering now is if the backdoor is still there in modern devices.
makes me wonder if other (d-link) routers have the same kind of backdoor.
sometimes i use a portscanner in the “home user ip range” of my provider.
i’m always impressed by how many router admin-interfaces are accessable from the web.
the default logins don’t always work ;) a backdoor like this would make things a lot more “interesting” ….
Looks more like a forgotten maintenance hook than a true backdoor. Either way, it’s a good find and a nice hack.
Except that the unlocking useragent says “edit by (04882) joel backdoor”
Justin means that the “backdoor” wasn’t supposed to be in the final shipped product, was supposed to just be used for development and debugging before being removed but someone forgot.
Haven’t had a chance to read the article in full, but I’m fairly sure that binwalk is only used for finding filesystems and the like, and not for doing the actual reading. At least that’s how I use it. If I’m right you might wanna change the description.
Do you even lift?
https://code.google.com/p/binwalk/
Binwalker can automate extraction and loading of embedded filesystems in the binary.
I never found a good reason to leave the router admin interfaces to be accessible from the web.
Thanks Joel for ruining for everyone!
Very interesting. I’ve a D-Link IP webcam, DSCG-900, that I’ve been messing around with. Does anybody have any insight into this webcam? I can’t find any custom ROM’s for it, which is a pity because it seems to be quite a capable device hardware-wise.
DIR-100 is a slow prehistoric non-WiFi model, so probably only have 256
or 512K FLASH and limited RAM and not have the resource to run ucLinux
based firmware. i.e. no OpenWRT, TOmato etc.
If that backdoor is only accessible on the LAN and not WAN side, it
might not be as bad. The intruder would need either physical access or
another hack to inject packet into LAN. If that happens, your LAN would
be a greater concern.
Coincidentally, the CTO of Alphanetworks is named joel. http://www.joesdata.com/executive/Joel_Liu_421313008.html
I wonder if he was pressured into putting it in…
Alpha Networks or ALFA Networks?
I know Joel’s brother, Luke Backdoor. Nice guy. Owns the domain backdoor.com and has the email address luke@my.backdoor.com.
But who is his father?
Actually, I happen to be working with Alpha developing network equipment.
Somebody’s going to face the firing squad here.
You should probably watch the code they insert/inject then :) heh
Possibly some more rants on the same from: http://blog.nsecure.net/2013/10/do-not-trust-chinese-routers-especially.html
“The same string has been found to work on seven D-Link routers (DIR-100, DI-524, DI-524UP, DI-604S, DI-604UP, DI-604+ and the TM-G5240) and two from Planex (BRL-04UR and BRL-04CW).”
-[http://www.bbc.co.uk/news/technology-24519307]
1) thanks for helping me guys, now i willknow where to start on breaking your security ;)
(brand/model of firewall always helps/nessesary in “getting past” it)
2) if internet link is 200ms then what the heck will going from 200+10 to 200+1 goin to do?
aka gigabit instead of 100mb is useless, unless you have 500$/month+ to spend on friber ???
last i checked thats how much residential fiber costs, oh plus the installation, THOUSANDS!
3) a back door in a home router? THAT IS ILLEGAL IN GERMANY !!!
(unsecured wifi)
dlink will loose previlege to sell in germany, or at least get scrutinized
and newer models get inspected for more spyware.
hey that might even open a huge can of worms…
4) (redacted)