[Milosch] wrote in to tell us that he has recently released a bootable RFID live hacking system – something he has been diligently working on for quite some time. The live distro can be used for breaking and analyzing MIFARE RFID cards, as well as a reasonable selection of other well-known card formats. The release is based off the Fedora 15 live desktop system, and includes a long list of RFID hacking tools, as well as some applications that allow for NFC tag emulation.
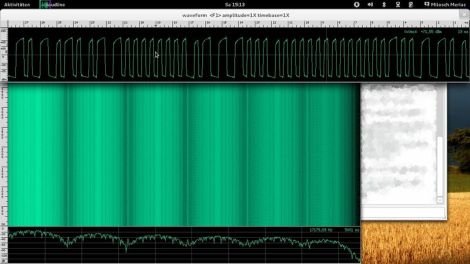
His toolkit also contains a baudline-based LF RFID sniffer package, allowing for a real-time waveform display of low frequency RFID tags. The LF sniffer makes use of a cheap USB sound card, as well as a relatively simple reader constructed from a handful of easy to find components.
We have seen some of [Milosch’s] handiwork before, so we are fairly confident that his toolkit contains just about everything you need to start sniffing and hacking RFID tags. If you’re interested in grabbing a copy of the ISO, just be aware that the live CD is only compatible with 64-bit systems, so older laptops need not apply.
















Sounds very interesting. It’s only a shame not being compatible with 32bit processors.
I’m all for keeping up with the latest and greatest…but come on; little early to bail on 32 bit completely isn’t it?
That sniffer hardware is neat though, might have to check that out.
I’m thrilled to see baudline [0] in the screenshot! Baudline is a phenomenal signal analyzer that has been used to investigate audio, radio astronomy, and now RFID!
[0]: http://www.baudline.com/
I agree it’s a bit early to bail on 32 bit. L learned long ago if you are a doer, and you would like to take advantage of what the doers are doing, you pretty much need to use what they use.
In light of the artist dude taking, posting photos of people using computers in a store found his booby in the wringer, I’d be curious what trouble there might be using RFID readers with tags you don’t own. My my assumption is just passively receiving the data that a tags sends out after being activate by reader the tag was indeed to work with is OK, but that depends what you do with the information receive. I assume that using a reader to activate a tag you don’t own would be a more egregious violation of the laws the arts is said to be in trouble over.
Hack this to allow RFID authentication on laptops for login etc in 3..2…
lol its called backtrack 5 XD … loads of useful RFID tools there
along with loads of other fun stuff
Sounds like a great idea! Will hook up tools and give it a try! :D
Awesome idea, I’ll have to check out the distro.
@Commenters
Early bail on 32bit? This is a late transition if anything. Nintendo 64 had it in 1996, and 15 years later we are just starting to make the switch?
By the way ive created a torrent for the file just in case, its web-seeded also:
magnet:?xt=urn:btih:8C1A407B61A3767CA17977BAC28C96912F7AFED2
I would like to see the ability to use an android phone such as the samsung nexus s or galaxy s2 as a reader/writer rather than having to buy one.
The biggest reason that this should be available for 32 bit stuff is very simple.
This system needs to be SMALL for hacking purposes. In other words, it needs to be compatible with microcontrollers such as arduinos.
I’m pretty sure someone would notice me standing really close to their RFID conversation with a laptop. But it would be SO much easier to pack the software into a microcontroller that I can stealthily place near an RFID or NFC receiver.
The sniffer hardware is only relatively simple reader. It would be better to have a high power reciever, which could be effective over a distance. Similar to wifi.
Has it got directional finding, so you could follow a shoplifter home? or a mass scan of passports, or ID cards.
IBM has got big ambitions with the internet of things and their global CPC-number database. This hack could really challenge their obnicious stazi supercontrol.