 Most spy movies (at least the ones worth their salt) will include a few scenes that depict nerds in a van listening in on conversations remotely and causing the victims phones to do things like turn themselves or their cameras on. We have been made to believe that it takes an entire van of equipment and one or two MIT level hackers to pull this off. Turns out all it takes is about $2300, some know how, and an unsuspecting target with a set of microphone-equipped headphones attached to their phone.
Most spy movies (at least the ones worth their salt) will include a few scenes that depict nerds in a van listening in on conversations remotely and causing the victims phones to do things like turn themselves or their cameras on. We have been made to believe that it takes an entire van of equipment and one or two MIT level hackers to pull this off. Turns out all it takes is about $2300, some know how, and an unsuspecting target with a set of microphone-equipped headphones attached to their phone.
The French Government’s information security research group ANSSI has been investigating this and published a paper with their findings. Unfortunately that paper is behind a paywall. Wired has a pretty good summation of the findings, which use a transmitter to induce a current in the headphone wires. This in itself isn’t surprising. But they’re able to do it with such accuracy that it can both trigger, and successfully interact with the hands-free features provided by Siri and Google Now.
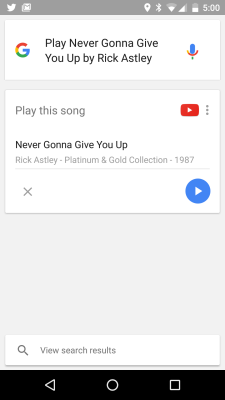
We think this is a really cool proof-of-concept. It’s mentioned that an attacker could potentially use this to make calls or do other things that cost the victim money. We think it’s more likely to be implemented by resourceful young engineers as a practical joke. Rick Rolling is a poplar go-to. But if you can make the phone “hear” audio, you should also be able to make someone wearing headphones hear ghosts. This has a lot of potential. The first one to make this happen really needs to let us know about it.
















poplar
Clearly the authors didn’t mean that Rick-Rolling is related to the species of tree. I swear, the spelling and grammar Nazis that read Hackaday are some of the worst on the internet. Did you understand what the author meant? I’m pretty sure you did. Are you paying to read this article? No, you are getting it for free (except maybe tolerating an ad or two). So just let it go, and if you think that a mistake is so heinous that it needs corrected, do it in a respectful way. Something like, “hey, I know you probably meant to use the word ‘popular’ instead of ‘poplar.’ I think it may confuse your other readers and they may not get your true meaning.” Single word comments making fun of a mistake are hardly constructive.
How do you know he’s making fun of a mistake? You’re reading an awful lot into one word.
*sarcasm on*
your totaly tru ! f**k gramar nazzi lol
*sarcasm off*
… If you promise not to sue us, you can shove one up your nose.” ?
Wow, nobody?
dick
I haven’t read so I’ll comment.
I expect guys send an AM signal that gets detected at audio input circuitry. Quite easy in theory, however, most recent audio codecs I meet have SNR decent enough to make this a challwnge.
P.S. First.
Since audio signals through those jacks are single ended, SNR or not not going to matter. The ESD diodes could act as rectifiers for the RF signals capture by the headphone cable acting as antenna.
polarized sound? Sound from ultrasound? https://www.ted.com/talks/woody_norris_invents_amazing_things
From the paper: “It was also observed that the minimal field required around the target was in the range of 25–30 V/m at 103 MHz, which is close to the limit accepted for human safety”
I didn’t have to read the paper to figure that. No way can you induce current remotely without serious output power. Also, they probably weren’t very far away from the headphones. If that were the case, your headphones would be picking up all kinds of garbage.
Chalk one up for using Windows Phone.
This attack is only relevant if you are wearing earphones that make a connection to the mic portion of the jack, also you need to have this feature enabled in the first place..
Does anyone know if plugging in standard headphones grounds out the 4’th mic pin in the 3.5mm jack? if so you also have to be using a specific style of headphones in the first place, pretty niche.
Also while you are wearing the headphones you’re going to hear siri/google responding to these commands, pay no attention to the guy holding an antenna near your wire while your phone flips out!
Yes, a TRS connector plugged into a TRRS jack will short the microphone and ground connectors.
Nor to your horrible headache and nose bleeding
Hmm. If this method works by inducing audio-frequency signals in the headphone cable, why can’t the person wearing the headphones hear it? What technique is used to make sure that it only induces current in the microphone section? I can hear noises if I walk through one of those anti-shoplifting sensors with headphones on, or if I let the cable get too close to my motorcycle’s spark plug wires. Surely these researchers would notice the same effect.
the impedance of the speakers vs the impedance of the microphone input?
I was thinking about doing the opposite the other day, playing your own stuff over what the user is listening to.
Or hijacking the users phone to make a threat on a public official….
Make someone hear ghosts…..sounds like a good idea for a Halloween prank (since it’s only a few days away)
Interesting in the past I have had to test audio equipment for compliance, one test involved broadcasting an AM signal modulated by a 1KHz sine into the device in a test chamber. We hooked the audio stage output to an spectrum analyser and we were not meant to see a 1KHz signal at all. If we did it’d mean the amplifier circuit was demodulating the AM which would have been a fail. It passed. Tempest testing works along the same sorts of lines.
“But if you can make the phone “hear” audio, you should also be able to make someone wearing headphones hear ghosts.”
Unlikely – the input impedance of a microphone input is very high, and the expected signal is very small. In contrast, a headphone is the opposite – low output impedance from the driver, and high amplitude.
Phones with FM radio tuners would be easy to exploit — assuming that user voice recognition is turned off while the radio is playing. Just transmit on the same FM frequency as the user is listening to and at a power level strong enough to silence the actual broadcast (trivial to do over short distances).
So would it be possible to record an “OK Google” command, increase the frequency to inaudible levels, and just play it back over a loud set of speakers to activate every phone in hearing range, without any people hearing the command?
No, voice recognition systems typically use band pass filters for “AF” Audio Frequencies (defined by the human voice model). This range is roughly 20Hz to 20KHz, but implementations will probably reduce this bandwidth further to reduce the amount of information they need to process. Anything outside this range detected by the microphone is ignored in software. It may be possible in principle to alter the software to use ultrasonic frequencies to recognises voice patterns but it is improbable that the microphones or the speakers are designed to operate in that frequency range. On top of that it is likely that the hardware itself has band pass (or low pass) filters to limit the frequencies captured / generated.
ps. I like your idea though, sneaky!
You can find the paper for free (in french) on the anssi website : http://www.ssi.gouv.fr/agence/publication/injection-de-commandes-vocales-sur-ordiphone/