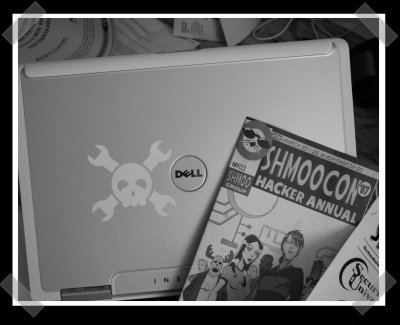
[Eliot] and I are in D.C. at Shmoocon for the weekend. We’re armed with the latest Hack-A-Day sticker. Find us here and we’ll hook you up. Right now we’re checking out [H1kari]’s talk on using FPGA’s for high speed encryption key cracking. By using dedicated FPGA hardware, they’re smoking dual core Intel’s left and right for the calculations. He also talked about an interesting application called VileFault – it takes in a certain fruit vendors encrypted FS and spits out a decrypted image – once you’ve cracked the pass phrase. (Guess what makes finding that key way faster.) Now he’s getting into brute forcing bluetooth pins…
[Update so I don’t run off the page…]
The con’s first round of talks was pretty interesting. I definitely enjoyed the keynote by [Aviel Rubin]. He discussed his teams efforts to crack the Exxon Mobil Speedpass, which happens to be the same technology that’s used to RF disable several newer cars. They used some FPGA in a similar manner as [H1kari] – to speedily decrypt the encryption keys. The defeat of the Speedpass is pretty old news, but it was heartening to hear how Johns Hopkins University stood behind his team and was happy to saddle up their lawyers in dealing with the release of their paper.
The boys over at team hack-a-day – our unofficial Folding@home team (#44851) asked me to remind people that the PS3 folding client has been released – give those spare cpu cycles a home! The team has their own forums that hold quite a few gems. Not the least of with is a handy DXF of the Hack-a-day (and team Hack-A-Day) logo.















Fiiiiiiirst :P
Does VileFault has to do something with FileVault :) ? Sounds similar to me :PP
No, Ondra, by fruit vendor I think they meant BananaFS or something.
damn, i don’t have a ticket. I live around DC, and I’d love a sticker.
How does one go about getting one of them spiffy stickers?
But the thing is that it may likes the other peoples too. Any guess why??
mmm stickers, pity I live about as far away from dc as you can get (actually as far away from the usa as you can get)
where, when and will I be able to DL videos of the talks?
My 96 Honda Prelude had a transponder chip key stock..Not exactly “newer cars.” Interesting because the Acura Integra didn’t get chip a key till 2001 when bills started being passed in congress.
I think the Corvette got a TI based chip key in the late 80’s. GM also used PASSKEY 1 and 2 which was resistor based and was a no brainer to bypass.
If you wanted to save some time you could just buy a cloner and key blank. In CA chop shops they get the VIN for a target car and just get there professional mechanic buddies to get the pre-cut blade and code the transponder with an in shop cloner.
The FPGA encryption cracking is cool, but backpacking an FPGA array around wouldn’t be practical for a thief.
Has anyone ever done FPGA tests on other ciphers like A5 or triple DES?
is there a link to learn more about their FPGA cracking efforts? how many FPGA’s do they typically use in tandem (or, do they use use one?)
thanks
man this sucks if it was last week i so would have been there but now im off of break and in the middle of nowhere PA
#8: I don’t see how backpacking a FPGA around would be impractical, as my 500K gate FPGA is barely an inch square – and that is probably overkill for this application. You might need some buttons and an LCD, though :)
#10 They where using an FPGA array hence it being impractical. Not sure what cores the FPGA’s used but you could be right. They might have been able to use a single board with a faster core.
Also I followed there research for a few years. I seem to remember them being forced to remove details from there site not even a year ago by some corporate lawyers. That’s why I stopped paying there research any attention.
Also the transponder ECM system is the best security measure out there currently; even better than rolling code systems. They’ll have to go back to the drawing table if the transponder chip ECM system becomes too easy to crack.
if there are leftovers can we send in SASE’s and get a sticker?
I’d put a hackaday sticker on my laptop in a heartbeat.
I’d even send in a photo of it.
Wow, that sticker looks awesome. Any chance that you guys could set up a send in money, get a few stickers thing for the ones unlucky enough to not be able to do?