[Nils Pipenbrinck] has been working on a very interesting problem. The SIM card in your cellphone talks to the contactless near-field communication (NFC) chip through a cool protocol that we’d never hear of until reading his blog: single wire protocol (SWP).
The SIM card in your cellphone has only a limited number of physical connections — and by the time NFC technology came on the scene all but one of them was in use. But the NFC controller and the SIM need full-duplex communications. So the SWP works bi-directionally on just one wire; one device modulates the voltage on the line, while the other modulates the current, essentially by switching a load in and out.
This signalling protocol makes snooping on this data line tricky. So to start off his explorations with SWP, [Nils] built his own transceiver. That lead [Nils] to some very sensitive analog sniffer circuit design that he’s just come up with.
If you get interested in SWP, you’ll find the slides from this fantastic presentation (PDF) helpful, and they propose a solution very similar to the one that [Nils] ended up implementing. That’s not taking anything away from [Nils]’s amazing work: with tricky high-speed analog circuitry like this, the implementation can be more than half of the battle! And we’ll surely be following [Nils]’s blog to see where he takes this.
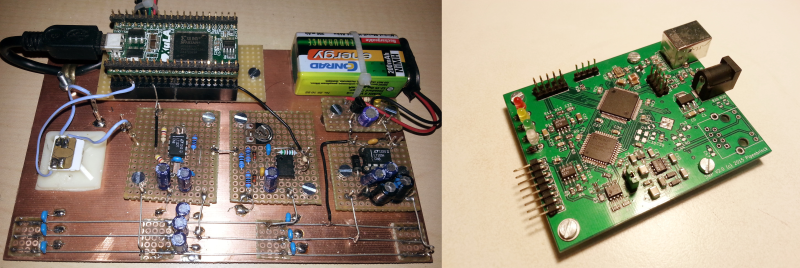
Banner image: An old version and a new version of the transceiver prototype.
Thanks to [Tim Riemann] for the tip!
















Apple MacBook chargers also use the one with protocol to control the charge indicator light. It’s a very interesting protocol :-)
I don’t think SWP and Dallas 1-Wire are the same thing…
It makes me laugh that things like this are so interesting today.
In the analog days we could have bidirectional communications along a single co-axial cable that also provided power to the remote transceiver.
By “bidirectional communications” I mean NOT one, but thousands of different bidirectional channels.
And unlike digital communications that has to wait for the next clock cycle … an analog signal change at one end was instantly observable at the other end.
So, what I am saying is that having *only* one channel over a single wire bidirectional signal path is not a difficult thing … at all!
Except in your analog times, “instantly” was microseconds, now it is nanoseconds. And “small” was “fits in a bag”, and “low-power” was “less than 1 W”.
…and ‘one wire’ was two, because it was *co*axial…
Single Wire Protocol also have two wires. One signal wire and one GND wire.
:o)
Now tell us about how punch cards were more reliable
They were!!! Until you put them in the wrong order and the machine spit them all out allowing for a fun game of pickup.
I never saw a unit record machine throw cards unless it was malfunctioning, never because the stack was disordered.
I saw it in a movie once! B^)
Punch cards were not reliable. They can jam up and cause quite a problem, often they could screw up a number of cards and they would have to be remade since they would be wrinkled and no longer feed.
2 words, Hanging chads
B^)
Let’s not go down some meaningless “analog vs digital” route. What you describe is how cable modems work, and it’s only used for applications requiring that sort of bandwidth because it’s rather expensive (cable modems are what, $10s of dollars each retail). Today the modulation techniques are digital across a coax line, simply because higher effective data integrity and bandwidths are easier to achieve across arbitrary distances. Think analog television vs. digital television.
Single wire buses as described cost approximately nothing in terms of BOM cost, and have enough bandwidth for quick and easily engineered communications within an assembly.
Much as I’m not all that into analog electronics, I just absolutely love the attitude the old designers had of doing as much as possible with what they had.
Now it’s a race to do as little as possible(AKA a “Focused user experience” or whatever the marketing for it is now) with the most resources.
I love modern high res screens, lithium batteries, and GUI interfaces, but it kind of seems like some areas have a little less innovation and a lot more disposability.
All of these protocols are very well documented. And what he is snooping on already has a lot of documentation on if you search the internet in the “seedier” parts of town. Cellphone hacking forums and the likes has a lot of interesting information on this stuff.
Yes, it’s all documented. However, I haven’t found a working transceiver circuit for the SWP protocol online and all the commercial solutions have all been extremely expensive (like 10.000 € for the cheapest device, 30.000+ for one that really works). That’s why I started this project.
The product NomadLAB from the Keolabs company is arround 1500€ with ISO7816/SWP spy and analyser
http://www.keolabs.com/SC-NomadLAB-SPY-CT__product__nfc-testing.html
Arround 1500€ with ISO7816/SWP spy and analyser..
Wha, that’s cheap. Last time I’ve looked (Comprion, Raisonance) they’ve been much more expensive.
Still… Nils, what’s your BOM / cost?
1500€ is enough to keep most any amateur hacker out. (Though it’s less than 10,000!) If this tool lets people play around with the tech who otherwise wouldn’t, it’s a win.
Hi Elliot,
my BOM is about 50€ for singles. If I would replace the expensive Linear chips and calculate for 100 pieces it’ll obviously much cheaper. I guess i’ll end up around €30 or so. My project doesn’t aim at sniffing the traffic. That was just a byproduct of the analog design (I may add that to the next board though). I focus on talking the SWP protocol and interface with the SWP SIM just like an NFC controller would. Including the very interesting CLT protocol which sits on top of the SWP layer. That’s more or less raw unmodulated RF data. Plenty of of opportunities to exploit here because I can emulate completely illegal RF frames and sequences and see how the SIM behaves.
Interesting, did you look into the higher levels of the protocol?
Maybe the osmocom project (http://osmocom.org/) would be interested in your work.
The project description from its page is:
“The Osmocom project is a family of projects regarding Open source mobile communications. It includes software and tools for a variety of mobile communication standards, including GSM, DECT, TETRA and others”
They have several project related to SIM cards, including a SIM card
trafic shiffer (http://bb.osmocom.org/trac/wiki/SIMtrace) and a program
to easily dump the list of the permission the modem gives to the SIM (https://terminal-profile.osmocom.org/)
Denis.
I think it’s great that this is getting investigated. As a recent defcon talk involving writing custom firmware for a sim card brought up, sim cards are actually really powerful little systems in their own right. They were in fact originally intended to *be* the cellphone itself, while the cellphone they fit into was supposed to be a dumb, interchangeable shell, much like those laptop shells that would have taken a cellphone but instead people are fitting with a PI zero.
Anyway, with NFC becoming a real thing, especially with paying for things, it’s good to have someone having a look at things and paving the way for security research. I’m not too thrilled about having my cell carrier also having a more or less literally physical backdoor into my bank account.