If you don’t live under a rock (though you may want to now) you probably saw yesterday’s article from Spiegel that revealed the NSA has its own catalog for spy gadgets. Today they released an interactive graphic with the catalog’s contents, and even if you’re not a regular reader of Hacking & Philosophy, you’re going to want to take a look at it. I recommend glancing over IRATEMONK, in the “Computer Hardware” category. As the article explains, IRATEMONK is
An implant hidden in the firmware of hard drives from manufacturers including Western Digital, Seagate, Maxtor and Samsung that replaces the Master Boot Record (MBR).
It isn’t clear whether the manufacturers are complicit in implanting IRATEMONK in their hardware, or if the NSA has just developed it to work with those drives. Either way, it raises an important question: how do we know we can trust the hardware? The short answer is that we can’t. According to the text accompanying the graphic, the NSA
…[installs] hardware units on a targeted computer by, for example, intercepting the device when it’s first being delivered to its intended recipient, a process the NSA calls ‘interdiction.’
We’re interested to hear your responses to this: is the situation as bleak as it seems? How do you build a system that you know you can trust? Are there any alternatives that better guarantee you aren’t being spied on? Read on for more.
As for alternatives, I want to pose one scenario as presented by [Hasan Elahi]. You’ve probably seen him on television or his TED talk; he’s the guy who flooded the FBI with data about himself.
He came to my university to give a lecture on his experiences with the surveillance state and made some interesting points worth repeating. The first of which is that information is a commodity, and access to your personal life is valuable. By providing these agencies with large amounts of personal data, you’re essentially “flooding the market.” If everyone shared their data to this extent, he thinks the surveillance state couldn’t keep up (and if you haven’t seen [Elahi’s] talk, it goes WAY beyond Facebook: he takes pictures of every meal he eats, every toilet he uses, every hotel room…everything).
It’s an interesting idea, and if we truly are becoming a culture of sharing, such a future may be inevitable. Perhaps it’s possible to saturate cyberspace with information to the point where our true selves are buried in the noise, and I agree that information overload on a person/individual may paint a very strange misrepresentation—or no clear representation—which could work in your favor. For [Elahi], it’s about reclaiming a sense of control, and that’s something he definitely achieves. Toward the end of his TED talk he shares his server logs, pointing out which government agencies visit his site and when. Perhaps it’s an illusion of control, but [Elahi] is absolutely creating and hosting his own archive rather than wondering whether the government is doing so. (They probably are).
Here’s where I break with this strategy: during his lecture at my university, [Elahi] seemed to suggest that interested governmental entities (NSA, FBI, etc.) sort through this data with people, who—when faced with the overwhelming mountain of pointless photographs—will give up trying to profile you. It’s not a person sorting through your data, though. It’s a machine, and it doesn’t care how many thousands of pictures are out there: that’s more material for it to use to make assumptions about you. Their data collection is automatic, global, and seemingly limitless. I suspect they’ll gladly integrate anything you provide and file it away for reference.
Let us hear your responses in the comments: is it hopeless? has the list of manufacturers in the catalog influenced your future purchasing decisions?
















I remain of the opinion that the same government that bungles the easy things will bungle this too, only with more zeros.
You’re confusing the [incompetent and/or corrupt] legislative branch of our government with the professionals that actually implement and execute the surveillance state.
It’s the ones who are smart enough not to be voted in by the public who are dangerous ;)
It is time to consider the importance of the 4 freedoms that are the basis of free software. You should be able to rebuild the firmware for your hard-drive and the drive should come with full documentation. Just like any other device, be it storage, interface or whatever. The time when “blobs” were acceptable is definitely over.
The trust is gone and a new regime should be established that gives access to devices so that you may trust again.
Not realistic. It needs knowledge that most people don’t have.
Does it really matter if it’s a “blob” or a BGA, TQFP or other high-density SMT package? What matters is if you can check if the logic and firmware inside match what you think should be in there. You can’t do that without uncapping it, taking very high resolution pictures of every single layer, and analysing it in great detail. Even if you could get the design files, it would take many manhours of highly trained engineers to verify that the device you spent hundreds of thousands of dollars to destroy was or wasn’t bugged.
But then you would still have to verify the firmware and you would actually have to prove the “correct” design and firmware files you’re checking against haven’t been tampered with in the first place.
I think by “blobs” he means pre-compiled binaries, with no source code and no way to compile your own. In this case, the hard drive’s firmware. If the user could put their own firmware on it, he could be sure there’s no spying routines hidden in there. Currently, you can’t.
He _still_ can’t tell if there is some spying going on at the hardware level. If NSA can install their own hardware devices, they could just replace whatever circuit they wish, you wouldn’t even know it has been switched. Then you can use any firmware, and it works, but also does something extra. There is really no difference between firmware “blob”, FPGA with “code” from some external or internal memory, code in ROM memory, PLA, or pure ASIC. They are way too complicated to check. You have no idea if some parts should be there or not, nobody but the original designers do. It’s also not simply doable to have reprogrammable locig everywhere, there has to be some logic under it to actually get the reprogrammable instructions to right place and start execution. A “bootloader” if you wish.
Amen. Time for an open source SSD SATA drive. Or maybe start with a thumb drive. Even then, you’ve got to trust that the nand flash chips from whatever company (pick the smallest Asian company that makes em!) don’t have ‘bugged’ circuitry. It’s a start though… at least we’d be in control of the firmware.
Do you also run poison checks on every bit of food you purchase at the market? Do you know for sure that the other drivers on the road are not drunk? At some point you must trust the fellow members of our society or else you are not going to be able to participate in it.
Actually that’s probably not a bad idea about the food.
http://io9.com/5810568/ten-foods-in-your-kitchen-that-contain-gruesome-poisons#
http://www.trutv.com/conspiracy/bizarre/poison-food-fluoride-cancer-children-fish-mercury/photos.html
If someone spies on you then he/she doesn’t trust you, therefore acting in the same manner is justified.
Weak analogy. We’ve no evidence of some grand government conspiracy to poison our food supply, so why would we poison-check every food item we buy? On the other hand, there’s plenty of evidence of large scale government surveillance, so discussions on how to detect that surveillance are very relevant.
Sure we have evidence of mass food manipulation, Monsanto’s frankenfood. They have opened Pandora’s box with our food supply and it can’t be closed. If you think about it, protecting our fundamental human resources (healthy food, clean air, fresh water) is much more important than any perceived privacy at this point. We all spy on each other every day, listening to someone talk on the phone, looking out our window, and spreading gossip. Privacy is really an illusion, but it can be a necessary part of the modern Matrix we’ve built for ourselves. That doesn’t change that we are all inherently shaved apes with fancier tools, so keep that in mind to gain perspective.
I’ll grant you that we should view corporate tampering with our food supply with concern, but that’s not the same as F’s analogy or my rebuttal. And the food supply concerns in no way lessen the surveillance / privacy concerns that should exist too. It’s not a binary, this or that choice. Why do we need to choose just one battle to fight?
I agree we shouldn’t limit ourselves in fighting for what is right, but we certainly should prioritize and things that keep us breathing should be higher on the list. So with realistic perspective it certainly lessens concerns and makes priorities clearer.
This “F” poster is very likely a paid shill or a “sock puppet” account managed by pro-intelligence interests.
My food can’t put me in Guantanamo. Drunk drivers can’t arbitrarily dictate new laws or plant evidence of wrongdoing on an encrypted hard drive.
Say “No” to Spooks.
“F”‘s IP is coming from Norfolk, VA…
100% security can only be achieved through 100% isolation. A computer with no internet access cannot be hacked into without physical access.
Not that this is very convenient…
“Internet” should read “network”.
Sorry.
That has been proven wrong, The computer, display, keyboard, mouse, etc, needs to be in a Faraday cage as well. Look up TEMPEST and see what they were able to gleam from the electrical noise.
And that is assuming that all your hardware was not compromised already. Did you inspect all of the hardware and firmware carefully for modification?
This makes me think of Gene Hackman’s character in that move “Enemy of the State”. At the time that first came out I was thinking pretty much all of the government surveillance capabilities were rubbish, but over the years they’ve brought more and more of those techniques to fruition.
You have to see Gene Hackman in The Conversation.
http://www.imdb.com/title/tt0071360/
Enemy of the State is trash for mass consumption. The 74 film is the super hacker flick. I mean get with the program already!
And to understand who “The Conversation” was loosely based on, read the story of Marty Kaiser:
http://martykaiser.com/fbi1~1.htm
He uncovered illegal activity inside the FBI, and they in turn basically ruined his professional career.
For some reason I’m not allowed to reply to asdf, but what a load of BS that Marty Kaiser link is. You can verify exactly zero things in that article, and he describes a lot of fantasy technology the germans supposedly had in WWII. What he describes is literally impossible, and even if you correct for some massive ignorance (which is especially suspect because he should be and claims to be knowledgeable in such things), you end up with devices that aren’t mentioned in any accounts of WWII I know of… and the concept of the alleged devices are still questionable at best.
Even if people can get info from your device, the device itself cannot be hacked.
The point is, you can hide behind a flow of information. it is called dis-information.
And all of this is the obvious stuff. There are a lot more options if you are targeted as a person of interest. Hell I have seen arduino’s used in some pretty clever covert stuff by common data thieves, I guarantee they do the same. Some people claim you are a bad person to look into it, but look at the Black Hat and CCC archives about how credit card skimmers do their thing and how they use relatively low tech to make a convincing and effective stick on system to steal data directly from you. And those are the rank ameturs that get caught…
The NSA is not the only gang in town spying on you. If your data has any worth, organized crime is after it as well.
Those of us who have managed networks with DMZ’s and monitored activity on all sides with tools like ethernet sniffers probably would not get all that exited. The NSA doesn’t have a magic key for every box and it doesn’t have a single tier access method to workstations.
In all honesty, the people they are most interested in are completely of the map, whilst the average nob with an XP box directly on the modem is simply overly surveyed.
I agree with the comment that regards them as not competent enough.
Also, bomb, oil, president, terror, allah and attack.
It’s not “the people they are most interested in” that concerns me. Obviously the average Joe has nothing to worry about from the institution itself.
But, look at what Snowden did. He accessed a huge repository of stored data without the institution catching on, He happened to plan to release it as a whistle-blower (at least that’s the picture he’s painting) — which you could say is a white hat action. There must have been others that were poking around in the data without consent of the institution whose motives weren’t so innocuous. I often wonder how much money was made through insider trading because a contractor was able to get their hands on this type of data? And that’s not even a malicious scenario.
You forgot to include other keywords, I’ll help you: islam, train, bus, Volgograd, putin, olympics, jihad.
Except for the fact that the hacks are in the network card drivers and none of your application software will ever see these rogue data packets. Unless you’ve manufactured your very own Ethernet PHY you are not going to be able to detect what is really happening on your network.
sorry not the network card drivers, but rather the firmware on the network card itself.
An external sniffer on the segment would see it all. You just have to sift through all the information to figure out what is good and what is bad traffic.
They do identify and track down people who they consider bad/dangerous, who are then often enough killed by drones or attacks. This stuff is real and gets plenty gruesome at times.
But obama says he’s an infallible genius and he picks who to kill, so it’s all alright… no really..
An surely no nuclear-weapon state would go to war over military aircraft trespassing into their territory, right? :trollface:
Are you sure they didn’t do that to keep that area of the disk from getting worn out or something? The beginnings of hard drives are way more prone to errors and bad sectors.
also check out http://spritesmods.com/?art=hddhack
he did his own similar style hacks on a hdd, and explained what it can do and how
wow… that is an awesome article… the final video was indeed impressive
That was the first thing I thought of when I read this. I was going to post the link, but you beat me to it.
The papers are quite old.
As Bertho pointed out, free software is one of the most obvious way to be safe(er). There was only one application mentioned that targeted an operating system which has anything in common with free software: JUNOS a FreeBSD derivative but… JUNOS is not free. The rest that were advertised as supporting Linux or EXT3 filesystem look only as means to deliver a rootkit. Maybe NSA has conceived something something that actually works. It appears there is not many better ways than transparency to assure integrity.
A few years ago Prof. Kim Fowler visited my university and gave several lectures about different challenges an engineer may face when designing and creating a device. I’ve asked him how to assure integrity of devices, especially if they do only things they were meant to (not doing things is rather obvious). Sadly, he wasn’t able to give any good answer, however, admitted the subject is interesting. I wonder if he has researched it since.
This recent talk from Jacob Applebaum @30c3: To Protect And Infect
http://www.youtube.com/watch?v=b0w36GAyZIA
might surprise most of the hackers.
http://bernhardkubicek.soup.io/post/382953085/Would-you-download-a-human is basically what I currently think about this issue. Privacy has lost.
that mold spore’s a SPY!
I really feel sorry for anyone reading my emails, or looking through my records. it would be like looking though a junk drawer…..
Most of us have boring and uncontroversial stored histories that could become quite interesting and controversial and potentially criminal if someone decides to go in and make edits to the stored data.
The danger in surveillance is NOT that people will see your boring life but rather that they will overlay someone elss’s criminal activity onto your history and turn you into the culpable one.
True. Suppose that someone hates you and puts CP on your HDD…. aaaaand you’re fckt. Read about a case where some guy used a remote desktop software to do exactly that. While they found out in the end it, but makes you wonder on how many occasions it went all as planned and how many innocent ppl ended up in jail.
No.
The danger is that someone will see my boring life, whether I allow them to or not.
What someone decides to do with the information is beside the point. The fact that an organization – that I am forced to support – is not only capable of monitoring all my actions and interactions, but willing to do so, is what is wrong here.
Also, protip: Polonium turns green in tomato sauce.
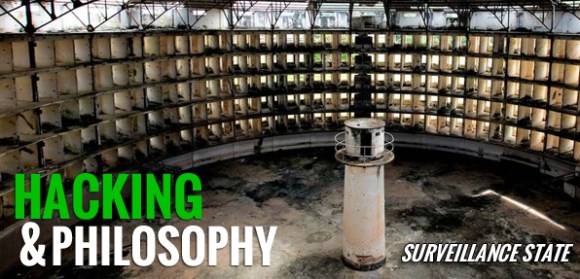
Bit of a tangent–what is that a picture of on the banner?
http://en.wikipedia.org/wiki/Presidio_Modelo
or let me google (image) that for you..http://images.google.com/imghp?hl=en
Google image search says this is the Presidio Modelo prison in Cuba, an example of a Panopticon.
http://en.wikipedia.org/wiki/Presidio_Modelo
http://en.wikipedia.org/wiki/Panopticon
Panopticon
It seems highly unlikely that the vendors would be complicit in compromising their own products. It would be commercial suicide and leave the company and officers open to a lifetime of shareholder litigation. I don’t think NSA would even consider asking. There are easier ways to accomplish their goals.
What’s being done is state sponsored hacking with large budgets and staffs. If HackaDay contributers and readers build easter eggs into devices for fun in their spare time, what can engineers given 6 figure salaries and lots of time do?
There have been academic demonstrations of mask level attacks in which additional functionality is inserted into a chip design. The NSA has been very worried about manufacturing level attacks for good reason. A considerable portion of “US” electronics is manufactured in China. As a practical matter once they’re potted it’s impossible to verify that all the chips produced on a line match the original design tapes. Most attacks are probably firmware based simply because it’s easier and cheaper. But subverting the chips in a particular batch seems highly doable if you control the factory. and know where that batch is being shipped.
How much time can one afford to spend reverse engineering devices to detect hidden functionality? It’s easy to prove a device does something. It’s impossible to prove it doesn’t do something. Ken Thompson wrote about this in his Turing award address, “On Trusting Trust” and he was just installing a backdoor in Unix via the compiler.
For individuals the only protection is to stay off the radars of all the adversaries.
“t seems highly unlikely that the vendors would be complicit in compromising their own products. It would be commercial suicide and leave the company and officers open to a lifetime of shareholder litigation. ”
You DO realize that there is pretty conclusive proof that this is PRECISELY what happened at RSA?
You DO realize that there is pretty conclusive proof that the Chinese are doing PRECISELY the same thing?
“Ken Thompson wrote about this in his Turing award address, “On Trusting Trust” and he was just installing a backdoor in Unix via the compiler.”
You DO realize that MAYBE PERHAPS there is some more sophisticated commentary on this subject than a paper written in 1974:
https://www.schneier.com/blog/archives/2006/01/countering_trus.html
” leave the company and officers open to a lifetime of shareholder litigation.”
How is this supposed to happen? What sort of testimony do you expect to hear in open court? Do you really think that the government is going to let its dirty laundry get aired in civil lawsuits?
AT&T was exposed as illegally siphoning ALL phones to a secret room of the NSA in their exchange, they got ‘pardoned from prosecutions’ by 2 presidents (bush and obama)…
Draw your own conclusions.
I think this is pretty solid evidence that the NSA doesn’t need help from the vendor:
http://spritesmods.com/?art=hddhack
It is interesting to see their tricks, even when this information refers to dated projects and it must be several generations ahead to what the spiegel shows.
It is also depressing and upsetting…
Thinking that the NASA doesn’t have the capabilities to do 100% of the outlined programs is your first mistake….
Forgetting the NSA has a classified budget equivalent to a few countries accumulated GDP’s is your second mistake….
Forgetting that the NSA has ‘sister agencies’ (CIA, DIA, NIA, AIS, ATF, HL,FBI, Local Municipalities) to “share” information with is your third mistake…..
Lastly, if you were a secret organization, your best and greatest weapon is ‘plausible deniability’, right next to ‘disinformation’ and intelligence.
Plausible deniability is pointless. Who are you going to deny your involvement to? that Predator drone that just launched a hellfire missile at you?
> Who are you going to deny your involvement to?
The Supreme Court, perhaps?
Technically, there’s still a Constitution in force in the USA.
Hey, I got an idea… let’s store all our data in the cloud!
Haha, great idea, sign me up.
People don’t get half of what I tell them anyway, so good luck NSA guy, working out what I am blathering on about at any given moment of the day. ;-)
They way I read it is the IRATEMONK seems to be a tool designed around those manufacturers products. I wouldn’t be surprised if intelligence agencies approached manufacturers about back doors, I doubt they have 100% success though.
I agree that publishing your whole life on a webpage to ‘obfuscate in the noise’ isn’t that effective. Especially if you are only documenting things that play a role in your life ie; types of tacos you like, types of conferences you go to, styles of food you like. Just watching the TED talk we know a variety of places he holds or held residence, shopping habits, travel logs. I think he is being more specific than he realizes and isn’t actually obfuscating anything.
The EFF(I believe) had a recent project that determined how unique your browser was compared to others. Based on the amount of routine data sent when you visit most webpages. There are enough identifying marks in your browsing history, shopping choices, travel arrangements that without concerted efforts to be ‘faceless’ that you can be identified from the crowd. Even if you are ‘faceless’ it only takes a few slips for patterns to be matched or documented.
In the age of ‘Big Data’ where millions of data points are routinely and quickly processed with R, Python, Matlab and others I am reminded of the stainless steel rat by Harry Harrison:
“We must be as stealthy as rats in the wainscoting of their society. It was easier in the old days, of course, and society had more rats when the rules were looser, just as old wooden buildings have more rats than concrete buildings. … It takes a very smart rat indeed to find these openings. Only a stainless steel rat can be at home in this environment.”
Yep, Panopticlick: http://panopticlick.eff.org/
It’s a bit frightening how unique a browser can be.
I think that Harrison quotation fits really well here, and we may have to add a different type of rat once everyone is walking around with chips implanted inside them. (Which complicates F’s comment about checking every food you ingest. What happens when you literally ingest technology into your body on a semi-regular if not regular basis?)
@Kerimil Yes this is indeed an issue.
I have read about a similar case involving a whistleblower and he had to go to court and spend time in custody before the obviously forged “evidence” was revealed as having been planted using a virus.
Last time I checked he is still out of work, despite having MCSE, A+ AND numerous character references to prove his innocence from his time as a professional photographer.
You are actually better off if in this situation signing a pact with “The Man” and disappearing into whichever rabbit hole they want you to, than trying to fight a broken system.
Normally this is done to high profile targets to convince them to work undercover for the State, or just as a way to silence dissidents/political activists/assange clones/etc.
i thought security through obscurity was deemed insecure.
Besides what today can’t be analysed due to lack of resources, manpower, or anyother reason, tomorrow that might easily change.
Although the situation does seem bleak, there is at least a small chance that outrage over the NSA’s spying programs will result in some real reform. And you can help.
Take a moment to send your representatives (http://whoismyrepresentative.com/) an email and let them know you would like them to support the USA Freedom Act (http://sensenbrenner.house.gov/legislation/theusafreedomact.htm). It could go further, I think, in prohibiting these kinds of mass-data-collection programs, but it’s a fine start to closing this stuff down.
That seems like a waste of time. I don’t see the NSA simply ceasing activities. Instead, I figure they would circumvent the laws using loopholes or devices that cannot be attributed to the NSA.
Just another proof why we need to adopt open source hardware wherever we can.
Of course not everyone is capable of looking at the inner working of say a network or disk controller chipset, but having a few hundred thousand people in different countries who could do that, would make things much harder for the evil NSA guys.
USA = Universal Surveillance for All. Very seasonal message by the ACLU:
“The NSA is Coming to Town” http://www.youtube.com/watch?v=8pcWlyUu8U4
Not much you can do even with Open-Source-this-or-that (TM) when the HDD
firmware, Internet backbone and your email/social sites providers have a backdoor for
the NSA and others. You are stuck with older and more expensive
hardware.
“We are for Socialism, disarmament, and ultimately for abolishing the state itself. We seek the social ownership of property, the abolition of the propertied class, and the sole control of those who produce wealth. Communism is the goal.” Roger Nash Baldwin, founder of the ACLU.
i’d put my money on that they have all encrypted hard drives compromised by this or a master key of sorts.
IRATEMONK: “the firmware” can mean many things. Even the MBR and HBA an be considered a form of firmware that exists like BIOS/UEFI, before the OS’s kernel. Also, the HDD’s own chips load software and calibration data off of the spinning disk. Nothing prevents extending that on-disk firmware other than limits of the drive’s memory. They probably just use it to fake a boot sector or allow for a secret backdoor password to work or to save and give encryption keys on a drive that has that feature. They have the key for secure boot, I’d imagine, also. NSL’d
http://hddguru.com/ has more low-level info.
I have read through all of these postings and it seems as one aspect is clearly missing. You will never be able to prove or disprove what products, people, or agencies may or may not be trying to do to you, your food source, or your data. At that point you have two options. One, stop worrying about it all together because you could probably literally drive yourself crazy worrying about it and never truly have the answer. Or two, realize that in order for any product, person, or agency to actually harm you, they must be able to physically interact with you in some way.
Now I can already start to see the comments starting on how that is exactly the opposite of this posting, and imagine all the damage done to you just by having your data compromised. Ok, ok, ok, maybe for the way you live your life now. Ingulfed in a society of endless technological sophistication that most people could not imagine how it would even be possible to live in a world with out continuous Facebook updates from there smartphone and the magic of there direct deposit debit card. But really think about it. Let’s look at the oldest and simplest hack on the planet that still addresses one of the concerns in these postings. Worried about where your food comes from? Grow your own food!
Now I can see people starting to think how I’m one of those technology haters that has decided to tarnish the pages of their precious hack-a-day. Not the case at all. I love technology and the handymans ability to re-create what before took years and millions of dollars to invent. So then you might ask, where is this going? Well let me get to my main point I guess.
So one of the postings talked about having CP placed on your computer. Assuming in the scenario that you are 100% innocent. When this actually happens, how does it affect you? Immediately it doesn’t. You are completely unaware. So now how this information is then leaked out to the government is the main concern here right? Well forget about it like I said, you’ll never figure it out. But what’s the next step? At some point the government has to physically come to your house and take you away to actually start affecting you. Or blow you up with a missile from a drone like some people posted. (No this is not a pro-gun post either) Either way, if you are honestly worried about the government or whoever else coming after, beat them the only way you can, when they actually come after you.
You’re worried about your data, like someone else said, don’t connect to a network. You’re worried about a drone, who here is going to build a way to detect them? Or put together an online group that reports any known drone locations or sightings? If you’re worried about black SUVs coming to take you away, build your own drone to detect black SUVs based on engine sound, or body shape or any sort of ingenious crap the people on this site come up with everyday. Back to the CP on your computer, lets take it to the extreme. Your computer is not network connected so someone actually went old school and physically placed CP on your machine with even older school floppy disk. Then despite being non network connected the gov’t finds out threw one there advanced methods. Since the gov’t is so set on getting you, you detected their drone and developed a way to make it blow up your neigbors house instead of yours. Then your homemade drone sent you a text giving you a heads up on the insuing raid. Maybe then, when the FEDs come to take you away you can counter attack with some sort of EMP machine that renders all of their vehicles and technology useless giving you just enough time to escape to your local hacker-space where you and your rag tag team of hackers find away to prove your innocence. ( Soon coming to a movie theater near you starring Brad Pitt?)
The point is, stop worrying about what you can never know and control and focus on what you can. You are hackers, makers, innovators, and inventors. You are all an inspiration to novice tinkerers like myself. If the government or big business or whoever wants to take us on, I say bring it! I think they underestimate the force they are dealing with. Until someone proves me wrong and develops some super awesome audrino controlled thing that detects all possible government and or other intrusions into your data and devices I say, buy more things with cash.
-THE END
“Or two, realize that in order for any product, person, or agency to actually harm you, they must be able to physically interact with you in some way.”
Did you notice all the remote control gizmos etc for smartphones? Download some child pr0n to your iPhone while you’re sleeping then the next day at work, acting on a “confidential tip” you get busted for it at work. You’re innocent but forget proving it. Kiddie pron is treated as worse than hacking up entire families by the courts and the media. Compare prison sentences of it VS violent felonies, and what offenders have to do after they get out of prison. Most places they have to register as sex offenders for the rest of their life.
I know a guy (older than me, in his 50’s) who was accused of “inappropriate contact” with a minor female and spent 10 years in prison. That in spite of the accusers confessing they lied, that wasn’t allowed in court. No lawyer will take his case without being paid huge amounts of money up front. They don’t want to be seen helping a “child molester”. The State owes him for the crime of stealing a decade of his life, being barred from voting, owning a gun and all the others of his rights they violated and are still violating every day until they admit their crimes against him and restore his rights.
iphone security limits every app to only access its own files, so it should be obvious which app (the remote control) created the files in question
As much as i would Love to agree, and accept “Trust” @ Face value. human experience has taught me differentely. Besides, “Acta~nOn~VerBa”, trust is earned, just like respect. participating in a society/Community who doesnt Share the same Values or one that is Selfisly concerned about themselves and Two faced as far as race, religion and ethic s would be *ill advised. I would however love to live in a self sustaining community. That would be tight. You could say that, like privacy, trust is also an illusion and a borderline Delusion … trust in god, who ever you deem him/her to be. That aside, Love Life and the real people in it…TrusT_Is_a_Weakness™ -“UpLink”
_My humble opinion, no offense or malice or Judgement cast or intended. Personally i would like to learn more about the original topic and preventing DaTa LoSs. Funny side note thou…its Strikenly odd and Suspicious how this blog/thread touches on all the topics and issues ive delt with in the last few weeks, including my scheduled subliminal propaganda on my television. Alas, its time for my neurosis to Rest, or yeah Where’s MaL?