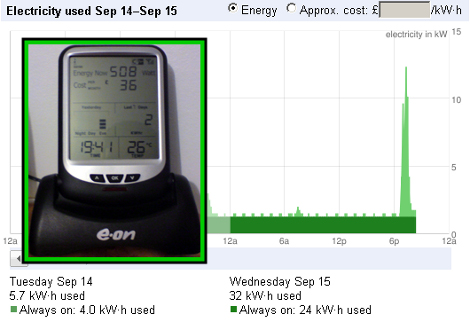
[Graham Auld] got his hands on an energy monitor for free from his utility company. The device seen in the insert provides a nice LCD display but he wanted a way to graph the data over time. There was an included cable and a method of using Google PowerMeter but only for Windows computers. He did a little poking around and came up with a Perl script to interface the meter with Google’s tools.
The hardware module is known as the Current Cost CC128 and the developer was nice enough to publish an XML output description which [Graham] used in his script. From there it’s just a matter of registering and authenticating through the Google PowerMeter API. The script is not fully polished yet but it serves as a road map for your own implementation.















So, How EXPENSIVE is this thing?
@HARaaM If you followed the links, you’d see it was being sold at various UK places for about £39.95
You now no-longer need a PC running perl. CurrentCost have started shipping their BridgeUnit, details here: http://hotzone.org.uk/currentcost-bridges-arrive-with-customers/
Smart meters are popping up now here in the states… I wonder how well that will work for us yanks (as some brits like to affectionately call us).
@jh No reason why it shouldn’t work since you report kW usage to google.
They have a ebay store that they are selling these things from.
http://stores.shop.ebay.co.uk/Current-Cost-Ltd__W0QQ_armrsZ1
It also seems they don’t currently have a north american distributor…
I’ve been watching the smart meter market for a while. This looks like a good start. I’m a big fan of their openness to 3rd party developers.
Wow, they’re very hacker friendly. They’ve produced simple rf transmitter boards that interface to their monitoring controls.
Do a search for “Current Cost Development Board” and you can find them online. Looks like this opens the possibility of monitoring whatever you like. A quick look says that each board uses one channel of Analog input that it transmits back to the base station.
Why exactly do people upload their power consumption data to Google? So they can show advertisements for frozen meals while you are using the microwave?
It is possible to profile energy consumption data and find out which appliances are currently running, nothing I would want Google to know.
I also don’t want Google to know my energy consumption but the only access I have to my smart meter data is through Google Power Meter. The only reason I “opted-in” to use the Google service is because there is no other choice if I want the data from the meter.
All I get from the Power Meter app is a few graphs and the ability to download my own data. Google on the other hand gets all of my energy usage data to some unknown level of detail. Over time and combined with usage from other homes, they could very well determine what appliances I’m using and when.
I purchased a zigbee smart energy gateway so that I could read the data directly from my meter but that functionality is not currently enabled on the meter.
@johannesburgel paranoid much?
@jones
Maybe but he has a point… I have implemented something simular just trough our regular power system (it’s a service offered here in denmark, each house who get’s it’s power from SEAS-NVE automaticly transmits the power usage over long distance wireless network, back to SEAS, and it’s letting everyone track their power usage online)
However their website sucks so I’m just scraping data each day and plotting it into my own MySQL database. Anyway, can’t see the need for sending this to Google or any other 3. part?
@jones
nothing paranoid about it.
maybe he doesn’t like volunteering to help data-mine his own life for gigantic unethical corporations??
gosh!
Have a look at rrdtool, does some nice graphing without the need for google. but it does need a local machine on.
Google actually have a vested interest in getting everyone’s power usage down – power is by far their biggest cost, and unfortunately they use most of it when we do – evenings, and latency means that datacentres need to be on the same rough timezone as users.
If google knowing your power habbits, don’t tell them much about who you are and use tor when viewing the results. Don’t forget your tinfoil hat though – StreetView cars have waaaay too many aerials :-)
You could use a webcam and some basic image-grab->OCR script to monitor a LCD display of a device without interface options. (irfanview on windows does basic OCR using an external plugin so I guess basic OCR stuff is freely available.)
Or read the data lines to the display and run it through an interpreter (arduino?), although you need some circuit to boost those signal lines, I can’t recall what signal levels they run at but it must be pretty damn low, and as a drawback you can’t read the display anymore on the spot then, unless you fork the input back at the right levels and find a way to feed them back again to the LCD, which can be tricky since such LCD displays always seem to use the small rubber with conductive parts as ‘connector’.
What are those called anyway? those rubber strips with conductive parts.
Think this unit will accurately work on 60HZ?
@Whatnot: I’ve seen those referred to as “zebra strips”. Generally, bare glass (no controller on the glass, as is often the case with consumer gear) is driven with multilevel voltages. So you’d have to do some work with comparators to differentiate the different drive voltages. If you have physical room to make the connections, though, you should be able to read the signals and use the display simultaneously, since your comparators could have high impedance inputs.
In practice, though, almost nobody gets display data this way. It is a lot of work. If you’re just looking for a hack to do, though, it should make for a decent exercise.
@Dom De Vitto
I see nothing stopping anyone from using a dummy google account that has no other personal information. If you did it right you could avoid being profiled.
You cannot escape google. Seriously.
You think you’re clever with your cookie clearing and multiple email accounts, but it accomplishes absolutely nothing. You might even be using a chain of proxies, or several computers, but that won’t really help you, either. All you can do is pretend that it does… but it doesn’t.
Ask the EFF – it’s trivial to identify you. Even they agree that it’s almost hopeless, apart from legislation… yet even the legislation they want will have more loopholes than the fair credit practice act.
Google (and other firms) keep dossiers, and has done so for a long time. Why? Because it’s trivial to follow you around the internet – even if you switch from dsl to cable and back again.
The bad news is that even your most well thought out anonymity schemes are trivial to figure out – and subvert. Having comprehensive maps of individual behavior is valuable to many firms and organizations, who will gladly pay for it.
It’s trivial. It’s even more trivial to associate all your email accounts – no matter how anonymous you think they are, and tie it to your real address and name – and thence to your credit history… and cellphone data. Think this is a paranoid rant? It isn’t – check your state’s privacy laws and notice that call info is not considered private, and can be sold or traded.
Your cellphone data pretty much allows companies (or people in the companies) to map where you spend your days and nights, and makes it trivial to accumulate pictures of your daily activities… not to mention archives of any photos snapped by your camera. And now that it’s trivial to record, compress and store speech, every conversation you have is recorded… for what are euphemistically called “voice quality maintenance purposes”.
Isn’t that cool.
BTW, the image capture function in modern cellphones can be triggered remotely… as can the microphone. That applies to most laptops as well, and apple just created a small tempest by patenting the ipad’s ability to identify you… and measure your heartbeat as a side effect.
Anyway – the bottom line: Anonymous accounts and throw away cellphones don’t fool anyone but some stranger you tried to hook up with. They don’t fool law enforcement or the people who make a living from collecting your data and filing it away.
PS – my usual disclaimer:
I don’t care about this state of affairs, or “the constitutionality” of it. That document (as GWB said) is a useless paper that doesn’t even apply to technology anyway. I am simply miffed that I cannot subscribe to my own data set… which would be incredibly useful to me.
Now I know it gets thrown around a lot, at me too, but you are actually paranoid bilbao bob.
And don’t get me wrong, much of what you say is true, the feds did activate the mic of cellphones remotely in documented cases, but they had to upload a modified firmware first, and there are many ways to link and track people, but you just go a step beyond reality, you CAN prevent a lot of it, and it’s impossible to sift through all the trillions of bits of data, you have to be targeted, even for commercial purposes they would run a script and do basic stuff to get some demographic numbers and maybe do some targeting of personality types for ads, but it’s just not economically viable to put an analyst on every person on earth, especially since then they would have to hire every person on earth to analyze eachother.
And linking emails isn’t so easy unless you actually help them by using them interchangeable or from the same IP, I mean yeah if you make 2 gmail accounts and read them using the same IP right after eachother it’s easy obviously, or if your contacts are the same, or if you don’t disable google scripts that are on 98 out of 100 webpages.
But your scenario of using a chain of proxies and different browser and not being able to foil google.. that’s just a bit out there.
Oh and you have a fetish for the word ‘trivial’ it seems, so yeah that would make it easy for analysts to spot you :)
Wow that meter is a overpriced piece of crap.
the TED is cheaper and has all that PLUS an open API already in the docs.
@Whatnot
I’m not making it up.
I disable javascript; I block known google and google-partner IPs with hosts; I avoid social media; I even periodically blow away flash cookies [which make regular cookies look impotent] and yes, that marks me as paranoid… But I’m french, so there it is.
However, when one accidentally sees a query run on an old account and is rewarded with a list of linked throw-away email accounts, locations, dates and from/to headers, one realizes that the game is over.
Is it total? No. But your mistake is in assuming that what you write is true:
“it’s impossible to sift through all the trillions of bits of data, you have to be targeted, even for commercial purposes they would run a script and do basic stuff to get some demographic numbers and maybe do some targeting of personality types for ads, but it’s just not economically viable to put an analyst on every person on earth”
I never said that each individual had a watcher. I simply said that the data exists, can be correlated and stored, and that this is being done on a growing scale.
– impossible to sift? Au contraire. Drawing conclusions is hard, but sifting is very easy.
– trillions of bits of data? Not even. An average cellphone user log containing call lists and cell location data for a week is <16k of data plus some account overhead. How big must a database be to profile the whereabouts of 1 million cellphone users? ~20 GB. I assure you – an off the shelf $600 PC is more than enough to keep tabs on several million people.
But you were probably talking about web and email usage. I'll just suggest that if you're using throwaway email accounts, you might take a few moments and peruse the HTML source of the web interface. The web may be stickier than you think… and the proxy thing is designed to foil MITM attacks, but it assumes that there is no way to correlate between ingress and egress.
I have no doubt that a well-disciplined and well-connected uber hacker following strict protocols could maintain multiple identities on the web. But I also think that joe "I know who schneir is" public and jane soccer mom ought to know that it's trivial [ :) ] to link their personal porn, private interests and political habits with their public persona… and that of their friends.
Again, my complaint isn't that it's being done – it's just that I want to subscribe to my own panopticon data. I forget everything!
One last silly comment –
Don’t think for a second that Google’s collection of Phds and nutty hackers are content to rely on google analytics scripts. Too many people block them or disable javascript. They know this… they’re smart guys who make Microsoft look like an amateur clown show.
The real work is being done increasingly on the server side by post-processing logs from various included elements – as simple and innocuous as a CSS include file or a spacer.gif file.
Oh, you could disable images, scripting and flash, and get ahead of the game for a few months, but in the end, there’s no point.
While the odds are good that you might have multiple networks/ip addresses that you use, but they’re a lot more stable than you think.
Now if you’re using an ipad, or a smart phone, or 3G, you’re already linked to your credit card. Use something like gmail, msn or yahoo? linked. Ever buy something online from a big name website? linked.
Use a semi-public work network with other people and assume that you’re anonymous? You’re not. We’re way past that now – you have a signature, and it’s getting easier and easier to detect.
Here’s the funny thing: I like this stuff! It’s very cool – and the possibilities are endless. I don’t think that “the government is out to get us” or “the web is evil!”. I think it will allow very big improvements in government efficiency and prevent crime and fraud, not to mention allowing us to quickly identify and remove trouble makers, criminals and sociopaths.
There are a lot of precedents for such tracking activities, and without them we wouldn’t have a usable census or a way for governments to provide us with benefits or law enforcement, or even immigration control.
or anyone in the UK IAM’s (Individual Appliance Modules) are now available to order
More info here:
http://hotzone.org.uk/currentcost-iams-available/