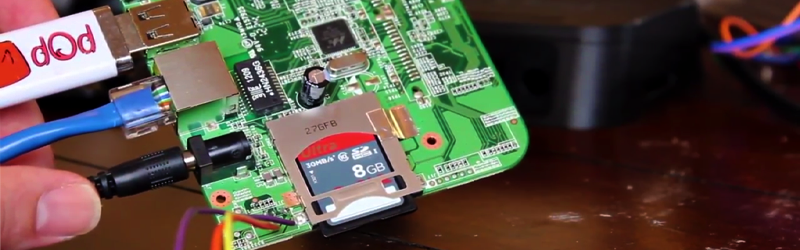
[Films By Kris Hardware] has started quite an interesting YouTube series on hacking and owning a PogoPlug Mobile v4. While this has been done many times in the past, he gives a great step by step tutorial. The series so far is quite impressive, going into great detail on how to gain root access to the device through serial a serial connection.
PogoPlugs are remote-access devices sporting ARM processor running at 800 MHz, which is supported by the Linux Kernel. The version in question (PogoPlug Mobile v4) have been re-purposed in the past for things like an inexpensive PBX, an OpenWrt router and even a squeezebox replacement. Even if you don’t have a PogoPlug, this could be a great introduction to hacking any Linux-based consumer device.
So far, we’re at part three of what will be an eight-part series, so there’s going to be more to learn if you follow along. His videos have already covered how to connect via a serial port to the device, how to send commands, set the device up, and stop it calling home. This will enable the budding hacker to make the PogoPlug do their bidding. In this age of the cheap single-board Linux computer, hacking this type of device may be going out of style, but the skills you learn here probably won’t any time soon.
















This is mobile v4 but prob applies to quite a few others too. and not just PogoPlugs quite a few Linux box devices have serial and work around the same principle.
Unfortunatly he explains that when you mess with the uboot partition he cant help you, Thats exactly the thing i was looking for here.
Maybe a Good soul might point me to some good vids regarding cpu uboot booting or ram booting if anyone knows.
The Uboot is your bootloader, I think you are in trouble unless there is a secondary recovery mode in which you could reflash the bootloader. either that or manually flash the chip if possible but you need the exact firmware for your device as it’s pretty much like a bios and specific for each version or revision of the device. what is your device?
I have one pogoplug V2 bricked, i’ve searched and saw methodes of directly communicating with the cpu over jtag with openocd and let it run uboot in ram and install uboot back into the partition.
However there is none or little known about this methode nor any useful vids
That sounds pretty cool, shame it isn’t documented well like you said.
I found no documentation about the JTAG port, but you could use a JTAGulator or similar to find the pinout, then load a copy of Uboot into RAM and reinstall everything. I only used the serial port but my Pogoplug wasn’t actually bricked (see my previous comment).
See http://forum.doozan.com/read.php?3,21789 for infomation on how to recover a PogoPlug E02 with Raspberry Pi for JTAG with OpenOCD. The method can be used with minor modifications for the PogoPlug v4 and other Marvell Kirkwood devices.
This probably won’t work, uboot is compiled along side your version on Linux when you’re building it using Yocto or Buildroot. You can’t just “load a copy into RAM”
Don’t know of any videos. But the V4 Pogoplug like many Marvell based devices can be booted via UART. See http://forum.doozan.com/read.php?3,7852,7852 for details.
Thanks for the info, very usefull
I have a second-generation Pogoplug (the pink one with four USB ports) and I bricked it while trying to install Debian. I opened it (danger: high voltage inside due to built-in power supply, disconnect it and use an external one for testing) and saw two unconnected but populated pin headers. After some probing I found one of them (the 4-pin one) to be a serial port and got a surprise: the Pogoplug wasn’t bricked! I only had to configure the bootloader to load the new OS, and I succeeded after some fiddling.
(I later found the serial port’s pinout documented on the web, but I spent less than 10 minutes “reverse engineering” the thing. The trickiest part was opening the no-screw case, which is surrounded by a difficult-to-remove piece of clear plastic; also, the pink stand can’t be removed without removing the motherboard too.)
Any chance to have a step by step. I found one unused in my old junk.
This may help you? Pogoplug V2 (POGO-E02 on bottom label ) https://openwrt.org/toh/cloudengines/pogoplug
Thanks!!!!
Came across a PogoPlug for only 5 euro at the local thriftstore recently. Didn’t know what it was (assumed it was a powerbank) until I googled it. The next day it was gone…
I have a bunch of Pogoplugs. They make very handy single purpose servers. Plus several USBs ports opens up various options from a NAS to using webcams for security.
I went and got one pf the PogoPlug PRO devices recently to make myself a server.
Many thanks for the posting of this-hopefully it will help. Unfortunately the disabling of SSH as an option has really complicated the updating of the OS and turning it inter a server-frankly, it stalled out as a project.
You can still open it and connect to the serial port to get a root login (that’s shown in the videos). The serial port also gives direct access to the bootloader’s console so you can reconfigure it if you need to.
Yeah, that is my plan after seeing the videos. I was going to just use the one project bootloader/os for it since I think they are already an arch box, just if I can get it less locked down I can get my imagehost up that I’ve been eying up making.
There’s this
https://archlinuxarm.org/platforms/armv5/pogoplug-v2-pinkgray
I’m using these for DNS as we speak – soon to be replaced with PI-Zero units.
I love these things except I’ve had one continuous issue with them – about 50% of the time during the boot they lose track of the bootloader and have to have it re-flashed. Most of these just require the old “revert” USB drive trick which gets them back to the default Pogo bootloader. Then I re-flash. But it’s very annoying especially if you want to move the unit around at all or don’t have it on a UPS.
Also if you aren’t paying careful attention it’s _really_ easy to seemingly brick these. Fortunately most of the time they can be recovered with the serial port. If you get one then invest the extra $2 for a Chinese made USB Serial->TTL cable. You’ll thank yourself later.
Oh also! SIMH runs effectively on these. I have a couple sitting on the back-burner with default MicroVax configs waiting to be set up. Cheap VMS clustering. :-)
Linux Device Hacking forum at http://forum.doozan.com is a very active forum with information on modifying uboot and loading Debian on various Pogoplug models and related hardware. Forum member bodhi is known for providing assistance to many posters who thought they had bricked their device!
You actually don’t need to gain access to the serial pins to own this device. https://www.exploitee.rs/index.php/PogoPlug_Mobile has a nice quick writeup on how to access a hidden diagnostic page and injecting some commands to gain root. SSH isn’t even needed for this method.
Have you tried this on a locked down pogoplug? It does’t work for me.
I’m trying to use a cisco rolled cable with the RJ45 cut off and rx, tx, and ground soldered onto the board and with the DB9 connected to a USB converter into my PC but I’m not getting any output through Putty (115200, 8, 1, none,none). Can anyone help me get this to work, I have 3 of these that I would like to setup.
How to setup pogoplug pro to see external hdd to see in local network ? Thx
Hello! I moved and found two brand new PogoPlug v4’s that I had purchased but stored due to the last move. They were never set-up. Can they be hacked easily enough? All advice appreciated. Thx! – T
Not sure I’m just starting to research it and make it useful all my computer home theater whatever or all old school and hand me downs that I’m trying to make function Happy Thanksgiving and let me know if you find anything out I’ll be paying attention to it and if it’s not against policy anybody with any old school stuff all the way back to the actually ’80s but the current most current thing I’m using is an optiplex 990 the other is a Dell dimension 8300 and I will be paying attention to this website and anyone that can help me out thank you much and I’ll definitely disclose any info that I find that can help somebody out peace love and happiness and Miles of smiles. THX