Back in the early days of radio, it was quickly apparent that the technology would revolutionize warfare, but only if some way could be found to prevent enemies from hearing what was said. During World War II, the Allies put a considerable amount of effort into securing vocal transmissions, resulting in a system called SIGSALY – 50 tons of gear developed by Bell Laboratories with the help of Alan Turing that successfully secured communications between the likes of Churchill and Roosevelt during the war.
Now, a small piece of the SIGSALY system lives again, in the form of a period-faithful reproduction of the vocal quantizer used in the system. It’s the work of [Jon D. Paul], who undertook the build to better understand how the SIGSALY system worked. [Jon] also wanted to honor the original builders, who developed a surprisingly sophisticated system given the technology of the day.
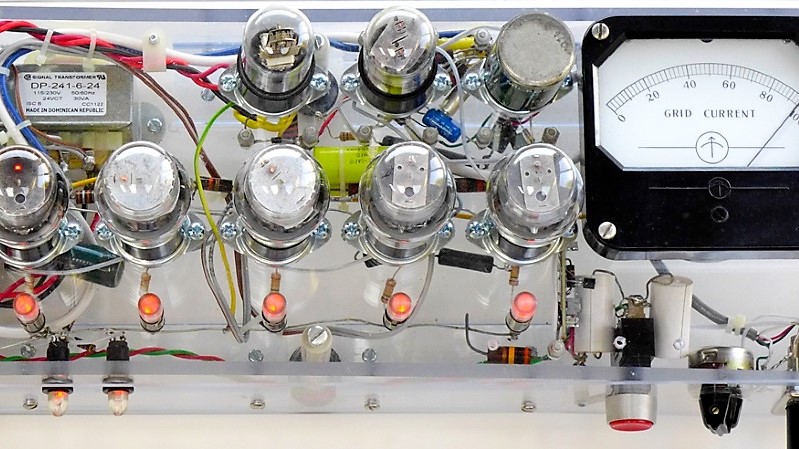
SIGSALY was seriously Top Secret in the day, and most of the documentation was destroyed when the system was decommissioned. Working from scant information, [Jon] was able to recreate the quantizer from period parts, including five vintage VT-109/2051 thyratrons scrounged from eBay. The vacuum tubes are similar in operation to silicon-controlled rectifiers (SCRs) and form the core of the ADC, along with a resistor divider ladder network. Almost every component is period correct, and everything is housed in a nice acrylic case. It’s a beautiful piece of work and a great homage to a nearly forgotten piece of cryptographic history.
Interestingly, Bell Labs had a bit of a head start on the technology that went into SIGSALY, by virtue of their work on the first voice synthesizer in the 1930s.















Very interesting and a great project and write-up, and not having to play a youtube video much appreciated, thank you.
Here in the UK we can go around Bletchley Park and see and learn much about the Allies code-cracking, Alan Turing, Enigma etc etc but hear virtually nothing on the schemes used by the Allies to encrypt their communications, or on the German’s success or otherwise in cracking them.
Very interesting stuff, these technological gems are easily forgotten. Thanks for posting this here!
Although the headline (combined with my own ignorance) made me expect a fully functional encryption system which isn’t the case (yet), so I anxiously clicked on the video only to learn about that this is just about a part of the system. Nonetheless still very interesting and I really hope that this project caries on, cool project!
PS: this could really be a nice topic for a retro-techcular item on hackaday
we would like to hear the encryption disks you know the ones that had to be synched up at both ends
I think that information about the source of the white noise on each pair of records in each set ( “Red Strawberry”, “Wild Dog”, “Circus Clown.”) would be far more interesting than listening hearing them. Most records of that time period would have been 15 minutes per side, so I can picture a few technicians beavering away in the background.
I also suspect that since they were using a One Time Pad, that each set was destroyed immediately after use to make sure that the communication cannot be cracked, that none would have survived until today. Handling of the one-time pre-shared key always includes destruction of the keys at both ends.
They were definitely one-time pads. The allies learned from their own codebreaking successes, just how bad an idea it is to use the same pad more than once.
As for what the encryption disks sound like, they sound like noise. Simple as that. Because that’s what random data sounds like.
BrightBlueJim – I think they used noise source like the sound of mercury vapor lamp interference and relay rack noise to generate random noise. They used synchronized phonograph players and vinyl disks to record all that. Those were used only once and may have been totally destroyed after use. The NAZIS did intercept the traffic but it sounded like hornets buzzing hence the nickname GREEN HORNET after the famous American radio character.
Not a lot of demand for thyratrons recently. The 2050 is in more demand than the lower power 2051 since it was used in some jukeboxes.
I used 7890 and 7390 thyratrons as radar modulators. They would switch 20-40 KV or so at some hundreds of amps. Not for long, though (microseconds). Stood about 18 inches high.
Read a nice book called “How to Wreck a Nice Beach” about early SIGSALY :) Easy reading and highly recommended.
Sounds like an interesting book, the title smart – from a mis-hearing of the vocoder-rendered phrase “how to recognize speech”
“Bell Labs had a bit of a head start on the technology that went into SIGSALY, by virtue of their work on the first voice synthesizer in the 1930s.”
In fact, that may have been the impetus for Bell’s work in speech synthesis. Bell Labs’ Voder attempted to reduce speech to 20 parameters, varying over time. These vary over time slowly enough that operators could control these parameters in real time using hand controls. By reducing speech to such a small set of data, encryption and decryption become much easier. But the Voder was just a proof of concept. In order to produce secure speech communications, you have to analyze and encrypt on the sending end, and decrypt and synthesize on the receiving end. Voder did just the synthesis, but did not have a correspondingly simple analysis method. SIGSALY used a less efficient analysis/synthesis method similar to a Vocoder, which divides the analog speech into bands and digitizes each band. This was not as efficient in terms of compression ratio as Voder, but it had the advantage of being simple enough for both analysis and synthesis to be done using existing technology.
The first realization of enciphered telephony
The first quantized speech transmission
The first transmission of speech by Pulse Code Modulation (PCM)
The first use of companded PCM
The first examples of multilevel Frequency Shift Keying (FSK)
The first useful realization of speech bandwidth compression
The first use of FSK – FDM (Frequency Shift Keying-Frequency Division Multiplex) as a viable transmission method over a fading medium
The first use of a multilevel “eye pattern” to adjust the sampling intervals (a new, and important, instrumentation technique)
https://www.nsa.gov/about/cryptologic-heritage/historical-figures-publications/publications/wwii/sigsaly-start-digital/