Most keyfobs out there that open cars, garage doors, and gates use a rolling code for security. This works by transmitting a different key every time you press the button. If the keys line up, the signal is considered legitimate and the door opens.
[Spencer] took a look into hacking rolling code keyfobs using low cost software-defined radio equipment. There’s two pars of this attack. The first involves jamming the frequency the keyfob transmits on while recording using a RTL-SDR dongle. The jamming signal prevents the receiver from acknowledging the request, but it can be filtered out using GNU Radio to recover the key.
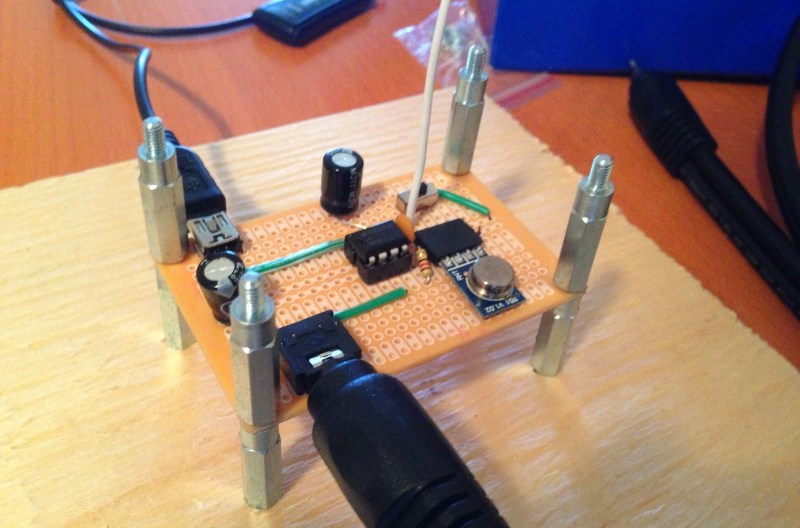
Since the receiver hasn’t seen this key yet, it will still be valid. By replaying the key, the receiver can be tricked. To pull off the replay, GNU Radio was used to demodulate the amplitude shift keying (ASK) signal used by the transmitter. This was played out of a computer sound card into a ASK transmitter module, which sent out a valid key.















brb, FBI.
this sounds like a serious screw-up in the systems design; any key that was transmitted should have been considered “used”, regardless of the acknowledgment. I thought most systems didn’t acknowledge the key at all, but use a window of keys that are considered valid, often 256 iterations after the last key that was received.
This means there are, at any time, 256 keys that would be valid for each keyfob, but effectively losing 8 bits of keyspace shouldn’t be a problem, and can easily be compensated for. It would seem both more secure and cheaper (it saves a transmitter on the lock side and receiver in the keyfob.
Most systems do not ACK the key in the receiver, they simply consider it used and only accept the next few ones for opening the door. He jams the transmission so the receiver can never see that this key was used, allowing him to replay attack it.
Off-the-shelf equipment for this exists for car thieves, see dx.com
Have you got a link or keywords please?
I spent a fair amount of time searching around dx with no luck. I have enough radio modules to do it breadboard style but I would be interested in seeing what an off-the-shelf item looks like and costs.
As the author says, this method will work only with this scenario:
“In a rolling code garage door system, imagine the following sequence of events. The victim presses the button on the RF remote to initiate the closing of the garage door. The adversary jams and intercepts the signal. The garage door therefore does not close. The victim presses the button on the RF remote again. The adversary jams and intercepts the signal again, but then replays the first signal he/she intercepted. The garage door closes, and the victim leaves the area assuming that their garage door is secure. The adversary then replays the second signal he/she intercepted and the garage door opens again.”
In case the victim presses a button on the remote, and if THAT code is grabbed and jammed, it will be useless if victim pressed the button again and vehicle received that second command. Any previous command is discarded if later one is received by the receiver.
You can jam a signal or receive a signal quite easily. But being able to receive an uncorrupted signal while jamming on the same frequency simultaneously is not so easily done.
True!
Really? You create the jam. Signal A + Jam B = C. Subtract B, you get A, no?
Not _that_ easy, but not a huge problem either. A better model would be A+s*B=C.
The constant s would change with transmission power, environment and probabbly distance/position of the transmitters, so first you need to calibrate a little bit or try multiple scalings and look if the remaining signal looks plausible.
As mentioned in the linked post, the jamming signal was simply removed in software with gnu radio.
If anyone thinks there is any “security” in a remote lock/unlock fob, then they are just plain old silly. Even your garage door is dead easy to get into as it’s remote does the same thing. Note the house “remote deadbolts” are the exact same rolling code tech and easy to defeat.
Why? Because the manufacturer does not want to provide real security, and people will whine like crazy if their keyfob does not work. so they make it insecure for price and reliability.
I don’t think the security if the tech is the weakest part of a house door or garage door…
When my place got broken into not a single lock was touched. The guy just took a crowbar to the frame…
Be end is right. Cue this XKCD cartoon:
http://xkcd.com/538/
Sledge hammer to the front door – in and out within 5 minutes. Not nice when it happens to you, but it happens.
Sledge hammer is way too noisy, a battery sawsall just around the outside frame where the lock bolt goes in, door stays locked, door and lock and part of the frame opens for easy access. Door lock and deadbolt, just make a longer vertical cut to encompass both locks.
yeah because 5 minutes of power sawing is so much quieter and discrete than a single hard thump.
shocked and annoyed: Most people wont think anything of the sound of a small power saw being used next door. A sledge hammer to a door certainly isn’t a standard suburban sound.
People living in suburbia would assume a saw is being used for renovations or something equally as innocent.
Overkill, noisy and messy. Two known working alternatives.
1. Commonly used against deadbolts. You need is 2 minutes, a truck jack, and a few wooden blocks in an alloy frame/carrier. Put the frame horizontally in the doorway just below lock level. Then widen the doorway enough to open the door.
2. Used against electronically locked hotel doors. Take a telescopic fishing rod and remove the reel and all the guides except the one on the tip. Attach a length of heavy monofilament to the butt of the rod and a swivel-clip to the other end of the line (adjust the length of the line to suit the purpose). Fully extend the fishing rod, bend the tip of the rod back-towards the butt and clip the line to the end of the rod making a bow. Slide the rod 3/4 under the door with the line against the floor. Turn the rod so that it is forced to bend upwards. Manipulate it so the line near the tip traps the door handle against the rod – then pull down to open the door. Then you are free to enter the room and await the occupants return (or whatever).
It’s hard to define what security really is. I remember reading a comment from here before that “inconvenience != security”.
The only secure house is one without openings for windows or doors. But then that presents additional problems…
Yeah, people have fun playing armchair security expert, but the fact is that real-world security is about balancing the level of threat against the cost/inconvenience of security. You don’t build a tool shed that’s hardened against artillery fire, and you don’t build a garage to resist attack targeted against you in particular by an actual expert. Home security–absent any unique scenarios like a multi-million dollar rare, antique buttplug collection–is mostly about elevating yourself above the low hanging fruit without painting a “I’m full of valuables” sign on your front door.
Odd that this should work, not for the technicality of jamming and spoofing, rather for the way that the majority of rolling code systems work (be they commercially available ones like KEELOQ or custom ones created by a manufacturer).
The vast majority I have researched at their core use an LFSR to generate the randomness. This LFSR is usually seeded by the combination of the fobs embedded serial number, an incrementing counter AND the value of the pressed button.
Recording and spoofing a lock button press would only let you (the attacker) lock the car once more (some models use this for deadlocking). Doing the same for an unlock command would only only leave you with an unlock packet that was valid till the owner then relocked their car again .. thus incrementing the counter and invalidating your stored packet.
May be the easiest way is to jam the frequency to prevent the locking command, but have a hidden speaker that plays back the recording of sound that that particular brand of car makes when it locks. To the owner, he/she thinks the car has been locked, but in reality it hasn’t.
Are you a super villain? That is genus!
Unless you can make the indicators flash three times too, I’m not falling for that!
A) How many people actually watch the indicators on their car when they lock it instead of just listening for the beep as they walk away
B) How many people would just shrug it off even if they did happen to notice the lights didn’t flash
C) How many people would actually come to the conclusion that someone was trying to break into their car with high-tech equipment involving signal jamming and spoofing just because they didn’t see the lights flash
I can’t remember hearing any lock sounds nowadays, all today cars are just silently flashing and maybe that’s a way to make the owner look at their car while locking. At least here in Sweden the cars are silent but maybe the US cars still have the sound?
My car does not make any sounds. It just flashes the lights. So I always look.
The people who make money at it are way ahead of you:
http://chicago.cbslocal.com/2014/02/27/car-thieves-break-into-cars-by-hacking-them-with-black-box/
My guess is they vend the boxes out for a grand or so after making them with $40 of parts – nothing illegal in that per se, though using it might be.
Of course once it becomes part of another security-theater panic, we can expect curious sorts like [spencer] to take it in the teeth, certain electronics to become felonies and related bits of jurisprudential stupidity to occur while the other guys skate.
The only way I can think of this working is if you manage to catch a lock, followed by an unlock, while leaving the user thinking the car is locked and walking away.
Perhaps, while the user if trying to lock the car, if you keep jarring they will press the unlock button by mistake in their frustration, allowing you to replay the first ‘packet’ you captured (likely a lock ‘packet’), and having recorded an unlock that will work on that lock.
However, you most likely have no way of identifying which ‘packets’ are locks and which are unlocks. So you just have to jam for long enough that the average person will go into button mash mode, then lock the car, then once they leave, replay the ‘packets’ in turn until the car (hopefully) unlocks!
I’m not sure what the plan is once you have an unlocked car, though.
No, if you jam and catch catch two “unlocks” and then transmit the first one quick enough, the car unlocks, and you still have the next valid key. Follow to where they’re going, jam the lock code, and you’re good to go. That being said, you really shouldn’t be doing ANY of this unless it’s your car and you just happen to be a tech security enthusiast…
nick stuff inside it, or take your time preparing it for theft(swap ecu, remove steering lock etc) as there is no broken glass or alarm going off. tbf, most cars around here are taken after having keys stolen. if one could do a spoof/replay attack on modern “keyless” cars that’d be smart.
I’m sure it will happen. If wireless CAN hacking won’t suffice, then watch out for implanted bugs the next time you pay for a cheap car wash, oil change or any sort of service job you don’t or can’t perform yourself. As more cars hit the Internet for entertainment, it might even be able to phone home the location whenever the doors are locked. ODB II “skimmers” to hide in plain sight?
Have a try at this house: 35 motion sensors at all access points to the property. 35 cameras with off-site recording, no dead-bolts only Medico key locks, someone always home (staff, etc.), homeowner armed to the teeth, shotgun, AR15, .45s everywhere. Property lit outside and in all night like daylight. House alarm includes impact sensors on all windows and doors, all windows double locked. House alarm triggered instantly when any entry point opened. No window glass large enough to get thru. Generator and USP back-up on entire house and all security systems. Now get in and out.
I would just wear a mask and steal all the cameras. They should net about $100 each on the black market.
Who wants to get into that house? They already spent all their money on goofy security items and have nothing worth stealing except security equipment.
I hope you don’t mind me asking. I want to learn how to hack rolling codes, can you be kind enough to tell me what exactly I need to buy in order to do this. I want to learn step for step while having the items in my possession I would find it much easier that way.
hope to hear from you soon!
thank you
A new key fob for my Jeep is $200. Finding a cheap way to get a second key appears harder than breaking into the car :-(