The first full day of DEF CON was packed with hacking hardware and cars. I got to learn about why your car is less secure than you might think, pick some locks, and found out that there are electronic DEF CON badges after all. Keep reading for all the detail.
theSummit
Thursday night ended with theSummit: a party fundraiser for the EFF. Beers were drank, EFF donations were made, and good times were had. The folks from Codame demoed interactive art installations, and Dual Core provided some great nerdcore entertainment.
The EFF ran a DC Dialer phone booth that encouraged attendees to call their representatives and request that they support Aaron’s Law. If you’re in the US, you should read more about Aaron’s Law and how to contact your representative. The EFF has a good overview here.

Hardware Hacking Village
The hardware hacking village was packed today, with many kits being sold and built. The DEF CON Darknet Project badge was one kit that made its debut here. Inspired by [Daniel Suarez]’s book, Daemon, this project encourages conference participants to meet people and learn skills by completing quests. [Smitty] gave me an overview of the board, which uses an ATTiny85 and communicates over IR with other badges.
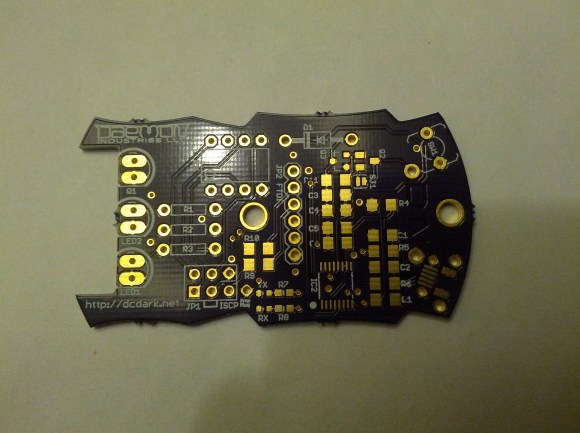
Pairing badges lets you keep track of people you’ve met. There are also skill quests using the badge. Two of these are for assembling the badge itself, one for the through-hole section and one for the optional surface mount section. A lock picking installation called The Rook kept track of what locks you had picked, and transferred the data to your badge. Data from the badge can be synced up with the Darknet website to receive experience points. The firmware is almost finalized, and the entire project will be released as open source hardware shortly.

DLP 3D Printing
[PacManFan] showed me his Creation Workshop 3D printing software. This software is designed to print using UV sensitive ink and a DLP projector. The advantages of this process include high resolution printing and a fixed print time per layer. His software does slicing compatible with G-code, but adds special markers for displaying images on the DLP projector. This allows you to use currently available hardware, such as the RAMPS platform, along with the UV cured resin. The software is written in C#, open source, and available on Github.
Automotive Hacking
[Charlie Miller] and [Chris Valasek] gave a great talk about hacking cars. They focused on Toyota and Ford vehicles, and managed to pull of some impressive and dangerous exploits on both (which we previewed a few days back). The hacks assumed that the attacker has access to the Controller Area Network bus (CAN bus) inside the car. CAN is used for communication between automotive controllers, and by faking CAN signals you can trick these controllers. From a laptop, they were able to actuate steering, braking, the horn, and disable the brakes.
By reverse engineering the diagnostic tools for these manufacturer’s vehicles, they were able to obtain the Unified Diagnostics Services security access keys. Using these allows you to perform actions that are related to security and safety, including re-flashing the vehicles controllers with modified firmware. Ford is currently working with them to fix the problems, but Toyota claims they are only concerned with remote attacks, and that these exploits are not a problem.
DEF CON: The Documentary
The DEF CON documentary premiered yesterday, and is now available as a torrent. You can grab it here.
Tomorrow I’ll be covering more villages, the contests area, and a talk or two.
















Totally want to get my hands on a video of the car talk (see what I did there?)
Here is one video
http://www.youtube.com/watch?feature=player_embedded&v=oqe6S6m73Zw
Ah, nice. Thanks, FJK.
Darknet badge has a typo: JP1 is marked ISCP instead of ICSP. Yeah, I notice stuff like that… and I can somehow still read HaD posts :P
(@SupplyFrame: I’m available for a full- or part-time proofreader position. #OnlyHalfKidding)
ISCP clearly stands for “Intercollegiate Surgical Curriculum Programme”, duh.
Integrated Serial Circuit Programmer?
I just spent several minutes looking for the typo in Eric’s post… ha!
Doh.. we missed that one. Glad everyone liked the HHV IR board. Makes the many nights I spent working on the design, testing, and finally assembing some 600 kits, worth it. Taking from what we learned this year, we have some good ideas to make it even better for next year’s DEF CON.
Nice Post. Thanks for sharing with us.
I wan’t to know has any one picked a medeco lock yet.
https://www.youtube.com/watch?v=AoISzlkmVdc
The reason Ford cares has nothing to do with safety. Ford maintains tight control over their dealers by having proprietary diagnostic tools (the VCM and VCM II) which they sell and charge fairly high yearly licensing fees for. If someone was able to crack the Unified Diagnostics Services security access keys they could make aftermarket scan/programming tools or just relicense existing Ford tools. I know for a fact that many dealers would jump on this if given the opportunity. It would also allow independent shops ability to perform services that are currently dealer only since the VCM/VCM II are essentially DRM dongles that force customers to get service from dealers.
There is an error on the page here. It is the one for author Daniel Suarez’s book. It seems the page confused the name and constructed the link to his pages incorrectly. Clicking on http://hackaday.com/2013/08/02/def-con-hacking-hardware-and-cars/www.thedaemon.com causes the raising of a 404 error, and it doesn’t bring up the author site.
Opps, I dropped the http://. Fixed. Thanks for pointing that out!
…weren’t Toyota the ones that said it was impossible for any kind of computer bug to cause uncontrolled acceleration in the Prius? I’m less concerned about outside hackers and more concerned that these things are controlled by reprogrammable software…
Hey Eric: Thanks for the kind write up of the DarkNet. Only on correction: my name is Smitty, not Scotty. ;-) Also, if you want a link to me, you can link to my twitter: @SmittyHalibut
Thanks, fixed.
Opps, really sorry about that. I think was a bit tired.