WPA2, the standard security for Wi-Fi networks these days, has been cracked due to a flaw in the protocol. Implications stemming from this crack range from decrypting Wi-Fi, hijacking connections, and injecting content. It’s fair to say, WPA2 is now Considered Harmful. The paper is available here (PDF).
This is a proof-of-concept exploit, and like all headline-making network security stories, it has a name. It’s called KRACK, for Key Reinstallation Attack. The key insight to this exploit is a vulnerability in the handshaking between routers and devices to establish a secure connection.
This is not the first time the researchers behind this exploit have found holes in WPA2. In a paper published by the KRACK researchers at the USENIX Symposium last August (PDF), they showed that the Random Number Generator used in 802.11 is flawed, ill-defined, and insecure. The researchers have also spoken at 33c3 on predicting WPA2 Group Keys.
The practical consequences of a poor definition and implementation of an RNG can be found in consumer hardware. The researchers found that in MediaTek-based routers, the only source of randomness is the current time. Meanwhile Broadcom-based routers do not use the RNG proposed by the 802.11 spec, but instead take the MD5 of the current time in microseconds. The researchers do not mention if the current time is a secret.
So what do we do now?
 This has happened before. In 2001, WEP, the Wi-Fi security protocol many security-ignorant people are still running, was cracked in much the same was as KRACK. This quickly led to the development of Aircrack, and in 2003, the Wi-Fi Alliance rolled out WPA and WPA2. Sure, you can still select a deprecated security protocol for your router, but the problem of WEP hacking is as solved as it’s ever going to be.
This has happened before. In 2001, WEP, the Wi-Fi security protocol many security-ignorant people are still running, was cracked in much the same was as KRACK. This quickly led to the development of Aircrack, and in 2003, the Wi-Fi Alliance rolled out WPA and WPA2. Sure, you can still select a deprecated security protocol for your router, but the problem of WEP hacking is as solved as it’s ever going to be.
The early 2000s were a different time when it came to wireless networks, though here in 2017 Wi-Fi permeates every cubic inch of our lives. Everything and everyone has Wi-Fi now. This is going to be a bit bigger than cracking WEP, but it remains possible to patch devices to ensure that this exploit is rendered useless. Install those security updates, people! Of course there will still be millions of unpatched devices in a year’s time, and for those routers, IoT baubles, and other wireless devices, turning on WPA2 will be akin to having no security at all.
That said, this isn’t a world-ending Armageddon in the way the botnet of webcams was. You will only be vulnerable if an attacker is within range of your router, and you will still be secure if you’re accessing secure websites. However, turning off Wi-Fi on your phone, relying on mobile data, not ignoring HTTPS cert warnings, and plugging into an Ethernet port might not be a bad idea.




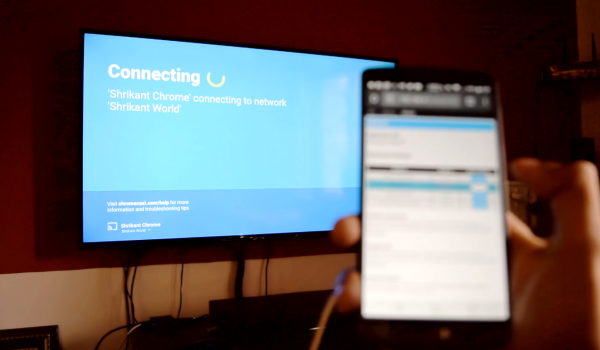
 The jammer is an ESP8266 development board — running some additional custom code — accessed and controlled by a cell phone. From the interface, [Nimbalkar] is able to target a WiFi network and boot all the devices off the network by de-authenticating them. Another method is to flood the airspace with bogus SSIDs to make connecting to a valid network a drawn-out affair.
The jammer is an ESP8266 development board — running some additional custom code — accessed and controlled by a cell phone. From the interface, [Nimbalkar] is able to target a WiFi network and boot all the devices off the network by de-authenticating them. Another method is to flood the airspace with bogus SSIDs to make connecting to a valid network a drawn-out affair.