So yesterday we gave you a round up of Transmission 1 which went out on April 1st. We quickly went from having to put something fun together for April 1st to running a full month-long ARG making things very very hectic at SupplyFrame HQ. Let’s take a look at what pearls of data were hidden in the week 2 offerings of the Alternate Reality Game. In case you’ve been stuck somewhere without Internet for a couple of days, the game was a lead up to announcing The Hackaday Prize.
Transmission 2 started with the following video appearing at the top of the Hackaday blog:
Major Tom in parallel then posted the following image on a page entitled Transmission 2.
 Since everyone assumed there was steganography used in the image from the previous transmission we decided we’d use that method to hide some data in this transmission. In order to do this though we needed you to find some keys and the appropriate steganography method to decode the data with. So we decided to hide some clues in the video.
Since everyone assumed there was steganography used in the image from the previous transmission we decided we’d use that method to hide some data in this transmission. In order to do this though we needed you to find some keys and the appropriate steganography method to decode the data with. So we decided to hide some clues in the video.
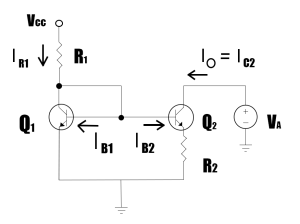
The video was largely made up by our friends over at IcoEx, but we wanted to encode some information in it. Inside the video (if you look carefully) are two almost subliminal images hidden in the noise, these are images made famous by [Bob Widlar]. As an additional clue we posted [Alek’s] epic article about [Bob] and his infamous career.
Additionally in the video you will hear our very own [Brian Benchoff] reading out a series of numbers in the style of the old school Number Stations. The series of numbers in the audio is 921763865 which is the decimal representation of an IP address 54.241.0.25. If you try to load this in a web server you get a simple response containing the following text:
DO AUTHENTICATION WILL ENCRYPT DO TERMINAL TYPE DO TSPEED DO XDISPLOC DO NEW-ENVIRON DO ENVIRON WILL SUPPRESS GO AHEAD DO ECHO DO LINEMODE DO NAWS WILL STATUS DO LFLOW DO TIMING-MARK
This looks a little odd without line-breaks (which is how it renders in a browser), but is actually the options statements that are issued by a telnet server when you first connect to it. This was enough of a clue that everyone then found the telnet server which gave them the prompt: ‘groundcontrol login:’. The username and password for this was a little obtuse, but was unearthed fairly quickly. It was ‘bob:widlar’ which is pretty obvious when you figure out the subliminal images.
Once into the telnet server you found yourself in a very restricted account with a home folder that contained 2 files and a folder. The folder was a complete red herring, we found the Apollo Guidance Computer source code earlier in the week when looking around for possible puzzle ideas and ended up dumping it into the home folder just for kicks. We had toyed with making you program the AGC using the fabulous MoonJS port, but it turned out to be pretty complex and we decided instead to go with something else. We were, however, very impressed at several people who downloaded the source, checked it for differences against the original, and even managed to get it to compile! Hackaday readers once again showing their persistence and ingenuity.
The other two files in the home folder were a file named ‘keyfile’ and a textfile called ‘reminder.txt’. The keyfile contained 3 sets of strings:
9186743BFDA92EE261752C138EBCD
FD332A7F1B1347BAFBA673B13EE3D
2D34FBA5FFBC69D2FBC1C1C25C484
The second file contained the text of the popular song Puff, the Magic Dragon written by [Leonard Lipton] and [Peter Yarrow]. This was a hint towards the popular steganographic encryption tool Open Puff. With the keys and Open Puff in hand it was possible to figure out that the 3 strings in the keyfile represented the 3 keys you can pass to Open Puff. Once you dialed in the correct settings you were rewarded with a text file containing the following message:
Current Status Inclination 52.3 Altitude 439km O2 76.2%
Once a few people had posted this up to the Transmission 2 page we had Ground Control close this round of the puzzle with the message:
Major Tom, this is Ground Control.
Message received.
Rescue mission planned, crew selection progressing.
Next communication at T-18180
This signalled the end of the second transmission, and pointed to the next one which would be at 18180 minutes from the T=0 time. This was a bit of a mistake on my part, as I still didn’t fully understand how to use the T- notation but had read people trying to solve it as minutes so I switched over to minutes this time. This caused a little confusion, but everyone still got there in the end.
I think this stage of the puzzle went really well, a lot of people contributed to the solution, and there were no major mistakes on our part which made everything go much smoother. At this point a community started to sprout around the puzzles and a new Hackaday IRC channel was born on freenode at ##hackaday. This later become the unofficial home and hangout for people working on the puzzles and has been an awful lot of fun. There were some outrageous coincidences as well, the ‘Puff, the Magic Dragon’ clue had unexpected relationships with other space things that we didn’t take into account. Some people thought we were referring to the Dragon spacecraft developed by SpaceX, others thought it might be a reference to the Dragon’s head nebula. These sorts of coincidences kept cropping up throughout the ARG, but I think they added to the fun.
Transmission 3 was where it all started to go a little bit wrong, but that’s a story for another day. See you tomorrow!
















I got AGC to compile. Spent an evening learning how the original was made and how it worked. And then had it ready incase it was going to be needed.
I got lucky in Google with openpuff and it was a shot in the dark when i posted it in IRC.
That inclination and altitude sure sent some people on interesting paths.
Nice Work.
I was watching Goatse when this video appeared. So strange…
Wow! This was so far above me (pun intended).
Should this really be filed under ‘stenography’?