WiFi networking is one of those things that is reasonably simple to use, but has a lot of complex hidden features (dare we say, hacks) that make it work, or work better. For example, consider the Distributed Coordination Function (DCF) specified in the standard. Before a station can send, it has to listen for a certain time period. If the channel is clear, the station sends. If not, it has to delay a random amount of time before trying again. This is a form of Carrier Sense Multiple Access (CSMA) channel management.
Unfortunately, listening time is dead time when–at least potentially–there is no data transmitted on the network. DCF allows you to use various handshaking packets to do virtual carrier detection and ready/clear to send, but these are also less efficient use of bandwidth. There are other optional coordination functions available in the WiFi standard, but they all have their drawbacks.
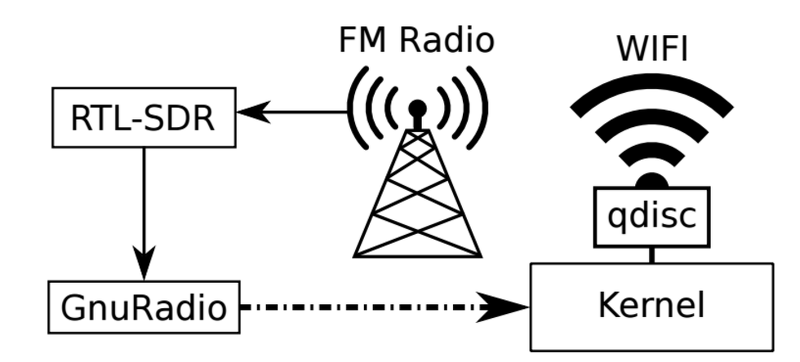
[Aleksandar Kuzmanovic] at Northwestern University and two of his students have recently published a paper with a new way to coordinate multiple unrelated wireless networks using ubiquitous FM broadcast radio signals called WiFM. Instead of trying to synchronize to the WiFi data channel, this new scheme selects a strong FM radio station that broadcasts Radio Data Service (RDS) data (the data that populates the song titles and other information on modern radios).
The computers don’t read the RDS data exactly. Instead, they find patterns in the data and use it to develop a common idea of time–even if they are totally isolated from each other on the network. The idea is that stations close enough to hear one another will get the same FM radio stations at about the same strength and virtually at the same time. Unlike, for example, GPS, FM radio signals easily penetrate buildings. As a bonus, many WiFi chipsets (like the ones used in phones) can receive FM radio, too.
Once all the stations are synchronized, they determine which time slots are in use and schedule the remaining according to an algorithm described in [Kuzmanovic’s] paper. When traffic volume is light or legacy equipment is present, the stations can fall back to ordinary DCF.
There are few things of interest to the hacker here. First, the paper isn’t just a theoretical idea, it is backed up by an actual test setup that showed promising results. It would be possible to use this same scheme in other wireless configurations as well. What’s more, the test setup itself is interesting. The researchers used the hacker-friendly RTL-SDR hardware and Linux machines running GNU Radio. We’ve covered many, many uses of the RTL-SDR, but this one is pretty unique.















How correct am I in saying that this is just a form of TDMA, using RDS as a clock or something?
That’s what I got out of it. The only fine point is that the TDMA isn’t rock solid but more cognitive. I guess which slots are going to be open and back off if I’m wrong. I think.
nice
My phone is dead now, I am pissed that phones have FM locked out.
One more word.
Conspiracy.
There will be a day when all broadcast media will yield their bandwidth to the internet.
phones have fm locked out?
Carriers like AT&T disable it because they hate their customers.
Why would they lock out FM? You know you need to plug headphones in, right? The wire acts as an antenna.
http://www.tmonews.com/2015/08/t-mobile-says-yes-to-the-fm-chip-will-push-oem-partners-to-do-the-same/
They’re frequently disabled by OEMs/carriers in the US, whose motto is “if we can’t charge you for it you can’t have it”.
but on the whole a pretty minor contribution to the reality that buying phones from carriers is a poor financial decision
That’s… unbelievably lame! That’s literally the most petty, stupid, lame thing I’ve heard for quite a long time, and I’ve got a Facebook account.
Still, you can get a small FM radio for a pound, so all’s not lost. Amazingly petty though. Americans! Well, business-wise. Them and the Chinese. I heard re-flashing the factory default software can help restore features.
As it is I use some lovely Bluetooth headphones, got remote control on the earpiece, and they only cost 12 quid. Which means no wire, so no FM radio. It’s all crap round here anyway, better off with MP3.
That’s some practical Cognitive Radio experiment indeed !
so back to slotted ALOHA?
“When traffic volume is light or legacy equipment is present, the stations can fall back to ordinary DCF.”
In other words, nearly always.
Yeah I thoght the same thing but that’s like saying N Wifi is no good because it slows down in the presense of B. Sure, but you eventually get rid of B. You just still want to interoperate with it. But yeah this is a long term thing (if anything) and not something that is going to make your network faster today.
Still, it’s backward-compatible and doesn’t sound hard to add. Maybe the IEEE need to give it a standard number, or maybe a few Wifi manufacturers will include it as a bonus feature to sell their stuff. The future’s coming quicker and quicker these days. Might not be long at all.
And all this just at the moment when everywhere in Europe governments are pushing DAB in order to stop broadcasting FM by 202x.
This will be a temporary solution only…