On December 2, 2015, [Syed Rizwan Farook] and [Tashfeen Malik] opened fire at a San Bernardino County Department of Public Health training event, killing 14 and injuring 22. This was the third deadliest mass shooting in the United States in recent memory, and began a large investigation by local, state, and federal agencies. One piece of evidence recovered by the FBI was an iPhone 5C belonging to one of the shooters. In the days and months after the shooting, the FBI turned to Apple to extract data from this phone.
A few days ago in an open letter to customers, [Tim Cook], CEO of Apple, stated they will not comply with FBI’s request to build a backdoor for the iPhone. While the issue at hand is extracting data from an iPhone recovered from the San Bernardino shooting, [Cook] says building a new version of iOS to extract this data would allow the FBI to unlock any iPhone. Needless to say, there are obvious security implications of this request.
Apple does not publish open letters to its customers often. Having one of the largest companies on the planet come out in support of privacy and encryption is nearly unprecedented. There is well-founded speculation this open letter to the public will be exhibit A in a supreme court case. Needless to say, the Internet has gone a little crazy after this letter was published, and rightly so: just imagine how better off we would be if AT&T said no to the NSA in 2002 – [Snowden] might just be another IT geek working for a government contractor.
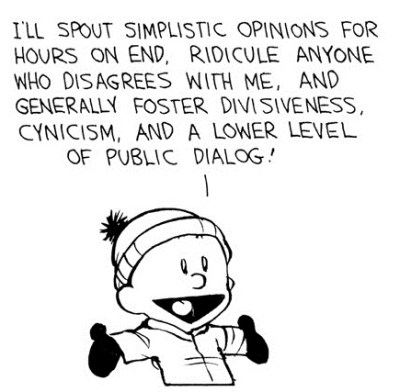 There is a peculiar aspect of public discourse that doesn’t make any sense. In the absence of being able to say anything interesting, some people have just decided to add a contrary viewpoint. Being right, having a valid argument, or even having evidence to support assertions doesn’t matter; being contrary is far more interesting. Look at any comment thread on the Internet, and you’ll find the longest comment chain is the one refuting the parent article. Look up the ratings for a cable news channel. You’ll find the highest rated show is the one with the most bickering. When is the last time you saw something from the New York Times, Washington Post, or LA Times on Facebook or your favorite news aggregator? Chances are, it wasn’t news. It was an op-ed, most likely one that was espousing a view contrary to either public opinion or public policy.
There is a peculiar aspect of public discourse that doesn’t make any sense. In the absence of being able to say anything interesting, some people have just decided to add a contrary viewpoint. Being right, having a valid argument, or even having evidence to support assertions doesn’t matter; being contrary is far more interesting. Look at any comment thread on the Internet, and you’ll find the longest comment chain is the one refuting the parent article. Look up the ratings for a cable news channel. You’ll find the highest rated show is the one with the most bickering. When is the last time you saw something from the New York Times, Washington Post, or LA Times on Facebook or your favorite news aggregator? Chances are, it wasn’t news. It was an op-ed, most likely one that was espousing a view contrary to either public opinion or public policy.
As with any headline event on the Internet, the contrarians have come out of the woodwork. These contrarians are technically correct and exceedingly myopic.
The Contrarian Opinion to Apple’s letter
The netsec industry is odd. Every day, my inbox is accosted by unsolicited emails from PR agencies, asking if I’d like to do an interview with a CEO or chief scientist on the security issue du jour. From the unending reminders to upgrade to Windows 10 to the security implications of a virus designed to destroy Iranian centrifuges, I have been offered an interview with someone who is uniquely qualified to speak on the subject. As expected, the first offers for an interview turned up in my inbox ten hours after news of Apple’s refusal to cooperate with the FBI crashed around the world.
The gist of the first pitch for this interview is as follows: Apple could have easily complied with this court order. This is not a crypto war. To quote this interview pitch directly and without attribution:
Apple didn’t need to react this way – it was premature and apples and oranges. Forensically speaking and legally speaking the Judge asked for reasonable assistance on unlocking THIS SPECIFIC phone. Even if that requires them to modify the firmware with a key they have they don’t have to give that software to the FBI. They can simple do a few steps:
- Give phone to Apple
- apple runs their secret sauce and makes a backup image of the data/phone info
- they give that image backup to FBI which only contains the data not the key. This is how forensics on mobile devices are done, by a backup image.
There is no threat to mass surveillance here. it was a reasonable search warrant request no different than a warrant to the free webmail services or face books asking for data. You’re not giving them your keys to ALL your data, you’re only giving them the very specific data of the account that was requested.
While this is an interesting counter to [Tim Cook]’s argument, it lacks the technical details required of a matter that requires a passing knowledge of topics ranging from electrical engineering to 18th century case law. Fortunately, the default mode of discourse these days is contrarianism, and there’s always someone else ready to glom onto the most important thing to happen in the Internet this week.
On the Trail of Bits Blog, [Dan Guido] plainly states Apple can comply with the FBI court order without compromising security for millions of iPhones, and gives a reasonable technical breakdown of how Apple can do it.
In plain English, the court order asks Apple to create a special version of iOS that works on only one iPhone – the phone recovered from the San Bernardino shooting. This custom version of iOS would never leave the Apple campus. After all, according to the court order, the FBI only wants the data on the phone and not a method to extract data from every iPhone they come across.
This is technically possible. New firmware can be uploaded to the recovered iPhone via DFU. This new firmware would require a valid signature from Apple, and the FBI does not have the keys Apple uses to sign firmware. [Dan Guido] ends his teardown with the conclusion it is technically feasible for Apple to comply with all of the FBI’s requests. This request would not necessarily make every iPhone insecure, and to limit the risk of abuse, the tools created to assist in this request can be customized to only work with the iPhone recovered from the San Bernardino shooting.
This is a Unique Moment in History
Apple’s refusal to comply with court orders is the largest news item to hit the Internet in a very long time. The CEO of Google has weighed in on the issue, concurring with [Tim Cook]. It is now inevitable that every god of silicon valley will weigh in on the issue, most likely in agreement with Apple’s stance.
Yet the contrarians remain. The entire argument of one of these contrarians – a chief scientist at a highly regarded security firm – revolves around “secret sauce”. It’s entirely possible for Apple to get around the encryption of the iPhone 5c recovered in San Bernardino, and doing so wouldn’t really be creating a backdoor for every iPhone. Are these assertions correct? Maybe. Possibly, even.
The metaphor of not seeing the forest for the trees is too often used, and anyone can be correct while still being incredibly dumb. Apple’s response to the FBI’s request is unprecedented. Apple is standing up to a court order – defying a court order – in the pursuit of privacy and security.
Historically, large companies haven’t cared about your privacy. The best example would be NSA equipment installed in an AT&T office in 2003, hoovering up Internet backbone traffic and sending that information off to points unknown. This wasn’t the first time AT&T provided data to the NSA; that occurred in 1985, with phone and email data being collected at points around the United States and sent off to NSA repositories.
Ma’ Bell isn’t alone, and for every conspiracy theory on government surveillance spoken in hushed tones over the years, there is always news telling us, ‘yes, the government is spying on you, and here are the companies that helped.’ Instead of the usual way of doing things, Apple is saying what anyone who knows anything about security has been saying forever. If a backdoor exists, you are not secure. Apple will not provide that backdoor, and Google concurs with Apple’s view.
What we have here is one of the largest companies on the planet, a company that is sitting on over two hundred billion dollars – cash – and wants to take this issue public. If anyone has the resources to stand up to a surveillance state, it is Apple.
And yet the contrarians continue to prove there is a difference between intelligence and wisdom. Just because Apple could comply with a court order, doesn’t mean they should. Just because you have a unique viewpoint doesn’t mean you should post it on your Medium blog. This is an opportunity for a company with a deep pocketbook to go up against a surveillance state that has acted against your interests time and time again. This opportunity will not come again.

















It could be possible that no one person at apple could make such a back door tool, and that this was by design. It is possible that having to come together to make such a tool would fundamentally compromise a piece of SOCIAL security at place within Apple itself.
I think apple are handling this perfectly. They will always comply with a court order but they have to make a show of fighting.
Welcome to spin…
Apple should comply if court ordered however the next update should male it impossible for anyone no matter what private keys you hold to unlock or flash a backdoord iOS non destructively to a locked phone.
It may be technically possible still but so long as apple can claim they are unable and charge a prohibitive amount to try no one will bother
Next court order they get they can quietly iignore.
I trust no one. Not Microsoft, or Linus Torvalds and not the FBI.
They don’t need to create any “backdoor”.
The reporting on the issue is slightly misleading, because the FBI is not technically asking them to break the encryption – they are simply asking for a way to get data off the phone without exhausting the 10-attempts-self-destruct mechanism that prevents them from trying to brute-force the password.
They are not even requiring Apple to break the encryption keys.
Technically, all that Apple needs to do is help the FBI dump the raw contents of the flash memory of the phone so they can poke and prod at it, and try to find whatever information it contains.
No, because without the hardware key, the memory dump won’t do the FBI any good – they’d be stuck trying to brute-force a 256 bit AES key instead of a 4 decimal digit PIN number.
And all of this doesn’t matter, because If apple complies now then it opens the door to them doing it in the future, eventually streamlining the task. And once the task is streamlined, the probability of this capability getting out into the wild (or at least getting copied by those asking for the data) goes up dramatically. Apple is making a stand that, no, they aren’t going to get pushed down that road.
And I agree with them 100% on that point. But getting the facts of the situation right does matter, and a whole lot of people here are arguing against strawmen.
Given the resources available (no doubt if they ask, NSA will gladly lend a hand) and the “need” (more like “want” :P) for this data, that should not be too much of an issue…
That doesn’t matter, because that’s what the FBI is asking for anyways. They want to try and brute-force the encryption, and all that Apple has to provide them with is the encrypted data out of the phone.
No, because with the phone’s cooperation, they only have to bruteforce a short pin number or passcode. With the phone image (but no hardware key), they have to bruteforce a 256 bit AES key, which is entirely impractical.
That is a backdoor the security of the phone rests on the fact after 10 progressively slower attempts it erases itself.
If you make it so you could make 10000 attempts without self destruct, which without the hardening delay would probably take seconds to minutes will unlock that phone and make it decrypt itself.
It sets a precedent which no one wants I do not have anything the hide but would not buy a phone the FBI could have decrypted in a heartbeat with a court order and apples compliance.
What if next week China recovers a phone and demands apple comply or iran? Apple is in a sticky situation and would not be able to ignore their request if it didn’t want to risk loss of the market
So the FBI shouldn’t be able to execute search warrants? This isn’t spying — this is regular police work. They followed the rules and folks STILL want to pretend this is about privacy?
This isn’t a search. If they had no ulterior motives and wanted to get the job done, they’d subpoena the companies that host whatever communication channels they used and get the data from them. But no, they want to be able to tell vendors to put in a backdoor at their request, as they’ve been lusting over for decades now. They want precedent that allows them to skip all that annoying police work, and go straight into devices without the owner’s cooperation.
The problem is that law enforcement has long history of abusing it’s Constitutional (USA) right to issue and execute reasonable search warrants When I say law enforcement I’m including the criminal court system as well.. The Miranda ruling resulted in more convictions upheld be cause it force la enforcement not to gather evidence in Constitutionally questionable ways. Activists working to change the status quo in a peaceful manner have been the subjects of surveillance. Other than coveting the Apple II E back n it’s day I have never been; and I use an iPhone because family and friends I communicate with most use them I’m not an Apple fanboy, but IMO this request should be challenged, and I can support Apple for doing so.
What you are describing– a firmware that doesn’t wipe data after 10 failed attempts– certainly is a backdoor. If you create a signed firmware that allows people to easily brute force the password, how can you be sure they won’t read that firmware off the phone and use it on every iphone they want to get data off of? What if the firmware is set free into the wild?
Hopefully Apple will take this episode to heart and make their next generation of devices impossible to DFU update without unlocking or wiping first.
Look, not everything that weakens security is a “backdoor”. We have a larger vocabulary than that, and trying to make “backdoor” serve all purposes just makes it meaningless.
Making it easier to bruteforce a password is not a “backdoor” because it’s not bypassing the regular authentication mechanism.
“how can you be sure they won’t read that firmware off the phone and use it on every iphone they want to get data off of”
Because Apple would lock the firmware to a single phone’s hardware ID, and sign it with their key. If an attacker can get around that, they can already write their own compromised firmware.
To be clear, I’m with Apple: this is a bad idea and they shouldn’t do it. But like the article says, it’s not technically infeasible.
<=10000 operations, no hardening delay and no self destruct
To break encryption which usually requires 2^256 operations.
Doesn't weaken security it breaks it.
It is a backdoor. It converts a high grade security to you need a teensy and 5 minutes googling to crack a iPhone in minutes.
Did you read my other comments? It isn’t high grade security, it is a high grade illusion that vanishes in the face of enough time and money. In the end a generic solution will be deployed by governments so all this does is delay the FBI investigation and make some people think Apple care about their privacy, rather than just profits.
Better for Apple to open it up, than have governments implement systems to do it. The argument from them is we could do it but don’t want to do it because then other countries will make us do the same. Well they can do that right now, because they realise that it is possible now. if Apple does not cooperate they just have to say open up this or that phone, or you can’t do business in our country. Apples claim was mute the moment they made it.
Apple can’t win in the long run unless the law in every country they do business in protects their right to refuse, which clearly is not the case and never will be, even if it turns out in the USA they have some constitutional protection or whatever.
No, for the umpteenth time, it’s not a backdoor. A backdoor bypasses the usual authentication mechanism. This does not. Not everything has to be a backdoor – what are you, a hollywood scriptwriter?
Not a back-door. Just shutting off the alarm system so the guys can crack the safe without the bank owners knowing about it. An alarm system that will, if need be, incinerate the contents of the safe if the combination is wrong too many times. Since the value of the information is likely that it is not in the hands of the safe breakers, eliminating it is good enough.
Since it does move the problem set from impossible to merely difficult, it’s pretty close to a back door. Maybe one day there will be a name that basically says ‘make it easier to bypass security measures.’
There is a name for that, it’s a “vulnerability”.
The pin is 6 numeric digits on newer phones and 4 on older ones, anyone in security would tell you when it is a-priori that a password is a fixed count numeric password, that is about of insecure of a password system as you can make.
If someone got hold of your bank card with it’s woefully insecure 4 digit pin, a thief could crack it at an ATM in a few hours. What prevents that from occurring are additional safety measures such as surveillance cameras at the ATM and confiscation of the card after a certain number of unsuccessful tries (typically 10 as well).
iPhone’s auto erase performs this function, turning a trivial brute-force problem into an insurmountable problem. So by asking this extra security measure to be disabled, they are de-facto asking for the keys to the kingdom that anyone with a few hours (or few days for a 6 digit password) of their time would be able to use.
They’re not asking for a master key, they’re simply asking Apple to modify this one phone to accept unlimited password tries.
And what prevents a corrupted government agency from taking the one time solution and applying it at will?
The fact that the image is locked to a single phone and digitally signed so it can’t be modified.
The question you should be asking is “What stops a government agency asking for this on flimsier and flimsier pretexts once Apple gives in once?”, which is the reason Apple is objecting.
yeah, they actually are asking Apple tp break the encryption keys by permitting the FBI to do brute force cracking.
This isn’t a unique case; there have been a lot of violations of the 4th and 5th amendments since the Patriot Act, enough so that it changed the landscape. The fact that we’re even discussing Apple being forced to comply as if it’s a reasonable thing is proof of how this country has changed.
Court cases depend highly on “legal precedent”. If the gov is successful here, any further attempts to invade the privacy of others will be that much easier. And for flimsier reasons.
Except that dead people don’t have such rights. The phone owner is dead.
But wouldn’t the phone then fall under probate or a successor in interest given a will? So the phone would still potentially fall under ownership of a living person i.e. his mother, whom would still qualify for protection under declared Constitutional rights.
The owner of the phone is the city, not the user who was issued the phone
The very fact that the person who owned the phone id dead only makes the FBI request that much more questionable. how many people who had a relationship with the dead owner and have no connection with the crime will find themselves under FBI surveillance? The history of the FBI on that subject is very poor.
Their death did not add or subtract from the number of “friends” therefore your claim is irrelevant.
Dead or not, it sets a dangerous precedent.
hi olagos
I will just say this. Even if companies comply with every request that NSA throws at them, this will not prevent “lone wolf” style mass shootings. It is easy to buy weapons in the US of A. So: all people lose privacy, and gain very little security.
Making weapons hard to get sure saved a lot of people in France, as did their surveillance state. Its funny that people, especially people who are not American, seem to continually phrase this as an ‘American’ problem, when in reality, it is far more widespread than that. All over the world, people in power are abusing that power to further their own agendas, while all the common people who make the wheels turn get dumped on.
If the weapons were hard to get in France, those loonies would not get them.
Open borders, smugglers, criminal rings and closed ethnic communities helped make the shootings in France possible. It is very difficult for the average citizen to buy a gun in the EU in general. I got the impression the shooters were not your run of the mill ciizen.
And no, I don’t think more guns in the hands of the French citizenry would have prevented the attacks.
Your right on that count: It would not have PREVENTED the attacks. But you can be sure that even if some of the individuals at the venues involved would have been armed, and knew how to use their weapons, a lot of people could have been saved! I think I can speak for most who carry on a regular basis when I say: Any one of us would be happy to put ourselves in harms way if it means that lives are spared and one more nut-job is off the street.
The very things you mention in your statement; Open borders, smugglers, criminal rings and closed ethnic communities are the reasons why gun control will never stop this kind of thing from happening, as much as people want to say that it would. See below! dominoembedded is right! Guns and their availability are not the problems: It boils down to an inner city culture of crime and mental health problems!
As for the topic at hand, I for one welcome a healthy debate about privacy! Those who think apple should just comply are either uninformed, or baiting for trolls! If anything, this issue will help bring awareness to hose who have never thought about the implications of ‘Government Overwatch’ in all aspects of their lives.
But it might of helped- like the Luby’s shooting… what?, 15 years ago?
Suzanna Hupp, who was present at the shooting where both of her parents were killed. She later testified that she would have liked to have her gun during the shooting, but said, “it was a hundred feet away in my car.” (She had feared that if she was caught carrying her gun she might lose her chiropractor’s license.) -wikipedia
Not saying it would have changed things, but we know how Paris and Luby’s turned out when everyone was unarmed… just like when my great-aunt answered the banging on her front door in the middle of the night… if she had a gun they might not have had a chance to shoot her in the back of the head as she laid on her living room floor.
Would the ultimate outcome have been different? Maybe not, but it sure as shit couldn’t have gone any worse. I’ve been asked ‘what if guns were illegal and the robbers didnt have one?’ … so she could lay there and be clubbed like a baby seal?
Easy access to guns in public in France might have maybe caused A) some fewer people dying during the recent attacks B) a total chaos where nobody knows who’s shooting who (the place was dark!) with even more fatalities. However, what it would have certainly caused is MANY more attempted attacks. European security has spoiled many attacks in recent months and years, often because it wasn’t easy to get guns or explosives!
Europe isn’t the US with an ocean between them and the bad guys. Any islamic terrorist can easily travel to France without much hassle. Just look at Israel and what they had to do to get some sort of safety! Fences, walls, drones, shooting kids etc. If the US were in Europe, it would be burning right now.
More guns – that’s what we need; one for every man, woman and child. Gun crime solved.
Extremists will always find a way to get arms wathever the country.
If it hadn’t been AKs it would have been suicide vests. Or a truck outside full of diesel and fertilizer and someone with a remote waiting for the people inside to come streaming out after the show.
I can use a hammer to drive a nail or crush a skull. The tool is far less important than the intent.
Apple is doing the right thing. What happens if something similar happens in China? Is Apple now expected to extend the same courtesy to that government? This is what is referred to as a slippery slope- if Apple does this for the FBI then at what level are they no longer expected to hack their own security? Local PD that is fishing for evidence and thinks there *might* be something they can use?
The government wants back doors into everything- your OS, your router firmware… before long we get to a Minority Report system where it becomes about ‘predicting’ criminal acts.
FACT: if the government had open access my ass would be in jail not for any act or intent, but just for mere curiosity. Sites like HaD could become red-flags in a browsing history because if you don’t respect ‘warranty void’ stickers then you must have a problem with authority and if you don’t respect authority then you’re probably willing ignore other rules and under it all laws are just rules so you’re willing to break the law too so now you’re a person-of-interest and hello mind-crime.
(Hows that for contrarianism, Benchoff? Seriously though- ended the article on a strong note.)
You could reduce the hyperbole – such as labelling blatant speculation as “FACT” in all-caps.
@arachnidster- no… pretty sure it would be fact in that world. I’m sure that in the authoritarian dream world they would have systems in place that would have flagged me for being a curious kid who wanted to know what exactly was in that so-called ‘Anarchists’ Cookbook’ that I heard so much about. In this day-and-age I get paranoid when I talk about the band ISIS with all that Snowden confirmed for us…
See, “I’m pretty sure” is how you prefix speculation. Not fact. “The US president is Barack Obama” is a fact. “If Trump gets elected he will set all Mexican-americans on fire” is speculation.
“I’m pretty sure” was used as… sarcasm?… I don’t feel that is the perfect word I’m looking for, but its what is at the root.
Here… how bout this- I know for a FACT that in the authoritarian dreamworld we our web activity would be tracked and analyzed. I know this is a fact because of the NSA, Snowden only confirmed what we all knew all along. Our web-activity is tracked and analyzed, its the reason that we see targeted web advertisements for things we look at on amazon.. its the reason I get store.hackaday adds when I’m reading random blog posts.
Only reason we dont go to jail for our web searches is that the courts still recognize the difference between thought and action.
Now go away troll.
That pesky problem of criminals ignoring laws…. They should make a law that makes ignoring the law illegal!
Sorry… an old tired argument that couldn’t hold water the first time is used. Murders happen although murder is illegal. Illegal booze exist although booze is legal. Where legal prostitution exists , illegal prostitution exist, and so on. Although no one attempt at a solution is perfect, some work better than others, to address negative issues. Not much of a stretch that that making weapons harder to get works better than making them more readily available.
The united states does not have a gun problem, it has a mental health and inner city crime problem. Gun control only ever hurt the law abiding citizen.
Yaaay! Gun debates!
Why doesn’t the US have orders-of-magnitude more diagnosed people with mental health problems and an orders-of-magnitude higher inner city crime rate than other countries, then?
Higher costs of heath care and less people seeking help could certainly be a factor in the lack of diagnoses.
How convenient that factor exactly reduces the rates to what you’d expect from a country that’s generally consistent with other similar countries!
Because guns or not, mental health is under diagnosed in all countries, even the UK, where we have free healthcare.
And presumably because everyone’s scared that if they get a diagnosis, they’ll have their guns(=security) taken away.
“Why doesnât the US have orders-of-magnitude more diagnosed people with mental health problems”
You’re saying we don’t? Don’t think our mental health problems are resolved because we shut down the vast majority of mental hospitals a few decades ago…
“and an orders-of-magnitude higher inner city crime rate than other countries, then?”
We do:
http://www.mapsofworld.com/world-top-ten/countries-with-highest-reported-crime-rates.html
Ken >
I don’t think you understand what an “order of magnitude” is, and that site doesn’t understand what a “rate” is.
“Inner city crime”?
Pretty sure the overwhelming majority of mass shootings in recent history have been committed by white middle-class men/boys.
‘Inner city’ is a racist dog whistle. Be an adult, own up to your racism, and simply admit that you don’t like the idea of poor people of color having access to weapons. At least it’ll keep the discussion honest.
List the murders in Chicago for the last year.
“Pretty sure the overwhelming majority of mass shootings in recent history have been committed by white middle-class men/boys.”
Oh that’s cute – you want to ignore the hundreds and hundreds of ‘onesie-twosie’ shooting that occur day-in and day-out across the country each year and focus on ‘mass shootings’.
You are trying to deflect from the previous commenter’s point, but a fair number of ‘mass shootings’ were perpetrated by non-white, non-middle class people:
Ft. Hood Virginia Tech San Bernadino
>
Good Point x3n0x. People are generally good, so we should help them enable themselves to do what’s right. Because criminals always find a way to take advantage of their freedom. I think privacy is an important part of freedom, and I would give up a bunch of security to maintain it.
I want to agree with you. The problem is trusting your government. If people could trust their government to protect them and not take advantage of them, security situations like this wouldn’t occur. The shooting would have never happened because the communications would have been intercepted. The crime could have been prevented. On the other hand, what happens when the government decides they want everyone to obey certain rules because it’s for everyone’s safety. No more fun. Well, to a certain degree we all like to have a little bit of fun, even if it’s wrong. Nobody is shooting up places, I’m referring to speeding a little, drinking a little, target practice on your own property, etc. These are activities that the government allows but one day might wish to revoke for our safety. Imagine if we gave up our privacy now to protect everyone from terrorists, which I truly wish we could have. Later this blanket of security snowballs because the government can see not just the terrorism, but all the other crimes. These crimes might be petty: running a stoplight, forgetting to pay a tax, etc. If they could easily find you, if your technology that enables you also gave you up, everyone will begin to lose. It’s what makes us human, to defy the law to a degree. I don’t want someone watching my back in the interest of my safety. When money gets tight, suddenly they want cash. They know what you’ve done and they want some money to make it all go away. This is a scary world. There are other resources to fight terrorism, and to a degree we will never be able to stop it. It takes radical changes in thinking, not surveillance. When I first heard about what apple did I was disgusted, mostly because the headlines sparked controversy. Now I have come to the realization that while apple may be a technology bully, they did something very respectable and they earned my trust.
Good points. Well they (Apple) haven’t earned my trust, they’re just a tech company. I would not “trust” an internet device with a mic, unless I built it. But the American government has become unlimited and oppressive. I think historically, the “DIY-HACKADAY-mantra”, and the realization that we only have to answer to nature and man, has given us more in two hundred years, than most have now. It would be a shame to force a society to be only as fast as it’s slowest runners. (I.E. nobody has guns, because idiots shouldn’t, nobody has cells in the car, because some cannot use them responsibly.) There is no reason to trust your government, even if you “like” what it is doing. Otherwise the government, has little reason to continue working on your behalf, like we see now. Our system shows that it’s not even up to the government to force a company to hack their own product, prevent people from defending themselves, etc. This is because government does not provide these innate rights, but is forced to recognize them. This is the issue to me.
Considering that the Bataclan was the deadliest attack in France since WORLD WAR F*CKING TWO, yeah, I’d say that making weapons hard to get sure HAS saved a lot of lives in France.
“Considering that the Bataclan was the deadliest attack in France since WORLD WAR F*CKING TWO, yeah, Iâd say that making weapons hard to get sure HAS saved a lot of lives in France.”
Some are only considering attacks as bad as the one in France, any lesser tragedy, like say a sandy hook or Virginia a tech wouldn’t register because they involved fewer victims?
Are you arguing that in France they had: WW2, peace and tranquility with no shootings until 2015, some 70 years later, when someone finally figured out how to get a couple guns in France?
>
That’s more or less true. We just don’t have many shootings in Europe. Organised terrorists, once in a blue moon. But we don’t have to worry about unhinged citizens or pissed-off teenagers shooting us. In the UK we get a loony-massacre maybe once every 10 years, how many’s the USA had in the last 10?
” We just donât have many shootings in Europe.”
Yet… Give it time, you’ve just started experiencing the fun that (effectively) open borders bring a nation.
“Organised terrorists, once in a blue moon.”
I seem to recall a fun-loving bunch of Irishmen and women that had a nasty habit of blowing things up for a few decades
I recall flying to London pre-9/11 and walking up to the (sub machine gun-toting) policeman at the airport asking him where there was a trash can in the terminal – he told me there weren’t any, people kept putting bombs in them.
Ken >
Er, you do realise that Europe has been around, with effectively open borders, for a lot longer than the US, right?
Well, now that all those angry young men from the Middle East are streaming into your nations in astronomically larger numbers than ever before, with their interesting views on women and a belief that Martyrdom is a noble cause things are a bit different than they were, say, in the second half of the last century… The first half of the last century was pretty chaotic as I recall, what with two world wars and at least one massive Genocide in Europe (with another in Russia)…
>
We’ve had large Muslim populations in Britain and Europe for decades. We’re fine. I grew up in a place where around 90% of the houses had Muslim families in them. Thousands of people. I’m a white atheist. I was one of the few white kids at my school. 95% or so Muslim.
And you know what? We got along fine. We made friends. I can walk through my old neighbourhood today, 20-odd years later, and people come up and ask me how I’m doing, pleased to see me, and I’m pleased to see them too. They’ve got kids of their own now.
Because Muslims are just people like any other. In my life, coming from a town with a large Islamic population, most of the trouble people have ever given me, has come from white people. I’d happily live in a Muslim neighbourhood again. You tend not to get many drunken pains in the arse, for one thing. It’s a nice, safe, place to be a kid.
The issue isn’t the religion, it’s the culture they grew up in, and the 95% ‘Muslims’ you went to school with were likely born and raised in your area, have adopted English culture and are, I’m quite certain, wonderful neighbors.
That said, those folks you hold out as ‘Muslims’ were raised differently than, say, the ‘Muslims’ that have recently arrived in places like Germany or Norway, where the gov’t (for some reason) feels compelled to tell them that, you know, rape is bad.
All ‘Muslims’ are not the same (nor are all Jews, Christians, Hindus, etc).
>
>the 95% ‘Muslims’ you went to school with were likely born and raised in your area, have adopted English culture
What, in 1980s Britain? No. Most of my contemporaries were born in England, yep. Their parents were mostly born in Pakistan. 5-times-a-day prayin’, Urdu / Punjabi speakin’, Halal eatin’ Muslims wearing salwaar kameezes and saris everywhere they went. Going to the local mosque however many times a day, we had several, often just converted houses.
Of course, one tries to fit in wherever one lives, but they still had a strong Pakistani culture. Many of the parents’ generation didn’t speak much English, they all spoke Punjabi at home, the kids were bilingual.
And still, we got along well, better than many white neighbours I’ve had. Almost no suicide bombs! There was one kid at school who exploded once, but we suspect that’s cos his maths homework was overdue.
As people, their lives were mostly about raising their kids, seeing them marry, working, spending time with friends and the community, and religion. Just like everyone else. Except the religion, most British aren’t religious in any meaningful way. A small majority identifies as Christian but you’ll only see them in a church for births, deaths, and marriages.
Later generations have adopted some “British culture”, if that phrase can be said to mean anything. We have a diverse culture here. Lots of “foreign” influences, as well as the many regional and other differences. There’s thousands of accents in the UK btw, if Dick Van Dyke is listening. Our town has a Mela every autumn. A festival for everyone. Music on stage in the park, a parade of kids with candle-lit home-made lanterns (round the lake, so not much problem with fire). Stalls, great food, trinkets to buy. Was great! More culture than most British towns of any size.
Still the Pakistani Muslim culture is strong. Many of them identify that way. But pretty much everyone just gets on. Friends and neighbours they’ve known all their lives. We go to each others’ weddings. It’s also nice to have shops open on Xmas! Though you’ve bugger-all chance of getting a taxi on Eid.
We’ve lived happily together for 30 or 40 years. A city with a Muslim population of around a quarter, has less racists than I’ve met since moving to the South of England, where they’re all over the bloody place. I miss decent, cheap, Pakistani food, and friendly strangers. Don’t miss the weather so much.
Muslims just aren’t scary. They don’t identify with terrorists any more than American (just a wild guess, but that’s you, right Ken?) Christians identify with the Westboro Baptist church. They’re actually being very reasonable, considering the way the lives of Muslim people around the world are seen as disposable in the interests of big business and Israel. Despite the ridiculous fear that ignorant and prejudiced people around the world, largely Americans,are revelling in and spreading as best they can. Still, our Muslims are ordinary, decent people.
Hi,
From France here.
I never saw a real gun in my life. And i feel much safer that way. I won’t trade the kills in terrorist attacks that happens once in a while, and won’t be prevented by people having guns , for people beeing armed and shooting everywhere when they loose their mind. As of now someone going crazy gets to punch people, or even stab a few. Not to mass kill with automatic weapons.
The point is that in the US you are more likely to get killed by an american citizen with a gun than by a terrorist.
Of all rich countries, USA has the largest proportion of kills by firearms. I don’t know mass shootings in France by a crazy person, whereas i can remember multiple shootings like that in the US.
Guns are not the only factor, since canada has a lot, and much less kills. However, with no guns, the power of an individual to cause large kills count is seriously hindered. Sure, one can craft a bomb or such things. But most people don’t know how,and are not smart enough to figure it out. And if they do, they’ll probably have calmed down by the time they finish their weapon.
Having a gun is of little help if you are shot at by military automatic weapon, unless you are an highly trained soldier,used to be under fire, able to quickly take cover, identify the shooter, aim accurately at him and take him down without killing someone else.
Had i been there with a gun that i would probably have forgotten it, and hid as well as i could. Had i remembered of the gun that i probably wouldn’t have been able to be brave enough to get out of cover to shot at the attacker. Even if i were, i wouldn’t be likely to hit him but rather another random person. If i was accurate enough, i may have harmed one guy, but never the full squad. And i would probably get killed anyway, by retaliation fire, or even by the police when they get there (what do they do when they find an armed person at a terrorist attack?)
All of this to say that guns won’t help here. We don’t want them, keep them in the US if you want, but not here. Most modern countries ban guns for citizens and have a lot less gun kills compared to the US (and a lot less murders in general).
Being scared of and spending so much effort on trying to prevent terrorism is totally irrational, so many things people do every day is much more likely to get you killed.
since 9/11 ~600,000 have been killed in traffic accidents and ~400,000 have been killed in gun violence
That was part of my point up there.
Having guns would have caused a net gain in deaths over terrorism.
PS :
Ken says:
February 19, 2016 at 7:33 am
Well, now that all those angry young men from the Middle East are streaming into your nations in astronomically larger numbers than ever before, with their interesting views on women and a belief that Martyrdom is a noble cause things are a bit different than they were, say, in the second half of the last century… The first half of the last century was pretty chaotic as I recall, what with two world wars and at least one massive Genocide in Europe (with another in Russia)…
-> this is nonsense. You obviously know squat about europe. There always have been “angry young men form middle east” in europe. There have been terrorist attack in the past (1995 for instance).
You recall something about irishmen. Ok, there were a few bombings once in a while, against buildings mostly. Anyway, having guns would have solved nothing there. And as another commenter said, we have NO random shooting. Because simply it’s hard to come by a gun, (again i never saw a real gun in my life, and i’m 32), so when someone goes mad he will punch people, throw a rock on a windshield and that’s it.
In US, they go mad, grab an automatic weapon, and kill dozens of people. You have those events all the time. And you have more guns than people. How did having loads of gun helped prevent this?
All in all, i bet that the number of people killed in guns accidents is superior to the number of people shot in those killings.
So not having guns would yeld a net decrease in deaths.
Nope, automatic weapons in the US are about as easy to acquire as a Sherman tank and likely the same amount of paper work and background checks. Anything newer than 1986 with automatic or burst fire are banned, prior to 1986 require an FFL to own, which is like 6-month wait for background check then $10,000+ for the purchase itself.
Hardly the situation that everyone has an automatic weapon in arm’s reach that you try and fail to paint.
I find it interesting motor vehicle fatalities are often brought up in relationship to other cause of deaths, ignoring that the rate of motor vehicle fatalities have been reduced. Reduced because there’s an active effort to prevent those fatalities. Using a motor vehicle fatal ties to dismiss efforts to reduce the rate of fatalities by other cause doesn’t make sense. Not to me anyway.
it is not about dismissing efforts, it is about making the effort (and fear) proportional. If the object it is save as many lives as possible you should spend the money on improving things that is dangerous and kills lot of people
That’s it. This fact is always lost in the handwriting over communications security by both sides in the aftermath of tragedies like these. The only thing that effective interdiction via intercepts would accomplish in the long run would be to make the perpetrators of these outrages more careful.
I see very little discussion of the fact that this seems to be an order for Apple to DO something simply because it can. This is different than a search warrant for existing property or information, or an order to comply with terms of a contract, or an order to cease doing something contrary to a law or regulation. I’ll posit one admittedly extreme example–if you were a crack sniper, could the court order you to kill someone they concluded presented a direct and imminent threat to national security simply because you had the capacity to do so? If not, how is this different?
Opposition should put moral pressure on Apple.
I think, they could conscript you (passing laws to allow conscription if needed), they they could order you to kill. You could still refuse, at which point you could be court-martialed.
I don’t think companies can be conscripted. They can however be taken to court on any old crap the government can dream up, their assets can be frozen, and their CEOs can be arrested on trumped up charges – as often happens to companies run by “dissidents”, ethic, or religious minorities, in many countries.
Conscription would require an act/law of the president/congress. You can not have a judge arbitrarily declare an independent entity, be it company or person, to be a slave. I think they had a little ‘discussion’ about slavery in the past and decided to get rid of it in the US.
In that light I’m wondering if trump’s support of declaring a private company to basically being owned by the US government will lose him votes, because I always though the republicans really didn’t like that concept.Hell I though all americans did, even the ones supporting the american communist party.
We still have the Selective Service “volunteering” in face of large fines, denial of education and possibly jail-time for males 18+, so I would argue that the US still has slavery it is just “volunteer” slavery.
Citizens United seems to hold that corporations are people, so surely they could be conscripted just as legally as a meat person could. The main problem seems (from the other side of the Pond) to be a government that seems to be doing all the stuff that we did under George the kraut, plus a bunch of stuff from his 1930s compatriots, which appear to have gained a lot of traction in the US. I’m thinking of things like the businessmen’s puch, the popularity of eugenic sterilisation, etc.
Apple seem to me to be resisting a court order to cooperated with an admittedly criminal organisation, to break their security “just a little bit” – which is like being “just a little bit” pregnant, except that if your encryption is “just a little bit” fucked, you can’t get a termination.
That’s a very interesting and valid point. apple is wealthy but what if they weren’t? another slippery slope, could courts bankrupt a small software company that invents a new encryption method they can’t even break for example…
Same thoughts here. How the hell can they force you to make something? How can they prove that you CAN do it?
As for me the solution would be open source software, and have it audited, designed such as that even the maker couldn’t break it, and this fact beeing proven by independant sources.
However for rich mega-corporations such as apple, they probably can say no, and go to the court.
I’m fairly ignorant on that point. As far as I know Apple hasn’t been convicted of any criminal activity, so what gives any court the ability to order Apple to do anything? Perhaps there’s a provision in the so called USAPATRIOT act, I don’t know. From what I have read of that GWB and pother republicans pretty much gutted much of the bill of rights.
Apparently there is an “any writ” provision, or something of the sort, that basically says that a court can order anyone to do anything that is not against the law. In theory, a court could order you to fly by flapping you arms, and then jail you for failing to get airbourne. Admittedly, it would be difficult to lock a corporate “person” up in the same way as a real one, but there are equivalents, or they could go after the people making up Apple – kind of like shooting hostages until someone manages to take off.
And this is why Apple need to take a stand now, if they create the tools the FBI asks for then next time a simple warrant to hand over said tool will be enough
So the take away is that Apple is offering at your local Best Buy or AT&T store a phone the NSA can’t crack… That sounds great, but how long will it last?
If the iPhone offers impenetrable security, won’t it soon be considered as all other highly-advanced cryptology and have severe controls placed on it’s import/export in the US?
This public letter from Apple is about 90% marketing hype, 10% last act of defiance – I expect the gov’t will find a way to open up this phone, they just thought they could get Apple to roll over, like it did some 70 times before.
The export of cryptographic technology from the US is, today, largely unrestricted.
[citation needed]
This might help:
http://www.cypherspace.org/rsa/legal.html
>
“Crypto software can exported with minimal restrictions now.” – exactly! I’m confused why you were trying to argue that if the iPhone was secure, it would be export-restricted, given that.
I made the original statement, It was challenged, someone called for a citation, so I researched it. That what I found contradicts my earlier statement means I shouldn’t have shared it?
I haven’t looked into it in decades, but I still believe my point stands – the US gov’t would try to limit import/export of highly-effective, purportedly ‘I breakable’ cryptography.
>
Okay, I didn’t realise you were retracting your original statement. Bravo!
The US government did try to restrict the import and export of effective crypto, but it didn’t work – so they’ve given up. Secure cryptosystems (nobody in crypto says ‘unbreakable’ because that’s just asking for trouble) are widely available worldwide.
FBI can’t crack it doesn’t mean the NSA can’t. I don’t think the NSA would publicly say what they can or cannot crack.
Exactly; I’m fairly confident that the highest intelligence services of US, UK, Russia, France, Germany, Isreal, et al, already know the answers to a lot of cases like this, but can’t be seen to know it. I read, recently, how the SIS actually love it when ‘people of interest’ use encryption, as the opaque packets stand out like a beacon.
100% agree. Apple can’t have the public appearance of selling a device which can be cracked by-design. Privacy-conscious people would flock to competitors. And by writing this “open letter” (advertisement), Apple is making more people “privacy-conscious”.
There’s very few “privacy-conscious” people. Giving it a special limited-edition spangly silver case would sell more than decent crypto would.
I believe in this case it’s the password challenge they’re having a problem with, a 4-digit number. If you get it wrong enough times, the phone wipes, apparently securely enough to give The Man a problem. Unless it’s a sophisticated double-bluff (and we’ve found out through recent years that the paranoids weren’t paranoid enough) to get people to trust a flawed technology. Certainly could happen.
I suppose all of this might give Iphone owners something to brag about, and that’s 90% of the reason people buy them, so there is that. Even if they don’t understand encryption or data security.
If it was me, I’d use actual, proper encryption. Dunno if you can get PGP for the Iphone. Of course that depends too on there being no key-logging type stuff, you have to trust the platform. But even then there’s ways around that, randomising the arrangement of the keys for inputting the password, or setting the password on a separate machine. Sure Apple COULD have used flash chips with twice the claimed storage, re-marked the packages, and secretly stash copies of everything. Of course they’d want paying. There’s plenty of black-budget money, but there surely must be more efficient ways of spending it.
Then there’s people analysing the code that Iphones run. Again, they could’ve stashed some a secret CPU and stuff onboard the flash chip. But they probably haven’t.
[Just as a nothing to do with anything point, why do people capitalise Flash, as in Flash memory? I keep doing it but I don’t know why.]
I think if I cared about phone privacy, I’d get an Android, and run some proper encryption stuff on it. Linux stuff should port easily. As it is, the great big hole at the other end, the phone company, would be most people’s main problem. If I had any terrorist plans I suppose a phone is a place to keep them, so it’s near you. Would be the first place they’d look though if they captured me. And if I was a terrorist. Or wasn’t one, but just looked a bit funny, or the police / government fancied fucking with me. Which happens to people now and then.
Nowadays governments are second citizens after transnationals Corp. like Apple. It is transnationals corp. who rules the world not governments. So if Apple and Google says no, it will be no. If needed they will buy all politicians needed to buy.
That is just BS.
No matter what they say, the US government definitely has ways of making them jump when they whistle, it was, is and will be this way as long as the headquarters and biggest market are US-based.
When the Google battle fleet makes port, let me know.
I’d love to see their aircraft carriers.
Why bother? Oil companies have the government to do that for them, and taxpayers to pay for it. You don’t need to actually PAY for your own troops, fuck that. Well, except on-site in Africa, but there it’s paramilitary machine-gun toting “security guards”.
Google’s battle, if they have one at all, is on different ground. They can advance their interests in much quieter ways.
I used to be really pleased such a huge company had “Don’t be evil” as their motto. Til they dropped it. Coincidentally right about the time they went public selling shares.
Feel the Bern, baby! Or even better, Jeremy Corbyn! At last, at fucking last, some actual socialists in power!
Well, I hope so at least. Be a massive landslide change. I’ve often said the reason so many people don’t vote is not apathy, it’s disgust. One lot of arseholes, or another lot substantially similar, only 10% less out to fuck the common man over. It’s no choice, and people decide not to endorse either of them. Meanwhile politicians chase after an ever-smaller group of right-wing voters.
There’s now an actual left-wing to vote for again! If Corbyn gets in in the UK, I’m prepared to change my view of the public as shit-throwing brainless monkeys. I might even start hoping for society again.
Either way, the USA really ought to do something about all this lobbying, and all the money people spend to get into power. It’s a huge root of corruption. In the UK it’s different. Here, the Tories are rich men helping out their old school chums and business associates. Much more on a personal level, I think. More subtle.
“Either way, the USA really ought to do something about all this lobbying, and all the money people spend to get into power. It’s a huge root of corruption. In the UK it’s different. Here, the Tories are rich men helping out their old school chums and business associates. Much more on a personal level, I think. More subtle.”
Same in the US – once Obama became President, he directed the DNC (his party) to stop accepting donations from lobbyists… Now that the DNC is broke – literally broke, owe more than they have – the DNC quietly changed it’s position and told lobbyists they are ‘open for business’. Just to recap, Dems took lobbyist money in 2008 election to seat Obama, then banned it, then in 2016, as Obama prepares to leave office, they quietly start taking lobbyist money again.
But we also have the politicians helping old friends in full effect also – the firm that failed to compete the half-billion dollar Federal Healthcare Exchange website (a no-bid, no penalty for failing contract I might add) went to a fellow classmate of Michelle Obama’s from her Princeton days.
>
Can’t they just beat the code out of the phone’s owner? Or did the US police shoot first and ask for passcodes later?
Right, blame the police for killing active shooters who’d already taken several lives – I guess you think the police should have sat outside the civic center and waited till the couple either ran out of amp or targets, then ask them why they did it…
>
Nah Ken, he thinks the police should’ve joined in shooting the public, then rounded them up into camps, and instated a communist state with Sharia law. Then shipped murderous Muslims in by the boatload, to burn down all the churches.
That’s what happens when the government won’t stay out of your Medicare.
The government is the party that acted hastily here, not Apple. All this pressure will do is encourage Apple to engineer a more secure next generation OS. So next time, when the government wants help on something valuable, unlike this intelligence dead end, Apple will be able to say with complete honesty they’re unable to comply.
Just to start off, I am not saying that Apple should comply with the court order. I read your article and multiple examples were given where people have laid out how they think Apple could comply while still maintaining overall security and encryption. They were labelled as contrarrian, so I was hoping that I would find some details as to why they are incorrect. I didn’t see that, and with the missing counterargument I find myself asking why those people are wrong.
The whole point of this article is that they’re not wrong about Apple’s ability to comply – they’re wrong in assuming that they _should_ because they _can_.
The main argument is that the technique cannot be uninvented. Once is is in existence, even if it does not somehow leak into the wild, the precedent has been made – which is probably what the FBI is after. Having said “yes” to hacking into a phone for the government once, they then lose or seriously weaken the ability to say “no” in the future, until we get to the point that the local sheriff can have a rummage through your phone whilst he’s confiscating your car and college fund to pay for that new riot tank that the Blackwater salesman was showing him.
Good luck to Apple. The US government handed them free cool PR and they’ve taken it.
FISA court order – yes every single time (no bad PR risk)
Warrant that will be recorded in a public court record – No (high risk of very bad PR)
There is a big difference between criminal activity and terrorist threat. When it comes to mass killings in the name of some Deity, then I suggest that anything should go in the world of national protection. No true of criminal activity.
What makes terrorism different from criminal activity (other than “I say so”)? Why should a crime be treated differently if someone does it for profit than if they do it to pursue a radical agenda?
Might have something to do with a fair bit of people ceasing to be alive.
We have a crime for that, it’s called “Murder” or “Manslaughter”, and it’s a civil crime, not a military act.
Time to go get chipped then Walter.
Get an RFID tracking chip embedded in your arm, and go get your fingerprints and DNA catalogued. While you are at it, install a GPS tracker in your car, and install the newest big brother app on your Apple/Android device.
I know you openly say anything can go for national protection, but think about someone listening in and snickering next time you’re getting hot and heavy in bed with your wife because your smoke alarm has a microphone in it.
You should also think about the ’employees’ that are responsible for monitoring and administering this stuff… People seem to forget that a business or entity is merely a collection of people. Some of those people are there for a pay-cheque only so do you trust ALL the employees of the government?
being there for the pay-cheque only is not the problem. The problem is when they want to make more money on the side.
No, the problem is our government devolving into a fascist state due to surveillance becoming a trivial task. Seriously, if we don’t respect our right to liberty we won’t be able to enjoy it.
Terrorism is nothing but a tactic. And a tactic this country was founded on…
…Revolutionary War- the British commanders complained because we wouldn’t line up shoulder-to-shoulder on the field-of-battle instead preferring to set roadside ambushes and to fight from inside the treeline.
One mans terrorist is another mans freedom-fighter.
Guerrilla Warfare is not necessarily terrorism.
Kinda splitting hairs now… Do you think the British troops weren’t terrified by these heathens who didn’t respect the so-called ‘rules of engagement’?
Both terrorism and guerilla tactics share similarities in that they are both ‘unconventional warfare’ also in the fact that they are both intended to help overcome an enemy that outnumbers, is better equipped or otherwise out-powers you.
IEDs are bad because they are improvised while landmines are okay because they are mass-manufactured yet they are both intended to accomplish the same goal.
“IEDs are bad because they are improvised while landmines are okay because they are mass-manufactured yet they are both intended to accomplish the same goal.”
I don’t know of anyone that considers landmine ‘okay’, the real difference between the two is that land mines are typically deployed in a publicized manner to control passage thru an area, while IEDs are typically deployed randomly to keep a their enemies at constant levels of alert.
>
True, but the Boston Tea Parties were most terrorism. Economic terrorism in a sense but still terrorism.
Well, in theory, the country that the Revolutionaries created is better than the one that ISIS (or whoever) is now trying to setup.
That is irrelevant to the matter at hand.
Besides- look at what has become of the country the revolutionaries created… spend billions rebuilding a region on the other side of the globe that we’ve been blowing up for 15 years while we neglect places inside our own borders… we can rebuild Fallujah but turn a blind eye to St. Louis and Detroit and pump tainted water straight into homes in Flint.
We have become what our Founding Fathers paid to free us from with the blood from their veins.
Oh… I forgot the part where I point out that ISIS is merely filling the vacuum that we created.
That is because our “leaders” have neglected some of the core guidance given by our Founding Father like “Engage in foreign commerce, do not engage in foreign entanglements”. We the People are not much better having failed in “remaining ever vigilant”. Government like fire is a useful servant but a fearsome master.
Anything?
“Kill them all: God will know his own”?
Water boarding? Red hot pincers?
Torture the suspects’ children to make them talk?
In James Blish’s “Cities in Flight” series, he has the west falling (or more precisely, being considered to have fallen) not because they are defeated by Soviet Russia, but because they have become indistinguishable from them. (Animal Farm also springs to mind)
At what point is it unacceptable to become what you behold, and be satisfied?
“This is an opportunity for a company with a deep pocketbook to go up against a surveillance state that has acted against your interests time and time again.”
This is laughable. First, if Apple *truly cared* about privacy, then iPhone encryption would be *as impossible for them to break as for the FBI*. They would not have a “master key,” so complying with this request would be a “sorry, we can’t do it either, we care about privacy so our phones don’t work that way.”
Additionally, this does not refute “it’s just this specific phone,” or the legality of the request, or anything other than an appeal to paranoia and distrust. This is a specific case, this is a warrant approved with all the checks and balances, and they don’t have to hand over the “keys to the kingdom.” If you’d care to actually refute any of *this*, you might have an argument.
Personally, I think it’s just Apple being scared that their sales are going to take a nosedive when customers realize they can look at any “private” data on any phone with little to no effort. Shouldn’t we be *even more* concerned about *that*? Apple doesn’t even need a court order.
Before declaring something “laughable”, you should educate yourself on what’s actually happening.
Apple does not have a “master key”. The FBI is asking them to provide modified firmware which eliminates password retry delays, doesn’t wipe the phone after 10 tries, and allows password attempts to be submitted over USB instead of via the screen. All of these permit the FBI to mount a practical brute force attack on the user’s pin.
This changes nothing. At best, there’s a 4-digit pin standing between you and the world. Apple can still do this as trivially as the FBI; probably better since they can just make an image that brute-forces it right on the phone. At worst, they can just bypass it directly. Nothing on your phone is secure either way. Apple doesn’t even need a court order. Maybe you don’t trust the government, but then why do you trust Apple?
Nor does this address the legitimacy of the court request in this case. This isn’t a secret warrant from a secret court. It’s not *for* a traffic ticket, or something trivial. The slippery slope is *a fallacy*, not a valid argument.
The better argument, if anything, is that if Apple has to comply here, they would also have to comply with *other* governments’ requests to do similar. But, that’s the price of doing business in a country: *following the law*. (Obviously, if they’re “not complying” in a legal way, filing in court etc, ultimately to abide, great.)
If they *truly* cared about privacy and human rights issues, they would build a phone that’s *actually* secure and perhaps not do business where the laws aren’t desirable.
“This changes nothing”
Of course it changes things! You implied Apple had a master key and that was the only way they could technically help; now you’re shifting the goalposts to make a different argument.
“At best, there’s a 4-digit pin standing between you and the world.”
iPhones permit much longer passwords. It’s up to you to use a 4 digit numeric one, and if you do, that’s the vulnerability, not the phone, or Apple’s software engineering. Apple does its best to make a short pin code as secure as possible, given the constraints, and they’re refusing to weaken it further for the government.
“Nor does this address the legitimacy of the court request in this case. This isn’t a secret warrant from a secret court. It’s not *for* a traffic ticket, or something trivial. The slippery slope is *a fallacy*, not a valid argument.”
Nobody’s arguing anything of the sort. They’re pointing out that asserting that a warrant can compel a company to create something entirely new and affirmatively weaken their product is unprecedented, and that the FBI’s interpretation of an ancient statute as allowing that is incredibly broad.
“If they *truly* cared about privacy and human rights issues, they would build a phone that’s *actually* secure and perhaps not do business where the laws aren’t desirable.”
And just how would you propose to do that?
“Of course it changes things! You implied Apple had a master key and that was the only way they could technically help; now you’re shifting the goalposts to make a different argument.”
Um, no. How they technically accomplish this, the result is the same: Apple *can* break the iPhone security. Whether this is by having a master key (as is not the case, it seems) or simply by using a firmware which trivially cracks the pin, the result is the same. The argument is *identical*.
“Nobody’s arguing anything of the sort.”
But that’s *exactly* where this article ends, and what is laughable. “Going up against the surveillance state” is nothing of the kind.
“They’re pointing out that asserting that a warrant can compel a company to create something entirely new and affirmatively weaken their product is unprecedented”
Except, this has already been refuted, and I have not seen arguments to the contrary. The article itself concedes that is not the case:
“In plain English, the court order asks Apple to create a special version of iOS that works on only one iPhone – the phone recovered from the San Bernardino shooting. This custom version of iOS would never leave the Apple campus. After all, according to the court order, the FBI only wants the data on the phone and not a method to extract data from every iPhone they come across.”
So this comes down to not that Apple *cannot* comply, only that they *should* not. But I have seen no convincing argument why this is the case. Clearly, not only can they comply, but they can do so without compromising *any* other phone to the FBI. What argument is left? That there’s an old law in the country? (Guess how old the Constitution is…) That “evil gubmint” and “big bad FBI,” as per this article? That Apple is somehow a privacy crusader and this is a *privacy* issue, despite their record for the opposite?
The paragraph you quote as refuting my point instead corroborates it: the government is asking Apple to create a new capability in response to a warrant. This is what’s not before been demanded, and it’s overreach – one small step from requiring them to insert backdoors into their software.
Apple don’t have a “master key”, they would have to completely deconstruct the operating system and make a version of iOS that has a master key for this phone. So it’s not as simple as plugging in the iPhone and typing some stuff, they’d have to make an entirely new version of iOS, which is doable but not with “little to no effort”, and this method of bypassing encryption doesn’t exist at the moment. This scenario you describe is what the FBI wants, and Apple doesn’t want
That’s not what the FBI are asking for at all.
Yes, it is. Here’s an idea: why don’t you go learn something rather than sit here and spout ignorance, making yourself look like an idiot? Wouldn’t that be a better use of your time?
No, it’s not – they’re asking Apple to remove some key protections that make brute forcing the PIN impractical. Not write an “entirely new version of iOS” or “make a version of iOS that has a master key for this phone”.
Your ad-homenim does nothing to strengthen your argument.
The understanding I have right now is:
On this version of the iPhone, some of the PBKDF2 ratelimiting is in the OS itself, which Apple can change without invoking a hard penalty (wipe/alter/reset of UID). At a minimum – you can only enter passwords manually, you can’t run a program to brute-force passwords on-device. Such a program, on this older device, might succeed within hours if the user has a weak passcode.
The FBI wants to run a brute-forcer on-device.
Newer iPhones have a 5 seconds per attempt ratelimit in the Secure Enclave. It is unknown whether Apple can update the SE firmware without invoking a hard penalty. If they can, on newer devices it might be possible to allow a bruteforce ratelimit to be dropped from 5 seconds per attempt down to 80ms.
The iPhone 5C uses an older ARM processor that doesn’t support TrustZones which is where Apple implemented their “Secure Enclave”. This means that the software that does the rate limiting for the 5c isn’t any different than the normal iOS code which is signed by apple to verify updates for integrity.
We know even with iPhones that use the SE the firmware/OS can be updated without losing the keys since apple has modified the delay times in the secure element with previous software updates. The newer iPhones aren’t immune to this issue either. Apple needs to require the phone to be unlocked before proceeding with DFU, or wipe the keys in the SE on update if forced in DFU.
Terrorism is a big deal. If Apple says “ok, just this one time”, then next comes an abducted child, a murder, fraud.
Next thing you know, courts order Apple to dd a single phone to help prosecute txting while driving.
If they can for this phone, they can for any.
I have my suspicions that the data is already recovered, and this display is to make someone think it isn’t. And if Apple were to comply, it would be under the condition that it’s done secretly. It’s to the FBI’s advantage for it to appear like these phones are a good place to store incriminating data. The more people that know a secret makes the secret likely to be found out, and I think that goes for electronic devices as well.
I would think that one task before going on jihadi rampage would be to wipe phones & computers. Like they are witnesses…
“Itâs to the FBIâs advantage for it to appear like these phones are a good place to store incriminating data.”
Yes, it is.
>
Forgive my ignorance, but your example seems silly. Why would any court need to ask any phone manufacturer for help with ‘txting while driving’ when that information can very simply come from the network company?
One Word: iMessage. It’s not a text message, but data on TCP/IP. It doesn’t show up as a text on your bill.
I think you forget that those tcp/ip messages are routed and logged by the same network operators. Since the necessary information is timing, even encryption and systems like tor won’t offer much protection.
The impression I got is not that Apple can’t or won’t help or that they even think the FBI is wrong for wanting this. The issue is a two parter;
1. You have an agency they is invoking an old writ that may allow it to over exercise their power and by complying you are creating precedence for all future cases where they may try to invoke the All Writs Act for things that are much more mundane. After all, you complied once, why not again?
2. iOS codebase is probably fragmented between teams with the intention of not allowing any one person access to the whole thing. Also, their concern is that by just allowing this version of iOS to merely *exist* poses a security threat. In terms of technology, that version of iOS would be comparable to smallpox or some other weapon of mass destruction. If it leaked, that would be apocalyptic potentially for Apple.
True, they are asking for this support on a specific phone for a specific case, but the negative implications that could arise would far outweigh the positive. *Removing my anti-big-gov hat* I as much as anyone want to see justice for the victims and their families, but the risk involved is not worth it and I agree with Apple (I dont even like Apple).
At this very moment, Apple is being pressured by the FBI to unlock a meth cooks phone also.
I consider that mundane, indeed.
Good comment.
I personally think this is Apple enacting the terms of their cooperation – we cooperate privately, but publicly we get to pretend otherwise.
The media has been claimign encryption was a problem with san B thing since hours after the event started – before htey had the phone or the whole official story.
“What role did encryption play in their lack of identification?” the press asked. “Surely with the dragnet surveillance the security agencies knew about these people” the press asked.. Before the event was even over – before the people were caught.. Remember the people were caught supposedly because they returned to the scene.
I am totally cynical at this point, and certainly dont believe anything a telecon company, the government, or apple CEO say. Nothing they say is trust worthy. They all reserve the right to lie to us peons. National security is well understood to mean corporate profits among other things.
The question about mass surveillance was a good one, and the answer of “encryption” is rubbish. These people either didnt use digital communications, or the whole narrative is lies.. Meta data was more than enough if these people were communicating with nefarious entities. Meta data IS THE DATA. From google to AT&T, the government has open warrantless access to this information.
This is more security theater, but of a different type.
I sense something much bigger at play than simply getting data of a suspects device.
From teleco’s to cloud data services, there is probably a lot of (meta)data available to piece together a lot of answers to questions.
The perps are dead, and won’t be going to trial. A high burden of proof is not required. The more speculative nature of any data available would seem sufficient for policy, training, etc. (cynical me says:”when was the last time politicians let facts get in the way of policy”).
So why go after the phone so aggressively? It’s got to be the legal precedent that is being sought after, and the feds are using a very tragic event to build democratic support for gaining new powers/authority to monitor/manage the people.
Feds are trying to call san b. “workplace violence”.
The feds lie. They only lie. It is their charter.
I agree completely with you. There is more than enough metadata to piece together their digital contacts. The systems for doing so are already in place, IE xKeyScore or whatever it’s still-secret replacement is.
The government wants to track all domestic political activity. It is that simple. Further, they want to make their jobs ever easier when they enforce things like drug laws to seize property. The cops and the DEA already use illegally gotten digital surveillance data to bust the pettiest of criminals, if they have property to seize. Meanwhile, big banks merrily launder as much drug cash as they want, with only tepid fines and zero personal risk for the bank operators.
Doesn’t the NSA already collect massive amounts of data from multiple sources? You mean to tell me they have not collected this data already? So much for the mass surveillance so the world is safe – this just shows how not picking your targets and just doing a mass collection does nothing to heighten security at all, and just tramples over citizens privacy and freedoms.
This also shows how inept 3 letter agencies are, since they need help of the parent company to do any sort of reverse engineering. Somehow I doubt that they do not have an exploit to break into this phone, but in doing so would show their cards so to speak, and they still want to guard that secret from the world until a more serious issue arises where their exploit would be used.
Perhaps the back door here is not technology but PR. Apple publicly denies they helped but in a back room is actually complying with the order. Apple gets the rep for being a secure device, more people buy iPhones, the government is ok with it because they know Apple will comply when asked behind closed doors outside of public scrutiny.
This is mostly true. The government actually wants pervasive automated access though – which will be their end goal in all types of data.
They want to know who said what about who.. Not stop any terror. They thrive on terror. Without terror, large swaths of self-important, role-crazed authoritarians loose their mandate, their reason to exist!
Once you create a role/group that very role/group must continually justify its existence, and that is a very dangerous thing especially where big salaries and long careers are involved.
Not to mention willfully and purposefully ignorant leadership, bent only on domination, power, and control. IE, all authoritarians.
Authority is a type of ignorance.
Whether the iPhone has a backdoor or not, by publicily stating Apple will refuse to help FBI could look bad for Apple in the mind of paranoids. It could be viewed that Apple had a hand in the mass murder and they don’t want incriminating evidence released that could damage Apple.
I don’t know how the files are stored on iPhone but couldn’t FBI carefully desolder and remove the flash chip to dump the content? Install a socket in the iPhone and run all 10,000 possible combination to find the right code to decrypt the file. If the file is erased, take the chip out and reprogram it with original that was dumped earlier. Or if the FBI has access to the same encrypting software that can be run on desktop computer, run the dumped file through that.
They can’t do that because the flash is encrypted with a 256 bit AES key that’s stored in the iPhone’s main memory. The key never leaves the firmware, so short of decapping the chip, they can’t access it. And guessing 10k passwords is a lot easier than guessing 2^256 possible AES keys.
I was curious how the encryption works. Is the key just preset in the firmware? Where does the users pin get stored? Is that part of the encryption, or is it just a hash check before it releases the preset key? If that’s the case wouldn’t flashing it with a new OS change the key and cause the data to be lost anyways? This whole thing doesn’t make any sense and I can find a good technical article.
From what I understand the actual encryption key is stored in a tamper-proofed (self-destructs if physically breached) chip which evaluates the PIN, and passes the actual key along if the PIN is valid…or can be set to delete the encryption key if there are too many bad PINs entered, which is how this phone was configured.
You can’t have looked far – this very comments section links to Apple’s official doc, and many tech news sites like The Register have discussed it in detail.
The user’s PIN is combined with a hardware key embedded in the device to create a device key, which is used to unlock the phone and decrypt the data. A device image won’t include the hardware key, and so would require brute force checking every possible AES derived key.
The iOS security scheme is in their book:
https://www.apple.com/business/docs/iOS_Security_Guide.pdf
There is no back door, the AES key on the chip is missing one part. That part is the passcode key the user creates for their device. (tl;dr look on page 11).
Even if Apple were to provide a dump of the NVRAM on the device, it would be encrypted. The FBI would still have to brute force guess the passcode key.
I am not sure what they are looking for. The texts and meta data should have been on the carriers servers. If they are looking for word docs or text files of manifesto’s or next plans that might be stored on the phone, I think they are looking in the wrong place.
It seems that the FBI wants Apple to create a special form of software that will allow running an electronic brute-force attack on-device in the hope that the attackers chose a weak passcode that is brute-forceable.
Also unknown is whether on newer devices, it’s possible for Apple to update the Secure Enclave firmware without invoking a hard penalty (UID reset). The Secure Enclave adds a 5-second retry timer on top of the 80ms or so per attempt PBKDF2 limitation.
Apple’s architecture is designed such that a brute-force attack is not executable off-device. Although it might be possible, with customized OS firmware, to just hook up the input and output of the AES engine that the UID is used as a key for – I’m not sure whether the AES engine is within the PBKDF2 loop or if it’s just used on the output of that loop to encrypt the key. If it’s outside the loop, in theory, you could run a rainbow attack with parallelized PBKDF2 off-device, send a series of inputs to the AES engine to be encrypted with the UID, and send the resulting data back for a brute-force attack on a data image. (The 5-second timer on newer devices would neuter this kind of attack).
At least one former Apple employee who worked on the Secure Enclave is on record as stating that its firmware can be updated just like any other, without wiping the keys.
” It could be viewed that Apple had a hand in the mass murder and they don’t want incriminating evidence released that could damage Apple.”
Complete rubbish and utter non-sense…
Listen to yourself… Apple had a hand in a mass shooting and are protecting themselves? If you genuinely believe that even 1% is true then you are a fucking imbecile and I am completely unapologetic for the strong language and the insult.
Maybe I didn’t word my post right but I didn’t state Apple were behind it. I only inferred that paranoid people may think Apple were behind this somehow. Same people who thinks JFK assassination were inside job. Same people who believes moon landing were faked,
http://www.dailymotion.com/video/x5ouiw_bill-hicks-jfk_fun
Pretty sure the FBI already has hacked and/or a backdoor into Apple products.
The FBI likes to make this big media stink over encryption every so many years to give terrorists and the mob a false sense of security. That their phones are ‘secure’.
The fact so many here buy this shit is amazing. You of all people should be smarter than this.
If Apple can make such a firmware update – it means they already have a backdoor. No good for their business after they said “we have no access to your data”.
And about privacy – there no fundamental difference between “NBA has access to your data” and “Apple has access to your data”. So best for Apple – to state they have no access so they can not give it to NBA.
Again, read the actual background and you’ll learn this isn’t true. Apple’s update wouldn’t give them access to the data, it would make an FBI brute force attack on the user’s PIN practical.
Does not matter: time to bruteforce PIN (4 or 6 digits? LOL) is really small.
And about possibility for Apple to make such a firmware. There is a question: do you need to unlock iPhone to update firmware? If yes – Apple can’t help NSA. If no – there is a security hole already (I suppose there is no such a vulnerability in iPhone 5s/6: PIN attempts counted not by firmware but by Secure Enclave).
Stop shifting the goalposts – you said “If Apple can make such a firmware update – it means they already have a backdoor.”. Since when is “trying all the pin numbers” a backdoor?
Since the 70s or so, when bruteforcing a 4 digit PIN became trivial. If Apple is able to install a firmware update that changes it’s security policies to something easily broken into, that’s a back door. The phone should need to be unlocked for a firmware update, to be secure (ignoring other vulnerabilities).
The fact that Apple even has the option of complying or denying means that the phone is insecure.
Believing that the FBI can’t break in without Apple’s help is exactly what the FBI wants. I wouldn’t be surprised if they orchestrated this whole thing with Apple. False sense of security for criminals, and free advertisement for Apple. It’s not surprising that Google is jumping on board with this.
See my other recent comment for some background on the tradeoffs at work. The fact that different device firmware can weaken some protections does not constitute a backdoor unless you stretch the word’s definition to breaking point.
Since Apple stated “we erase all data after 10 attempt to enter PIN”. If someone can turn erase off – it’s a backdoor.
Now lets see you do it in less than the 10 tries before the self wipe trigger kicks in. One tiny tidbit that makes a 4 digit pin massively more secure. I have a password dongle that only has a up down left and right on it. your password ot get in is 4 presses of those buttons and it’s uncrackable by brute force… because after attempt #3 it erases the contents.
The ability to modify the behavior of the chip that evaluates the PIN through an Apple-signed software update *is* the backdoor. A short PIN is trivially easy to brute-force, given the opportunity. If the iPhone required the user to enter a long password that was the actual encryption instead of a short & convenient PIN number that just unlocks the encryption key – in other words working like a typical PC with full-disk encryption – there would be no backdoor.
So… letting users choose short pin numbers is a backdoor? That’s certainly a… novel… definition.
No, forcing users to use a key storage system that can be easily brute-forced with a software modification is a backdoor.
It can’t easily be bruteforced – it’s still slow, just not as slow once you remove the firmware-imposed delays. If you choose a longer passcode than the default of 4 digits, bruteforcing is still completely impractical.
Here, let me show you the definition from Wikipedia “A backdoor is a method, often secret, of bypassing normal authentication in a product, computer system, cryptosystem or algorithm etc.”. Normal authentication is not being bypassed – it’s being made faster.
Further, the possibility to install a backdoor – which there isn’t, but let’s assume for a moment there is – via an update mechanism does not equate to it _being_ a backdoor. ‘Backdoorness’ is not transitive. By the same logic, Apple’s iPhones all contain listening devices, because a future firmware update could install them.
arachnidster says:
…
“Here, let me show you the definition from Wikipedia “A backdoor is a method, often secret, of bypassing normal authentication in a product, computer system, cryptosystem or algorithm etc.”. Normal authentication is not being bypassed – it’s being made faster.”
You’re getting lost in the semantics, but not looking at the security system as a whole. If you remove part of it, and it compromises the rest, you have created a backdoor. The “normal authentication” is a x digit password with x number of attempts. Changing any part of the authentication is a backdoor because it is no longer normal.
No, you have created a vulnerability. See, we have a word for that thing, there’s no need to try and repurpose another for it.
Being able to update the firmware on a device with the knowledge and consent of the person in control of the device does not constitute a backdoor unless you alter the word’s meaning beyond recognition.
I can agree they could have made other tradeoffs, but that’s what they are – tradeoffs. If they made it mandatory to unlock a phone before a firmware update could be applied, it would be impossible to unbrick a bricked phone. If they made it impossible to update the secure enclave, it would be impossible to patch out a vulnerability in its firmware. If they made updating the secure enclave require wiping the keys (this is the tradeoff I’d personally think was the best idea), you would effectively have to reimage your device before you could upgrade it.
Error 53, no?
How do you back-door data encrypted by a key created by the phone user? Do they install firmware with a key sniffer and force the dead (San Bernardino) owner to unlock the phone? Though in the case of the phone owned by the meth cook, persuasive use of a monkey wrench may do the job, at the expense of a few broken bones.
https://imgs.xkcd.com/comics/security.png
They’re dead…. That is why this is so useful to the spies.
“How do you back-door data encrypted by a key created by the phone user?”
Easy – have the encryption software store the encryption key in an undocumented location deep inside the phone BUT be sure not to tell anyone!
>
Was just going to post this. :)
Help me understand. If the FBI has the encrypted phone image, and Apple provided an unencrypted image, doesn’t that give the FBI an edge to being able to unencrypt other iPhones? Perhaps it’s more complicated than that.
Regardless, if the government wants to legally or illegally invade one’s privacy they should do it themselves, not expect others to commit the acts for them. I think the judge over stepped his authority to demand an action from a citizen.
If encripted+unencripted message helps you to get encription key – it’s a fail. All modern cryptographic schemes are created to avoid this problem.
“. In the days and months after the shooting”
Key word after. Having back doors would not have been enough to prevent this.
The solution is not backdoor computers,
First recognize Islam for what it is, a dangerous death cult. Do not allow any who claims to be Muslim into the country, evict anyone already here. If no one wants them, drop them in the ocean. Blockade all countries with theocracies.
Second, is to eliminate “gun free zones”. 9-11 would not have happened if pilots and stewards were armed. San Bernardo would have been mitigated if one of the innocents was armed.
Third, make gun control, about gun control. Teach gun safety and marksmanship as a standard aspect of elementary schooling.
Fourth, eliminate background checks for getting guns. Dangerous people with either mental or violent criminal history should not be free in the first place.
“Second, is to eliminate âgun free zonesâ.”
The Gabby Giffords shooting aside, every mass-shooting in the past few decades has occurred in a ‘Gun-free zone’ – creating more gun-free zones doesn’t seem to be a valid response.
>
Umm… you seem to be attributing the meaning of ‘create’ to the word ‘eliminate’. Polar opposites… that’s like the Fahrenheit 451 use of firefighter compared to the guys in the station down the street from my house.
Gun-free zones only keep legal guns out of the area, they don’t seem to deter mass-shootings… In fact, they are almost exclusively where mass shooters go to act out.
Do gun-free zones cause mass-shootings? Of course not, but they don’t seem to be an effective deterrent.
>
He says to GET RID of gun free zones, not make more of them.
And I agree with that, which is why I gave my supporting argument…
I didn’t say he was wrong, I didn’t say he was calling for more gun free zones.
>
I’m always fascinated when Americans are so keen to throw out core aspects of their own constitution in a quest for ‘safety’.
Even when they had intellectual giants like Ben Franklin warning them against such acts.
Don’t forget about Thomas Jefferson and Patrick Henry (<– my personal favorite)
Amen.
It is not just Americans. Stupidity and Surveillance (SS) is spreading everywhere.
I think it is a moot point. Apple doesnt give a crap about its users if you think they do consider apples response in the past to paying taxes, reinvesting in the united states / its people. They said they were under no obligation. They dont care one bit about you or your privacy. This isnt the big bad wolf standing up for my rights, this is the big bad wolf doing its best to limit its own exposure over the proposed solution. That is the first point. The second is they could just as easily make a one off hw stand , and copy the encrypted phone contents into it and brute force a totally software version of the phone . Brick it and repeat at the speed your dev box could address another virtual phone.
There is no such thing as secure.
If it can be done… It will be done.
PS this would mean they controlled the illusion of time, controlling the simulation and could brute force them at any speed they chose, and they could use their HUGE banks of storage to facilitate fast changing of the virtual box’s contents to refresh after they get wiped.
No, they can’t – the hardware key is embedded in the device, can’t be read by firmware, and is necessary to decrypt the storage.
Yes, that’s exactly what I’m saying. It’s derived from the user’s pin or password and the hardware key, which cannot be read by firmware. The only operation allowed, even with firmware updates, is deriving a key, and the derived keys give you no information about what the secret hardware key is.
Clarification – by ‘it’ I mean the key used to decrypt the user’s data.
I’m not sure I follow – what is?
Yes. But it doesn’t have to be able to read it – it only has to be able to derive the encryption key for the disk encryption from it (given the right passcode), which the hardware will allow it to do.
Why is it reasonable for apple to invest what looks to be thousands of man hours to do this? It’s unreasonable no matter how possible it is.
Thousands of man-hours?
To remove the failed-attempts counter that resets the phone, wiping it’s contents – that number seems a bit padded…
>
Must be a project manager ;)
It’s funny… This has strong echoes of Apple’s 1984 and 1985 SuperBowl commercials.
“Itâs funny⦠This has strong echoes of Appleâs 1984 and 1985 SuperBowl commercials.”
My friend, you and I have different ideas about what is and what is not ‘funny’.
>
The solution is simple, the president should order the NSA to give the information to the FBI.
Because we all know the NSA already has what’s in the phone, recorded while it was created.
They have the position,. the numbers, the times, and very very likely recordings of conservations.
Plus copies of all digital communication.
It’s a bit idiotic that there STILL is this refusal to cooperate between the agencies, when it was previously determined by the government themselves that that lack of communication was what allowed 9/11 to happen. (assuming you believe that excuse)
But of course the NSA has a history of many decades of not wanting to share with anybody. But as I said, the president can order it and nobody needs apple to be their henchman.
Isn’t there also an issue that iCloud syncing could have been enabled on the phone, and thus Apple itself has possession of information, even apart from the engineering request/command on the iPhone? If that is the case, and Apple has iMessage logs, usage logs, location traces, etc, that should all be information that can be demanded under a legal warrant.
Furthermore, does the iPhone use an encrypted filesystem? Surely some NSA lab could dismantle the phone and do a extremely technical hardware attack on it.
Apple already completely cooperated with all they could so far, so any cloud copy available was already obtained.
Also it’s not the NSA that demands this hack but the FBI, as I say in the comment above yours, the NSA likely already has all the info that possibly could be in the phone but just isn’t sharing it with the FBI.
And yes the filesystem is encrpted, this isn’t 1970 and the whole locking down without apple having the access was a response to incidents with the massive snooping by the feds as exposed by Snowden and the like.
why not beef up the existing pre cursor laws and anyone caught buying say for example heating fuel or diesel fuel and lawn feed then would be flagged for arrest for making an anfo bomb
they already have a system in place that if you buy too much sudafed, lithium batteries, drain cleaner they then bust them for the makings of meth.
same for moonshine buy too much sugar and corn and propane fule they then suspect moonshine
What has that to do with this case? It’s about a guy who together with his wife gunned down 14 people, not about a bomb.
And incidentally when he transferred money to his mom (I think it was his mom) he seemingly deliberately did it in the below 5K amounts to avoid flagging. Not that the NSA isn’t know to specifically flag people doing that kind of thing (we can conclude that from leaked NSA programs), but they (the NSA) won’t talk and this is an FBI investigation.
if the nsa gets involved it usually is terrorism like isis so instead of cracking the encryption to discover the plot they monitor the precursors and then interrogate everyone who buys anything that can be an implement of terror or drugs and alcohol.
Check this video : https://www.youtube.com/watch?v=vILAlhwUgIU , at the 45:15 mark.
If these documents are to be believed, and I think they are because they came from very serious agency, Apple’s encryption is just smoke and mirrors. The fact they can crack your phone speaks enough about it. Good encryption is impossible to break, for example guys who designed AES can’t break it, nobody can, in a reasonable time. If somebody uses AES and stores key on the phone then that’s just crap, not AES, they could use ROT13 or something like that.
So Tim Cook is basically refusing to open up the back door?
.
Am I the only one to make that connection today?
Nope, I’ve got the same impression. The way I understand his words is like “we won’t do it” which is not exactly the same as “we can’t do it”. Therefore, if Apple can do it then it is possible, hence anyone “can” do it (of course not for free). When I write “it” I mean get the data cheaper then by brute-forcing soldered off flash chips.
These are very strange words of Mr. Cook’s because they make the whole iOS security, as described in the “iOS Security Guide”, look more like security by obscurity than a solid design.
“If Apple can do it then anyone can do it” – how do you draw that conclusion?
If Apple can take a route that bypasses encryption (files are encrypted) and is shorter (cheaper, quicker etc.) than brute-force attack, then it means the shorter route exists. UID/GID extraction from a chip, code injection via JTAG into a booted device, you name it.
Then, to be precise I need to explain that by writing “anyone can do it” I mean an entity which has enough: knowledge, tools and time, but still less (especially tools and time) than it is required to search the full key-space.
Well, Apple’s options still require a brute force attack – they can’t avoid that, only make it quicker.
But even if Apple could bypass it, that doesn’t mean anyone else could – the iPhone will only accept firmware updates signed with their private key, which only Apple has. There are a number of options open to Apple but not to anyone else.
until they (Apple, Google, and other smartphone makers) come clean on whats going on (i.e. publish source code so it can be compared with firmware) in the Secure World (SW state of TrustZone), I am treating this as Smoke & Mirrors… this could be a win win situation for government and Apple: Apple seems trustworthy, and government can make Apple look like the devil’s advocate…
clarifying the last seentence:
this could be a win win situation for government and Apple: Apple seems trustworthy _since their goal is selling phones, or higher prices from government per snooped bit of data_, and government can make Apple look like the devil’s advocate _since their goal is illustrating how crypto enables terrorism, and getting more legalized spying laws enacted_…
I too remain skeptical. But even when it’s smoke and mirrors, the law precedents flowing from it are real.
which may be even scarier, if plaintiff and defendant are working together so as to manipulate the arguments for and against to achieve a desired precedent… like parallel construction but to set a precedent in a controlled way…
So to underscore the BS, I hear he had several phones but destroyed (burned) them before the attack, he only left his work phone, which is the phone talked about here.
Or in other words it’s almost certain that there is no information at all on that phone, not only because he’d have to be silly enough to use his work phone for terrorist activities, but he would then have to deliberately not destroy it.
So it’s all about setting precedents for the FBI not about the non-existent info in the phone. And that info would incidentally be info that isn’t in the cloud copy or in the celltower logs etcetera, so yeah it’s all BS
John McAfee’s take:
http://www.businessinsider.com/john-mcafee-ill-decrypt-san-bernardino-phone-for-free-2016-2
I’m keen to see him try, just to find out how he’ll socially engineer a dead person.
https://en.wikipedia.org/wiki/Substance-induced_psychosis
If the phone is virtualized none of this matters, they just keep trying on different copies of the phone until they get in. duh.
I’d be very surprised if the NSA can’t already do this, and I am sure they could if they were instructed to do so because there is no hardware than cannot be read down to the individual component state and then emulated in software.
If you have the device in hand, which they do, all encryption will fall if it uses such a small key, it is the law, a law of physics, the only question is the cost of making it happen vs the benefit of doing so.
Apple’s short term PR strategy just puts off the inevitable and motivates governments to find a universal and complete solution to the problem.
[N.B. I am not making a statement about the ethics involved, I am just pointing a few facts that are very hard to ignore once you are aware of them.]
Again, they can’t virtualize it, because they can’t get at the hardware key, which is required for decryption. They could potentially decap the chip, sure, but that’s involved, expensive, and far from certain to work – if you screw it up, you lose the key for good. Less risk to try and coerce Apple into helping you guess the pin.
If you have a coherent X-Ray source you can read electrons via their diffraction influence. Military intelligence in my country have know about this for over ten years. I know this because I was privy to a discussion that involved the implications of publicly published science that is even older. You don’t even need to touch the device so it is completely non destructive. Seriously, you guys have no idea what is possible when you have a lot of money and the power to get time on the gear at almost any facility. It really is just a question of two variables T*$.
Go and study some physics child and stop defaming members of the community. I’m not even a yank..
No one in their right mind will lay out a register that will hold a cryptographic key in a neat row so it’s easy to pick out the key bits once the chip has been decapped or X-rayed.
Done right you will end up with register bits in seemingly random locations on the chip and out of order. So even if you find all the 256 Bits of the key (there are other registers as well), you have no idea of their order. For that you need the whole set of masks for the chip and trace connections.
I don’t dispute that this could be done, but it’s expensive, slow and error prone.
You didn’t understand a word I wrote. The changes in electron density in a live conductor can be read, in real time because of how they interact with x-rays and having a coherent x-ray source is the key to doing it to solid state circuits.
I’m not quite yet a senior citizen. I remember saying the pledge of allegiance every morning in school, and even the nuclear bomb drills every month where we crawled under desks and did the duck and cover similar to the later instituted tornado drills. We were proud to be Americans, but if we had come out of homeroom in high school to find that the doors were barred and we were locked in, we would have kicked the doors down, screaming that we weren’t criminals. We were Americans with constitutional rights! The school would have probably been sued by parents for false imprisonment! I can’t count the number of times I drove to high school with either my shotgun or rifle in my vehicle, where it stayed locked til after the last bell, when I would retrieve my camo from my locker, change in the bathroom, before leaving straight from school to go hunting. I toted a case pocket knife with 3 blades(exactly like me Grandpa’s) everywhere, everyday. We were in the cold war, nuclear destruction was at least a passing thought in everyone’s mind on a daily basis. The USSR was a whole lot scarier enemy than these piss ant terrorist. Our rights are being eroded at the fastest pace in history, and our children are being taught in public schools that whatever anyone in authority (teachers,principle,etc) is ok because they are in authority. They forget to teach that the authority was granted by us, the people. Case in point: My Daughter was given in school suspension for talking in Middle School. I had no problem with this. The day she served her punishment she came home with a note stating she had after school suspension the next day for, guess what, talking, but this note went on to state that she received the suspension for smiling at someone. To Quote the Disciplinary Referral “Smiling is communicating therefore she was talking”. When I tried to protest I was told I had no say in the matter and told to leave the school grounds or they would call the Sheriff’s Office. To quote Ben Franklin, “Those who would give up essential Liberty, to purchase a little temporary Safety, deserve neither Liberty nor Safety”. The Courts are supposed to prevent this erosion, but will go alone with whatever the majority will tolerate. It appears the majority are now a bunch of sheep. Thank you Apple, or having a little backbone.
So glad I don’t have kids in school, cause I would be in so much trouble! My reply to that administrator telling me I have no say, CALL THE COPS! BUT first call your self an ambulance cause in the 5 to 20 minutes the cops take to arrive I will trash your ignorant butt! I do have say, My kids would not be in that school, the school would be subject of legal action, as would any idiot telling me I cant say anything and a smile isn’t anything close to the “communication” my fist is going to make when it “talks to your jaw, eye socket and nose!! and its fast communication to faster than you can reach for a phone! and if you reach for it I will take that as you communicating you desire a busted wrist as well! ZERO TOLERANCE HAS NO PLACE IN SCHOOLS, Schools seem less and less education focused and more bent on punishment and teachers making it through the day with no confrontations or actual “work”!!
Amen! I was raised in much the same environment. I am unwilling to sacrifice personal freedoms to facilitate temporary -or even long term- security.
I think the true question here is does anybody have a true right of privacy? Or should a government -any government- have unlimited power to twart any and all measures to maintain such a right of privacy?
The US government fortifying the illusion that the NSA uses those circuits in the Snowden leaks and has a lot of idiots inside..
So, you install FBiOS on my phone. It gets you past the login screen and you have an unencrypted filesystem. Now explain how you actually read my private data which is encrypted via an AES-256 block cipher using a key that has never been exchanged. People don’t actually still trust the default security on mass-market consumer devices do they?
This is the issue with choosing a 4 pin code, the key space is tiny. If the iOS is changed to disable the destroy the encryption key for FDE after 10 tries, and eliminate the exponential backoff then they can brueforce it trivially.
They should expand such PIN codes to include letters, that at least will increase the number of possibilities and surely people can remember 4 or 5 letters/number codes. In fact remembering thing with a letter or two in it is probably easier.
And I think there’s enough screen real estate to display a larger keyboard, or you can limit the letters to say 6 or some such which would still increase the range a good amount. and you can easily pop up a pad with 0-9 and a-f.
“Being right, having a valid argument, or even having evidence to support assertions doesn’t matter”
That’s the Brian we have all come to know and love!
Technology does not matter, Encryption does not matter.
What matters is the admissibility of evidence and a court order compelling innovation.
First Evidential: Most of the above suggestions ignore the fact that the FBI wants this data for an ongoing and potentially other cases, which requires very careful handling to avoid all risks of later accusations of planted evidence. This means that the FBI is stuck asking for Apples help because if they ask anyone else, those entities would have to be court licenced for the purpose.
Second Innovation: Apples thrust here is that this court order is in effect compelling them to innovate a way around their own product. Imagine if Apple were a safe manufacturer and the FBI comes to them and says, ‘you must provide to us a means by which we can open this model 5c safe, without risk of damage to the contents’. If you wanted to stay in business you would be compelled to say NO, Until the highest court in the land had affirmed the order.
In the end each party is following the only path they can take to protect their own interests, to do otherwise for the FBI would render the evidence inadmissible (Sorry McAfee) and/or result in a charge of fiscal irresponsibility by the shareholders of Apple.
Yeah I’m sure that the US authorities would let a ISIL member go on his merry way if they found out about him through illegal means.. as history has shown, they are very proper, it’s not like they do black ops and run torture camps and prisons without any legal basis on say some marine base on some island.
Nuh uh!
As to the device and OS, it is no different than a lighter and paper docs. Oh, remember those magnetic slots to quickly erase floppy discs! Will they next ban destructible info, unwipeable memory? Eventually more of our stuff will be cloned off into the cloud without consent.
“This was the third deadliest mass shooting in the United States in recent memory”
All I can think of when I read this is: wow, if ‘recent memory’ is this short, it’s high time for a memory upgrade… There were 7 mass shootings in December 2015 already. http://www.gunviolencearchive.org/reports/mass-shootings/2015
In any case, I will only ever consent with a backdoor like this when there is a 100% guarantee that governments will never turn criminal. Which will probably coîncide with Hell freezing over.
I would worry more about the police shooting than terrorists in US. They were supposed to be the good guys.
http://www.washingtonpost.com/sf/investigative/2015/12/26/a-year-of-reckoning-police-fatally-shoot-nearly-1000/
stats between 2001-2003:
Deaths due to terrorism in US is about 20-30 a year (except 2001). Death due to gun violence is 33000 per year.
Quite recently me and my teammates discussed what if Intel was asked by the U.S. government to disarm some security measures in their CPUs. We thought about making cmpxchg non-atomic or preventing (IO)MMU from reporting memory protection violations. Some of these should be possible with properly crafted microcode update. Not to mention ME being a huge “backgate”.
intel? They would probably pitch the idea to the spooks, and if they said no would get very angry.
Personally if it were up to me,I’d ban comment sections on all websites. While it does have many advantages..i.e. people sharing ideas and communicating with each other….it also has many disadvantages….trolls sharing stupid ideas and communicating offensively with each other. BTW I’m fully aware of the irony of discussing the banning of comments section in a comments section. I guess I’m hypocrite…and in a way I’m sorta glad that banning comments sections is not my decision to make.
Google makes its money through ads….and so it ultimately makes money from snooping on people. Microsoft is increasingly doing this too. Using Windows 10 is almost like interacting with that really nosy (and sometimes perv-y) acquaintance that everyone avoids. Unlike Google and Microsoft, and surely many of the other tech giants, Apple makes a significant portion of its money selling overpriced hardware with better than average software integration. There is an (if only partial) offline nature to the Apple business model that companies like Google and Microsoft simply could not follow. Hence, Apple’s business model plays well to providing a high degree of encryption on its devices. This is why Apple has to take this stance. It offers something that others don’t offer nor monetize at least in the same way.
I also find it hard to believe that The FBI, NSA e.t.c really need access to the phone at all. Smartphones are rarely used to store things that didn’t originate on the internet or mobile networks. I’m pretty sure the NSA is capable of probing every little text, email e.t.c..possibly every literal ‘bit’ of information that originated from or was transmitted to that phone.
To me this seems like a bit of double speak and drama cooked by US security organizations to justify having back doors to the very few computing/communication devices left that still don’t have back doors. The public will naturally agree, because they view the state as a parent responsible to keeping them safe. The state would never use these these powers against its own people….nope that possibility doesn’t exist. The American public has come a long way since the times of Benjamin Franklin who said, “Those who sacrifice liberty for security deserve neither”.
I’m still questioning whether the St Bernadino attack was actually perpetrated by the accused couple. But perhaps I’ll post this conspiracy bacon in the comments section of a site that has little to nothing to do with hacks and making stuff and more with conspiracy bacon.
” The public will naturally agree, because they view the state as a parent responsible to keeping them safe. ”
I disagree: most people are afraid from expressing opinions that deviate from what is being propagated as “public opinion”, we are merely made to feel alone with our opinions. Whenever I keep digging for someones opinion, they always blame the “public opinion” … this “public opinion” is manufactured, and few people actually hold these opinions…
A wise green alien Jedi once said “Fear is the path to the dark side. Fear leads to anger. Anger leads to hate. Hate leads to suffering.”
Perhaps this is why someone like Trump; who knows how to capitalize on people’s fears is winning the Republican primaries.
As I said elsewhere, I agree that the NSA must have all the info, but I think they probably are refusing to share it with the FBI.
Realistically the phone is of no importance whatsoever at this point, except to get some nasty precedent set.
fully agree
“Realistically the phone is of no importance whatsoever at this point, except to get some nasty precedent set.”
There *could* be value in the contents of this dead man’s phone, but I agree this is/was a very compelling case to get whatever the gov’t wants as a precedent:
“Never let a crisis go to waste”
>
I love when people fight social constructs with social constructs.
Less people have that opinion.. Must be a troll..
There’s an insinuation here that if a person disagrees with you or with Apple that they are “just being contrary.” Seems strange to me
FBI is aiming for long term backdoor option than just a temporary access to the shooters phone. Its not just about the one iPhone, and they are using this sensitive issue to gain access to people data globally.
http://techcrunch.com/2016/02/20/decentralized-or-panopticon-pick-one/
Just because you could write this blog post doesn’t mean that you should. #LogicFail
Apple should have said yes to encryption… For a prepaid fee of $12B.
The government does not have the right to compel Apple to work for free.
The FBI is not asserting that cracking this phone will save the country from immanent harm, save lives or bring people to justice. No, the say it might – might – halo determine a motive.
Does anyone think if Apple creates this software that every 3 letter government agency won’t have a copy of it before it finishes compiling? It anyone that naive?
The government has misused every method of spying on citizens it has ever had. Every damn one.
There is nothing worth finding here. This is just the FBI using a terrorism case to get what it wants. It’s not worth the price.
https://www.youtube.com/watch?v=HmVakIrLEL0
Why don’t they PHONE CLONE
Boot Phone Test 10 keys reclone 10 modified boards running alternate sequence of the 4 digits
Aprox time about 20 days
Because they can’t clone the hardware key.
Never mind me, http://www.cellebrite.com/Pages/ios-forensics-physical-extraction-decoding-and-analysis-from-ios-devices
Recent phones and versions of iOS encrypt the whole device, not just emails and messages.
Pretend that Apple did not give up the code…PEROID !!!!
I prefer just not encrypting in the first place and store data in multiple offline secure locations. This also avoids RIPA/etc hassles and also prevents losing my own data due to encryption related problems (ie lousy stinking ransomware)