Bose, every salesperson’s favorite stereo manufacturer, has a line of Wi-Fi connected systems available. It’s an impressively innovative product, able to connect to Internet radio, Pandora, and music libraries stored elsewhere on the network. A really great idea, and since this connects to a bunch of web services, you just know there’s a Linux shell in there somewhere. [Sara] found it.
The SoundTouch is actually rather easy to get into. The only real work to be done is connecting to port 17000, turning remote services on, and then connecting with telnet. The username is root.
The telnet service on port 17000 is actually pretty interesting, and we’re guessing this is what the SoundTouch iOS app uses for all its wizardry. [Sara] put a listing of the ‘help’ command up on pastebin, and it looks like there are commands for toggling GPIOs, futzing around with Pandora, and references to a Bluetooth module.
Interestingly, when [Sara] first suspected there could be Linux inside this box, she contacted Bose support for any information. She figured out how to get in on her own, before Bose emailed her back saying the information is proprietary in nature.















Nice! One of the first things I’d have done is sniffed the traffic from the mobile App. That’s how I found out how to control some generic Wifi bulbs :)
Being able to connect to internet radio, fileservers etc is not innovative. There’ve been audio systems doing that for many years…
I use a $40 chinese android tablet with some spare computer speakers to play music from samba shares as well as act as an alarm clock. Sure, the sound output is not quite up to Bose quality, but it’s also a fraction of the price.
Now you should just find out what the os exactly is and if they use any GPL software.
proprietary using linux? if it truely is linux something should be published by bose I know not all but something..
now in reality do i expect bose to publish anything at all…..no. but they should
You can (and many do) implement something that is largely proprietary on top of Linux, after all it’s a fairly rare product where the innovation is actually at the OS level; but if Bose Legal thinks that just saying “It’s a black box, go away!” constitutes GPL 2 compliance… They might need to work on that.
but if you hand out GPLed code produced binaries, you are required to give a reference where to find the sources, even if you did not change it. At least to my understanding.
So not giving away the info about which kernel version and so on might be forbidden by the license.
Being forbidden by the license doesn’t mean much if they can afford bigger legal fees than anyone who gives a shit. Not right, not fair, but I’m not sure there’s a good answer.
Yeah, that worked well for Linksys…
Yep, money talks, bulls*it walks so all I can say is GPL better have some good shoes.
This is the exact reason the FSF encourages people who license under the GPL to assign copyright to the FSF: so when a project encounters a GPL copyright violation and the violator is unreasonable and behaves with bad-faith, they can take an GPL violator to court in order to enforce compliance with the copyright.
Nothing is required if you don’t produce any derivative code. If the code you’re building off of is already available, without modifications, from another vendor in source form, then you’re in the clear to go 100% binary. The code you run on the machine does not have to be open source.
no snark here, genuine interest: has this been defended in court?
The article forgot to say that the username is ‘root’ and the password is .. wait, there is NO PASSWORD!
Right, a completely unsecured root shell on an internet connected device that is being sold to general public. Even better, one can get the root shell remotely!
I was going to write whether this thing is secure against exploits like the recent Shellshock bug, but no need, it comes with a free backdoor already!
Why are hardware companies shelling out millions for nice looking product design but then outsource firmware writing to the lowest bidder producing atrocious crap in the process? I am really wondering whether we should start treating all these “smart” devices or “Internet-of-things” gizmos as “hacked by default” because of the universal incompetence of the manufacturers. Soon my fridge is going to attempt to steal my washing machine credentials so that my bank account could be hacked :(
Have you confirmed that the device actually allows connections from non-local IP addresses?
Thankfully most home users are behind a NAT by default so accessing this thing remotely wouldn’t be possible.
its a feature.. in bose russia, speaker listens to you.
Oh /. how I miss thee…
Not only that, but speakers are just poor microphones.
So what is it you’re afraid of happening? Not a snipe; I’m seriously asking. I’d assume they stripped down the install enough that it’d be non trivial to get the speaker to DO anything other than play unwanted audio.
Having an unsecured node open to the internet gives attackers a nice vector to probe your internal network. What they do with that is up to their imagination.
Or just brick the device remotely and force the user to shell out for a new one.
Also thinking of nefarious hacks that use the speaker as a microphone instead, or some other wizardry.
Because unlike you or I, most consumers could care less about security, in fact most relish in the fact that they can use their internet radio **anywhere**, or do their banking at the !!AIRPORT!!. or have their refrigerator send shopping lists to whole foods or whatever.
Why would any company invest in technology that user doesn’t know exists or cares if it does. It’s not going to boost sales or even limit sales. For most, it just doesn’t matter.
Is this a problem? Yes, but these are the times we live in.
There’s a relatively high barrier to entry for hardware, but any stupid asshole can call themselves a programmer, and the suits in charge of the project aren’t equipped to tell the difference. If it were possible (and it is possible for some products) for stupid assholes to make atrocious crap hardware without the suits or most consumers noticing, they would.
Another asshole big player, that is taking the communities work without giving anything back, not even credit.
And even worse, they are too dumb to implement the faintest hint of security.
Don’t touch them with a ten foot pole.
WAS proprietary….:)
Can someone who has bought the device please report the product’s GPL violation?
http://www.gnu.org/licenses/gpl-violation.html
I have a Soundtouch speaker, but I don’t have the original packaging or paperwork anymore, but out of curiosity I went scouring though the Soundtouch Android app I use for it and buried in the settings there is a link to licence documents which do mention GPL and several other licences they use.
“The telnet service on port 17000 is actually pretty interesting, and we’re guessing this is what the SoundTouch iOS app uses for all its wizardry.”
More random bits of unsubstantiated nonsense from Brian Benchoff. It’s highly unlikely they would open a telnet session from the iOS app and muck around with parsing ASCII strings. Any competent designer would use something off the shelf — like SOAP or REST.
While I agree that Brian barely makes any sense at the best of times I don’t see why it’s impossible the iOS uses the “telnet” port. It’s just a socket with text being sent back and forth..
>muck around with parsing ASCII strings.
>like SOAP or REST
Both of which would involve parsing “ASCII strings”.
There’s no reason that the “telnet” port couldn’t go into some lower level less human friendly protocol. Why would you bother with SOAP when you could do all you need with a simple field and delimiter protocol?
Because the iOS libraries for parsing http queries are well established and trivial to use.
Why get into lower level networking when you can send an http request with half a dozen lines of code at most?
Precisely.
Can you give me a hint, i would like to control the sound touch via url in my browser.
Looks like they’ve closed it down in the latest release – the only command at the port 17000 “->” prompt not reported as invalid is “help”. This includes “remote_service on” so it’s not clear how to enable remote access any more either.
Has this officially been closed? Was there any mention of this from Bose?
It was never officially open, so No. Also there’s a full developers API available from the Bose site that details hoe to drive these programatically using XML over HTTP.
Just got one myself. Port 17000 is still open over telnet.
I also discoved that there is a websocket on port 8090 that returns XML.
If you run webserver stats on the box and you’ll see something like this :
-> webserver stats
========================
mostRecentMSTimeInCURLSend = 127ms
mostRecentURLSent:
‘http://localhost:8090/volume’
maxMSTimeInCURLSendSoFar = 1039ms
URLForMaxTime:
‘http://localhost:8090/swUpdateCheck’
========================
WebSockets Total:
TotalIncomingMessagesOverWebsocket = 53
TotalOutgoingMessagesOverWebsocket = 65
RequestsToBoseAppCount = 53
ResponsesFromBoseAppCount = 53
NumberOfOutstandingRequests = 0
NotificationsSentOverWebSocket = 108
NumberOfCURLErrorsReported = 0
LastNotificationSent =
MaxAllowedRequests = 50
NumberOfOverflowErrors = 0
WebAdapterFreePoolListCurrSize = 50
Hello, I have been reading a little about soundtouch, because I live outside US and the BOSE server recognizes my location blocking the iHeart Radio app (the one why I bought this) This happens even downloading the iOS app from US ITunes account. I tried to use this account, because the iOS iHeartRadio app downloads and works perfectly outside US if you downloaded it with a registered US iTunes store account.
So, I would like to know If there is any chance to modify this and avoid the BOSE server to find out where am I…I already denied location use by the Bose app and it did not work.
I hope someone can solve this issue.
Obs: I know that using the iHeart app with AirPlay works…but the idea is to be free of my phone/iPad to listen to the radio.
Thank you and have a Fantastic 2016
All said, is it possible to mod these knowing all this info? All the GPL violations aside, still a clearly hackable device :D I have the Soundtouch 300, I would love to be able to add a second pair of Virtually Invisibles to the setup. Bose has stated it only supports a single pair. But if the OS is controlling the hardware, then it should be trivial to unlock that if its handled by the OS.
Hi,
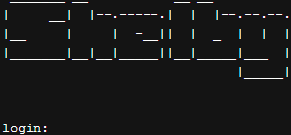
– Connect a USB/serialTTL converter to the 3,5mm “service” plug TX=tip, RX=ring, GND=GND
– Use Putty or similar at 115200 to view the boot process when powering on the soundtouch system-
– See Uboot, kernel and busybox until login prompt.
– Login as root, no password, you get: root@lisa:~#
– root@lisa:~# touch /mnt/nv/remote_services
– root@lisa:~# /etc/init.d/sshd start
You are finished now with the serial interface and can login with
ssh root@ipaddress.
This persists on power cycles.
To disable sshd you have to delete the file /mnt/nv/remote_services.
A USB-Stick is mounted automatically onto /media/sda1.
/dev/sda1 on /media/sda1 type vfat
(rw,relatime,fmask=0022,dmask=0022,codepage=437,iocharset=iso8859-1,shortname=mixed,errors=remount-ro)
So you can store your mp3s on the stick and the system will see it.
This is where I need help. Can somebody build a kind of microdlna
server that we run on the system (maybe from stick), that reads the
mp3-files and stream it via the net. From there we could play it
with the system as a dlna client.
Bose refused to give me links to the open source used under GPL.
Some insights:
root@lisa:~# uname -a
Linux lisa 3.14.43+ #2 Fri Jun 23 20:38:40 EDT 2017 armv7l GNU/Linux
root@lisa:~# busybox
BusyBox v1.19.4 (2017-04-14 14:30:45 EDT) multi-call binary.
Copyright (C) 1998-2011 Erik Andersen, Rob Landley, Denys Vlasenko
and others. Licensed under GPLv2.
The device supports NAS drives through UPNP, so you don’t need to host the files on the device for any reason.
I have a Bose SoundTouch 30 and the procedure to connect is a bit different than the ones stated above.
1. You need to use the aux plug with a 3.5 mm jack to connect to the speaker. You need to use 4-pole connector and use the 3rd and 4th pole (second ring and sleeve). This will give you the possibility of receiving the boot output, to send data (commands) you will need to somehow connect to the pin on the outside of the connector (search for Bose SoundTouch 30 service manual and you will find a schematic). Furthermore, you need to use a USB/serialTTL, baudrate 115200.
2. If you follow the step above you seem to be already authenticated as root (the drive is mounted as read-only but you can remount it).
3. If you want to issue TAP commands, you will have to connect locally to port 17000 (telnet 127.0.0.1 17000). Unfortunately, the only commands that seem to work are: ‘async_responses on’ and ‘local_services on’, the rest don’t work, even if you type them several times.
How I discovered all this?
I bought the speaker from Facebook Marketplaces, and big surprise, it is not working. Meaning that it does not boot all the way, it stops at around 80% on the small display, the only button that seems to work is AUX (if I keep it pressed long enough it will cause a reboot), trying to update the firmware fails (all these methods fail: USB stick, micro-USB stick, micro-usb connected to computer). After using the procedures described above I managed to get a command line working. The interesting part is that the operating system does not detect the USB, wifi or ethernet – maybe a board is dead? However, the speaker connects to the wifi and if I plug a cable it also connects – but I cannot see the devices (ifconfig, ip link they only list the loopback connection). If I manually run the BoseApp I get a segmentation fault.
Don’t expect anyone to be able to help, but I want to contribute with the steps I used to get the command line.
Are you still having issues with this? I may possibly be able to help
I bought 2 SoundTouch 10 and discovered that them auto turn off in few minutes.
Some body know the way to change this configuration?
Br
I tried the bluetooth and volume + hold as well, however, did not hear any tone. How long am I supposed to hold it? 30s? 60s? Thanks
My SA-4 does not recognize any commands sent at port 17000 and refuses on other ports.
Is this what I need to connect the 3.5mm to the PC?
https://www.amazon.com/Adapter-Serial-Converter-Development-Projects/dp/B075N82CDL
My solder-fu is weak, but time is cheap now.
I can’t figure out how to edit or delete posts, so apologies for the clutter.
Connecting to the micro USB Setup port with a regular ‘phone cable worked for me.
PuTTY telnet to
203.0.113.1
port 17000
–> sys timeout inactivity disable
Might require entering the command twice.
The speakers still ‘pop’ when I activate after an extended period, indicating that the amp powered off. Dammit.
Source hint:
https://www.bose.com/en_us/support/article/updating-soundtouch-sa4.html
BoseApp version: 24.0.7.46067.3722005 epdbuild.trunk.hepdswbld05.2020-01-29T17:25:57
I recall seeing another command related to auto power off but I can’t find it now.
This help list dump is sort of useful but outdated, I think, as some of the commands are not recognized:
https://pastebin.com/EwPKS26G
‘?’ and ‘help’ are not recognized commands on my SA-4.
All I want to do is disable the auto power off.
Does the Soundtouch 20 need a 5-pin jack for Serial? Is there a shell in the Cinemate 120 or only with the Soundtouch adapter?
I tried the bluetooth and volume + hold as well, however, did not hear any tone. How long am I supposed to hold it? 30s? 60s? Thanks