Here’s a puzzler for you: If you’re phreaking something that’s not exactly a phone, are you still a phreak?
That question probably never crossed the minds of New Yorkers who were acoustically assaulted on the normally peaceful sidewalks of Manhattan over the summer by creepy sounds emanating from streetside WiFi kiosks. The auditory attacks caused quite a stir locally, leading to wild theories that Russian hackers were behind it all. Luckily, the mystery has been solved, and it turns out to have been part prank, part protest, and part performance art piece.
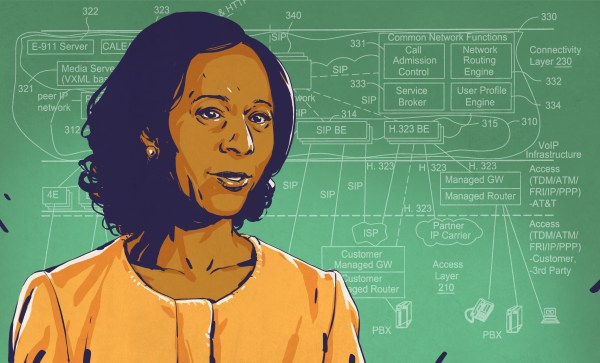
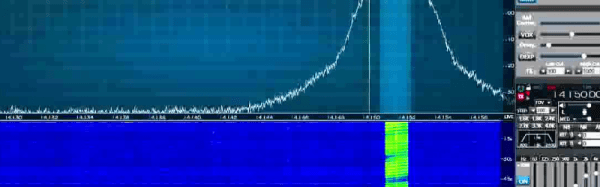
To understand the exploit, realize that New York City has removed thousands of traditional pay phones from city sidewalks recently and replaced them with LinkNYC kiosks, which are basically WiFi hotspots with giant HDTV displays built into them. For the price of being blitzed with advertisements while strolling by, anyone can make a free phone call using the built-in VOIP app. That was the key that allowed [Mark Thomas], an old-school phreak and die-hard fan of the pay telephones that these platforms supplanted, to launch his attack. It’s not exactly rocket surgery; [Mark] dials one of the dozens of conference call numbers he has set up with pre-recorded audio snippets. A one-minute delay lets him crank the speakerphone volume up to 11 and abscond. The recordings vary, but everyone seemed most creeped out by the familiar jingle of the [Mr. Softee] ice cream truck franchise, slowed down and distorted to make it sound like something from a fever dream.
Yes, it’s a minimal hack, and normally we don’t condone the misuse of public facilities, even ones as obnoxious as LinkNYC appears to be. But it does make a statement about the commercialization of the public square, and honestly, we’re glad to see something that at least approaches phreaking again. It’s a little less childish than blasting porn audio from a Target PA system, and far less dangerous than activating a public safety siren remotely.
Continue reading “Manhattan Mystery Of Creepy Jingles And Random Noises Solved” →