
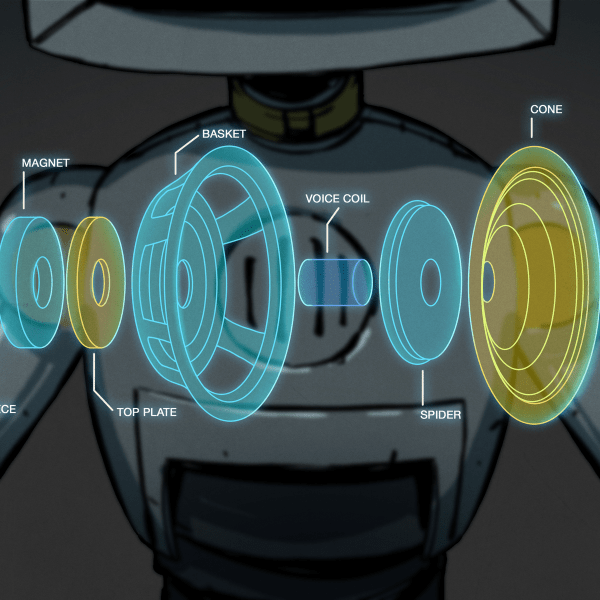
[Gray] over at Geek Chique had a bit of an eBay mishap and was suddenly the proud owner of 16 Vocera B1000A badges. If you are not familiar, these badges are small, lightweight communications devices similar to the famous Star Trek communicator, which allow users to talk to other individuals via VOIP. He was working on getting the remaining badges up and running by reimplementing the server software, and figured that since one of the badges he purchased was not working, he might as well take it apart.
It took him awhile to get the well-made badges apart, requiring a rotary tool and some elbow grease to get the job done. Inside, he found that the device was split into two circuit boards, one being the “WiFi” board, and the other the “CPU” board. The WiFi board uses a Prism WiFi chipset, which was incredibly common at the time of construction. The CPU board sports small SRAM and flash chips as you would expect, with a Texas Instruments 5490A DSP running the show.
While it remains to be seen if tearing the device down helps [Gray] to get things up and running again, it never hurts to take a closer look to see what you are working with.










The hospital I work at uses these…If you are not scavenging these for parts, they make fairly good paperweights.
Sorry, so whats the point of this article? He bought some badges and took them apart.
Not trolling or anything. Just wondering if I’m missing something.
So…are these like WiFi FRS radios? I guess I don’t understand why you wouldn’t just use radios or a cell phone instead.
You’re not missing much, to be fair. My basic aim is to reproduce the software to be able to use these without the £20,000 server application. Buying the 16 extra badges wasn’t really intentional, but since I had them I decided to tear the broken one apart. Ideally, I’d love to dump the contents of the flash chip and have a look at what it’s made of, but this is made harder by the fact that everything’s BGA. It was still interesting as a curiosity exercise that the device is not much more complicated than an arduino with a wifly shield.. The big problem with the project is that to easily reverse a network protocol, you need to be able to listen to communication between both ends – and I’ve only got one.
@M4CGYV3R The point of Vocera badges is that they’re nominally hands-free. You press one button, and the server uses speech recognition to understand what you’re trying to do, e.g. “Call Doctor Samuels.”
So hospitals have them but they don’t use them?
so basically they are WiFi VOIP phones .. with no keypad?
do you have sniffed captures?
@Zee No, hospitals do use them – they’re nicknamed ‘nurse crack’. @rasz I have captures of the initial requests from the badge to the server, but I haven’t been able to source a copy of the software, and the only place near me that uses it is Plymouth hospital – I figure if I started sniffing there I’d be in trouble. My local Apple store just has walkie talkies.
@Gray Simpson
Not sure if this is what you’re looking for, but this may be an alternative to the Vocera server software… It seems as if Lync (what the video is about) is able to communicated with the Vocera badges possibly on it’s own, without the Vocera server software.
Check it out here: http://www.youtube.com/watch?v=zB5C6gwDNSY
We’re back up, sorry about the downtime – dyndns went funky on me. @m1ndtr1p – Thanks for the lync (sic) but I’m afraid on closer inspection they’re still using the agent interface of the Vocera System Software. (And it’s still not open source!) It’s still a pretty interesting video, and I want a white badge now!
http://cgi.ebay.co.uk/31X-Vocera-Communications-B1000-Voice-Badge-Repair-/120724899065?pt=LH_DefaultDomain_0&hash=item1c1bc3c4f9
I saw this and thought of this….
There’s also this one! http://cgi.ebay.co.uk/Vocera-System-C2000-Chargers-x-2-B1000A-Badges-x-16-/320697421826?pt=UK_Computing_Networking_SM&hash=item4aab0e5002#ht_500wt_951 – In the UK, mostly working and with everything you need (Except for the Vocera Server Software)
hey you hacks, interesting conversation I have stumbled upon albiet old….we use a lot of these, but can’t find anyone to repair them….lets do some business….
I seem to be really late to the party looking at the post date but I can’t really find to much out there on what if anything can be repurposed to use in other DIY projects? I have accumulated a handful of these over the years and although I still lean heavily towards novice when it comes to electronics, I’ve been breaking apart and salvaging parts from every thing and before I toss these I figured there had to be a few good components. As for the use they were extremely helpful when I worked in the OR. As you can imagine the need for a hands free communication device is absolutely necessary. They could also do a lot more depending on your clearance like asking it where someone is? And it would tell you the location of whoever.. Etc and could also call outside lines not limited to the network. Anyway, hope you didn’t get stuck with 16 paper weights but if it’s something you ever revisit I believe I could help with what you were looking for.
Actually, currently I’m at about 40 paperweights. 18 of them work properly, of which three are B2000 and the rest are a mix of the B1000 versions.
Problem is, I only have one side of the conversation. I’ve been able to get three different handshake messages from the badge. Problem is, the only message I have from the server side is one I found in an old screenshot on a Cisco blogpost.
The problem I’ve always had, is that I only have half the conversation. Without a transcript of a badge logging in to the server, I can essentially go no further.
The original plan with the teardown was to see if I could recover data from the flash chip, either directly or through some kind of jtag/serial interface. But I’ve torn down both a B1000 and a B2000, and in both it’s a pretty gnarly looking BGA part. Even if I’d been able to do that, I’d have been stuck with the thorny problem of asking someone else to decompile and describe the process, so that I could then write clean room code.
I picked these up to play with today, and I’ve learned some more things about them – but there’s a lot that looks vaguely dead end-ish. I always suspected the four exposed test points on a B2000 were the usb ethernet connection mentioned in the firmware configuration tool, but while I’ve found a ground, none of the other four are power – so I’m struggling to see what the other three pins are – USB without power would only need two of them. When you actually pull the sticker off, they’re revealed to be part of two blocks of fourteen pins. Tracing them by eye is a nogo.
No idea what to do now!
Any update on your project? I work at a vet hospital that could really use this but 20000 is not in our budget + the company has flat out ignored us once they learned our size
github.com/combadge