Most of us will know that Apple’s precursor to the Macintosh series of computers was a machine called the Lisa. Something of a behemoth compared to those early Macs, it had a price to match and wasn’t a commercial success. Working Lisas survive, but unlike a Mac you won’t find many at your local swapmeet. But what if you really must try this early Apple GUI? Never fear, because [AlexElectronics] is here with a much more accessible version on a FPGA.
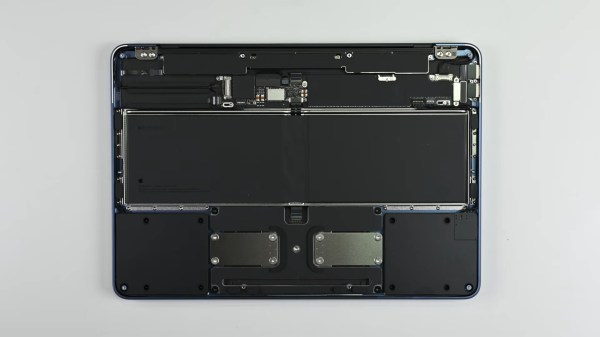
This Lisa has a surprisingly large PCB compared to the size of the FPGA, because of the number of connectors. It takes the approach of mixing new and old in interfaces, for example as well as original Lisa keyboard and mouse support, you can also use modern USB versions. There’s also an HDMI output for a modern monitor, and an SD card. Unexpectedly alongside the FPGA there’s a 40-pin DIP, it’s a UART chip because there’s no handy pre-built one for that particular chip. We’re told it will be up on GitHub when finalized.
Keeping old computers alive, especially rare ones, is hard. We like projects like this one, and we hope to see more developments. Meanwhile you can see the machine in the video below.