CDMA2000 was one of the protocols defined for 3G networks and is now years out of date and being phased out worldwide. Nevertheless, there are still vast numbers of phones that will happily connect to it, creating an opportunity for hackers seeking to run their own cellular networks. [Chrismoos] recently made this endeavour significantly easier by releasing 1xBTS, a Rust implementation of the lower three layers of a CDMA2000 network.
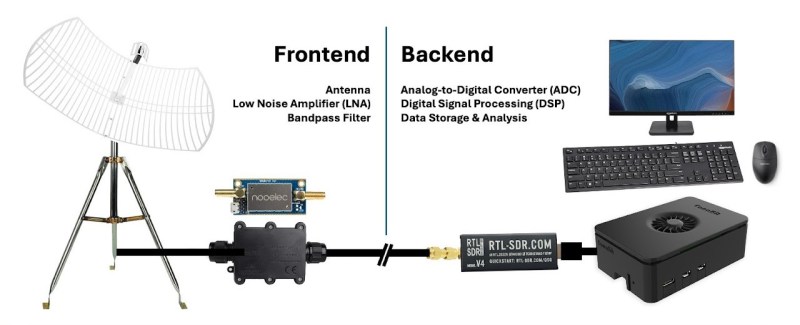
The lowest layer of the stack is an SDR for the actual radio communications. It’s been tested with the USRP B200 and B210, the LimeSDR Mini 2, and the BladeRF Micro 2.0. The code might work with certain other SDRs using the SoapySDR abstraction layer. The SDR is controlled by the base station (BTS) software, which, in turn, is controlled by the base station controller (BSC) over an Abis link. The BSC manages channels and mobile device associations, and exchanges frames with the mobile switching center (MSC), which handles message switching.