When [Edward Snowden] smeared the internet with classified NSA documents, it brought to light the many spying capabilities our government has at its disposal. One the most interesting of these documents is known as the ANT catalog. This 50 page catalog, now available to the public, reads like a mail order form where agents can simply select the technology they want and order it. One of these technologies is called the Sparrow II, and a group of hackers at Hyperion Bristol has attempted to create their own version.
The Sparrow II is an aerial surveillance platform designed to map and catalog WiFi access points. Think wardriving from a UAV. Now, if you were an NSA agent, you could just order yourself one of these nifty devices from the ANT catalog for a measly 6 grand. However, if you’re like most of us, you can use the guidance from Hyperion Bristol to make your own.
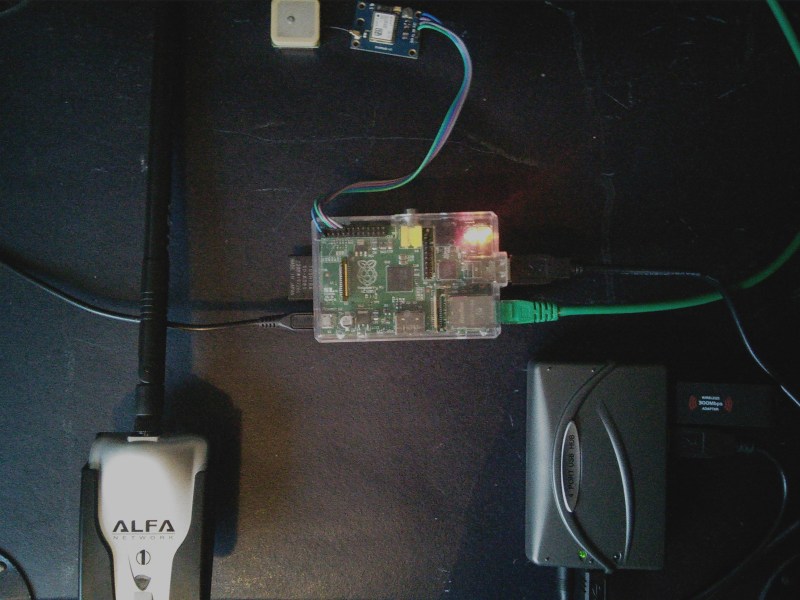
They start off with a Raspi, a run-of-the-mill USB WiFi adapter, a Ublox GY-NEO6MV2 GPS Module, and a 1200 mAh battery to power it all. Be sure to check out the link for full details.
Thanks to [Joe] for the tip!
















*cough* http://hackaday.com/2011/08/01/wasp-uav-gets-some-new-toys-now-intercepts-your-phone-calls-too/ *cough*
I don’t understand the angle of this one. What’s the point of tying the idea of an NSA capability to something based off speculation? Is this to show the NSA is wasting money? Does Hyperion Bristol think this is a novel idea? Wardriving is probably the oldest technique of all time. I think their article should have centered around reducing size and maximizing power of the capability instead of producing yet another method for wardriving that they can legitimately slap a raspi pie tag on.
IMHO there’s waaaaaay better things in that catalog to speculate over that require real effort and work.
To show that even if the “good guys” at the NSA can do it so can the “bad guys” (i.e. the ones who will sniff your unencrypted data for identy theft and stealing credit cards and whatnot). Mass surveillance is so cheap that anyone can do it, not only goverment agencies with billion dollar budgets.
But this is completely external to the NSA. This is something being done by anyone with a smartphone (and before that, anyone with a laptop and car). The only differences between the methods are the size of the product and the cost.
It’s not really a good example of ‘NSA technology going open hardware’ since only parts of the final product are (loosely) open source and only the description of the product relates this idea to the NSA. It wasn’t the NSA’s idea to geo-tag waps, and they certainly didn’t create revolutionary hardware necessarily worthy of imitation.
The 6k price tag probably exists for several reasons: high-quality, reliable parts produced by verified and secure American production facilities, small batch sizes assembled in secure facilities in the US, and tons of r&d to minimize size/maximize battery life/create end solutions for the data. You can’t really trust foreign parts or construction when your industry’s built on security.
@Anon – True. You could just download NETSTUMBLER and do the same thing. NSA R&D has things I tried to replicate as they are NOT willing to go civilian transfer yet on. Namely the word parsing program that discovers the salient “subject matter” from a huge textual sample (i.e. PTAH?). I used a huge database of English nouns and verbs from Princeton (.edu) but the darned thing was just too slow to be functional. It generally worked but it doesn’t work well on commercially available IT hardware. A DEC VAX or a CRAY would be better. NSA has those super-Jaguar’s (CRAY XC30?) at Bluffdale Utah.
Thanks you Figureitout ;)
I am reading this in the Black Sparrow. Free WiFi inside and on the street!
Comes now something blacker than black.
Overview of the NSA’s CTX4000/PHOTOANGLO Radar Units:
https://www.youtube.com/watch?v=rPQmIYb5E2o
NSA R&D didn’t invent this. This was invented in the 1950’s by the Soviet Union. It was called a “cavity resonator”. They use a microwave interrogator transmitter aimed at let’s say a bug in a US Seal embedded in a US Embassy in Moscow. The audio bug uses no batteries and can be hidden anywhere.
Overview of the NSA’s TAWDRYYARD Radar Retro-Reflector:
https://www.youtube.com/watch?v=KDQxDxiflyo
So I can use this to geo-track VGA video monitors? Why would anyone want to do that? A better device would be the classified TEMPEST system It can not only track a VGA monitor but capture what is being displayed on said monitor. It could possibly work on LCD monitors (smartphones, laptops, and tablets) too, NSA is claiming fame on this one but it was actually invented by Dutchman Wim Van Eck in 1985. With TEMPEST you do not have to break-in and plant anything. You just point and click and capture. Where are you pulling this stuff from? Snowden docs?
wait did someone say Bristol != nsa
because Bristol….
Next you install them into your fleet of google streetview cars, and if anybody finds out you say “Oops! Was that there? My bad. We forgot to remove that” “And BTW we have nothing to do with the NSA, at all..”
you know what else snowden did?
he also made it now so if we want to ship lithium batteries or even cells we need to be hazmat certified.
when the leak methods had nothing to do with batteries (i.e. he did not use any battery powered devices to store the stolen data).
in fact it was a lady gaga labeled cd used to burn the database to cd.
that was in place for years in almost every country
So it’s not actually his fault then, is it? Some opportunist government butthole / bungling idiot implemented the lithium thing for the wrong reason, and apparently blamed it on Edward. Just going by what you say.
He also proved that “democratic” governments spy on their citizens, all the time, without legal permission. And further proved that nobody really seems to give a shit. Thank the NSA in your prayers tonight! You know they’re always listening.
In the REAL world “they” use micro-SD cards. More data than any CD or DVD and much more easier to hide and/or destroy. Oh and it too requires no batteries. The Brits use rf-repeater PDA’s hidden in fake rocks and get discovered when the batteries fail and the field agent goes to fix it out in the open. http://www.rense.com/general69/rrus2.htm (Epic fail!)
Bradley Manning was the one that used the Lady Gaga CD.
The reason lithium batteries aren’t shipped by air is because of the UPS crash and the many other incidences involving the batteries, most of which didn’t make the news because everyone’s worried about the Kardashians.
https://en.m.wikipedia.org/wiki/UPS_Airlines_Flight_6
I have the VERY SAME hw functions on my PHONE…… just need an app
:)
Here it is :-)
https://play.google.com/store/apps/details?id=de.carknue.gmon2
That’s very impressive – I didn’t know you could run Metasploit on your phone…
Really wish you’d add a “comments” link at the bottom of each story when there isn’t a “Read More” link. Trust me, we’re here for the comments as much as the stories!
100% Agree.
I miss the [Read More…] button at the very bottom of posts. It just doesn’t flow when I have to have to scroll back up to hit the comments link.
I’m wondering what is the news here, if i know from some years ago that the aircrack-ng suite was running on android and i-phones..
So, what’s the point of using bigger, less portable, less running time, and with a total cost also bigger, can’t see logic instead of trying to kill a ant with a atomic bomb. :S
Wait. This is newsworthy why? Google has already been doing this with their Google Street View cars. For some reason they are collecting geo-mapped undocumented wf-fi hotspots. Why I don’t know. I can only speculate. I can think of only one “no such agency” that would need such data. Connect your own dots on that one…
The only thing I could use a micro-UAV for is not war-driving. WD requires too much loiter time in air to capture enough data to be useful and it would have to cover large areas taxing the on-board batteries. Now what AMAZON (regional distribution centers) is using UAV’s for is fascinating. They are about to release the first ones soon. I would love to see how these things are going to deploy let’s say in an urban environment where the indigenous population might steal them. But my favorite UAV application is the still classified Sikorsky Cypher (prime) – you know the UAV that looks like a UFO and actually never had a big honking camera mounted on a tripod. The camera(s) are embedded in housing and really does look like a UFO. Why a UFO? Plausible deniability maybe? “No it wasn’t us… it was dem’ aliens spying on you…” :)
How about REAL bugs with cameras? Now that’s fascinating… http://www.telegraph.co.uk/science/science-news/3335131/Insect-spies-fitted-with-video-camera-implants.html
DARPA (.mil) calls them “un-tethered cyborgs”. Moths and Beetles with camera, microphone, and xmtr “built-in” at birth. Batteries are wireless rechargeable.