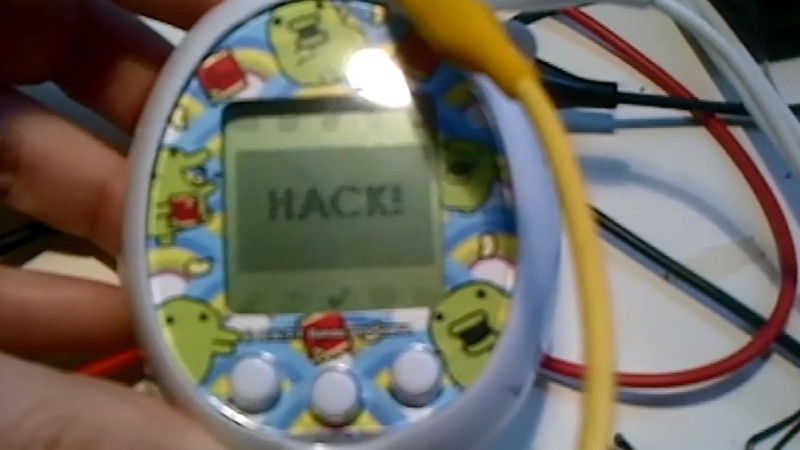
In this strangely fascinating talk, you can follow along as [Natalie Silvanovich] reverse engineers some Tamagotchi. Even if you have no interest whatsoever in digital pets, you’ll probably pick up a trick or two by listening to how she went about taking over the toy. She can now push her own images to the screen, and evolve her Tamagotchi at will.
Listening to her story you might be able to pick up a few tricks as she takes almost every angle possible. She uncovers the black blobs, she attempts to socially engineer her way into datasheets, decaps chips, she dumps and breaks down code. It is also worth noting that, in the beginning, internet electronics enthusiasts were adamant that it just had a PIC processor inside and they were wrong. Having an internet full of experts is a wonderful thing, except when it isn’t.
Then again, having that internet full of experts might be her savior in the end, she’s missing a piece of software and asking if anyone has it available.















There are a lot of largely fascinating talks from 29C3. One of the most interesting ones I’ve seen was the Cisco phone hacking ones, from the same guy that hacked HP printers last year. You can stream/download all of the talks from http://events.ccc.de/congress/2012/wiki/Documentation
Cool! Why don’t they put this stuff on youtube?
Feel free to put it there. ccc relies preferably on own infrastructure.
Thank you for posting this. A lot of people tweeted that it was one of the better talks, but then I couldn’t find it anywhere.
I wonder if she’s willing to share the data she managed to pull of the chips. Sounds like it’d be a trivial thing to get up and running in MESS.
at the end she says something about it all being on github.
Thanks for the heads-up Caleb, I’ll be sure to check it out. :)
Doesn’t she say that the actual code haven’t been dumped?
on github are the hacking tools.
ill fart randy. (old school tami hackers know what this means)
I love how there’s a lot of armchair hackers… ooops, morons that insist that every microcontroller based device out there uses an AVR, PIC or more recently, ARM. It’s like those morons can’t conceptualize the idea that a 6502, or any other architecture for that matter, can actually be a microcontroller core.
I guess it’s a second generation of Internet Experts. The first one grew up with PICs being synonymous with microcontrollers. The current one does not even know much about microcontrollers but remembers some PICs.
Don’t know what generation number I’m in, but circa early 90’s I grew up desoldering IC’s from matrix printers, vcr’s and anything with a hint of digital to salvage whatever looked like a controller or RAM/EEPROM. Then off to the library with a list of numbers to photocopy the specs from the dead tree catalogues. Most of us (we had a club) were programming without knowing the controller family – the serial numbers were often variations with long suffixes.
Yeap, PICs aren’t even that price efficient for jobs like that.
Isn’t that where everyone hacks from? Their armchair.
My pet peeve is EE types that don’t know much about OS design, network integration or much anything bigger than a microcontroller yet claim they know all about computers, servers, and networks. It’s like a dentist deciding he is an expert on knee replacement surgery.
It’s always 6502!
Stupid kids today…
You’re very mistaken. It’s a z80.
It’s not. Where did you listen it was a Z80?
EVERYTHING is a Z80.
For the longest time, I was given to believe that PIC was Programmable Integrated Circuit, which would make it synonymous with microcontroller. People are idiots.
Still waiting for someone to hack a way to reset single use temperature loggers.
I don’t know what you are talking about, but it sounds interesting! Would you be so kind to be more specific? :)
In the talk she mentions that there are high resolution die photographs on her blog. I could not find any at http://www.kwartzlab.ca/author/natalies/ . Any pointers?
Other than suspected in the talk, the mask version of the chip still has the test interface present: The datasheet lists a test input pin and in the memory layout, there is a “test program area” and a “test interrupt vector”! I would guess that toggling that pin (or holding+reset) will execute a test program.
The only challenge might be that the test pin is not accessible on the pcb or it might not be bonded to the pcb (high resolution photographs!). It you are lucky, the epoxy removal process could leave the chips working tough!
The highest resolution that I could find is uploaded to Travis Goodspeed’s flickr account (assuming they’re the person that graciously decapped the chip). You can see it here: http://www.flickr.com/photos/travisgoodspeed/5713302509/ (go to Original Size; It’s 5684 x 5715px)
Wish the pictures were a better, but it gives an better idea of the IC at least.. I’d like to decap them on my own but I have neither the nitric acid nor the necessary microscope.. Being able to “dump” the mask ROM right from the chip itself would be a dream.
-returns to hours of looking at datasheets and trying to find FortisIDE and everything else Tamagotchi-hacking related..-
exceptional
The link is dead. https://www.youtube.com/watch?v=KxeA33yhm7o seems to be the same thing the original one was.