The Linksys WRT54G is probably the cheapest and most widely sold embedded Linux device in the world. It is also incredibly fun to play with. A lot of people don’t want to take the full plunge into Linux for fear of screwing up their computer. Why not screw with your router?! Your S.O. probably won’t even notice, until you break it? so try to blame it on the cable company if you can.
I’ll be walking you through installing the openWRT firmware onto a Linksys WRT54G. This is followed by setting the router up in client mode. Client mode lets you connect the computers on the wired side of the router to another router wirelessly, it doesn’t even have to be yours! Read on to find out how simple this process is.
I’m using the Linksys WRT54G ver. 2.0 with the “experimental” release. First things first: Make sure you read and
understand everything on the openwrt wiki before you attempt this.
Installing custom firmware on an embedded device is always tricky, but if you go in guns ablazin’ you will definitely
end up with a brick. I’m doing this in XP, but you can use what ever you want.
Grab the experimental binary firmware release from
the official server. Use the one that matches
your router and select squashfs since it is a failsafe device. The wiki seems to be pushing the stable builds, but
those are deprecated.
The “boot_wait” flag needs to be set “on” to allow for the firmware flashing (and reflashing if something goes
wrong). Boot_wait delays the router boot process so that in an emergency you can flash a new firmware during that time
period. Setting this flag involves typing commands into the ping.asp page built into the router. The details for how to
do this are in the wiki. I’ve already got the flag set from when I installed the Sveasoft firmware. Why aren’t we
installing that firmware? Well, Sveasoft started out with some GPL problems and I feel the web interface hides the
magic. Using openWRT will familiarize you with the command line and its lightweight nature encourages
customization.
We will be sending the firmware binary using tftp while the router is restarting. The computer must have a static ip
(not DHCP) so that it will have an active connection while the router boots. Type in the tftp command line, but don’t
press enter. Unplug the power to the router and then plug it back in. Now you can send the tftp command.

After the tftp transfer successfully completes the lights on the front of the router will flash for a bit. Then the
power and DMZ lights will turn on solid while the router boots and sets up the file system. After this is complete the
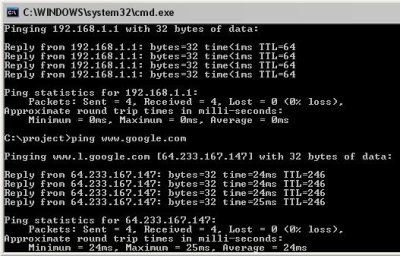
DMZ light will turn off. Congratulations you have successfully flashed your router, well, maybe; You should ping a few
things just to be sure.
You can even go to the router’s web page just to be sure. Just kidding, it doesn’t have a web interface, but the
developers were kind enough to leave a note saying as much.
Time to telnet into the box.
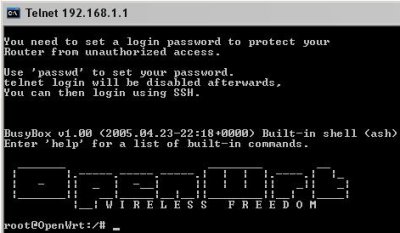
Type in “passwd” and follow the instructions to change the root password. Telnet will be removed on the next boot
and replaced with ssh because telnet is really insecure. Type in “reboot” and hit enter. Time to move to
Putty. Just type the routers ip address into the
host box and click “open”. The warning message is not a problem.
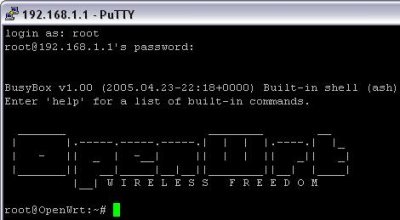
It looks the same, but is much more secure.
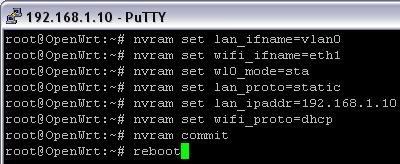
Now you have full control of the router. The router stores all of its operation parameters in nonvolatile ram
(NVRAM). These values can be changed at any time. If you don’t commit the changes before you reboot they will be
lost.
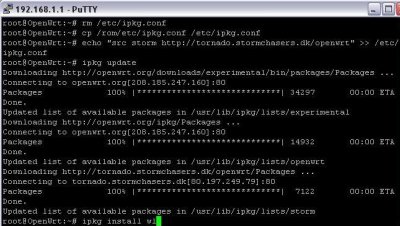
Before we tear down our good connection we need to install a piece of software. The “/etc/ipkg.conf” file is
actually a symlink to the squashfs partition. So to modify the file we remove the symlink and then make a copy of the
original file and then modify that copy. We then add the name of a package repository we’re going to use. After
updating the available software list we install the “wl” tool.
Now we need to axe the firewall since the internet will be available on the wireless side of our router. Remove the
symlink as before. If you decide to set up a new one (and you probably should) be careful because you could end up
locking yourself out of the router, I did.

Now we break the bridge between the wifi and lan ports. This is where the wrt really shines; the grouping of lan
ports and wifi is entirely up to your creativity. After the naming has been switched we set the router to client
mode “sta” and configure the lan for a static ip and the wireless side for dhcp. The changes are commited and the
router rebooted.
Using the “wl” command we can scan for nearby access points.
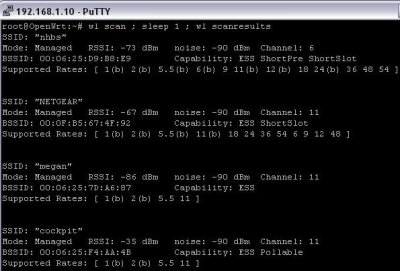
Just type “wl join ” and you’re done!
This is just scraping the surface of what the wrt54g is capable of. Using client mode you can hang your wired
network off of any wireless network you come across. You could plug in another wireless router to create a
repeater. Openwrt supports wds; which means you can make a client/repeater out of just one router. You could
set up multiple wrts in client mode like
Cringely and have a redundant internet
connection. You could install kismet_drone to do remote sniffing. Scripts like wondershaper can improve your network
performance. All of your regular traffic could be sent over the wan interface while your bittorrent was sent over
wireless to use your neighbors connection. You could separate the wireless and wired sides, giving free access to
passers-by while keep a secure wired connection for your home network.
Those are just a few possibilities that don’t require much more specialized software than is already installed.
Well, I hope you can see how easy this to do and will try it out on your own equipment. Good luck!
Oh, and Happy Birthday Vince! I hope your day goes far better than the date Friday the 13th would imply.
















nice. but the boot_wait hack doesn’t work on later firmwares (hardware version notwithstanding), leaving you no option for recovery if the firmware doesn’t boot.
or is there another way to set boot_wait?
happy birthday, er, friday, vince
great atricle but i think theres an easier way. i followed the steps on this fourm http://forums.anandtech.com/messageview.aspx?catid=36&threadid=1513386&frmKeyword=&STARTPAGE=1&FTVAR_FORUMVIEWTMP=Linear and it took like 3 min to setup and start surfing on some neighbour’s dsl
you could always downgrade the firmware to one that hasn’t fixed the exploit.
Looks like a good use for my super Router!
http://img.photobucket.com/albums/v417/ellectronico/lr3.jpg
I have been using this solution myself for a while now and I am very satisfied. The antennas on the WRT are just amazing, I can pickup a very distant WLAN and the connection is crystal clear and stable.
If you want to use WEP on the client connections, just set the following NVRAM variables:
wl0_wep=enabled
wl0_wep_bit=128
wl_wep_last=
wl0_wep_key1=abcdef….
Also, I can only recommend to anyone to set up a VPN with their friends. You can very easily install tinc on OpenWRT by adding a few sources to the ipkg.conf. The setup of tinc itself is very easy (maybe I will cover this in my blog later) and it’s a great way to access your friends’ computers without them having to open up ports to the entire internet. It’s also great for encrypted VoIP (I sucessfully routed Asterisk IAX connections via the VPN with good call quality).
I have the old version and the newer version however mine heat up realy bad I might modify mine into a “super router” too any instructions on how to do that?
So I could use one router as a client and repeater, but how do I enable wds?
I want to connect my xbox with my second router.
=cablemodem=wrt54g))((wrt54g=XBOX
You’re saying I can do this for free? Without paying for sveasoft?
SWEET! But I don’t want to end up with a brick or two.
Happy birthday, btw.
Hey! Happy Birthday there! interesting choice to put up a Linksys hack on Your big day… Are you a linksys whore? I know I am! but hey, I’m broke too!
-JD
Happy Birthday, Vince!
I don’t think I’ve ever posted to this site, but happy birthday! I’ve been a regular visitor here for a few months now and this hack is especially interesting.
Just to clear up any confusion: There are two people here. I’m Eliot, I wrote this how-to and I’ll be writing the daily features. Vince writes the lazy afternoons and the links. I’ve only been here a week (proximity card spoofer was my first post) so I’m sure most people haven’t noticed yet since I didn’t do an introduction post.
so, does anyone have a basic tutorial on where to find and install packages? the wiki didn’t seem to have any package links, and i’d love to fudge around with my router some.
how would i go about using my neighbors connection for bittorrent while maintaining a wired connection for normal things?
With your neighbor’s permission, that’s how.
screw openwrt firmware – get the firmware from http://www.teamxlink.co.uk instead, and use it to tunnel your xbox system link games and play them online! I got my WRT54g just to use xlink. Absolutely worth it.
Happy birthday! this is a great present. I’m still am having trouble starting to do this hack. I want to do it but i’m new to this sort of stuff and i don’t know where to start. help! I have all the stuff downloaded but i don’t know what to do with it. =(
Cool!
do you know if you could put a Mikrotik OS on the Linksys 54g?
that would be kick ass.
brandon, maybe you should use sveasoft’s alchemy firmware which has the user interface and you won’t have to use telnet -> http://forums.anandtech.com/messageview.aspx?catid=36&threadid=1513386&frmKeyword=&STARTPAGE=1&FTVAR_FORUMVIEWTMP=Linear <- follow the instructions there (tomgreen23’s link)
I’ve seen many of these tutorials but one thing is still lacking.
Why the hell should I care!?!
Okay, now that was not said to be mean at all but out of frustration that I, for the life of me, can’t figure out how, outside of creating a mesh network, any of this would be useful to me. I need practical, real-world examples. I want to do cool stuff but I can’t figure out how I could use it. :-(
This doesn’t really go as far as what a WET54G can do though – it’s not a transparent wireless->wired bridge.
I have something similar to the above, using WPA-PSK (wpa-supplicant, not the linksys one as that’s broken w/client mode). I had to use dhcp-relay to relay the dhcp across the two segments, but other things don’t work, such as my printer (which uses zeroconf) and Windows networking.
What’s really needed is a way to make a wrt into a pure transparent bridge.. there isn’t one yet though.
when the wrt is in client mode can you still connect to it wirelessly??
I have the same question as #23, so I am reasking for emphasis. Can you configure it so that you can still connect wirelessly?
I have tried Alchemy from seasoft and I can “NOT” get wireless connectivity while in client mode. I am thinking though that, isn’t this Linux? There should be a way to make this work.
Thanks.
I just noticed an unsual client shared on my local network. I live in an apartment using linksys wireless router connected to cable modem. Certain night I noticed my connection drops and my cd drive acted abit strange. Today I caught this person cause I saw his shared folder on my local network. Asked myself who he got connected to my local network? I got pissed and deleted all his shared files and documents and left him a nasty note to f’ off. I reconfigured my network and placed passwords. How this happened?
WEP is useless, that’s what happened. Search for how to enable WPA, it’s more secure, and you won’t get hacked by script kiddies :)
hi
Hi.
I’ve ALREADY upgraded my firmware to the whiterussian version.
How do I set the bootwait now?
Actually… all I want to do is reinstall the firmware, but I understand that in order to do so I need to have the bootwait set.
help!
Shawn,
this link should help you.
http://openwrt.org/OpenWrtDocs/Installing
the answer is in the middle of the page, I would reccomend reading the whole section though.
So my problem is, I am trying to extend a wireless network. My landlord uses a 2Wire WiFi router, and I have 2 WRT54G boxes. I was going to have one connect to his router (client mode), then route the signal to my second WRT54G (AP Mode).
problem 1.
Both WRT54G are version 3.1, and I cant find anyone who can concretely say that third party firmware will work. But I was able to set boot_wait and many people with v3.1 boxes cant. Also some guy took the v3.1 apart and noted it was identical to the others versions.
so do i take a $50 chance?
Problem 2.
the landlord is using WEP (no flames please) and I dont see a painfully apparent way of having my WRRT54G authenticate with his WEP protected box while in client mode. ANY ideas welcome.
thanks in advance.
–Mark
mark- Alchemy-V1.0 v3.37.6.8sv (or later) lets you put it in client mode and use all the common encryption. WEP, WPA, etc.. try the opensveasoft stuff.
Got the latest version of OpenWRT, enabled the client mode, connected to my old SMC router for testing. For some reason, the DHCP client is unable to get an address.
HELP ME!!
How can I reflash to the official bios??
Please Help! The Tutorial doesnt work for me It’s to hard for me I’m a noob in Linux I’m using windows
I have an Asus WL-330g which I’d like to use like this, but the Asus product, apparently, has a partial implementation of Proxy ARP. Thus, it’s a PITA to use the Asus product as a bridge. Has anyone hacked this device for that purpose?
-Thufir
I have found an extremely usefull script that I have adapted for my usage.
http://www.sephail.net/projects/openwrt/
This script will look for access points and try to connect. My version has added functionality to filter out access points with WEP and to try to associate to the strongest one first.
Response to Post #25
I really didn’t see why you acted this way, you left your network open and I assumed you just wanted to share it with neighbors, so I connected to use the internet…as a good neighbor I shared some of my files with you…
I really did not see why you had to delete my files and why you had to leave me this nasty note….
By the way has anyone has the answer to post #23 yet ??
In reply to post #35 by sle118.
Care to share your enhanced version of the script? I have a use for it (g) Thanks.
Simple question When you set up Router #2 will it broadcast its own wireless signal ie can you connect to it via wireless instead of wired connection?
mark: to use a wrt in AP mode, you have to do the following:
access the wrt user interface. if you don
Hi, Very intersting story about Linksys Router.
Im a complete idiot when it comes to networking setup. Every thing written on this site is never heard.
Im subscribed as Multi-user with SBC-Yahoo DSL. They gave moe a 2-wire 4port Router 1701HG Gateway. I moved for a vacation 30 miles away and my friend says he is also using SBC DSL. So I brought my 2Wire so we can both connect to SBC. How stupid of me to get a Linksys Wireless Router WRT54G and a Wireless-G card for my laptop. I can’t seem to work with all 3 PCs. 2 Laptops & a Dell PC with Speedstream 5100a model.
While trying to be an expert, I tried for 2 fucking days to install everything, but everything came out as a mess.
For 1: Just now, I removed all Dial-up short-cuts and left it without any dial-ups, and it worked when I connected it. My friend says he applied with the Security Access and Log-in via dial up to broadband connection. But, I never did the same thing to my laptop and we are both accessing the same access point with no problems at all. My setting is: Client Using DCE Cell and IEEE 802.11 with Fast Reconnect and No dial up shortcuts. So Upon opening the browser’s Internet Option, You cannot click any of those inside. So when you open my Laptop, You can go directly to any website w/o entering and username or password. (Im quite worried if it also happens to me)
Linksys WRT54G is so cheap that everyone has it in your neighbor hood. Im afraid not to use it as I can also log in to my neighbors w/o them knowing. I just had the Wireless-G card installed and select a Linksys on Site Survey.
Sadly, I still don’t know how to put security codes on my Linksys. Im using XP-Pro SP2 & SP1 on the other Laptop. Both are working fine.
So what step shall I do to put security system?
Thanks! Awesome site!
Please help me, im noob!!!
I followed the instructions above, upgrade the firmware to openwrt (which seemed to slow down my wireless throughput), then updated the available programs through the web interface ( I know it said it doesnt have one but i tried and it does) installed “wl” and did all of the rest. Now I can’t get into my router. Can someone give me a simple step-by-step intructions on how? and how to revert back to AP mode?
HI all
HOw can I change my speed on te mikrotik router and i wanna stay invisible
Hi every body and thanks for the great input “linksys support is here”
I have a small project I’m busy with trying to provide some friends with wireless access from my house to there APT across the road. I need to have a bridge connected to my AP then on the bridge side they want to connect a other router in AP mode so they can use there laptop and PDA’s and on to that AP one more bridge with the same set up.
Al hard ware is Buffalo Air station WHR-G54G with DD-WRT v23 sp1 for the Buffalo they all up no the first bridge after the Main router has to run in DHCP mode to provide the next AP and all the attached laptops and PDA with IP’s how can I do this we have in total 3 lnksys wrt54G 2 Vr 2 1 Vr3 and 5 Buffalo
My question has been asked twice already by others, and never answered.
Is it possible to set up my wrt54g to receive a signal and then send it out?
IE: I want to be able to connect to my school’s network, but i live just outside campus, and therefore just outside the network area. I’m thinking with a minor antenna mod, i can pick up the signal on my wrt. however, i need it to transmit too so i can use my laptop wirelessly throughout the house.
anyone?
Hi, If i get the ap working in client mode, can you set the router so that your own PC’s behind the router have different IPS?EG: the wlan i’m connecting to is 192.168.1.x , can i set up the routing so that all my pc’s behind the router are on the 192.168.0.x network? Thanks!flash
Hello, im living in a aparment unit with five schoolmates. Apparently one of them is this i.t. techie guy who blocks our ports, well not exactly block, but our download speed can only go up to 20kbps, while his reaches 300kbps. How do I hack through the router, and enable my port? He has a password installed, and a username that i don’t know of.
I realize this is an old article, but after trying a similar setup with client mode to allow my media center devices (xbox, satellite box, etc) to plug into a local wireless router which then relayed traffic to my main internet connected wireless router, I found that I could not get traffic to properly get routed between the two networks — for instance, while my xbox could happily communicate with the outside internet, it could not talk to my home PC which was hanging off my main wireless router. I’m no expert but after reading up on this for a while I came to the conclusion this may be by design, and could not resolve it using client mode.Instead, I flashed both of my routers (both Linksys WRT54G’s, one a v6 and one a v8) with appropriate versions of the DD-WRT firmware (took 5-10 minutes per device) and then configured WDS following the WDS page instructions on the DD-WRT wiki. This worked like a charm and took very little effort. Client mode has its advantages, but if you run into issues routing traffic between your two networks you may find WDS to be a better fit. The main drawback is that it does require both devices to support WDS, and many do not. Hope this helps someone out there — I realize this post is old but it comes up very high when searching on this stuff!
I hav got a mikrotik router in my college!!!!!1Could you please tell me how could I change my account speed staying invisible??????Thank You
so. What if I forgot my password is there anyway to get it back? Like by hack or some other physical way? Thanks for any information
lavidjio
how do you take the linksys router out of client mode to use it in normal operation????