http://www.youtube.com/watch?v=RYaz-s5SXCc
For months our dear Hackaday readers have been following the Mooltipass password keeper’s adventures, today we’re finally publishing a first video of it in action. This is the fruit of many contributors’ labor, a prototype that only came to be because of our motivation for open hardware and our willingness to spend much (all!) of our spare time on an awesome project that might be just good enough to be purchased by others. We’ve come a long way since we started this project back in December.
In the video embedded above, we demonstrate some of our platform’s planned functionalities while others are just waiting to be implemented (our #1 priority: PIN code entering…). A quick look at our official GitHub repository shows what it took to get to where we are now. What’s next?
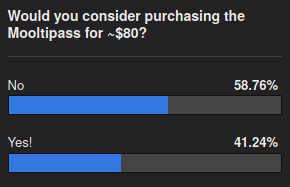 We need your input so we can figure out the best way to get the Mooltipass in the hands of our readers, as our goal is not to make money. The beta testers batch has just been launched into production and I’ll be traveling to Shenzhen in two weeks to meet our assembler. When materials and fabrication are taken into account we expect each device to cost approximately $80, so please take 3 seconds of your time to answer the poll embedded below: (poll has ended)
We need your input so we can figure out the best way to get the Mooltipass in the hands of our readers, as our goal is not to make money. The beta testers batch has just been launched into production and I’ll be traveling to Shenzhen in two weeks to meet our assembler. When materials and fabrication are taken into account we expect each device to cost approximately $80, so please take 3 seconds of your time to answer the poll embedded below: (poll has ended)
















Hi Hackaday,
Is there a second mode planned? for example emulate a usb keyboard and store for example 20 complexe passwords and press a button to write the specific password? i am asking this because i already have 2 password managers, so cool would be to use it also for truecrypt dull disk encryption or for bios/uefi password. Also it would be very handy to import from other password stores (import everything from keypass, lastpass). Will we be able to do a backup of the passwords/datastore? possible to clone the smartcard to a second smartcard for a banksafe?
Thanks in advance for a quick answer….
HID Device support and im in for sure…
Best regards
Mike
Hey Mike,
There will be a menu on the mooltipass itself that will allow you to make it type the passwords for you, as it is detected as normal keyboard (HID keyboard / HID proprietary)
We have a planned “favorite” feature that will give you easy access to your most used credentials.
Cheers,
Mathieu
I plan to get one to store my passwords for work(nearly 100 of them), this is exactly the mode I need for it :-)
I use a smart phone, a tablet (Android) a laptop and desktp with several VM on it.
How could I use this to access the same sites?
You can connect the mooltipass to any USB OTG enabled portable device (that’s most of them nowadays). As shown on the video, you can store several credentials sets for a given website/service on our project and select any one later.
Or you could have several mooltipass and synchronize your credentials on them (our export feature is already implemented).
I like the thought and I do want to increase my login security, but I don’t see this version answering my needs. So, I voted no, but felt it necessary to provide feedback on my no answer. I wish the project all the best.
I want it to help me login without plugging in anything external (USB port, etc)
I want it to connect wirelessly but only when I want it to (enable/disable switchable)
I don’t want to have to interact with it other than to enable/disable it.
I want it to be able to create an encrypted file on demand with my login info so that I can recover the login info if necessary
If I use it to log into a computer/device that’s not mine it removes all traces of my being there.
No problems, we appreciate constructive criticism :).
We thought of a wireless version but were ‘affraid’ of all the added costs due to the different certifications involved (RF, li-ion protections…)
Not plugging in was probably the most argued for feature that didn’t make this version, as I understood it mostly due to the effort required. And while I don’t have any experience building or programming with wireless, I’ld expect it to be a lot of work. I’ld beta/buy a wireless version.
>I like the thought and I do want to increase my login security
More complex systems have more bugs and more security risks. And yet you are asking it to be wireless (vs a wired system that outsider cannot snoop).
>If I use it to log into a computer/device that’s not mine it removes all traces of my being there.
Being watching too many badly written movies? That’s not what it is for.
I have strong feelings about wireless for just that reason, but all things being equal I’ve got 100s of accounts that are of low enough impact if hacked, wireless would probably be okay. The other 100 or so, maybe I’ll go through the bother of a hard link.
Wireless would be nice, perhaps it would be possible to mod a standard cheapo wireless keyboard transmitter to work with one like the logitech unifying kit type deal
Wireless would probably mean bluetooth, which might be nice for phones and laptops, but most desktops don’t have bluetooth support build-in (at least mine don’t). Bluetooth does offer authentication and encryption protocols, so after pairing the device with a computer or phone, the connection should be reasonably secure.
Not wanting any further interaction sounds like a VERY bad idea, because a compromised computer could simply read all username/password combinations from the Mooltipass without user interaction, and you’d never know it happened until everything you used it for is compromised at the same time.
One feature that might be useful would be to have the device also enumerate as a storage device, with the plugins for various browsers available on disk. On the other hand, any computer you would use it on which isn’t your own would most likely have an internet connected so you could download the plugin, and you probably can’t or aren’t allowed to install plugins on most computers you incidentally use as a guest anyway.
Is there an option to have the Mooltipass generate secure passwords, instead of having to enter them manually when they are first used?
looks great, maybe mitered corners?
We actually thought of that for the acrylic front panel. I’ll be asking the manufacturer when I visit him in Shenzhen.
Thanks for that first preview. I really like seeing the results of such a project, developed by so many people, thats awesome! I also like the design and the Jedi sensor, though i find the scrolling time between the inputs maybe a tad too long. I dont like applications which react slowly when you are using them on a day-to-day basis, knowing already what options are going to show up on the next screen.
Personally, i don’t see a need for such a device. Yes, i don’t care that much about my security, i don’t do online banking, develop anti-missile systems or write critical articles for NGOs. That is why i voted no, i’m just not interested, sorry. My interests are in hacking and building stuff in an open source manner, not in locking away any of my data with an extra device (and smartcard and plugins/software).
On this particular video we’re fetching the bitmaps from the external flash in a _very inefficient_ manner (we just finished implementing it yesterday)… so we’re quite sure it’ll be much faster in the future.
The mooltipass isn’t really for the use cases you detailed, but at least allow you to have different passwords for the different websites you visit :).
This looks pretty cool, I think what would put it from pretty cool to perfect would be to make some kind of sync feature with existing password managment tools, in my case i use KeePass.
I know i could bring it with me and use usb otg, but my idea is that i leave the mooltipass at work, and just remove my card at the end of the day, before doing so having it sync with my keepass file i keep in the cloud for my mobile/home pcs that i’m not as worried about.
Either way I’m pretty excited for my beta unit, and really hope by then there is at least an import tool to take all my passwords from keepass or some other similar format (it can export csv,xml etc)
I like this idea a lot! At present, I’d pay no more than $60 after tax and shipping, and I’d have to be in a good mood at the time. This idea might bump that threshold up a little bit.
Actually it should be fairly easy to devise some import tool… it’d be even easier for the plugin to parse your csv file and send the create credentials commands…
Wow, the user interface looks great. The demonstration of multiple-account storage is a feature I didn’t know about, but now I really want to give it a spin!
Oh really??!! Hopefully you can get your hands on one!
You’re telling me! I’ve been looking for Mooltipass for years, very fortunate to be beta testing.
I’ll admit i really haven’t followed this thing at all. But I see a bunch of contradictions in a device such as this. I know using the same password over and over is bad, so you should have a unique password for everything. I myself admittedly use a software app to do this. However, storing your password in any kind of readable format is defeating the purpose of passwords. The human mind cannot (yet) be read by anyone else. So remembering your passwords puts up a gate that cannot be bypassed directly, sure you can infer things, and social engineer, etc, but you can’t plug a brain into USB. Using a software app or hardware in this case puts all of your passwords in one place behind a single password… Which can be cracked. Not easy to bust encryption, sure, but it can be done. So you take the hardness of the mind and the security of multiple passwords and make them one in software or a hardware behind a single password. How is this thing safe? It plugs into a USB port, and if it can dump files or data over that connection, or worse, send keys as an HID, it’s sort of useless as far as security, no? And *GASP* open source, so I have everything I need to root the thing, right? I mean, its better than no password, and maybe better than software, since it can be disconnected, but how is it dfferent or better than any of the other hardware password storage solutions out there?
Hey Duwogg,
I’ll admit i really haven’t followed this thing at all.
>> But you’ll still formulate comments based on assumptions that you didn’t take the time to check. I’ll therefore point you to our FAQ here: https://github.com/limpkin/mooltipass and answer some of your questions.
Using a software app or hardware in this case puts all of your passwords in one place behind a single password… Which can be cracked.
>> If you had looked at our project description’s you’d have seen that 3 wrong tries of this “single password” would make your passwords unrecoverable.
Not easy to bust encryption, sure, but it can be done.
>> Just do a quick google search so see how long it’d take to bruteforce AES-256 encrypted data blocks.
It plugs into a USB port, and if it can dump files or data over that connection, or worse, send keys as an HID, it’s sort of useless as far as security, no?
>> It basically plays the role of a “super brain” that could make you type unique passwords for every single service.
And *GASP* open source, so I have everything I need to root the thing, right?
>> How about you take a few minutes of your time, check our source files and let us know how you can “root” the device from the outside? I have difficulties understanding how having something closed source will prevent you from being rooted. We welcome people that want to improve the security we implemented.
how is it dfferent or better than any of the other hardware password storage solutions out there?
>> I’m sorry but I’ll point you to the many discussions we had on the matter… but take 30secs of your time and have a look at our FAQ. In short, our solution prevents your passwords to all be “hacked” at once.
Wow,
So seeing how one of the creators and HaD editors was pretty rude to me, maybe someone who just reads HaD casually and has no clue as to technology, why the f*ck would I waste my time? I would say the first thing i would do if I wanted this to sell to the public at large is fire you as the PR guy!!!
You make the assumption that I know anything about any of this, so when I have the opportunity to ask some simple questions, I get attacked?
I’d like to see how long you’d last at the local best buy selling anything tech related to J.Q. Public…
Yikes.
You weren’t ‘attacked’ in any way you were merely given concise information about the points you brought up and you were pointed to the FAQ. and if you find seeking information about something you don’t fully understand an ‘attack’ and call learning something ‘wasting my time’ then please.. do get off the internet and stop bothering others when they try to inform you. or just keep quiet.
ontopic:
I’d pay about $35 max for this (otherwise i’d make something myself if i wasn’t content with KeePass), I understand that this probably less than the cost but I would personally remove things like the smartcard functionality (seems like a gimmick to me) and make it cheaper to produce by opting for a simpler case, swapping aesthetics for cost.
I don’t need beauty in a security device and i’d rather have actual buttons for navigation instead of touch. maybe something that looks like the things used for online banking but then matte black and with a backlighted screen. one of the banks i uses this device: http://www.asnbank.nl/upload/c357214a-d383-4b0c-a3e9-236eff9905a8_digipas.jpg
And having now read the FAQ, why would I bother trying to brute force AES256, which again isn’t perfect, there are holes, and GPU’s are pretty freaking fast, when i could simply stick a keylogger on the target machine because it does send keystrokes as an HID and blamo!? Or I spoof a webpage or email account of interest and this thing says *OK!* and sends me the passwords? And why would I want both a smartcard reader AND a smartcard, which are both going to get carried around together, which really just leaves the PIN, and if I do break the smart card in three tries, I can see this going over swimmingly, ebcause hsit ahppens… They make smart card readers already, so what does this buy me, a PIN? No thanks… I’ll pass… Or not.
If your data is valuable enough to be worried about AES256 then you’re just not going to find a good device in DIY solutions, you’d be better off looking at solutions offered by a company like Vasco.
As mentioned in the FAQ our goal is to reduce the number of attack vectors, which is why the mooltipass is entering passwords for you as if you were doing so yourself.
The screen is actually there to prevent the impersonation attack you’re mentioning (why would the user approve a request if he isn’t visiting the said website?).
The smartcard allows to deny access to the encryption key when 3 wrong pins are entered. This is the key element of the security chain.
I’m just saying, as a product, beyond being a novelty becasue it was created by HaD (sort of), there isn’t much to offer. It appears to have been a fun exercise by the creators, but honestly, it isn’t terribly useful over what’s already out there. I can get software for free that runs on my PC and also on my smartphone that syncs with those machines. So now I’m covered everywhere. And for those of us that work on machines that can’t have USB devices pluged into them all willy-nilly, the smartphone is the only other option.
Sooooo:
It’s not really all that secure.
It requires me to carry yet more stuff around, which my smartphone lets me carry less stuff around.
Some of us cannot plug whatever we want into our work systems, so it would have limted usefulness
And the marketing is really lacking. You point out some flaws and get blasted, when just trying to be honest. Ok, so I was baiting a little, but you’d have to expect such questions should you ever decide to mass market this… Not everyone knows everything. Do you own a car? are you a mechanic too? etc…
Finally, looking at the poll results, I am not alone in saying thanks but no thanks.
I’m just trying to say why I wouldn’t bite as well as try to squeeze the salesman a little bit to see how honest he’s going to be with me. Kind of brutal… but it tells me I wouldn’t buy a snowcone in hell from this guy…
Welcome to marketing a product…
It doesn’t have to be only hardware (though that is a must have for me), it’s open so people can add all the software support they can manage. They can also audit the software a feature unique to all the hardware options out there that I have seen. Not doing it all in software was one of the founding features. If a person is comfortable storing that information on computers or smartphones why would they buy hardware for it?
This version wasn’t designed to work places where you can’t plug stuff in. It’s these cases that I want to be able to display the password on the screen. Wireless is a much called for feature, would that meet your need with not being able to plugin?
How is your smartphone app more secure as than the pin and passcode you use? How is Mooltipass less secure if the pin is as long as your pin and passcode? Some would argue that having that information on a device connected to a network is less secure than having it offline.
Carrying less stuff around was a must have feature for me. Mooltipass lets me carry just the smartcard. Currently I carry a separate hand held device for managing my 400+ user/passwords. Wouldn’t you agree that carrying a smartcard is less then carrying a smartphone? I suppose if you’re gonna carry a smartphone anyway… but what if your not, or if you are particularly worried about theft or seizure?
From what I understand a 38% conversion rate is a winner and given all the comments it sounds like there are plenty of opportunities to get it higher. This is great news!
My interactions with Mathieu as a possible contributor and beta tester, has led me to believe he isn’t in this for the money. He had a vision, he made it a reality, I’ve been looking for that reality. If he gave any indication of being in it remotely for the money I would have been a contributor. I just don’t have time to code on yet another open source project without the possibility of a monetary return on investment.
Regardless, something great about Mooltipass is how few people it has taken to have a bit of fun and quickly create a device that meets their needs and that they went on to share! It’s great that if it doesn’t meet you’re needs you are allowed to make it do so and you can share that information without fear. To reach early adopters things can be far from perfect. IMO the early adopters for Mooltipass are the people that do have the skills to fix the things they don’t like about it.
I might get one for 50 bucks but thats about as high as I would go.
believe me when I say that we wish we could sell them for 50 bucks…
then make a separate version with normal buttons and a non-fancy case without smartcard :) call it a “Mooltipass Mini” or something.
it isn’t the case that drives the cost up… but we could definitely make a tiny version in the medium/long term future.
well OLED displey will be pretty costly, it would be nice if you could sell only mounted PCBs.
Stripping off the blinkies/smart card/arduino form factor off Mootpass , you can have something like this: http://hackaday.com/2014/06/14/the-worst-e-reader-ever/
This is much closer to my vision of a pass key. It is much more portable and less draining on wallet and that’s why I avoid the Moot pass project. Lose the battery and throw in a $1-$2 8/16MB SPI FLASH chip for storage and you are there.
One can probably sell it for $35-ish in small volume (if parts sourced and assembled in China) Probably can port the moot pass firmware over as that’s what open source is all about.
that’s actually an excellent suggestion.
If you ever want to have a go at this, we’ll provide you with support :)
What about make something tiny that slips on the Mooltipass smart card and acts as a read-only device? One could have the best of both worlds!
That would be something I would definitely buy! I would even slap a SD-card reader there to store the password database. SD cards are ridiculously cheap now a days, even if you buy one just to store a couple of hundreds of kilobytes on it.
So in summary, this is what I would want:
1) Small for factor and cheap (so I could buy several, one for work, one for the phone, one for the desktop).
2) Password storage in a removable device (SD card, etc..). I don’t want my encrypted password list in the internet (like software keychains do). I can to carry the SD card with me at all times, in a keychain for example.
3) Multiple authentication modes: Using a pin password + fingerprint reader + color code (or any other authentication mode different than pin code) combo to generate the password hash would be a plus. In case my SD card is lost, at least the password database would be encrypted using a strong hash (for AES you cannot go much higher) or even triple-encrypted using different ciphers.
Would it also be possible to make the interface on the mooltipass appear on-screen instead and spare the screen and buttons? And the motion-detecting-thing (pardon my laziness to not remember what its called) also be spared? Over all it seems very elegant and DEFINATLY something I would want to own as is… But its a bit overcomplicated isn’t it?
Does this support more than 2 accounts per website? Also, what happens when the username is longer than the provided area?
There’s no limit on the number of accounts. We haven’t decided if we will either trim or scroll the different user names :)
tjb1. My name is Mike and I’m the contributor that implemented the underlying data storage on this project. If you would like to see numbers on unique (unique web page + unique login + unique password) credentials that can possibly be stored.. please check out this sheet https://docs.google.com/spreadsheet/ccc?key=0Ah9q_27isFGDdDRfNS1wVUlpaHpWYm5HRmk4b3E0OGc&usp=drive_web#gid=1
Can you please expand on your second question about what happens when the username is longer than the area provided. I just want to make sure I am following. Currently, the max size of a login field is 63 characters of ASCII (including a null character so say 62 characters). I am unsure how it will be handled if your login is longer than 62 characters at this time.
like a wifi password? Some are longer….
Dunno if multipass is for browser only, or it can be used to other gui apps (eg. networkmanager) too.
It isn’t browser only :)
I was just wondering what happened when the name length would be longer than the area where test and test2 are. It doesn’t look like it can display a much longer name than what was shown in the video with multiple accounts.
The accounts questions was because I’m not sure how you select others. I guess you have more buttons than just left and right. I watched video on break at work so I didn’t have any sound which may or may not have explained some things.
tjb1. The UI is still in Dev (some other comment in this thread). As Mathieu mentioned that part was implemented yesterday. Please feel free to post suggestions! I’m fairly certain that there well be (planned but not just implemented) to easily switch between websites on the device. If the ‘display’ name is larger than what can be displayed.. I believe Mathieu answered that with either a trim or scroll (or possibly gui layout) As for actual storage. If we over run that limit (62 / 32 for login / pwd) we may need to revise the underlying storage system to allow for longer logins / pwds. This would decrease the maximum number of unique credentials that could be stored. I am also unaware if there would be any implications on the encryption side of things. None pop to my head. But we will cross the storage issue when it becomes a problem (as I sit here already thinking of a solution). But regardless.. There will always be a finite amount of storage. It will come down to what is the best compromise given x parameters.
First of all well done for a great job you did on this. There is a lot of work in something like this and it’s not trivial that the end result is very nice. I would work on the usability a bit, like having to press less stuff on the device and more on the screen so the workflow will be faster. Regarding the price, I think you should look into crowd funding or something to bring the price down to around $50 and you will have a much larger audience.
Thanks for your nice comment.
As for the workflow, it is true that first setup can be a bit cumbersome. However as you can see login recall is done with only one touch.
We’ll definitely work on bringing the price down… perhaps an early bird for Hackaday regular readers?
I can’t really estimate how many people who are Hackaday users are potential customers, however the site can do a wonderful job spreading out the word about the product which will help leverage a crowdfunding campaign. One way that you could bring the price down by a significant amount is to get rid of the display. I’m, personally, all for doing everything on the computer. I don’t know how much you pay for these but the fact I paid $7 for a really tiny OLED displays means these ain’t cheap. I know it’s a bit frustrating to hear something like that after you spent hours working on that feature, however sometimes it is for the best. Having no display would make the device smaller and cheaper to make. The cool blue LEDs can stay! :)
I don’t think frustration plays into it. The team wanted something, built it, and were generous to share it. Now that I should have the device I have wanted for years in a few weeks, I realize that I do want something like you are describing, but read only for my low security credentials. I could go as low as 1 blue LED.
dumb noob here, this looks like something that would work well on kickstarter/indiegogo to help get this off the ground. If there is something similar to help fund this, let me know and I’ll input and spread the word.
I love this idea and have been following the updates as HAD posts them in this form, but I have not spent much time at Git. As a result there are plenty of features I am not aware of, however I had the following questions:
1. I know that it was designed to be “big” due do the arduino and OLED, etc. But is it possible for me to take the code a stick it on something like a Teensy? Just looking to see if I could use it in a “slimmer” fashion. I have given it some thought and am not convinced that the OLED is completely necessary for most people.
2. When is the device going to be available for purchase? I haven’t found a release date…
Looking forward to hearing more, very excited and interested!
1) Of course, as long as there’s a way to visualize the service you’re allowing your credentials to be sent to to prevent impersonation.
2) Hopefully we should start taking pre-orders of some sort (final solution still to be decided) by mid / end september.
Thanks for your support!
This seams like a rather cumbersome device to take around with oneself, could have been a lot smaller.
It also doesn’t look like a safe way of storing a password, as the device could easily be taken. (when plugged in with card and everything, (And if you need such a device than you can probably not do much more then run after the guy))
And for a price of 80$ I would rather go with a small piece of paper. (As it’s a lot cheaper and probably even safer, considering that one keeps eyes on it while using it, or having it stored away in a wallet or something)
If it just was a small USB stick that was only plug and play, then I might be more interested, as it’s easier to keep track of. (If one has it on a key chain all the time)
The “smart card” is unnecessary, if one keeps an eye on the device. (And if the card is a key to the passwords, then we can hack around that.)
The pop-up looks rather annoying, why can’t it just update automatically, and display that it’s a new password/account on the device.
I see this device as a rather bad thing that can be replaced with cheaper stuff (aka paper) and is only making the storage of passwords less safe in public areas. (aka LAN parties)
I’ll only answer your security concerns remarks:
– anyone can steal your piece of paper
– following your reasoning, a pin code for your bank card is pointless as well
– wouldn’t it be a problem if some app would just request-bomb the mooltipass to store fake credentials?
1. Yes, anyone can steal a piece of paper. (A bit harder if someones already holding it.)
2. Pin numbers are short and can easily be remembered and are a safety feature. (As long as someones not leaning over ones back when one writes it)
3. And yes it would be a problem if an app tried to store a lot of credentials on the device, tho the device doesn’t need to store it automatically, you would still need to push a button on the device. (And anti-spam as existed for some time, because why would you enter 50 different credentials in under 5 seconds?)
1. My guess is that you aren’t always holding it though
2. And that’s why we have one… but it seems you were criticizing it : “The “smart card” is unnecessary, if one keeps an eye on the device. (And if the card is a key to the passwords, then we can hack around that.)”. Remember, the smartcard holds the encryption key
3. then it’s just a matter of time before your device is full of buggy accounts then. We’re therefore asking the user to press a button.
As far as cost is concerned, I wouldn’t pay $80 for it… but I’m a hardware hacker and student, the tightest demographic ever discovered :p I suspect the large number of ‘no’ votes are due to others who know the BOM cost and can’t justify the price to themselves. I know that price selection is hard (I just abandoned a business idea because I couldn’t bear the feeling that I would be ripping people off) but you people know what you are doing – trust the maths :) really good work everyone who was involved, and good luck taking it forward!
I’m voting “no” simply because I don’t want a box to store my passwords in. If it was $10 I might be tempted but probably not. Password security’s only as important as the stuff it’s protecting. A few logins to web sites like this one, wouldn’t harm me if I lost them. My information’s just not that valuable, most people’s isn’t. My signature and my bank’s PIN I keep intracranially, hack-proof for as long as I keep my head out of giant scanners.
What I DO want, is a smart watch that I can program. Nobody seems interested in making them yet, though. The few first efforts are over-priced, under-powered, and closed. If the smart-watch fad takes off, somebody’ll end up hacking the ones from China, and I’ll be happy then.
There was a recent watch on HAD, but it’s based around a $70 Arduino board. 70 fucking dollars! For a board with a chip on it!
The question is not if I would buy such a “pass” for 80$, the question is if I would buy anything that relates to encoding, if it is made in China.
If you don’t trust what we ship you you could always recompile the source code and program it yourself…
The firmware would be the suspect. Next, the hiddenware, buried in innocuous counterfeit chips.
And no, I do not believe the two towers were not brought down by the US government. Nor the Chinese, :)
Your motherboard’s probably “infested” with Chinese chips anyway. There’s only so much you can do.
There is a “your motherboard is so fat with passwords…” in there somewhere, but I’ll refrain myself.
I use stuff made in China all the time, but I am not, will not, store my passwords in any of that stuff. The people who manufacture these devices most likely don’t give a hoot about my, or anybodys passwords, but they sure are aware that their government does, and that their government can make them disappear, along with their companies, at a moment’s notice.
Considering the respective levels of organization, funding, and corruption, you probably have much more to worry about with the NSA and American goods than anything made in China…
American goods? Like, plywood from Down South? Jack Daniels? And the NSA is MY NSA, Beijing on the other hand, is too damn far to be able to meaningfully retaliate….
Oh yeah, if you don’t like the NSA you can always vote yourself a new one!
Looks pretty good so far. I’m sure during the beta test, some tweeks and stuff will be made to improve usability etc, as the use cases are better understood. Its like any product, you do a first pass and make adjustments from there as it matures and you learn its place.
Honestly, it looks like its coming along really nice for being a community developed project. I wish I could have contributed some more, but my prior obligations prevented it… Not enough time!
I think the $80 price point is a bit high, but not terribly unreasonable. I would be interested in an early bird or something similar for hackaday readers. If you get them to sub $50, you will have no trouble selling them I think…Crowdfunding may be the answer in this case.
That’s exactly why we’re doing our beta testers program… thanks for your comment.
We’ll try bringing the prices down for Hackaday readers, google group/hackaday.io followers…
It looks great but I would definitely prefer a more portable version without the removable smart card. I don’t have a fixed desk so I would be moving the whole device around.
In addition I would probably prefer a version without the case.
How do you compare with other existing product on the market, and convince people paying $80 for yours over certified ones? For example, the $89 IronKey 2G model with RSA Identity Manager, VIP for eBay and Paypal, strong password generation, Tor based secure browsing, and, 2G of secure hardware AES256 storage in a tamperproof package? It may looks like comparing apple with oranges, but functionally I can’t see something cannot be accomplished with the IronKey and your product can, and even there is, how to justify the $80 price tag.
Thanks for the link! This looks like an extremely neat device.
Correct me if I’m not mistaken (the technical description is a big vague) but it seems that to access the storage contents you need to present a passphrase to the key itself.
If so, the main difference with our device is that this passphrase is entered from the outside (entering your pin code) rather than from the inside.
Again, if I’m not mistaken, then if one program would hypothetically sniff this passphrase on your computer then all your data could be recovered.
I’ll continue looking for more details…
So the main difference is that when the host is compromised, your product offers a higher level of protection than others?
That is the basic idea. The user must authorise each login on the device to get access to the password.
The product is a neat idea, I’d rather use the secure storage on a SIM card. That would shrink the physical size down a lot.
So this is basically moving UAC click to outside of the OS. Fine, but I don’t see why, on a compromised host scenario, this product is really offering better protection. No detection of breach, trojans and malware can still go undetected with so many attack vectors unnoticed for who knows how long.
Cheap, too. You can SIMs for either 1 pound each, or nothing, if you just ask a phone company. They’re nifty little things, will lock themselves up completely if you get the password wrong enough, and can store a good few K of data.
Also innocent-looking and easy to conceal. You could even use your phone as it’s interface, via editing the phone book to change the stored data. As long as you store your data in phonebook-compatible format, which isn’t hard.
This is the sort of idea somebody should’ve thought up ages ago! Unless they already have. Much better than smart cards! In fact a PIN-protected SIM, together with a phonebook full of passwords, might replace half the gubbins in the Mooltipass. Something for the cheap “micro” version maybe.
Why paying more to something which is:
1. open source
2. developed inhouse, know-how is around the project, easily accessible
3. you can directly contact with the person who *made* the project, and not the sales people.
4. easily modified, small addition are possible, maybe they even endorse you in your adventure
5. Any information is public around the project, nothing paywalled. Hell even the project budget is freely browsable (I have seen a google docs published on the mailing list)
All the above, if I would be interested in this gadget, and I would hesitate between this and a ready made solution, I would seriously consider this.
(Ie. I would pay more then 50% for this then a commercial one).
I have not made up my mind if I really need this.
I’m kind of good at password remembering, and I’m a fast typing guy.
OR I never burned my hands yet…
TL;DR; you get more then the actual product, you also get the whole knowledge around it, future support beyond anyone could offer commercially.
wow thanks :)
np.
I may even buy one of it, just for the tech involved (touch buttons, oled screen, microcontroller, etc)
(((I would really like some kind of editing functionality: I’m really ashamed of all my grammar errors, missing words.)))
It is arduino compatible after all… just slice the openings on the back and connect your favorite shield ;)
Yup, this mirrors my own thoughts. Add 400+ user/pass combos and this is the cheapest/safest (only) solution I have found.
>>Why paying more to something which is:
>>1. open source
Well it depends. I don’t see open sourcing a project or not make a big difference. Kerckhoffs’s principle is not easy to apply when the system is complicated than, say, a simple cryptographic algorithm.
>>2. developed inhouse, know-how is around the project, easily accessible
Yes this is good for learning and education. But that’s it all about it. How about a security product that is focused on security itself?
>>3. you can directly contact with the person who *made* the project, and not the sales people.
I do this all the time at work negotiating with sales, and don’t have problem with that.
>>4. easily modified, small addition are possible, maybe they even endorse you in your adventure
Agree, dev boards for higher hackability usually cost more.
>>5. Any information is public around the project, nothing paywalled. Hell even the project budget is freely browsable (I have seen a google docs published on the mailing list)
Again it really depends. Not that I agree security by obscurity, but there are times drawing a line at what is seret is a subjective issue.
I’ve looked at IronKeys. I see lots of the same issues that other comments are saying (negatively) about mooltipass (so at least we are in good company). What I get out of mooltipass that I haven’t been able to find anywhere else are; remove the memory (via smartcard or whatever), especially when I am traveling. I want to be able to backup, not online, not on a computer, on another smartcard. I want to be able to hack it. I’ve done embedded stuff before so I can update the software as I need/want. It’s closed hardware/source, maybe lots of people don’t care about that, which is fine, but I do. Speaking of it being open, it can be modified. If people want a tamper proof case with the memory sealed in side, they can build one.
you dimwits realize market research is supposed to be done _before_ building a product, right?
which is why we asked for feedback 6 months ago when we wanted to start this project.
We’re just asking feedback to find the best way to bring this product to the hands of interested persons.
this project is a shining example of “design by committee”
remove some of the wankey features to lower the price to ~$50 and ill buy it … $80 is simply not worth not making my own
what do you consider these wankey features to be? As you can guess it’s tricky to please everyone…
IS the smartcard really necessary? It makes the whole device kind of bulky.
I’m total noob in security, but nothing else can offer the same security level?
I mean if I lose this gadget, I will most probably lose the smartcard along with it, plugged into the device.
It is a real security addition if its plugged all the time?
It’s like leaving the car key in the car all the time.
OR are you supposed to keep the smartcard in your left pocket while the device in your right?
I completely fail to see the additional security offered by a smartcard. Its like my sim card in my mobile phone, it is just in it all the time.
The smartcard provides several features:
– added redundancy
– automatic lock after three tries
Anyway if you at least made a copy of your smartcard (we’ll ship 2 pieces) and have backed up the mooltipass memory contents you don’t have to worry if you lose 1 smart card & your mooltipass.
In your analogy, the smart card is your car key indeed.
What is the “supposed use case” here?
a) Are you supposed to leave the smartcard in the device all the time? (with manual backup (one week?) to your other smartcard)
b) Are you supposed to unplug the smartcard when the multipass in not in use?
a) you aren’t. You don’t need to make a regular backup of your smartcard as the data stored in it won’t change (AES key).
b) you’re supposed to unlog… removing the smartcard is an easy way to do so
It depends what all security steps you want to be able to take in a given situation as if the smart card is necessary or not. When I travel, my smartcard will not be in the device, it will be with my ID and credit cards and it won’t be the smartcard with all the cool graphics on it. The mooltipass will be in my bag with all my other electronics. There has been some interest in a sealed tamperproof-case. I suspect someone, is gonna make a mooltipass like that.
Its exactly like leaving your key in your car. The encryption “keys” are on the smart card. Borrowing your metaphor, Is your car key really necessary? obviously your just going to leave the key in the ignition all time, since that easiest.
Well, I suppose that I am late to the party, having not participated in the initial feedback gathering six months ago. With that in mind, here are my comments…
1) The entire UX seems quite complex and tedious compared to a 100% software solution, such as lastpass. Yes, I realize lastpass is a different type of product, in that passwords are stored on the card in the mooltipass. I don’t really see any increase in security in mooltipass over lastpass (or equivalent.), but I do see much more complexity and bother.
2) To expand further, why doesn’t all user input take place via the browser plugin? Why should I have to do some things via the plugin and some things by physically “pushing buttons” on the mooltipass? Having two locations to interact with what should be a simple application seems needlessly complex and confusing.
3) Again on the topic of apparent complexity… why isn’t more functionality in the plugin, with less in the hardware? For example, all of the passwords could be stored in encrypted form on your desktop/browser, and you could use the mooltipass simply for decryption/encryption? That way, the user would never have to interact with the mooltipass hardware at all (other than to insert their card). And sharing / use of passwords across machines would be simple.
4) Detecting hand movement to enable the lower part of the display seems to be nothing more than a gimmick. Does it really serve any true function?
5) I guess that the ‘dashes’ on the right/left of the lower display function as ‘yes/no’ soft keys. If so, why aren’t they labelled as such, rather than simply being cryptic dashes? In general, the UI (all the lights, displays, etc.) seem to be very complex and visually confusing without actually making the device easier to use.
When I was just reading about the mooltipass, it seemed that it might be “ok” or possibly useful. However, after seeing the demo, it seems to me to be cumbersome and very gimmicky. In other words, most of the complexity and cost associated with mooltipass seem to have little function over that of looking cool. I really don’t see much value add here.
I have to agree, in principle, with some of the comments regarding an absence of market research prior to going into design and product creation. A logical first step would have been to create a functional mockup as quickly as possible solely for the purpose of letting people see what it would look/act like in real life. This could have been done very quickly (i.e., a few weeks) with a few displays and software running on a PC or full-blown development board. Yes, such a prototype would have no relation at all to the final hardware, but it lets one get to an answer much more quickly and with much less expense/effort than going from paper to something like we see in the video. I really do think you skipped a few steps here.
In brief, our advantage over a software based solution is that not all of our passwords can be compromised at once.
Hypothetically, given that you have your lastpass main passphrase in RAM at a given moment and your password database on your hard drive, it could be possible to decrypt all your passwords at once.
that makes no sense. you could still have your hardware decrypt passwords one by one on demand and require no user interaction outside the computer.
The user does need to approve the credentials sending.
Thanks!
1. By it’s nature, the project wasn’t interested in an all software solution, it is hardware. I’m actually interested in even less software, but seeing these folks in action I feel better about the software parts.
2. Input from the plugin sounds like an interesting feature. Maybe the button pushing could be an option, personally I want to see each request so I don’t fill it up with garbage if something goes wrong. Esp since I’m a beta tester.
3. Being stored not on a computer is seen to us as a feature. That’s why we call it offline. I hadn’t really thought about only having the hardware do the crypt. Might be an interesting concept for an optional feature, though I don’t see myself using it.
4. I’m thinking it could be used as the pin or part of it.
5. I’ll have to see if I feel the desire for labels once I get some hands on time. If we do end up labeling it might be more cost effective to use icons.
I think there is room for a read only mooltipass. I’ld beta/buy that too.
They asked, lots of it happened on google groups. Many of them are now on the team or trying to get on. I was pushing for a much more minimal initial feature set, but these folks have done an incredible job of getting everything they wanted to for a minimal viable product.
As I mentioned previously I was looking for a much more minimal feature set, but it was obvious to me with interaction with the team, that I was going to get my must haves and could work from there on my own (if someone else doesn’t beat me to it since it is open hardware/source). I think we had enough of our answers to work on the project. Simplification is opportunity!
Looks great, can’t wait! Of course I’ve been involved since the start, we’ve had most of these conversations on the lists. Kudos Mathieu for patiently answering the same questions over and over!
It looks really great, but I’m not sure if I should choose yes or no.
On the one hand, I think it would be a neat trinket to have and something to hack around with if I get time. It looks amazing, really good work
I can’t see it being particularly useful for me personally because:
– I use multiple different computers, phones, tablets, so I would have to have a bunch of mmooltipasses connected at work, at home, etc, and bring my card with me (or bring the device and plug it around). Seems more hassle than simply remembering a password algorithm
– I’m pretty good at remembering passwords for sites, and my fingers are already on the keyboard. I already don’t like moving to the mouse and this would be another hand distraction
A possible feature request may be some kind of key combination to accept, but that’s probably more trouble than useful
I like this project. Don’t know if I would pay $80 for it as I am on a fixed income, I will have to think about it.
I don’t understand all of the technical talk in previous comments, so let me ask a couple of questions. First, is there a means of importing my existing passwords from a software password manager, ie: Roboform, Keepass, Lastpass, etc? Second, I have 5 or 6 gmail accounts, how would I select the correct account?
I commend every one of you helping with the development of this device, you seem to be trying to think of everything.
Thanks Robert! If I were in your position I would defiantly NOT buy this product. IMO 6 gmail accounts doesn’t have the potential “hack loss” as I have with 400+ user/password compilations with probably 80 accounts that spend my money and another 20 that could cause me major distress. I’m assuming you’re not dealing with the sort of information in those 6 accounts that could lead to loss of money (freedom or life). And if you are, I would be sending encrypted attachments which contained the real information.
Whilst I can’t (yet) see myself as wanting a Mooltipass over a software solution (or perhaps not a Version 1.0 of anything :), I do give Matthieu full credit for taking the time to go through pretty much all of the comments here and provide a considered response to each, as he did with my own queries on an earlier thread not long ago.
If anything, it does show a high level of commitment to this project, so well done Matthieu, team and HaD on that.
I agree, Matthieu, especially, is a hacker in the true sense and has inspired me to be a better hacker.
you’re flattering me aha. thanks!
It seems like it would make more sense in some ways to make a cheep dock that plugs into your computers and has the pin # and micro-controller on it so you could buy as many of them as you need for a couple bucks each. Then make the more expensive part that holds your passwords ect. Portable. That way you don’t need to carry around two parts or shell out 80 bucks for every computer. Just an idea if you move on to version 2. I love the concept and the case/user interface look great. the more I think about it the more I like it. Give it another couple weeks and the 80 doller price tag might not seem so big. :)
Keep up the good work and good luck.
James
I like that idea! Makes me think there could be a read only mooltipass. Something a bit closer to it’s namesake perhapse.
I use a password software password safe, the idea it is neat, but here my 2 cents:
Usb hid as driverless it is a cool idea, but keyloggers are a common issue. To mitigate perhaps add an encryption mode over this layer, that it is handled between the chrome plugin and mooltiplass. On initial connection chrome plugin generates a key that can be added to mooltipass, multiple keys can be set, only the right keys can be used to decode comms, this is how my current pass safe does it. It is a nice way to authenticate and trust the right apps pooling data. Unsure how much overhead something like this has and if it is going to impact the speed.
I like this idea, I’ld feel better about the browser plugin with something to secure that communication.
A lot fo people seem to be complaining about the price, and I’m not really sure why. Isn’t an Arduino around $35 alone? And what about peoples time and effort that was put into it, thats gotta be worth a lot. I’ve tried to make a few thing with fabbed PCBs and good components, its not free!
Although none of my passwords are very secure (I seem to forget them) this is something that could push me in a more secure direction. I think 80$ is resonable for what it is. Of course I would like to pay less, but I would also like to spend my days on the beach with endless bikini babes and craft beers for free.
I’m in, you want my 80$, I’ll send it your way and eat some rice and beans for a week to save up the money. I think its a very nice project, and even though I dont “need” the extras like smart cards and flashy lights (The Worst E-Reader idea was pretty great), Im into it.
If your target audience is “geeks” and “hackers” I think youll do great. Maybe not make millions but how cool is it to show your friends “Hey check out how I enter my passwords *Pulls smart card from wallet* BAM”.
/end excited rant
This!
> Of course I would like to pay less,
> but I would also like to spend my days on the beach with endless bikini babes
> and craft beers for free.
This!
Matt, I just wanted to say you and the rest of the team have done a great job developing this product, and aspects of your design have been an inspiration to me for other projects. Thank you for making everything so open and thorough. Also, your responses to the trolls is amazing; I don’t know how you have such patience with them.
This video does a great job of demonstrating the features, and the product looks really slick. I understand the motivation behind all of the design decisions, and the haters clearly didn’t put as much thought into their suggestions as you did the solution.
As a consumer electronics product, people expect it to have unreasonably low prices because they assume it’s made in China in the hundreds of thousands and they don’t think about transportation, warehousing, distributor, and retailer cuts. I can see how you could get to $80 pretty quickly. If you’re doing a custom enclosure, the mold cost alone is going to be ~$10k, which has to be amortized over the units sold.
I don’t have any specific feedback or advice; I just wanted to throw some positive energy and support your way because I got tired of reading hater comments in this thread.
Thanks Bob for the positive comment Bob! I’m sure some of the haters thought they we’re playing useful “Devils Advocates” by arguing that the founding features Mooltipass was built on were useless… They don’t understand that we are early enough in the adoption curve that we really don’t care if someone won’t buy it at any price because it is worthless. That’s the mainstream part of the adoption curve.
That’s very nice of you, thanks a lot! :)
“hackaday is not officially endorsing it”. I was under the impression they were and that it was an official hackaday company project. The guys accent is very hard to understand.
I don’t know, but I suspect the lawyers of the company that bought HaD are concerned about having a bunch of people not associated with the company creating a security device and the company in question being held responsible for some unreasonable concept of what this security device can deliver. Mooltipass’s goal as a project is to limit possible attack vectors, but as you can see from various comments, many people see these limitations as bugs not features. If Mooltipass is successful as I think it will be over the course of the years, the various original “must have” will be seen as not marketable and watered down, to the point of not being anymore secure than any of the other hardware/software alternatives already available. Should the owner’s of HaD be responsible for yet another third parties unsecured implementation? The only viable answer is no.
Eghm, you are correct.
Steve, I’m French.
This is the right thing Hackaday should do. Any responsible security practitioner should be sure that their customers are well aware of the risks, inherent or not. They are bound to protect their end user. By making this statement, people will be fully aware of the nature of this project, and prevent someone from blindly believing this is the product that fit their need because “this is cool”, “this is open source”, “this is hackable”, and “this is from Hackaday so this must be secure!” etc.
Since you still have software on the computer talking to the external hardware, you might as well just use the ‘1password ‘ software and not waste money on the hardware.
Thanks for your thoughts, but not necessarily. If it doesn’t exist I plan on hacking in a offline only mode that doesn’t use any of the software. I’m more than happy with entering my online banking credentials manually and I wouldn’t mind a feature that you could flag various user/pass combos as manual only.
Any idea about the total price in Euro?
Looks promising, but (being a sceptic) i’m going to wait for a few demo videos with the finished product.
With security, skepticism is the right attitude IMO. And that’s why I’m looking at a 100% open solution.
Skepticism is the right attitude for a lot of things, science in general included. However, after taken care of the appetide of one’s investigative mind, is open source a good thing to security? We might not have a easy concensus. Quoting Bruce Schneier, “.. if the algorithm or protocol or implementation needs to be kept secret, then it is really part of the key and should be treated as such.” and “Obscuring system details is a separate decision from making your system secure regardless of publication; it depends on the availability of a community that can evaluate those details and the relative communities of “good guys” and “bad guys” that can make use of those details to secure other systems.” Consider buying a safe, one from a reputable company and another “open-source” safe manufactured by enthusiast with every details and schematics available online, and even “hacker friendly”. Which one will you buy if you are to store your most treasurable items in it? Which one will you choose if you are to store your daughter’s most treasurable items?
Assuming both safes are manufactured in China, I would buy the safe model NOT bought by any American government branch, “reputable” company or not…
As opposed to the mooltipass, an open source mechanical safe can be modified by the owner, to a point? An electronic device with chips of all kind, that is way harder, while keeping the originally intended functions.
I am happy to see the word “harder” in your mention. To me, making electronics schematics open source, and in this case a SECURITY product, is just making side channel attack “easier”. Think about this, tipping attacker to identify vcc and gnd, type of IC chip, and all sorts of things? Thank again, would you feel any safer to travel in the air if aircraft makers like Boeing and Airbus publish all the cockpit schematics and wiring and electronic communication protocol online?
Ya, I’m skeptical about wide consensus on what is secure as highlighted by Bruce’s writing, “There’s really no such thing as security in the abstract. Security can only be defined in relation to something else. You’re secure from something or against something.” Even if there is consensus on what all those somethings are, there are still the trust/risk/cost/protection trade offs which is going to depend heavily on an individuals needs in a specific context.
For the safe example to apply to Mooltipass, I’m assuming I have the skills to build/hack the safes, so I would like to build/buy the hacker friendly safe and further modify it, in effect adding some obscuring of the system details. I’ld also probably use other layers of security than just a safe, obscuring more of the details of my entire security system.
If you’re not too far from France or Switzerland we should meet :)
I’m in Aachen, Germany finishing my Master Thesis, so i’m a bit busy atm :)
Security eh and you are having it manufactured in China eh? What could possibly go wrong there???
(Moolti)pass on this project.
It would have been really nice to see this thing be done locally(er) but maybe I am missing the point or something.
I hope you’re wearing your tinfoil hat eh! you never know who’s looking into your BRAIN.
I mean come on, its a little racist to state that everything made in China has some counterfeit part to spy on amurricans. I mean, unless you have some proof of this I have not seen…… in which case I better check my 555’s for built in microphones and RF transmitters.
If you use your 555’s to manufacture American, or European, military equipment, yeah, check them. But, assuming that you are a hardware hacker, any government official cutting you in a military contract is the one who should have his/her head checked ;)
Read the news, buddy. It pays to live through history sometimes.
Are you saying you would buy it for $80 if it was made locally?
Hey this look strikingly similar to the ZTIC token from IBM! Putting together smart card, usb token, and such into one piece is not something new, like 4 or 5 years ago UBS partnered with IBM for a smart card based token, aimed to protect online banking even under the face of malware. This neat dongle even establish SSL connection without the fear of compromised host, and have its own display for user’s visual confirmation. I’m amazed this idea is repeated.. The ZTIC is for one single purpose though, for obvious reason. Check out this video https://www.youtube.com/watch?v=RGjfWza0Pj8
Cool, which my financial institutions had something like this.
Sorry but i really have a big problem with your project. I spend sometime time a to read everything whats happened since the first appearing, to really understand you.
So I’ll try to constructive and first of all I want to understand your point.
My biggest issue is, i cant find any usecase. Why want or should anyone use this?
I know this was questioning alot, but havent found an anwser for me. And its not fair to say, in which it wouldnt for me.
The second thing I cant agree with, why is it so shiny? Your focus so much on how it look and not how it works. Its look like you spend 90% of time in energy in how it looks.
Its maybe the perfect product for geekthinklike online shop. For me, this has nothing to do with security or hacking.
Maybe i change my mind when you can give a realworld usecase.
The text scrolling is uselss, static images can be read much faster by a human eye in my opinion. Maybe also increase the text size. 80$ is a bit high :/ is it possible to build a “pcb only” version ?
Could a USB flash drive be used instead of the smart card ? This has a nicer form factor than a big smart card.
It’s difficult to find well-informed people about this subject, however, you sound like you know what you’re talking about!
Thanks