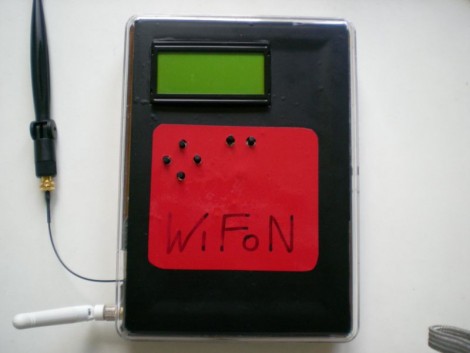
Inside this box you’ll find a La Fonera wireless access point. [Emeryth] and his band of miscreants built this portable device for WiFi security testing. The AP is running OpenWRT and has been set up to use the 16×4 character display as a terminal. An ATmega88 connects the LCD as well as six buttons to the UART of the La Fonera. From there, a set of Ruby scripts takes care of the communication protocol. As you can see after the break, this setup allows you to scan the area for WiFi, showing channel, SSID, and MAC information. Although not specifically outlined in the video we suspect there’s some more devious tricks up its sleeve too.
[youtube=http://www.youtube.com/watch?v=bPdmfo15eyw]















I fukken love it!!!
that’s a fun little box :)
It’s a great idea but it looks hard as hell to use.
I would suggest a palmtop with a supported wifi card running BackTrack as a solid alternative. That’s what I use.
Very very nice.
Point of this =’s?
You can do the same thing+ more with an iphone, itouch, etc…
I want one!!! :)
@Word
this doesn’t cost $500 and won’t crash every 5 minutes.
@word
You can get nmap for the itouch? how about metasploit? wireshark? pcap? aircrack-ng? It’s a bit hard for me to browse the app store on my linux box…
If you jailbreak your iPhone you can put aircrack-ng on it.
Sounds like a mystery, so what I’d want it to do is:
1. Identify and crack any WEP secured network in range. (Aircrack/similar scripts)
2. Sniff and decrypt packets for cracked networks as well as sniff open network packets. (Wireshark)
3. Filter these packets by keyword and save the “interesting” information (Ettercap/Wireshark/etc)
4. Perform ARP poisoning and/or DNS spoofing. (Ettercap/etc)
Of course this is all very illegal and care would have to be taken to be sure only your own networks are targeted, even though Google does some of it, haha.
Can’t believe we’re being featured on HaD, thanks guys!
It’s true that it’s big and doesn’t do anything a notebook/PDA with linux and a good wifi card can’t, but it’s way more fun.
The initial idea was to include automatic WEP cracking, password sniffing, AP spoofing using Jasager and other magic, but we ran out of time (this was a school project) :P
I believe that the hardware of the Fonera has much more to offer than most other wifi chipsets and I’m already working on “Wifon 2.0” to prove it.
@M4CGYV3R
Go ahead show me a pda that can run Backtrack :rolleyes:.
The closest thing to what you are talking about is an old Jornada 720 or 728 running aircrack and Jlime, but you would be limited due to the old hardware and only B pcmcia cards.
The other option is to buy a viliv n5 or an mbook bz from dynamism for ~$600, a seperate usb wireless card, and tweak Backtrack to work on it. The cost is likely far greater than building this.
Cliff Notes: You are an idiot.
I’ve been looking to purchase one of the original Fon routers, but I can’t find them for sale. It’s definitely for a portable hack device so the new one is a no-go. Where do you go to buy them? (fon doesn’t sell them anymore)
ROFL @ “DEADBEEFCAFE” MAC address. I’ll have to remember that one.
And it’s bound to have some tricks up its sleeve… It looks like it has a “deauth attack”, so probably some MITM stuff in there too.
@M4CGYV3R + WORD
Its not the point what else they could have chosen, they made it this way to quench their thirst for knowledge, and as a PROJECT, it means half (if not more) of the fun is in building/developing it.
Good job Emeryth + co
@Spliff666
Ignore those two, they are idiots, WORD somehow thinks the unsupported Marvell chpset in the ipod touch and the iphone can work for this, there is no LOL big enough.
I’m a mech engineer, so not network protocol savvy as most of you – would the intention of this device to impersonate the SSID of a network then examine the packets of failed connects to determine the key? Or is this more about passive packet sniffing and analysis…
@Shield:
“show me a pda that can run Backtrack”
http://www.asustablet.com/
http://www.newegg.com/Product/Product.aspx?Item=N82E16834146704
http://www.motorola.com/droid2
And I never said anything about a PDA.
“this thing” <<<<<< N900
The only advantage this has over it is the stronger transmission power and range. You could easily hook up some poratable wifi amplifier on your N900 as well…
Secondly that LCD is too small and you cannot enter wireless keys. On n900 you can bruteforce wpa networks/crack wep or inject packets in etc etc just like what you could do on a laptop.
I would rather call this project for some kind of wifi radar and NOT pentesting equipment and from those there are plenty others…
“…a set of Ruby scripts takes care of the communication protocol.”
Kind of like doing plastic surgery with knitting needles. Alas, the new generation…
Interesting stuff, besides maybe the choice of Ruby which I think is way overkill for these minimal platforms. Plain C, shell or even Lua would have been more suitable and fast.
Anyway I have somewhere one of those old Foneras (2100) I would like to reflash, but last time I checked the process was hugely time consuming and most pages about the reflashing process are outdated or link to non existant files. Does anyone know any working pages about easier ways to reflash it? Thanks!
None of us were familiar with Ruby before the project.
We decided to use it because: writing in plain shell would be too complicated, C would be a pain in the ass to debug, Python is too big to fit on the flash memory of the Fonera, and Ruby is surprisingly small and fast.
@qwerty
The easiest way to flash is by using a serial cable, but if you don’t want a hardware method, the OpenWrt wiki has info about reflashing from the original firmware, and the required files are still online.
@ M4CGYV3R
You must be joking. Seriously you are retarded. You are trying to compare $Texas 10.1in computers to a handheld device that cost the guy $20 and can fit in his pocket. Aslo why dont you show me Backtrack on a Droid? Show me that moniter mode and packet injection. Your wall posts read like a script kiddie.
@Cynyr
You can simply install the Metasploit Framework on the iPhone – see http://www.youtube.com/watch?v=l1GEaqYw3ds. I don’t think it works with Metasploit Express, though (commercial version).